Implementation method and system for SM3 algorithm in JAVA environment
A technology for implementing methods and algorithms, which is applied in the field of cryptography and information security, and can solve problems such as programming interfaces calling SM3 algorithms, and achieve the effect of avoiding cumbersome procedures
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0019] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
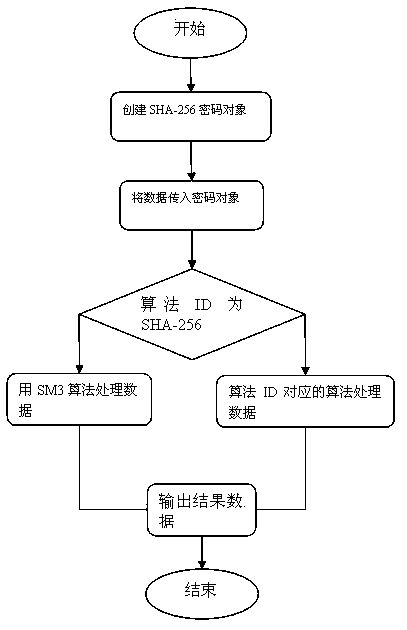
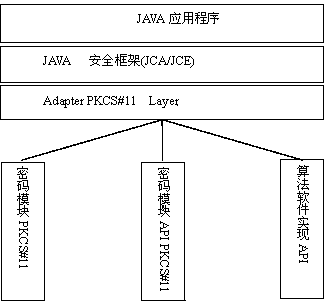
[0020] Such as figure 1 The flow chart of the implementation method of the shown SM3 algorithm in the JAVA environment. The invention discloses a method for implementing the SM3 algorithm in the JAVA environment, which specifically includes the following steps: developing and implementing an adaptation layer for algorithm replacement in accordance with the PKCS#11 specification; in the JAVA environment, when the application program passes the encryption framework JCA standard When the programming interface calls the secure hash algorithm SHA-256 algorithm in the password extension JCE, th...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More