Pointer analysis-combined software security hole dynamic detection method
A pointer analysis and software security technology, applied in the field of information security, can solve the problem of high system resource overhead and achieve the effect of reducing system resource consumption
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0023] The technical solution of the present invention will be described in detail below in conjunction with the accompanying drawings and embodiments.
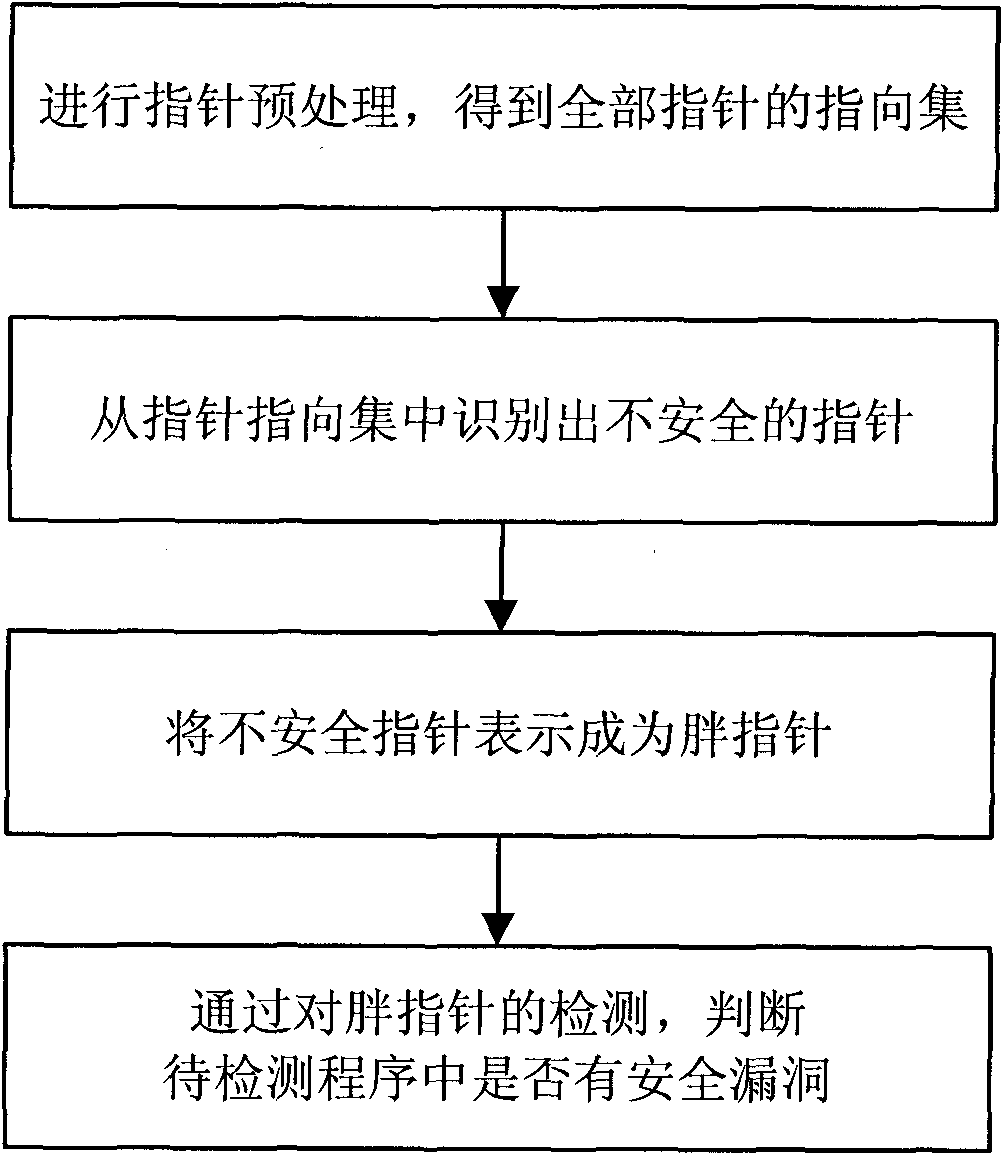
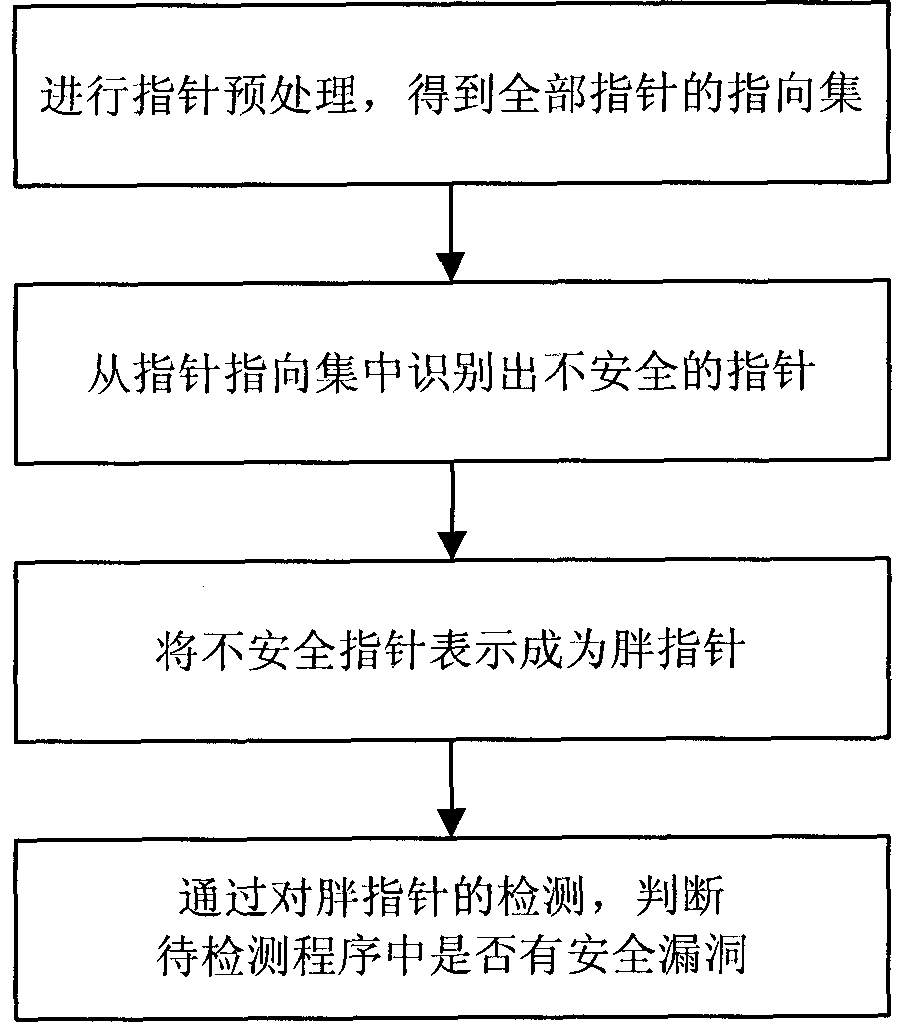
[0024] A schematic flow chart of a dynamic detection method for software security vulnerabilities combined with pointer analysis of the present invention is as follows figure 1 As shown, the specific operation steps are as follows:
[0025] The procedure to be tested is as follows:
[0026] int a[10];
[0027] int*p=a;
[0028] int*q=p;
[0029] *(p+11)=5; / / generate buffer overflow vulnerability
[0030] int i = 10;
[0031] int*r = new(int);
[0032] r=&i;
[0033] delete r; / / If r is not assigned NULL, it may cause a floating pointer error
[0034] *r = 15; / / generate a floating pointer error
[0035] Step 1: Perform pointer preprocessing to obtain pointing sets of all pointers.
[0036] Step 1: Perform pointer preprocessing to obtain the pointing set of all pointers
[0037] Andersen algorithm is adopted, and th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More