Patents
Literature
572 results about "Evidence collection" patented technology
Efficacy Topic
Property
Owner
Technical Advancement
Application Domain
Technology Topic
Technology Field Word
Patent Country/Region
Patent Type
Patent Status
Application Year
Inventor
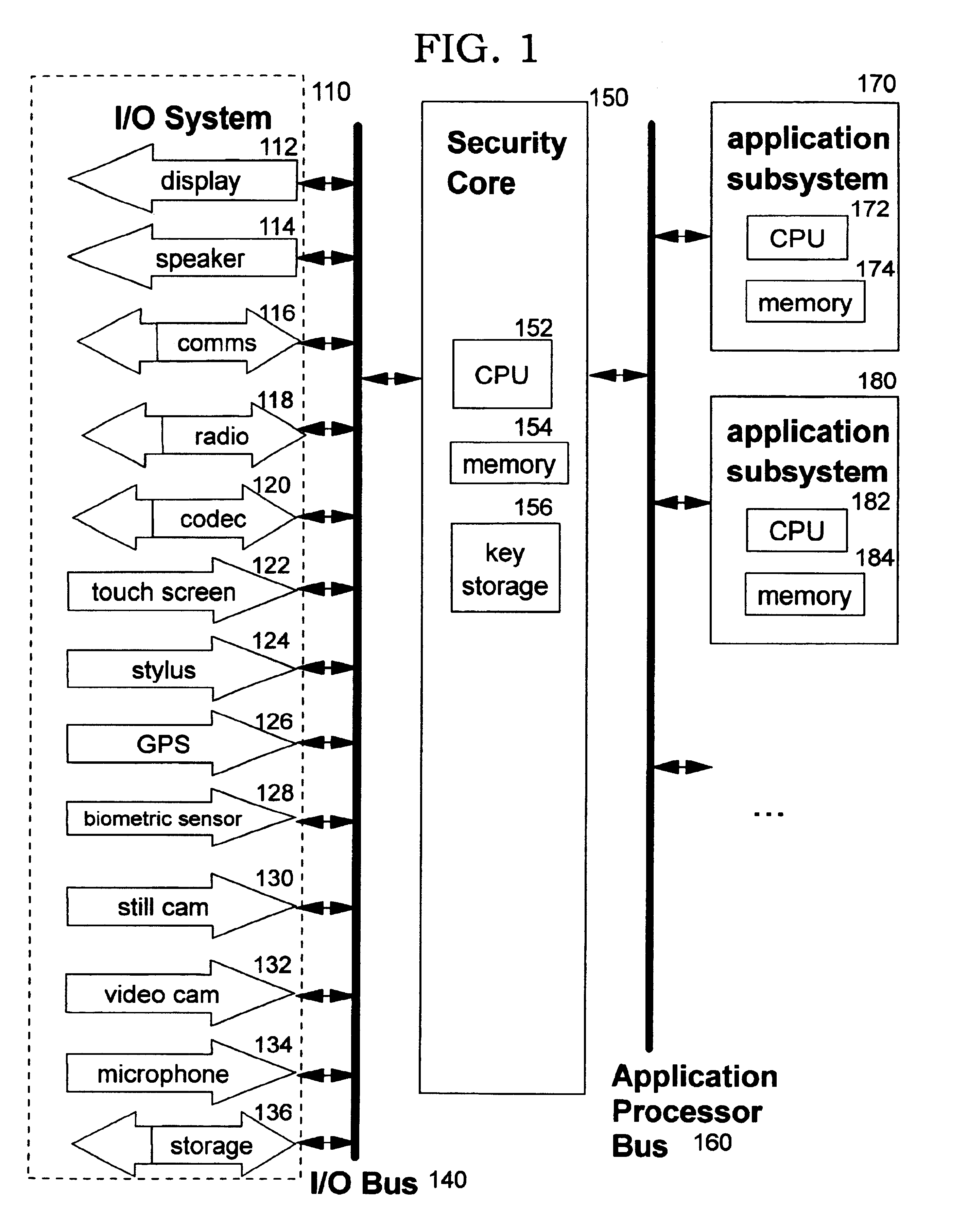
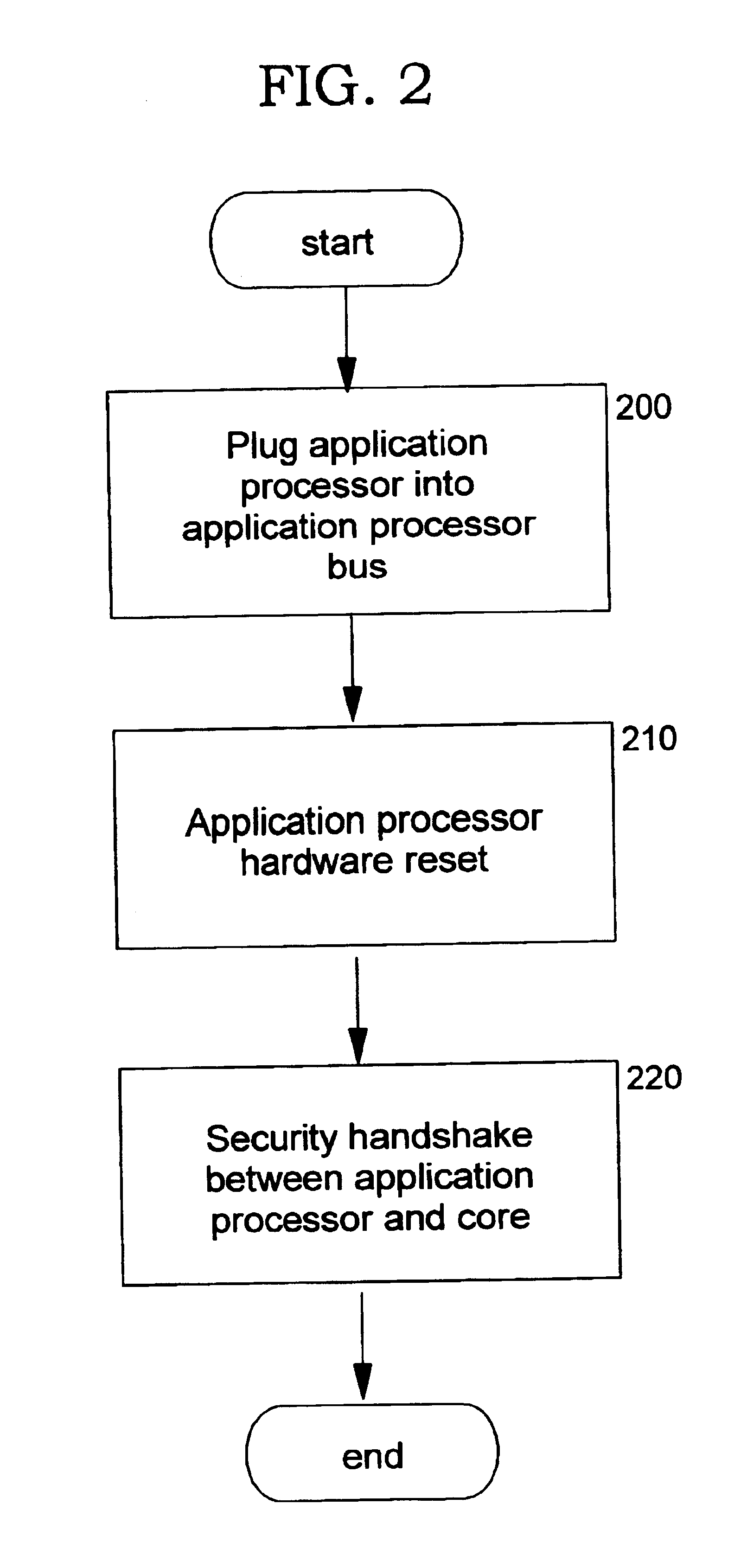
Technique for establishing provable chain of evidence
InactiveUS20020095601A1IntegrityMemory loss protectionError detection/correctionData streamDigital signature
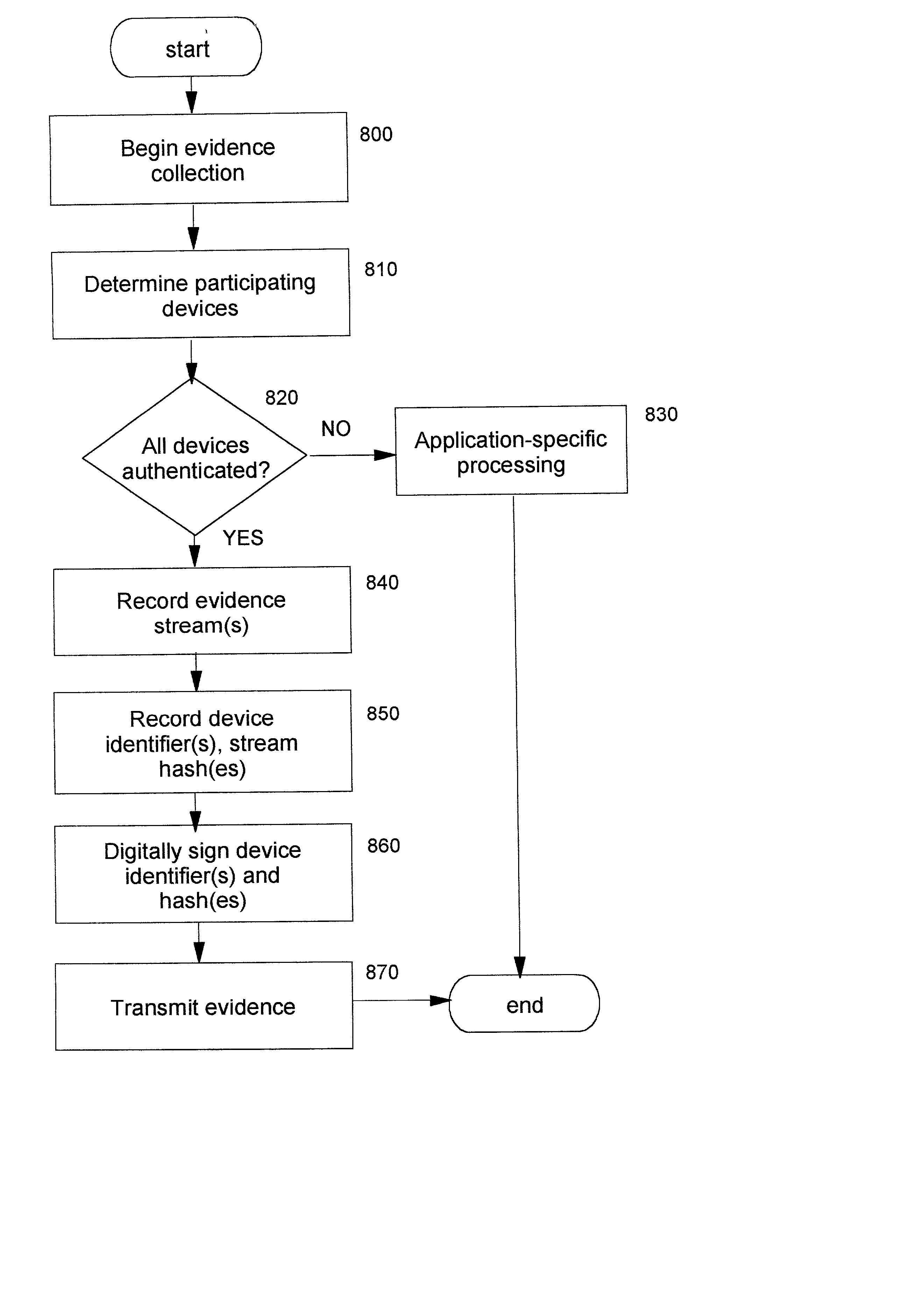
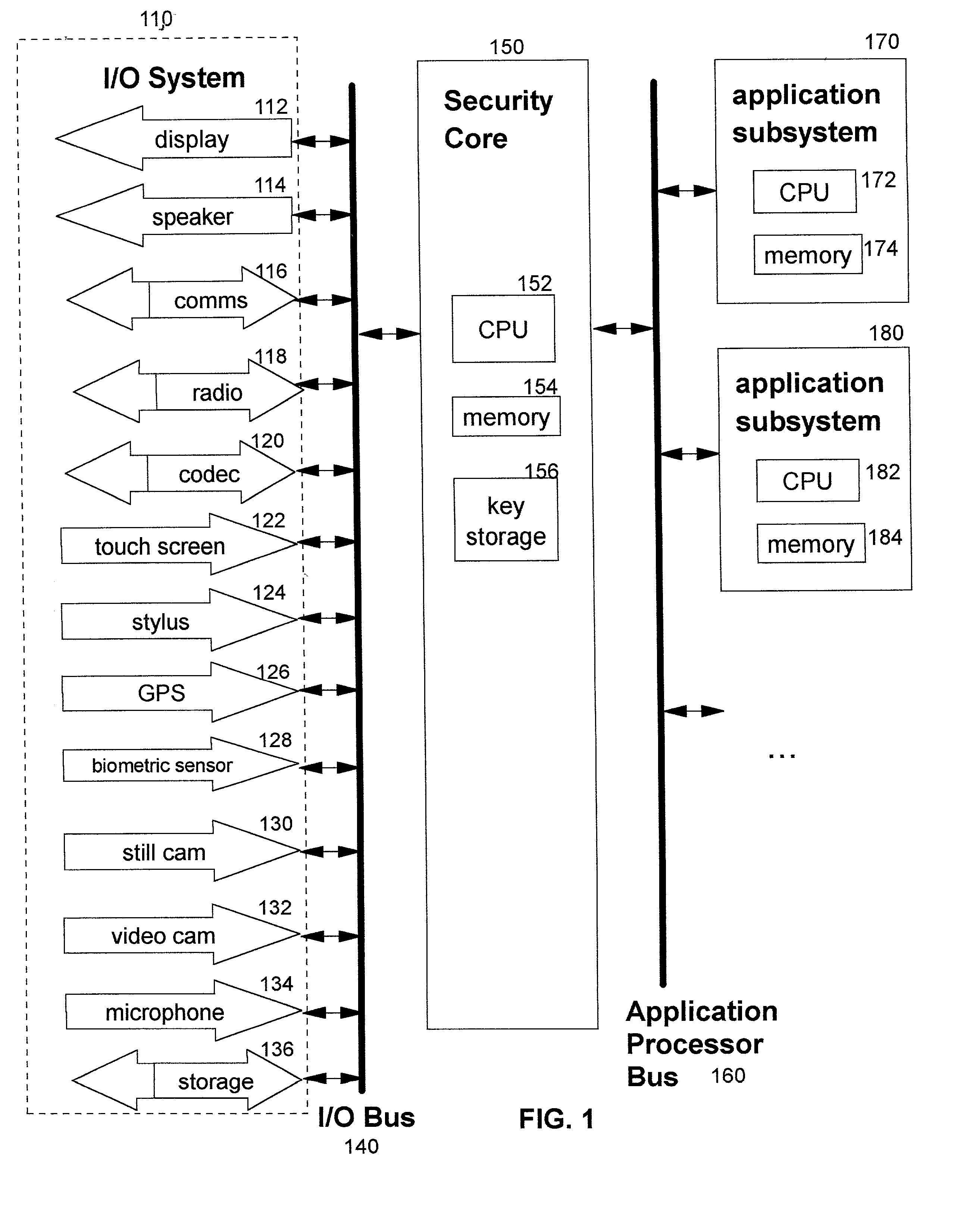
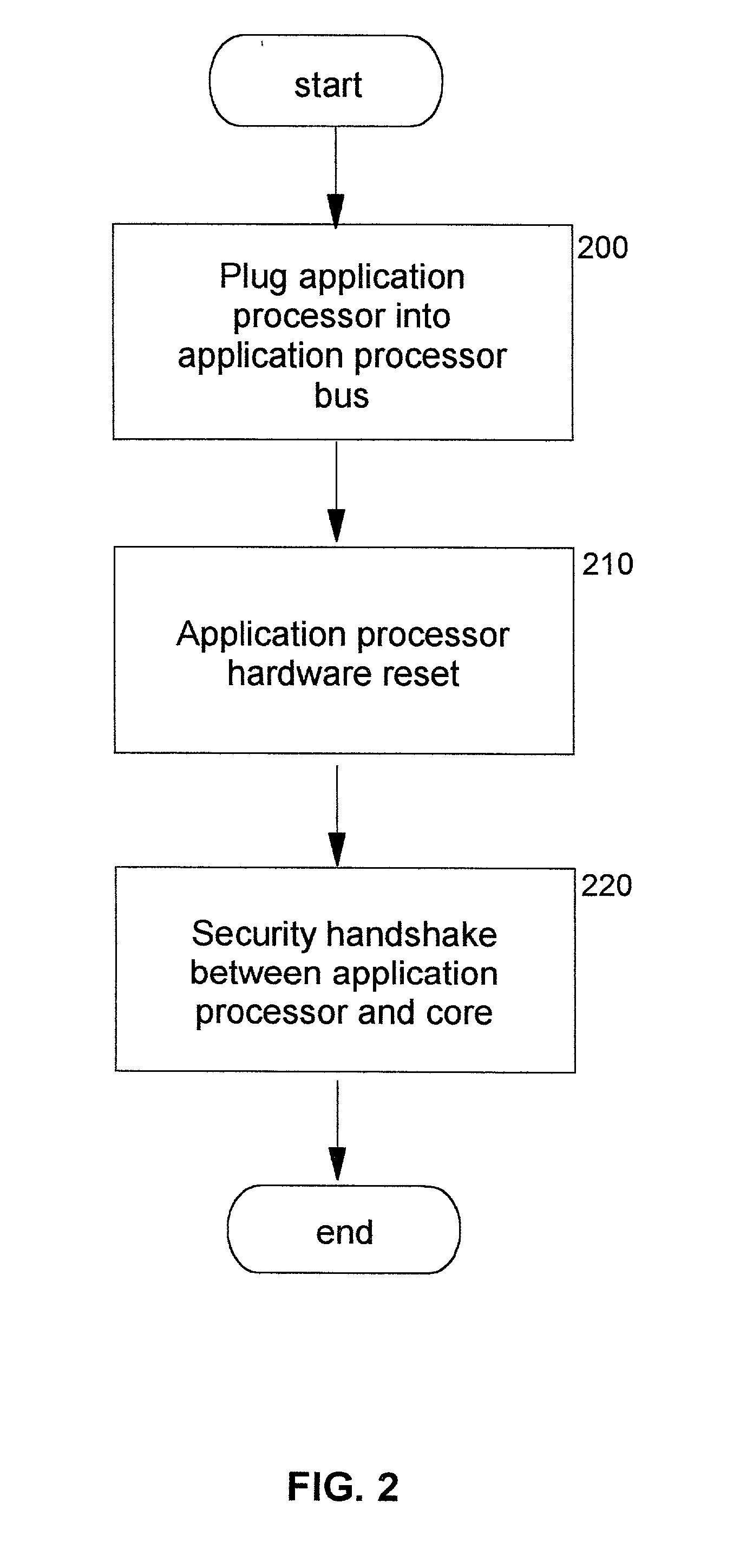
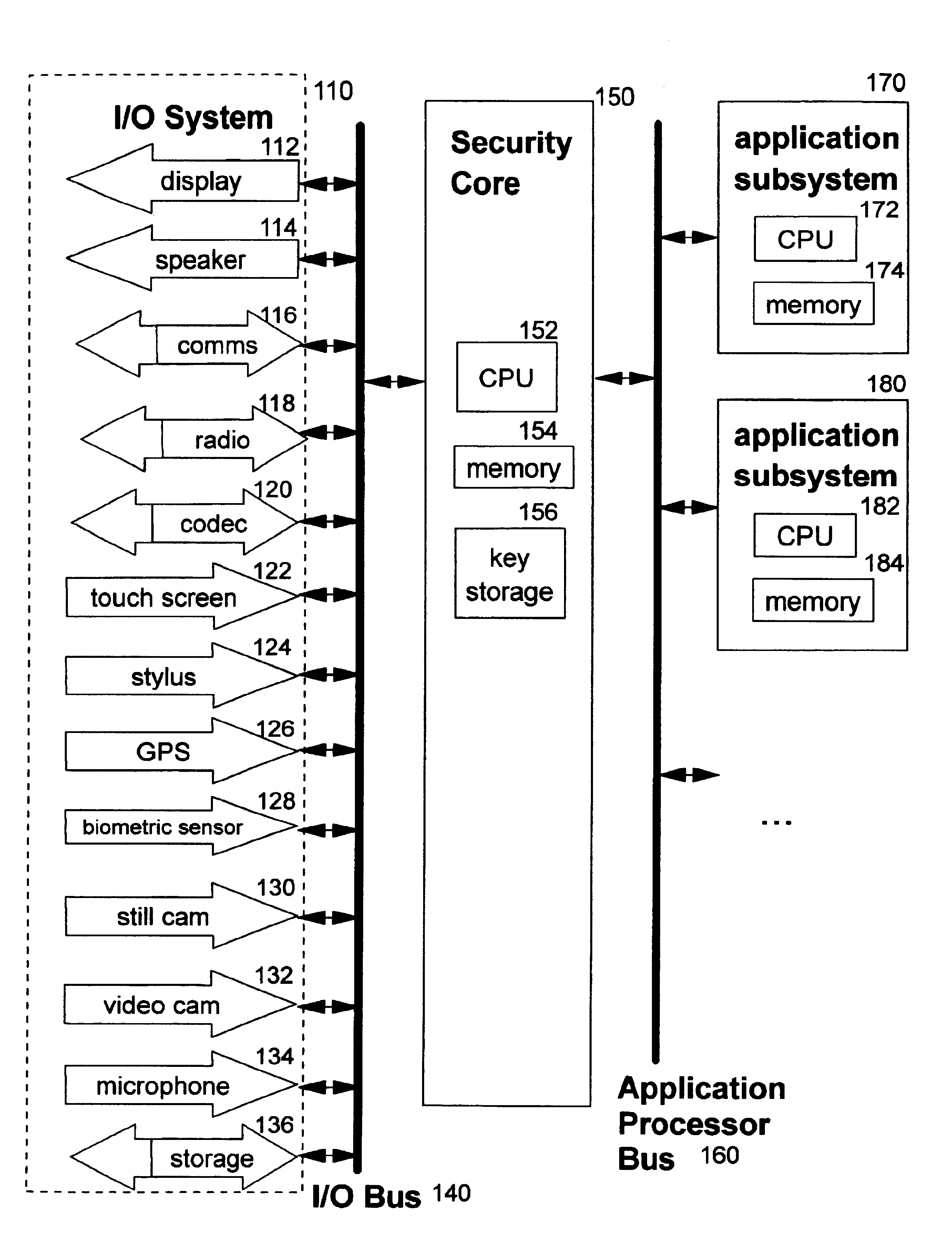
A method, system, computer program product, and method of doing business by providing a provable chain of evidence for data stream(s) created by one or more components (such as input / output devices and application processing components). Components that create the evidence collection are authenticated. A unique identifier of each such component is included within cryptographically-protected information that is added to the evidence collection. A digital signature is preferably used for the cryptographic protection, thereby digitally notarizing the evidence collection. The authenticity and integrity of the evidence collection can be verified. In preferred embodiments, the authenticated identities of components providing the evidence can also be determined from the cryptographically-protected information. One or more data streams may be included within the evidence collection to establish information such as the date and time the evidence collection was captured, the geographic location where the capture was performed, an identification of a person performing the evidence capture, and so forth. When present in a provable chain of evidence, these types of additional evidence are provided by authenticated components which are identified within the cryptographically-protected information.
