Method, network switch and network system for authenticating terminals
A network switch and terminal technology, applied in the field of communication, can solve the problems of the terminal being unable to respond, the authentication process takes a long time, and the configuration and maintenance are complicated.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] In order to make the purpose, technical solutions and advantages of the embodiments of the present invention more clear, the embodiments of the present invention will be further described in detail below in conjunction with the accompanying drawings. Here, the exemplary embodiments and descriptions of the present invention are used to explain the present invention, but not to limit the present invention.
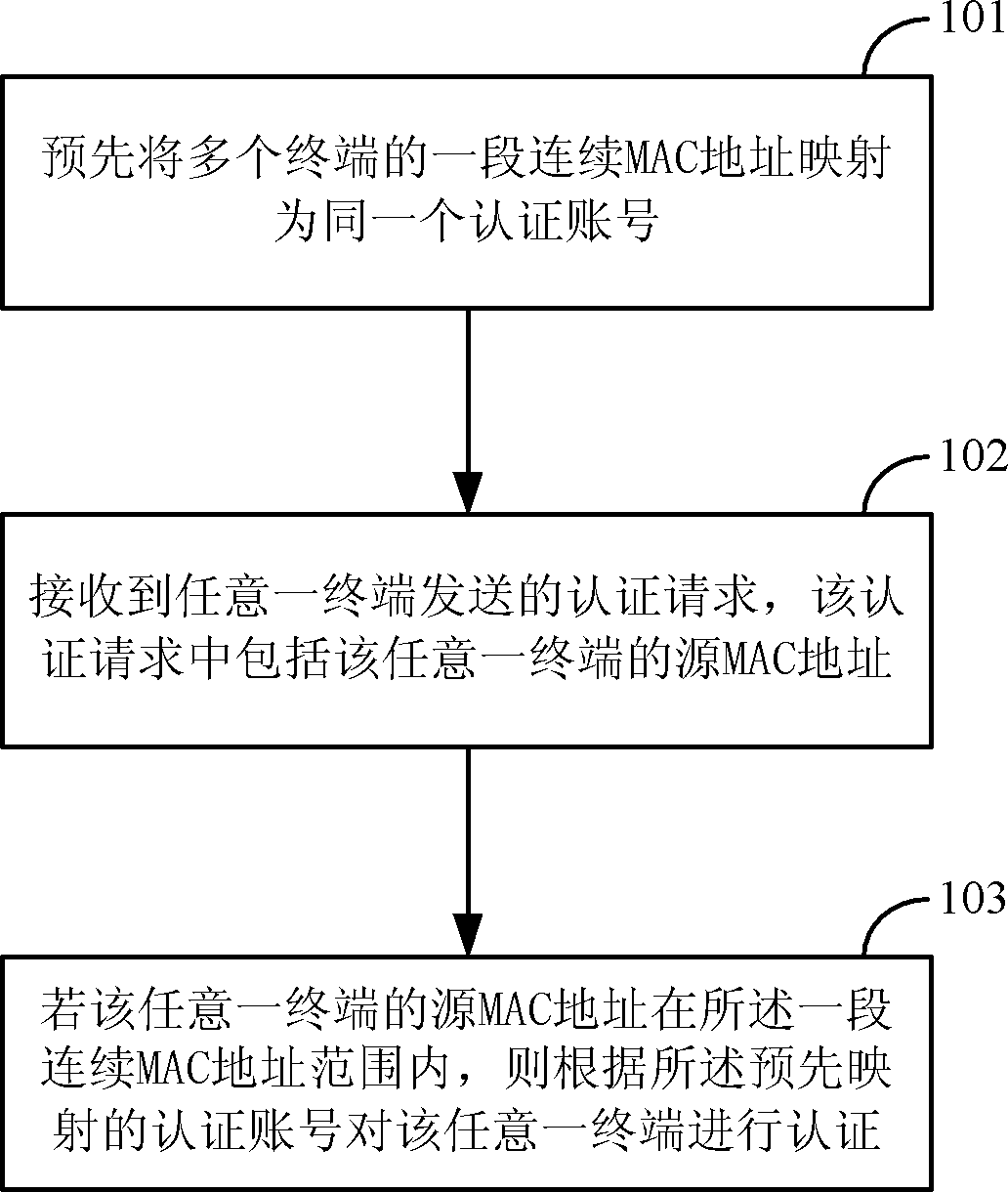
[0027] Such as figure 1 As shown, in the embodiment of the present invention, when performing MAC bypass authentication, the processing flow of the method for authenticating the terminal may include:
[0028] Step 101, pre-map a segment of consecutive MAC addresses of multiple terminals to the same authentication account;
[0029] Step 102: An authentication request sent by any terminal is received, and the authentication request includes the source MAC address of the arbitrary terminal; during specific implementation, the authentication request may be, for example, ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More