Credible extraction method for digital evidence of Android
An extraction method and digital evidence technology, applied in the usage of multiple keys/algorithms, telephone communication, electrical components, etc., can solve problems such as illegal data acquisition, and achieve the effect of ensuring originality and non-repudiation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
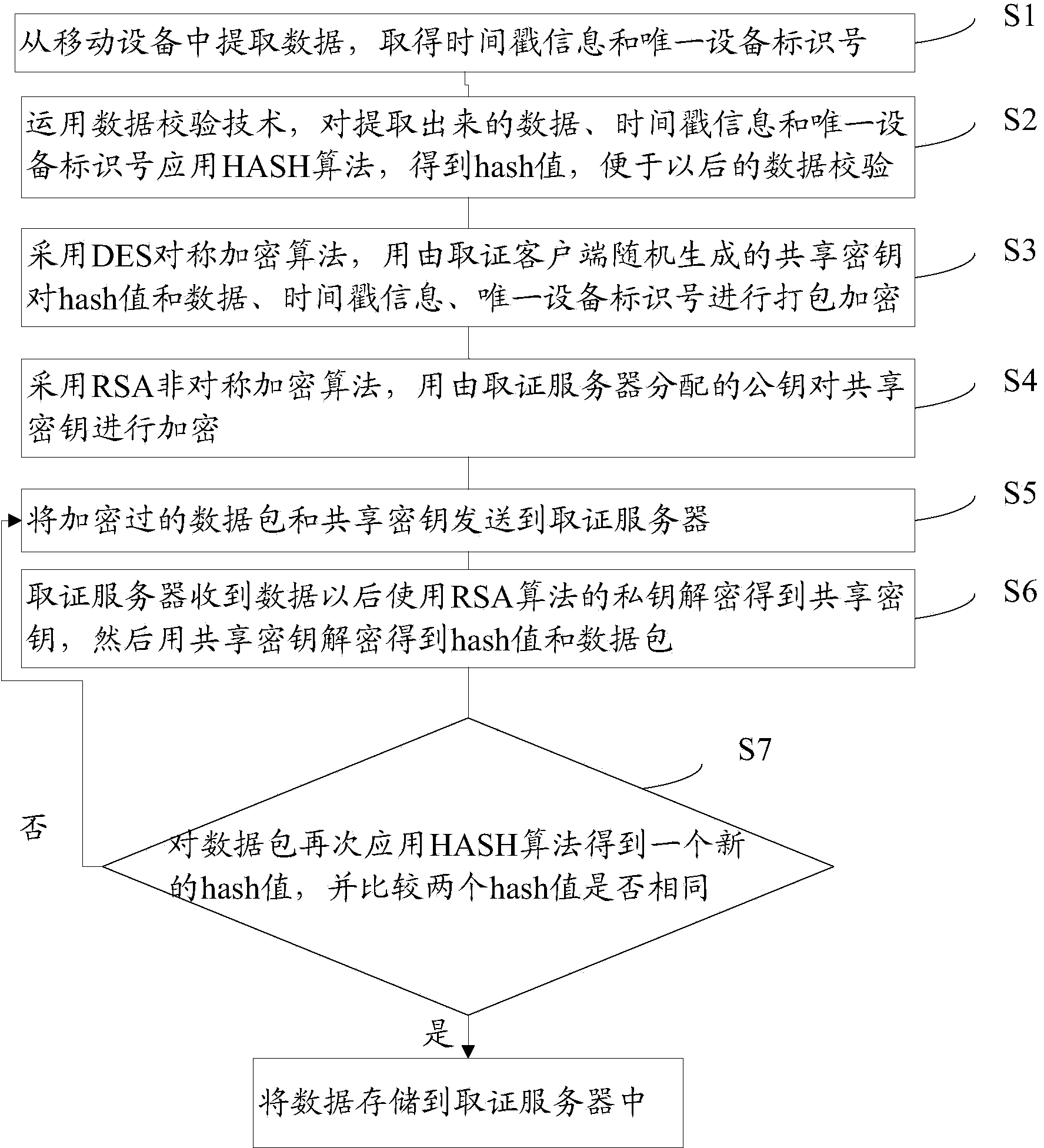
[0022] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and examples. However, the examples given are not intended to limit the present invention.