Owner:IBM CORP
Technique for establishing provable chain of evidence
InactiveUS6948066B2IntegrityMemory loss protectionError detection/correctionData streamDigital signature
A method, system, computer program product, and method of doing business by providing a provable chain of evidence for data stream(s) created by one or more components (such as input / output devices and application processing components). Components that create the evidence collection are authenticated. A unique identifier of each such component is included within cryptographically-protected information that is added to the evidence collection. A digital signature is preferably used for the cryptographic protection, thereby digitally notarizing the evidence collection. The authenticity and integrity of the evidence collection can be verified. In preferred embodiments, the authenticated identities of components providing the evidence can also be determined from the cryptographically-protected information. One or more data streams may be included within the evidence collection to establish information such as the date and time the evidence collection was captured, the geographic location where the capture was performed, an identification of a person performing the evidence capture, and so forth. When present in a provable chain of evidence, these types of additional evidence are provided by authenticated components which are identified within the cryptographically-protected information.
Owner:IBM CORP
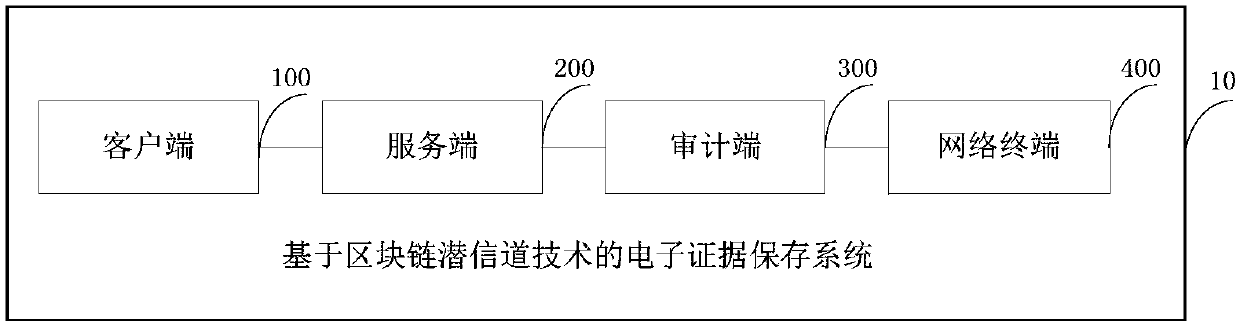
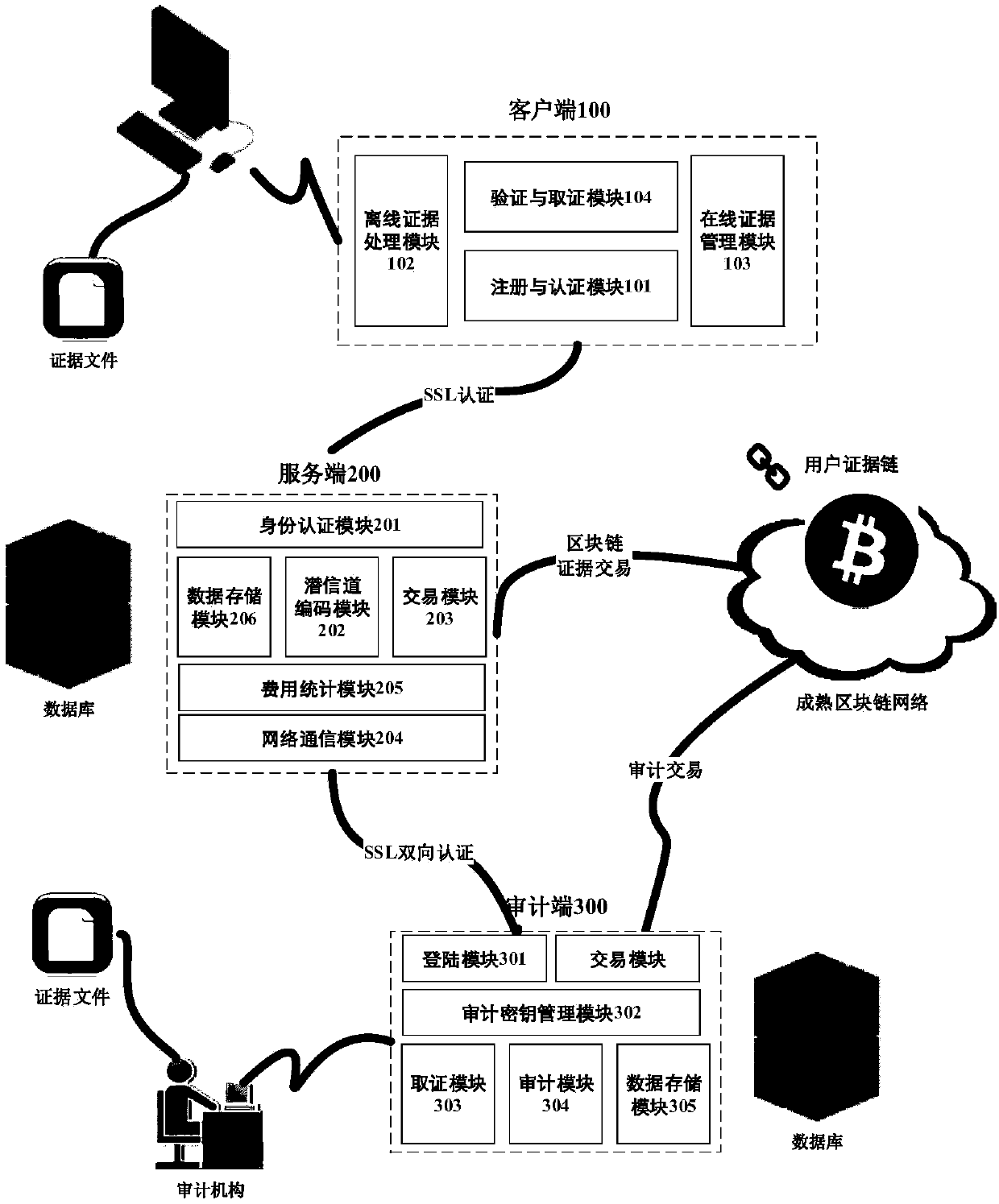
Electronic evidence preservation system based on block chain subliminal channel technology
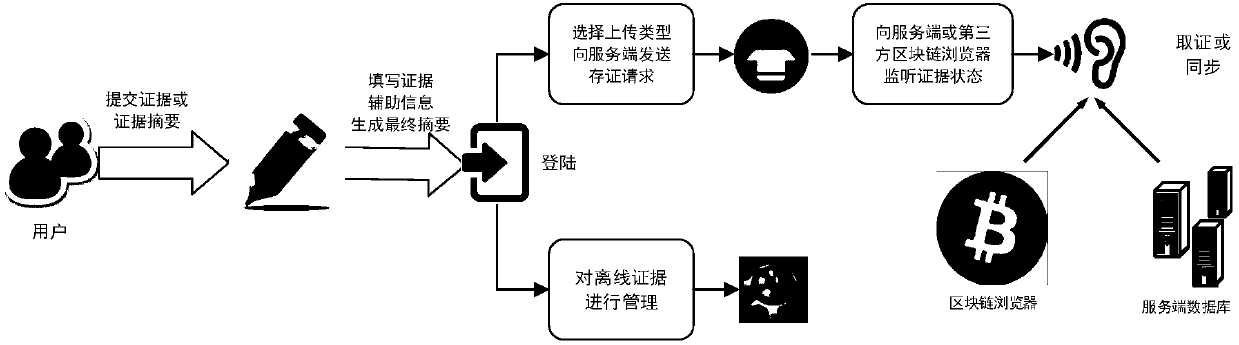
