Secure memory card with life cycle phases
A memory card and security card technology, which can be used to detect faulty computer hardware, record carriers used by machines, prevent unauthorized use of memory, etc., and can solve problems such as high cost
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0017] memory system structure
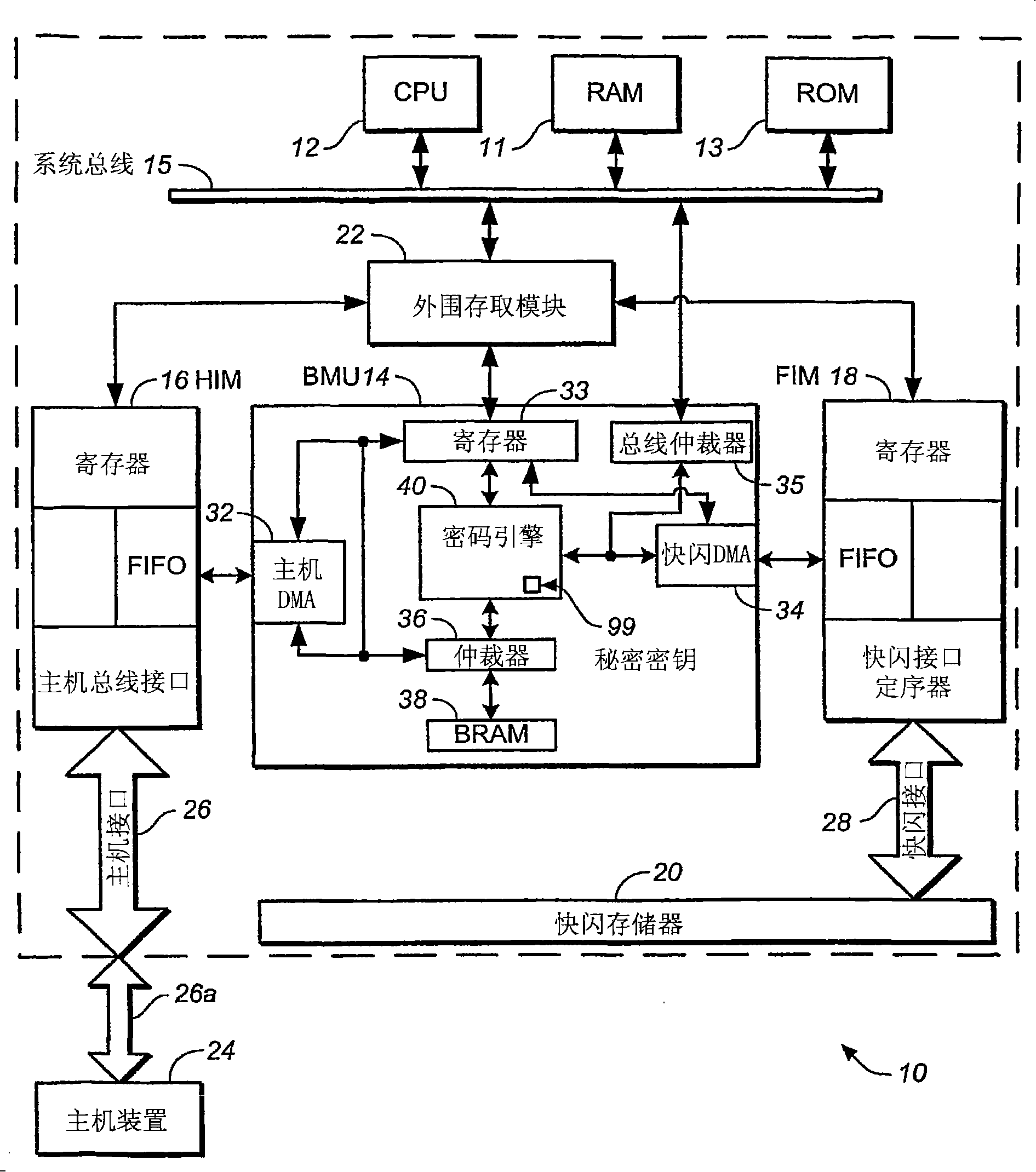
[0018] Figure 1A The block diagram of FIG. 2 illustrates an example memory system in which various aspects of the invention may be implemented. Such as Figure 1A As shown, memory system 10 includes central processing unit (CPU) or controller 12, buffer management unit (BMU) 14, host interface module (HIM) 16, flash interface module (FIM) 18, flash memory 20, and peripheral memory Take module 22. Memory system 10 communicates with host device 24 through host interface bus 26 and port 26a. Flash memory 20 , which may be a NAND type, provides data storage for host device 24 . Software code for CPU 12 may also be stored in flash memory 20 . FIM 18 is connected to flash memory 20 by flash interface bus 28 and, in some cases, by ports (not shown) if flash memory 20 is a removable component. The HIM 16 is suitable for connection to host systems such as digital cameras, personal computers, personal digital assistants (PDAs) and MP-3 players, cell...
PUM
 Login to view more
Login to view more Abstract
Description
Claims
Application Information
 Login to view more
Login to view more - R&D Engineer
- R&D Manager
- IP Professional
- Industry Leading Data Capabilities
- Powerful AI technology
- Patent DNA Extraction
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic.
© 2024 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap