Network security situation evaluating method
A security posture and network security technology, applied in the field of network security, can solve problems such as single network security indicators, high requirements for administrator experience, and inaccurate quantitative algorithm results, etc., to achieve the effect of accurate security situation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
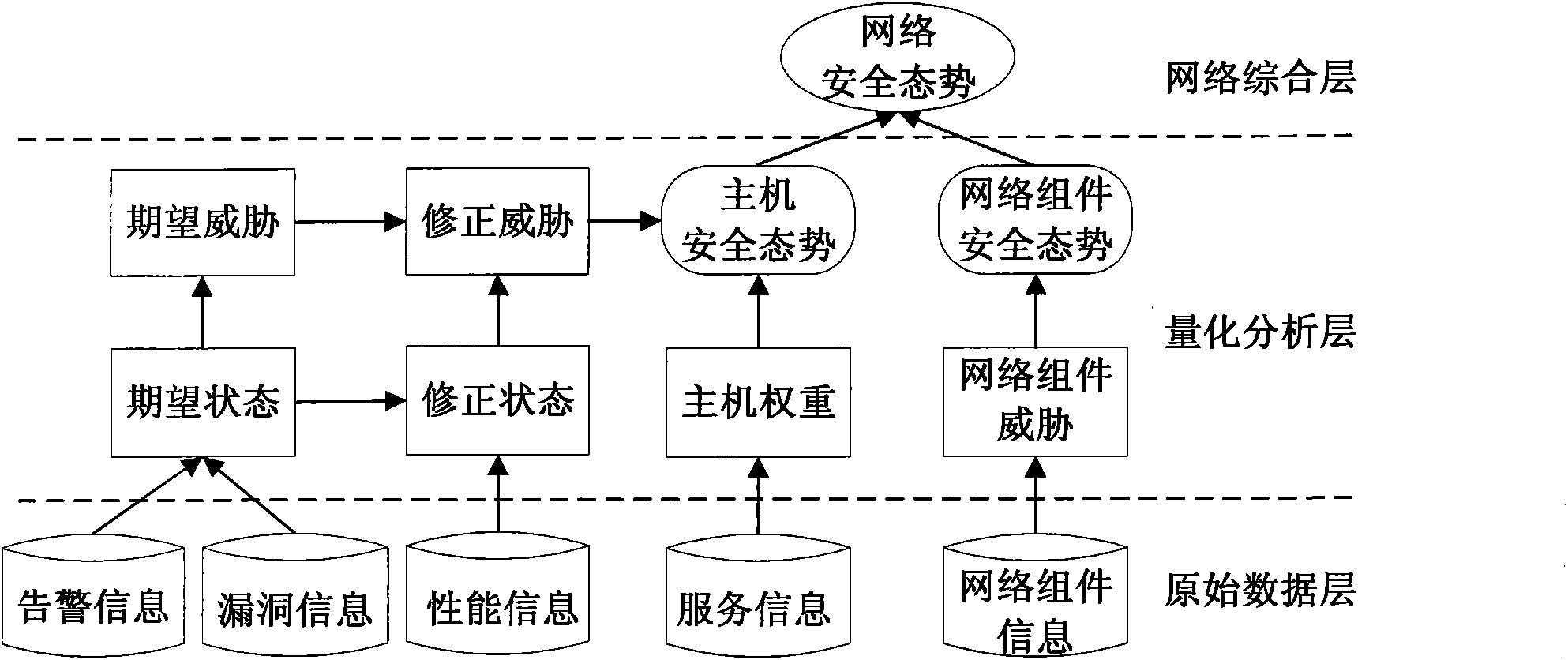
[0028] The input of the invention is alarm information, vulnerability information, host performance information and service information, network component performance information, network topology information and host trust relationship. Input information can come from various devices in any network system, such as hosts, servers, intrusion detection systems, routers, firewalls, and so on. After the data streams on these devices are processed by corresponding preprocessing devices, the extracted information can be used as input information of the present invention. The above information is required to be complete and comprehensive, and the more complete the information, the more accurate the evaluation result. Through the layer-by-layer processing and analysis of the input information, the network security situation assessment results are finally obtained, which are displayed in the network security situation curve diagram.
[0029] The detailed procedure is given below.
[...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More