ActiveCN107682308AAchieving processing powerAchieving covert storageDigital data protectionTransmissionNetwork terminationSubliminal channel
The invention discloses an electronic evidence preservation system based on a block chain subliminal channel technology, which comprises a client, a server, an auditing terminal and a network terminal, and is characterized in that the client is used for performing off-line acquisition and processing, online management and evidence collection on a user electronic evidence; the server generates an existence proof for the evidence and performs hosting and recovery on the chain evidence according to a user address; the auditing terminal is used for auditing the chain evidence, generating a corresponding transaction on a block chain and constructing an auditing proof so as to main the integrity, the timeliness and the non-repudiation of an auditing result; and the network terminal is used for performing state synchronization and real-time evidence collection on the user evidence on the chain. The system can dig a cryptographic basis of the subliminal channel preserved electronic evidence and the auditing result thereof in a mature block chain system, thereby realizing safe processing and hidden preservation for the electronic evidence, thus improving the safety and timeliness of electronic evidence preservation, and effectively reducing the preservation cost.
Owner:HANGZHOU INNOVATION RES INST OF BEIJING UNIV OF AERONAUTICS & ASTRONAUTICS
Blockchain-based electronic evidence storing method and system and blockchain-based electronic evidence verifying method and system
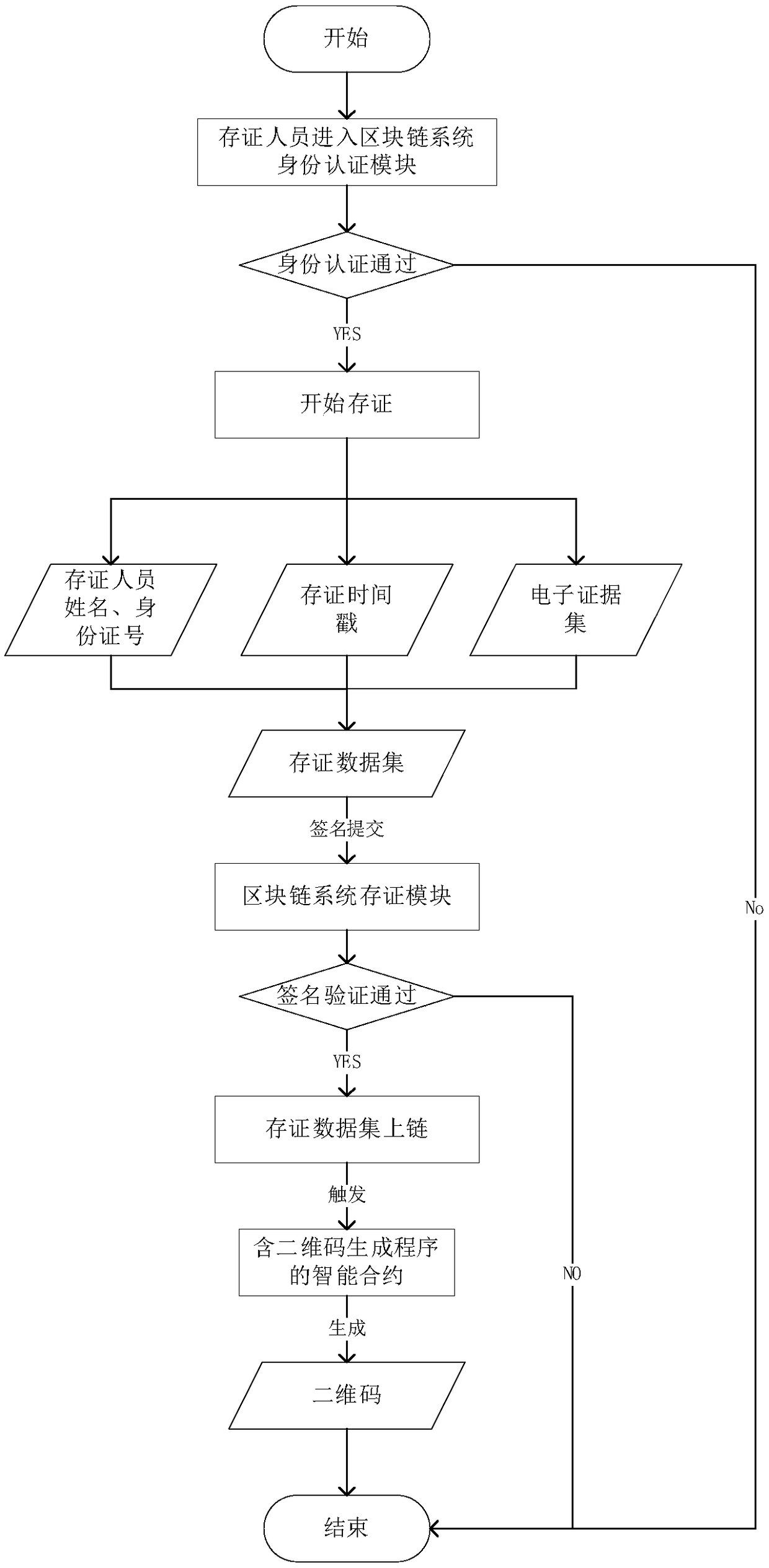
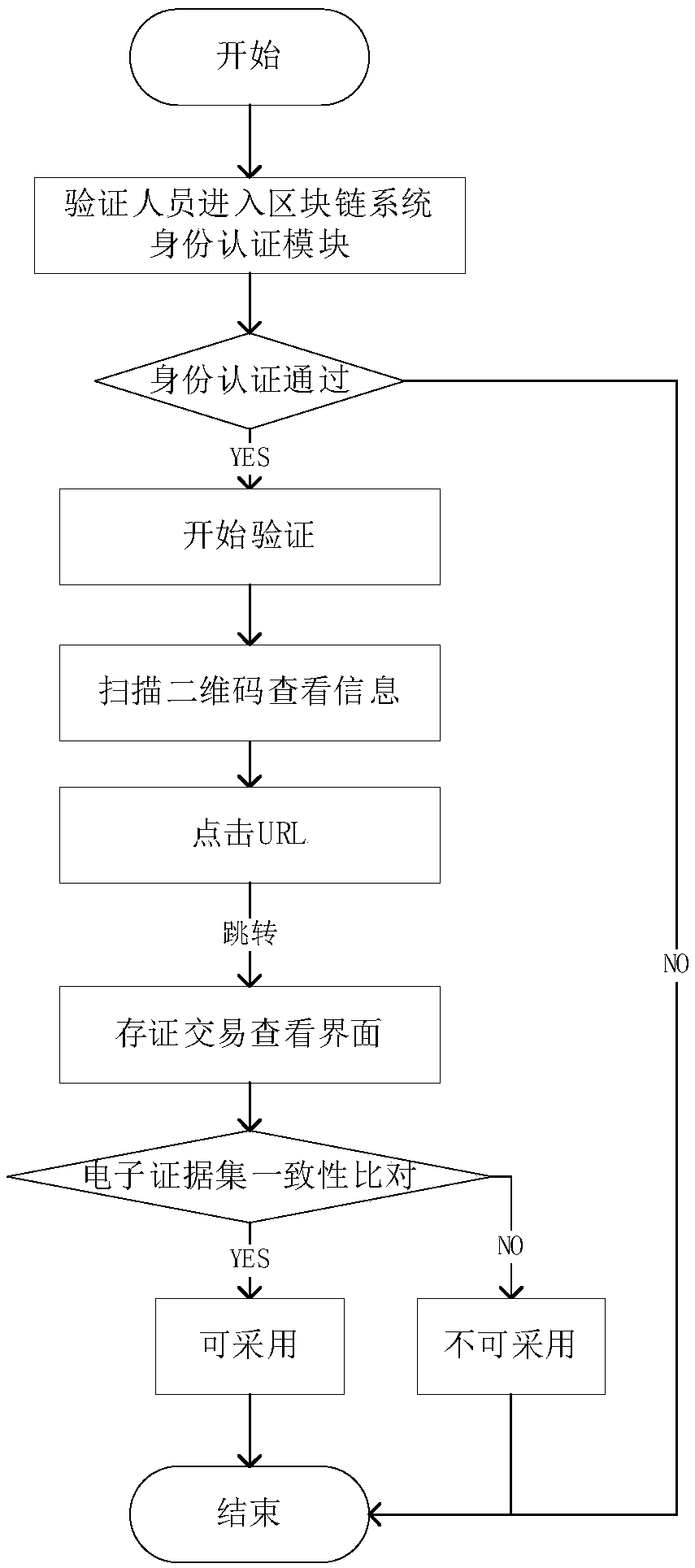
InactiveCN108717431AEnhancing AdoptabilityGuaranteed legalityDigital data protectionSpecial data processing applicationsTamper resistanceData set
