Threat detection in a data processing system
A database and statistical information technology, applied in the field of threat detection, can solve problems such as application layer attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
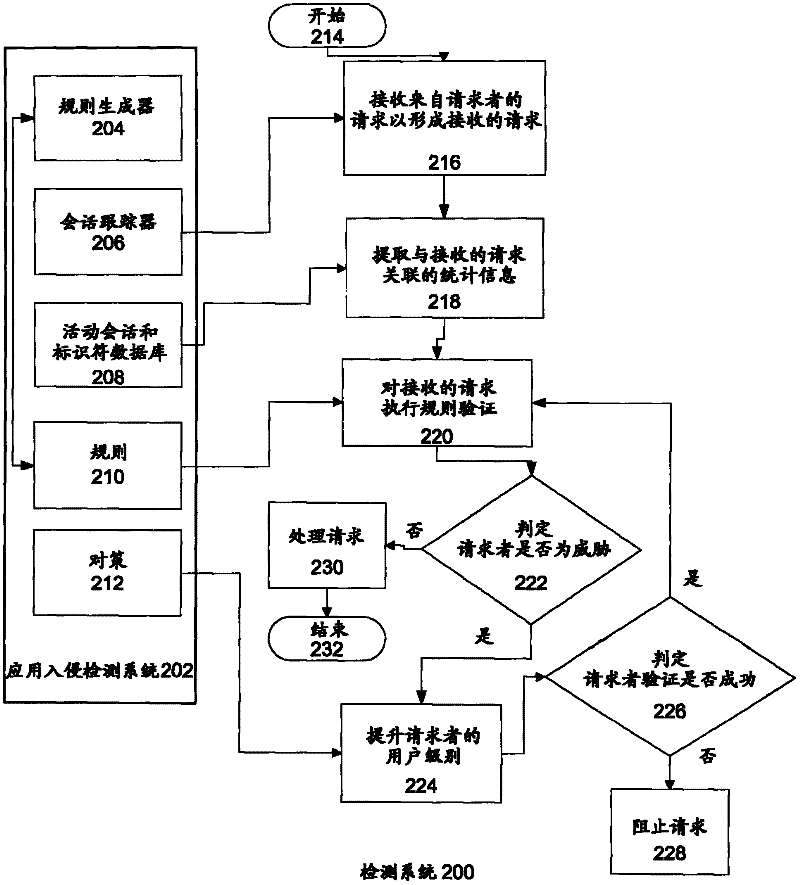
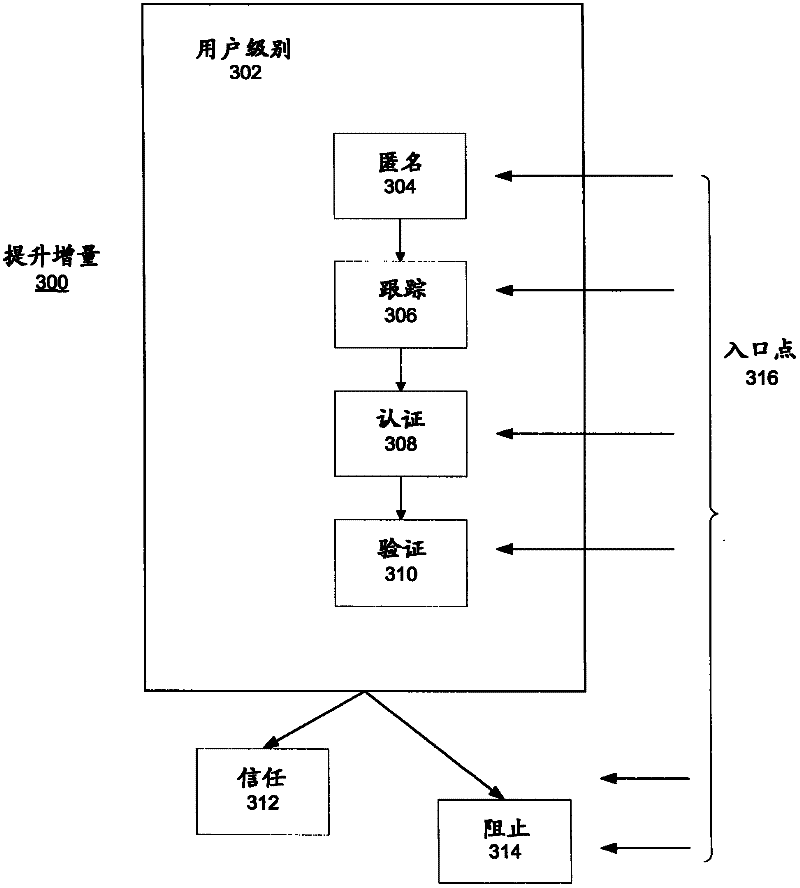
Method used
Image
Examples
Embodiment Construction
[0014] Although an illustrative implementation of one or more embodiments is provided below, the disclosed systems and / or methods can be implemented using any of a variety of techniques. The invention is in no way limited to the illustrative implementations, drawings and techniques presented below, including the exemplary designs and implementations shown and described herein, but may be modified within the full scope of the appended claims and their equivalents.
