System and method for verifying E-mail password
An e-mail and password verification technology, applied in transmission systems, digital transmission systems, user identity/authority verification, etc., can solve problems such as loss of important files and leakage of confidential corporate files, and achieve the effect of preventing loss.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
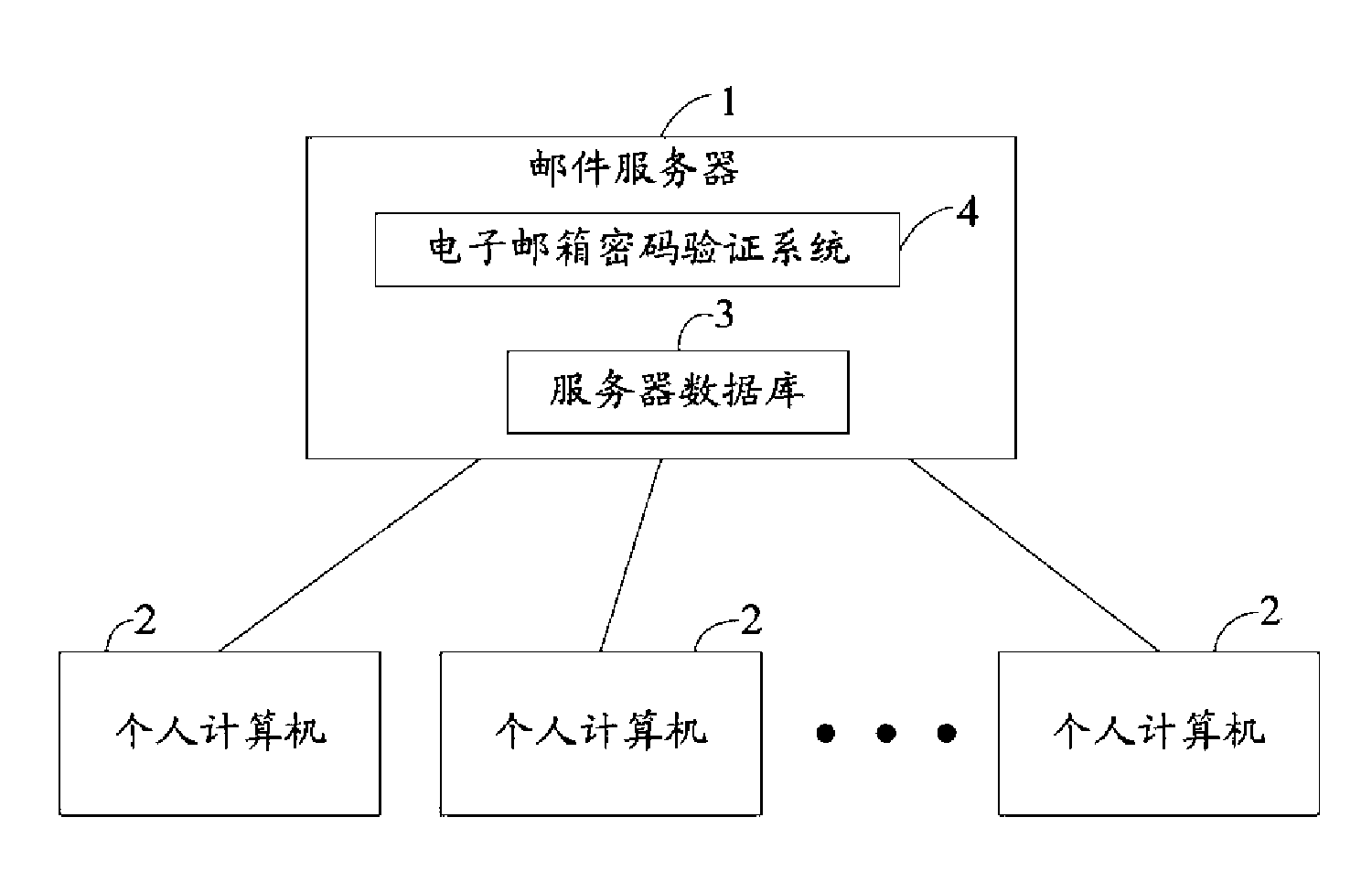
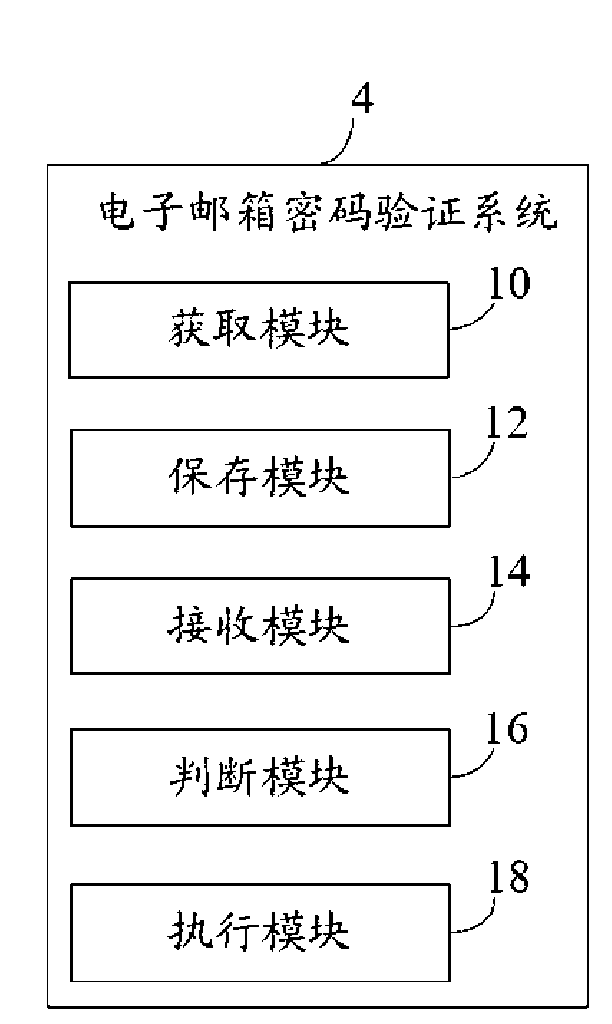
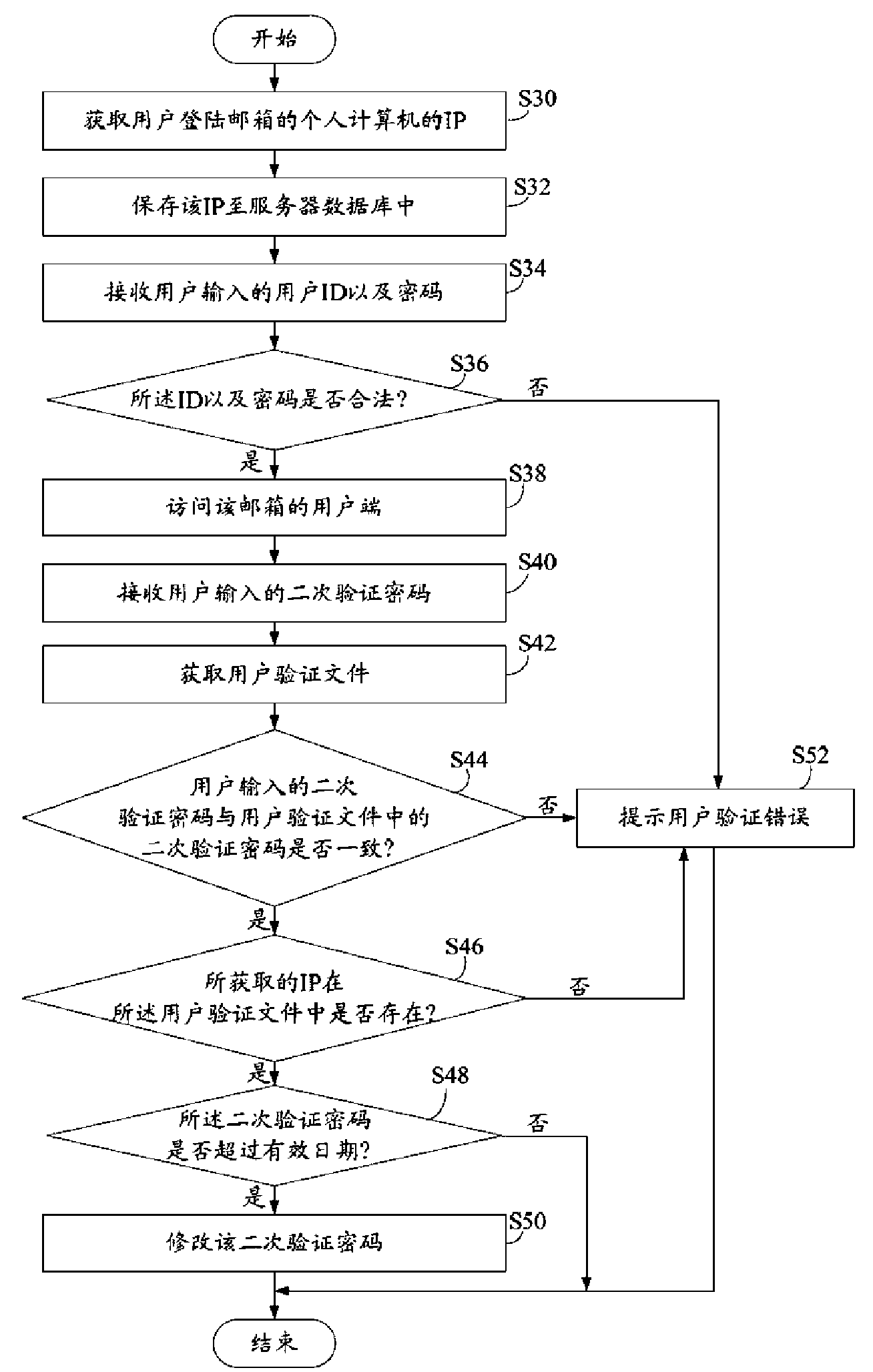
[0011] Such as figure 1 Shown is a hardware architecture diagram of a preferred embodiment of the electronic mailbox password verification system of the present invention. The present invention is applicable to mailboxes controlled by ACL. The email password verification system 4 runs on a mail server 1 connected to a plurality of personal computers 2 . The mail server 1 includes a server database 3, which is used to store the user's mailbox ID and the password corresponding to the ID, the user authentication file and the IPs of the plurality of personal computers 2. The user verification file includes: a secondary verification password. The user verification file can also include: the IP of the personal computer that allows opening the user's email box and the valid date of the secondary verification password. When the email box is a public email box and there are many public users, it is not necessary to set the The IPs of the personal computers that are allowed to open t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More