The invention relates to a blockchain-based electronic evidence storing method and system and a blockchain-based electronic evidence verifying method and system. The electronic evidence storing methodcomprises the steps of after an evidence storing person passes the identity authentication, forming an evidence storing data set according to an electronic evidence set formed by evidence collection,the identity information of the evidence storing person and an evidence storing time stamp; signing the evidence storing data set and submitting to a blockchain system by the evidence storing person;and generating a two-dimensional code through a smart contract, wherein the two-dimensional code comprises the certificate data set, the signature of the evidence storing person, the relevant information of an evidence storing transaction in a blockchain and a URL (Uniform Resource Locator) address pointing to the evidence storing transaction. The electronic evidence verifying method comprises the steps of after an evidence verifying person passes the identity authentication, scanning the two-dimensional code to view the relevant information; clicking on the URL to view the evidence storing transaction; and carrying out the consistency comparison of the electronic evidence set. The methods disclosed by the invention have the beneficial effects that the supporting information is added intothe electronic evidence set and the applicability of the electronic evidence is guaranteed; the storing of the electronic evidence set is carried out through the blockchain system and the tamper resistance of the electronic evidence is guaranteed; and the legality and the non-repudiation of the operators are guaranteed through the signature verification of the evidence storing person and the evidence verifying person.