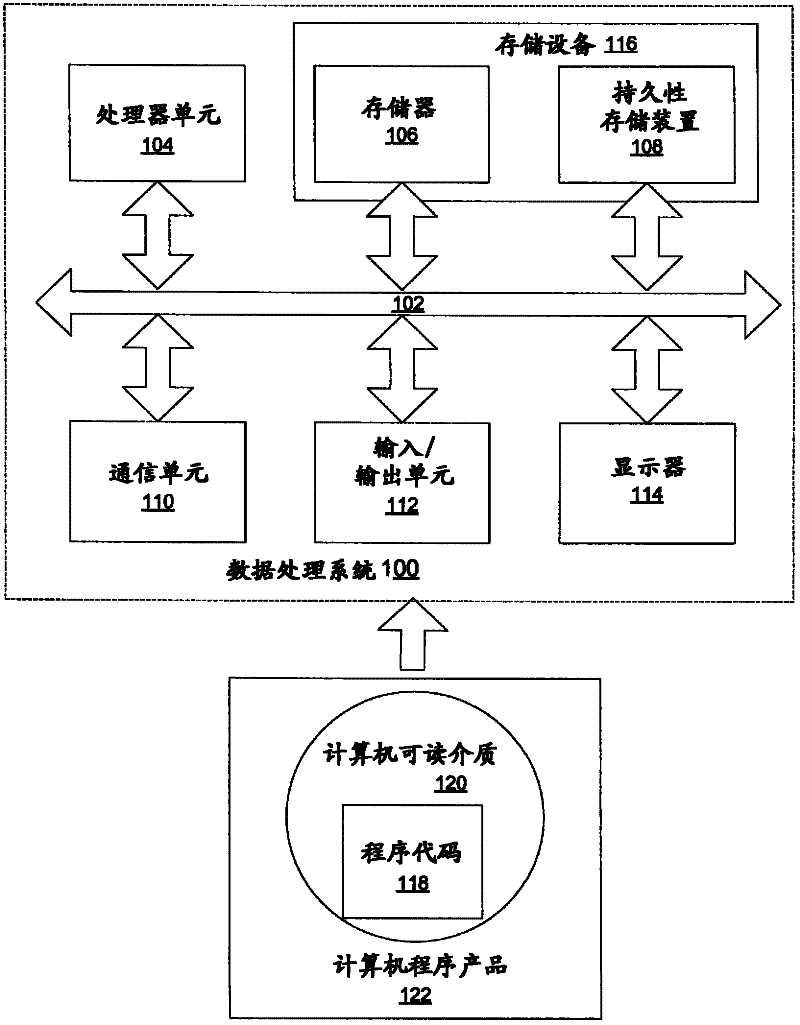
[0015] Those skilled in the art will understand that the present invention can be implemented as a system, method or computer program product. Accordingly, the present invention can take the form of an entirely hardware embodiment, an entirely software embodiment (including firmware, resident software, microcode, etc.), or an embodiment combining software and hardware aspects, all of which are generally referred to herein as " circuit", "module" or "system". Furthermore, the present invention may take the form of a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More