[0023] like figure 1 As shown, the present invention provides a schematic flow diagram of a credible extraction method for Android-oriented digital evidence, including:
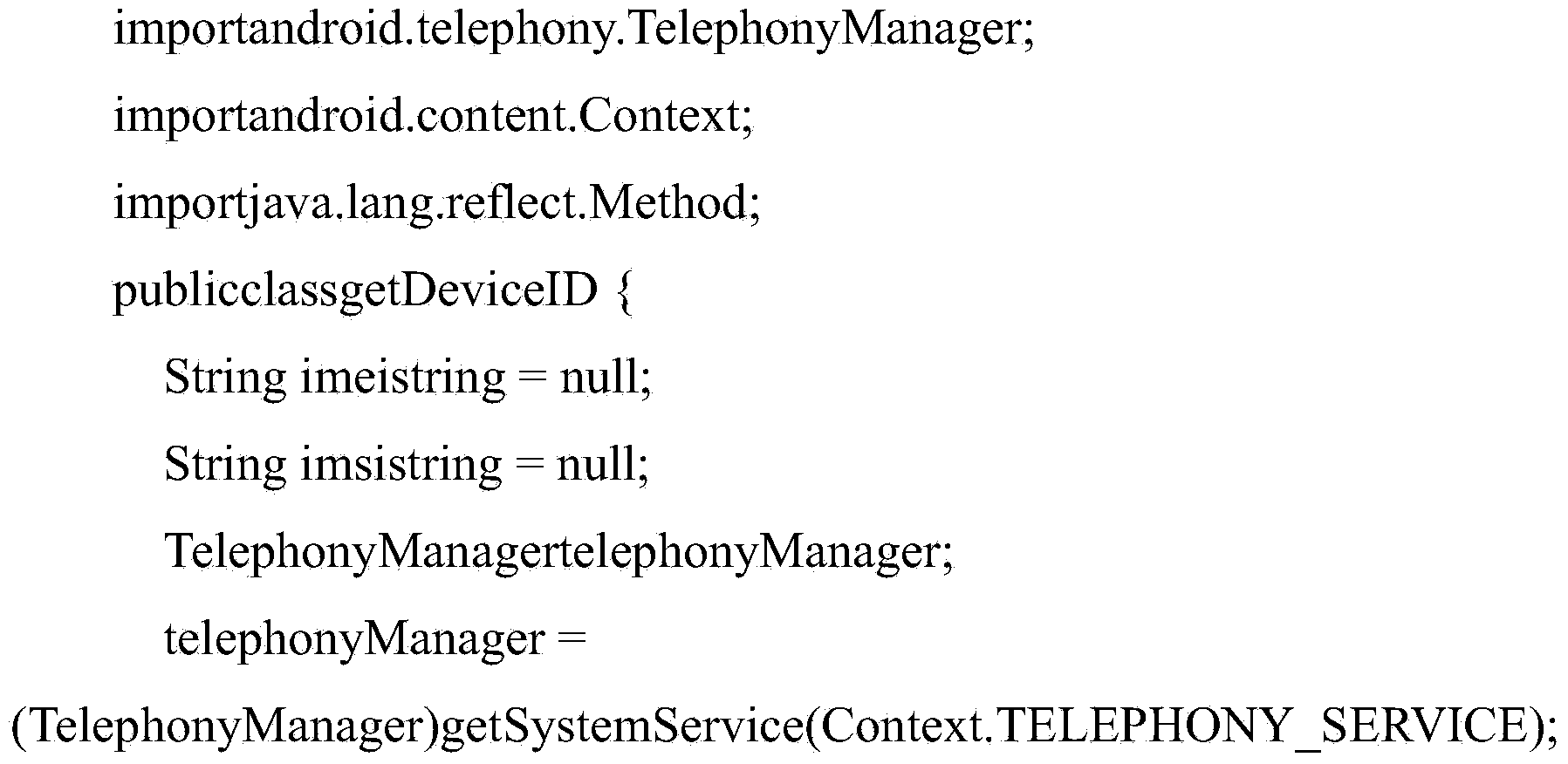
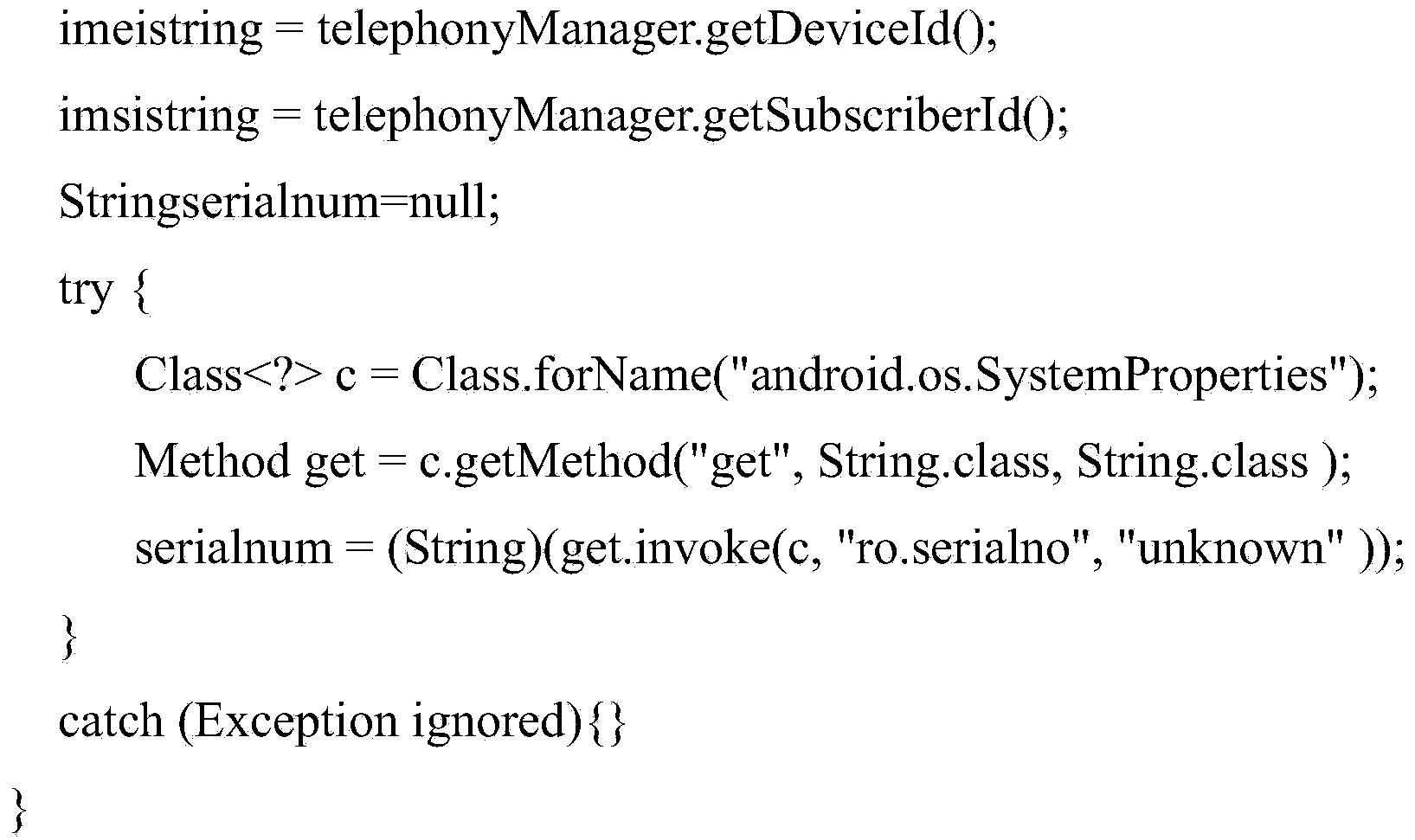
[0024] Step S1, extracting data from the mobile device, obtaining time stamp information and a unique device identification number;
[0025] Step S2, using data verification technology, applying HASH algorithm to the extracted data, time stamp information and unique device identification number to obtain a hash value, which is convenient for future data verification;
[0026] Step S3, using the DES symmetric encryption algorithm, using the shared key randomly generated by the forensics client to package an...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More