Owner:INST OF SOFTWARE - CHINESE ACAD OF SCI
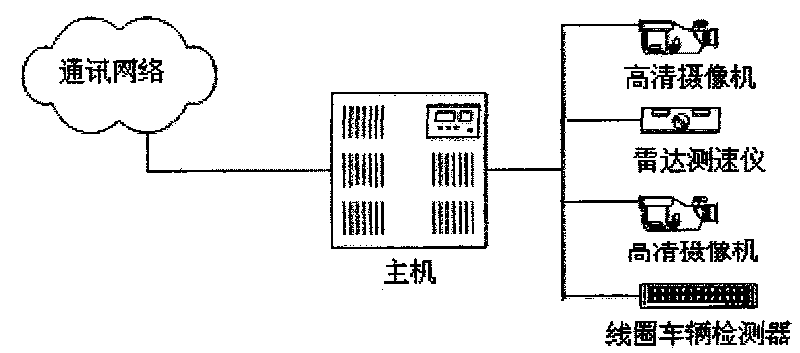
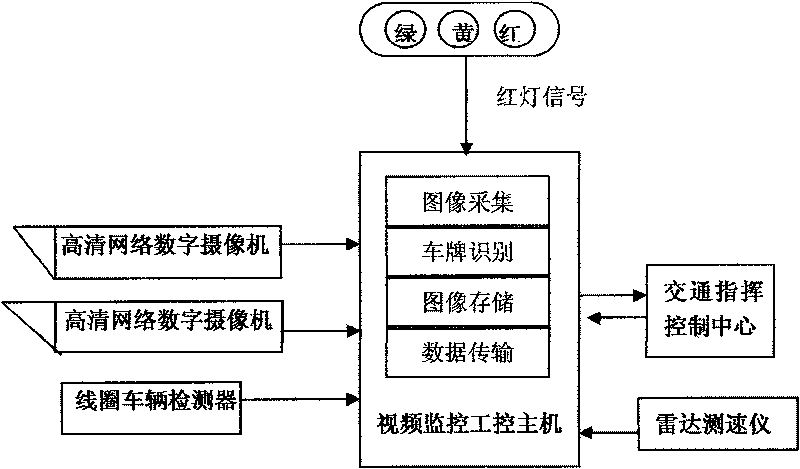
Comprehensive video monitoring system of intelligent traffic
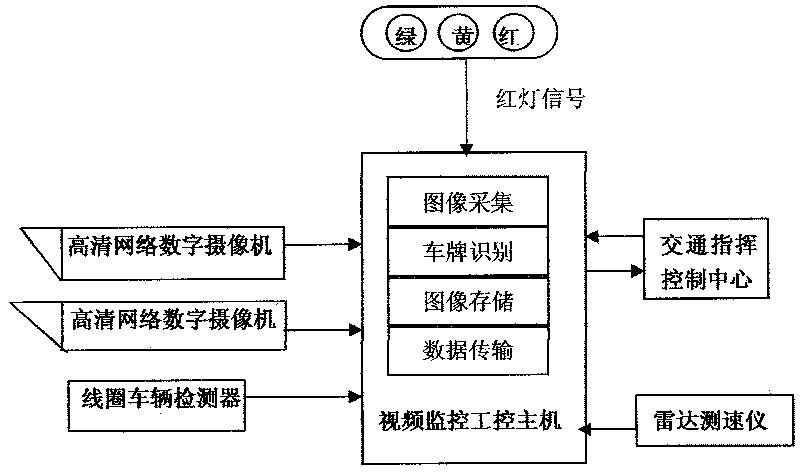
ActiveCN101692310AImprove anti-interference abilityLow costDetection of traffic movementClosed circuit television systemsLicense numberEmbedded technology
The invention provides a comprehensive video monitoring system of intelligent traffic, belonging to the field of intelligent traffic and electronic police. The monitoring system comprises at least one high-definition digital web camera, a video-monitoring industrial control host, a loop vehicle detector and / or a radar device and a high-definition intelligent traffic behavior monitoring unit. The intelligent system is capable of integrating various intelligent traffic monitoring behaviors as a whole, that is, fulfilling the functions of multilane illegal activity monitoring, license number recognition and traffic data acquisition on a single machine at the same time, and conducting detection, analysis and evidence collection on various illegal activities by using the Linux-based embedded technology in combination with the watchdog technology and the network management function. The monitoring system based on the invention has the advantages of high stability, low mistaking and missing rate and high anti-interference capacity, and the monitoring system can effectively filter the interference caused by bicycles, passersby and light; and the monitoring system has flexible, customized monitoring modes, thereby meeting the monitoring requirements under complex environment.
