Method, system and device for realizing WAPI authentication
A technology for authenticating devices and authenticating requests, applied in the field of communications, can solve the problems of increasing the complexity of device processing and deployment, and achieve the effect of simple device processing and simple deployment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
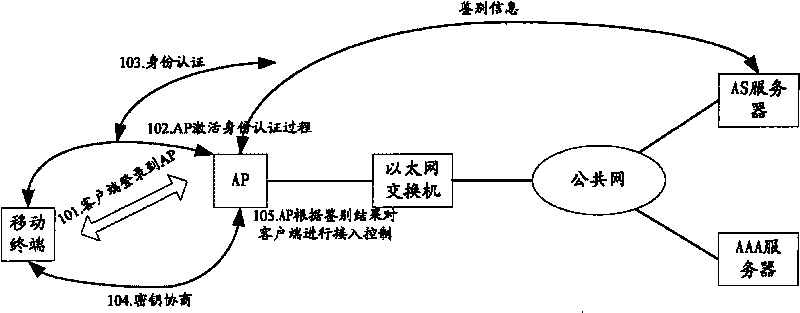
[0050] figure 2 It is a flow chart of a WAPI authentication method in the present invention. The WAPI authentication method is applied to a system including an access point and an authentication server, wherein the access point can be regarded as a kind of authentication device (also can be regarded as a commonly-called authentication client), such as figure 2 shown, including the following steps:
[0051] Step 201, the authentication server receives a WAI authentication request message sent by an access point, the authentication request message carries WAI group information, wherein the WAI authentication request message is encapsulated in a RADIUS message. Wherein, the manner of carrying the WAI group information is: extending the Vendor-Specific attribute of RADIUS, and carrying the WAI group request or response information in the Vendor-Specific attribute.
[0052] The specific implementation method is to add an extended attribute in the RADIUS protocol, which carries ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More