Owner:DERUISHI BEIJING TECH DEV
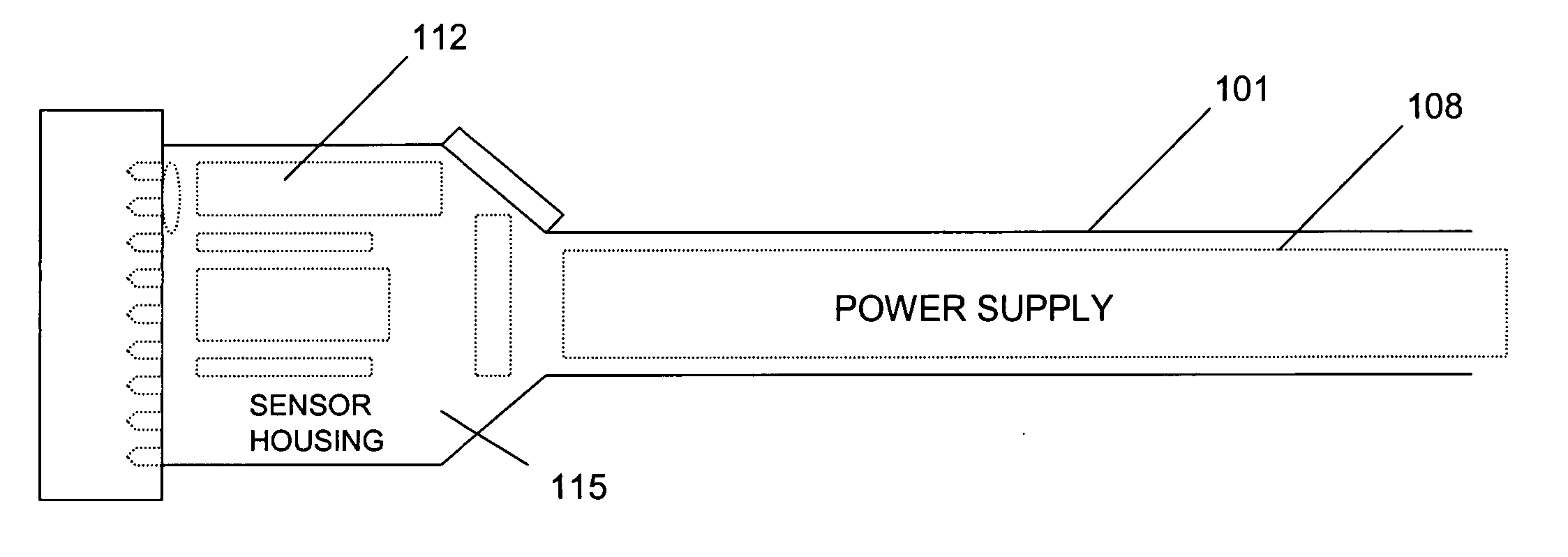
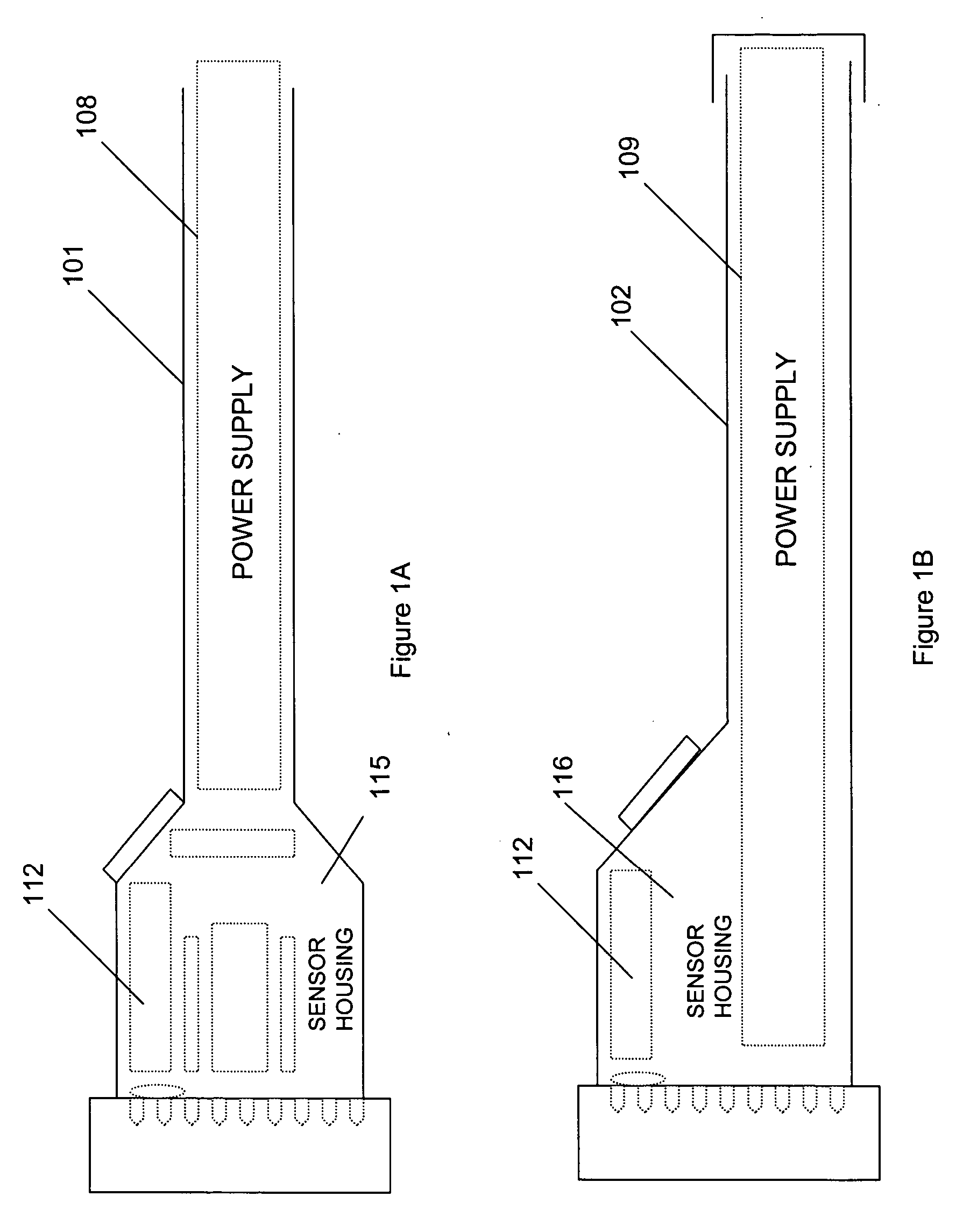
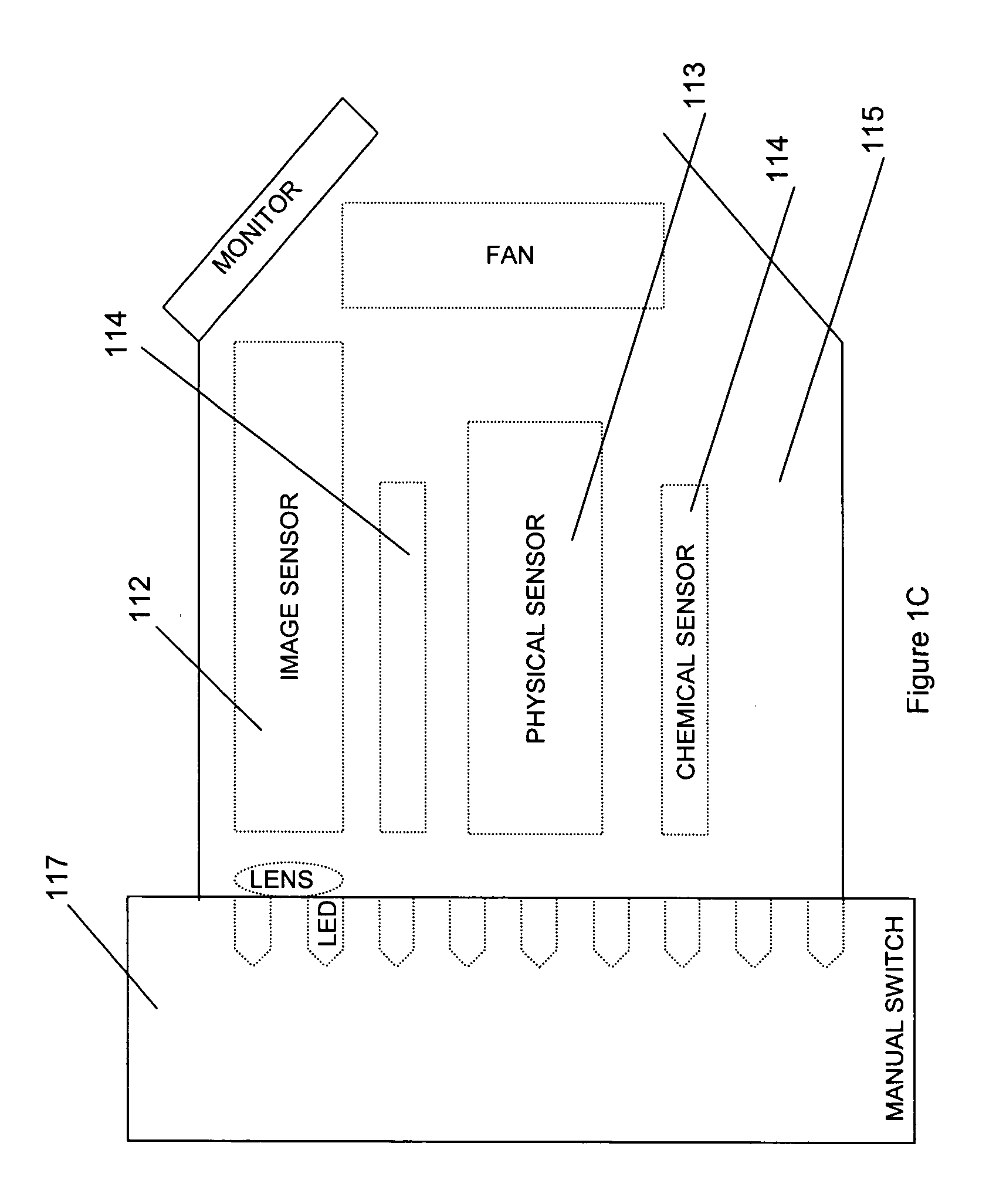
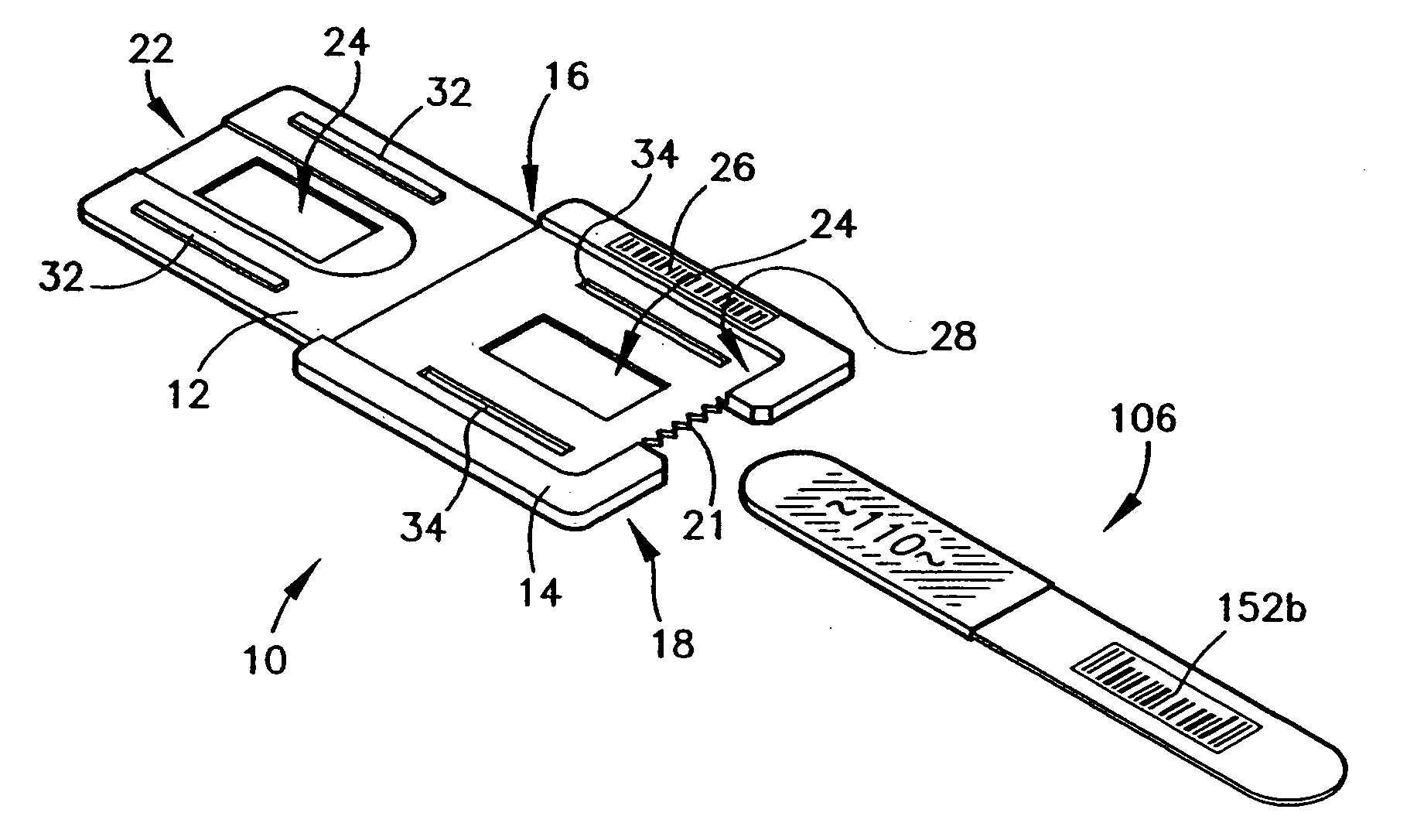
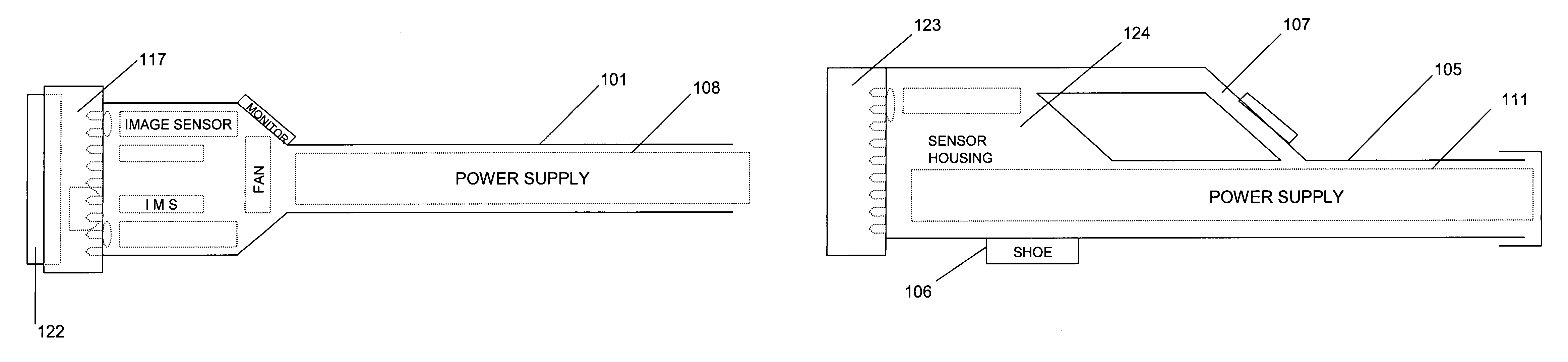
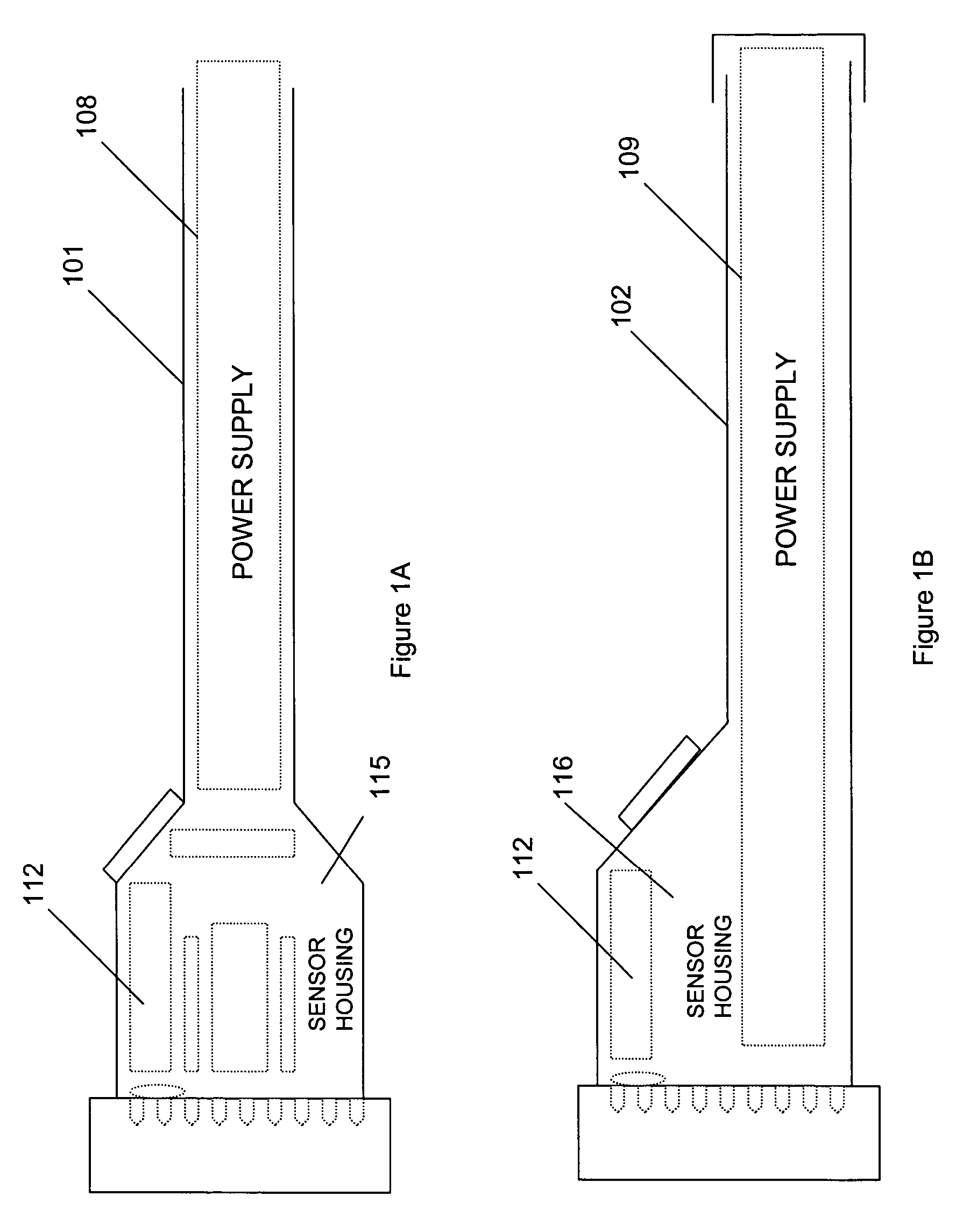
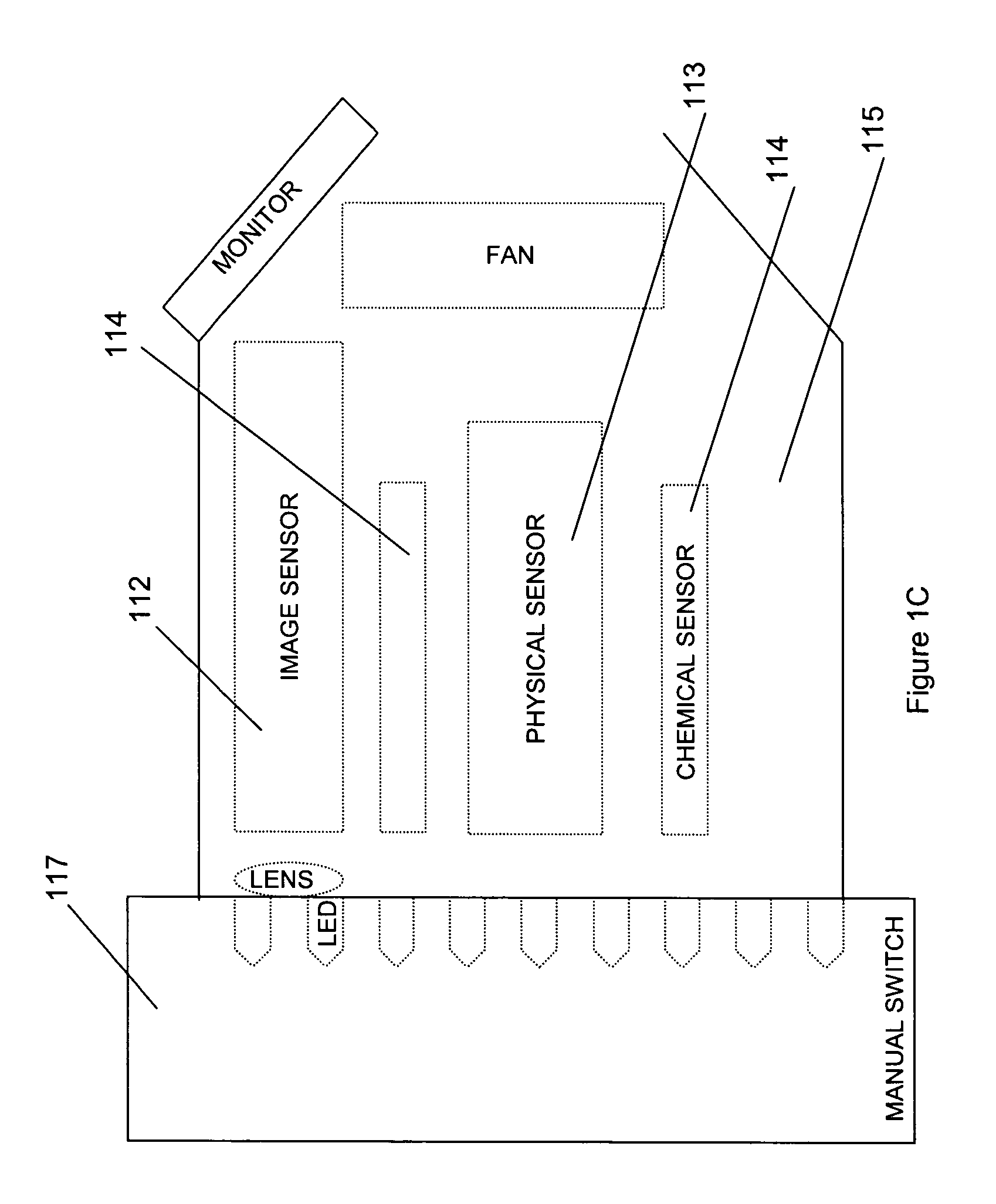
FlashCam - a flashlight camera method and apparatus for a multipurpose flashlight
InactiveUS20070098391A1Ease and convenienceSpeed up the processPrintersPoint-like light sourceEffect lightHand held
An improved method and apparatus for hand-held portable illumination, sensing and evidence collection is described. A uniquely configured multi-functional device selectively provides multi-purpose lighting and sensing in a hand-held portable device which is usable as a flashlight, camera and as an integrated device for evidence collection.
Owner:LYNK3 TECH
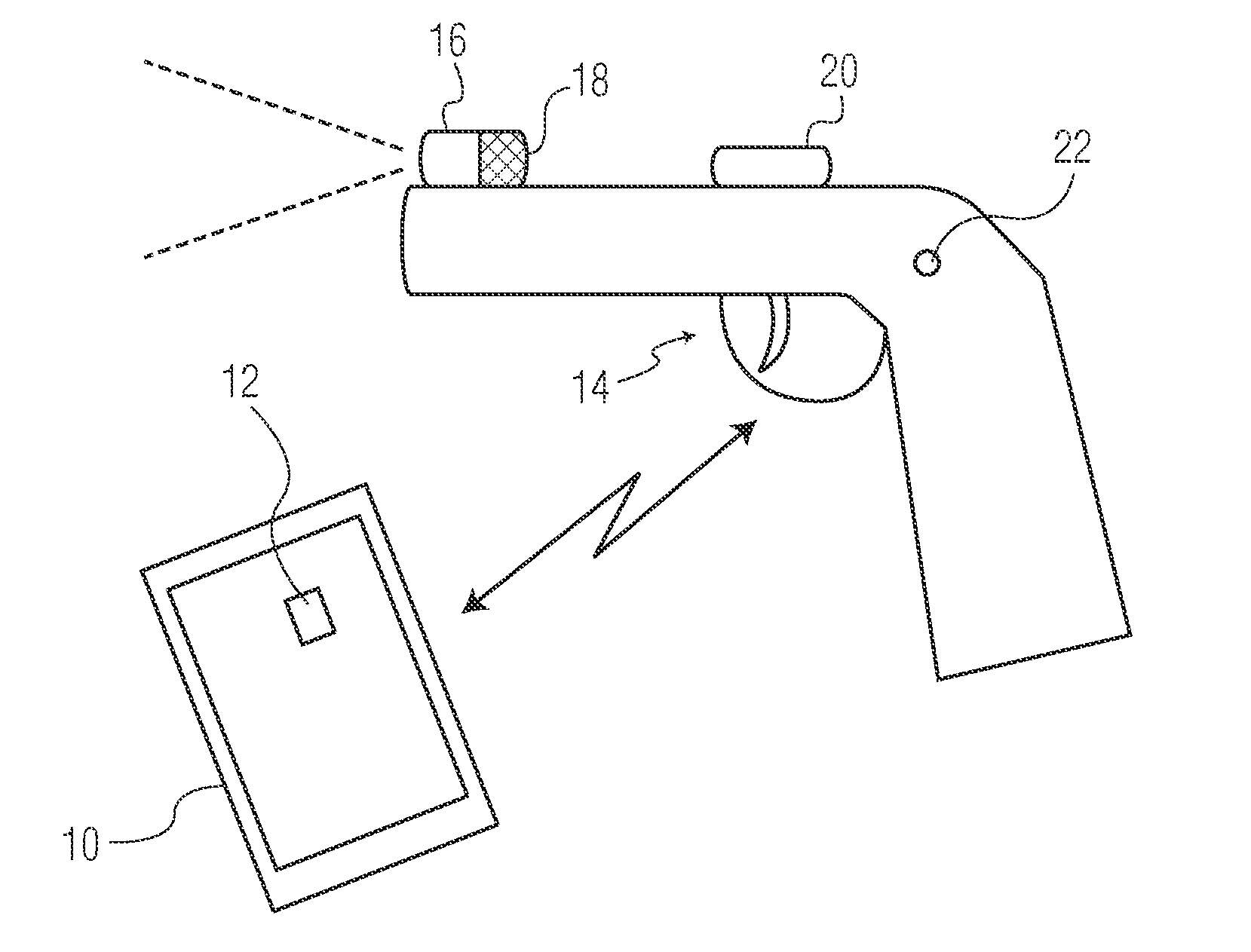
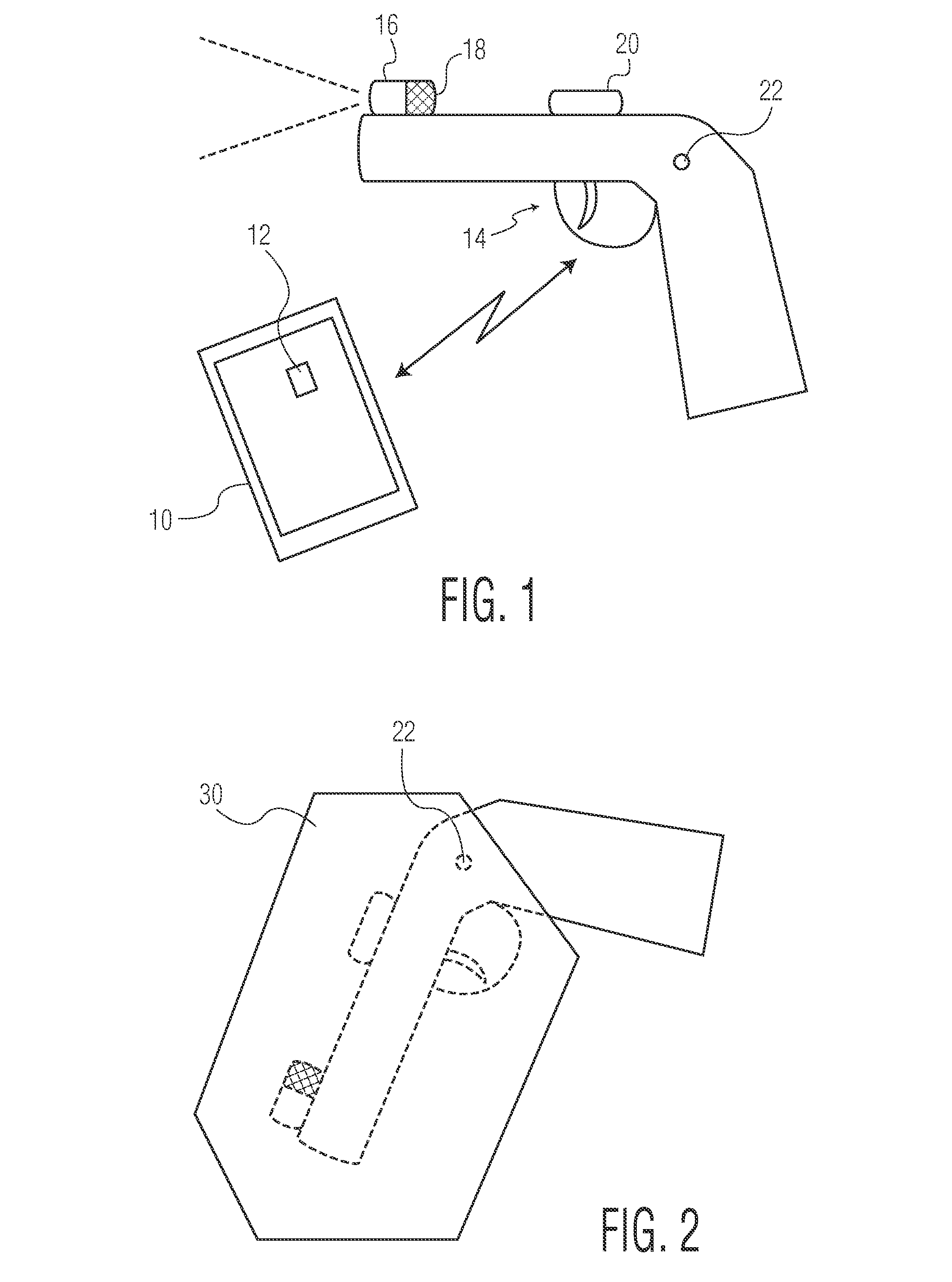
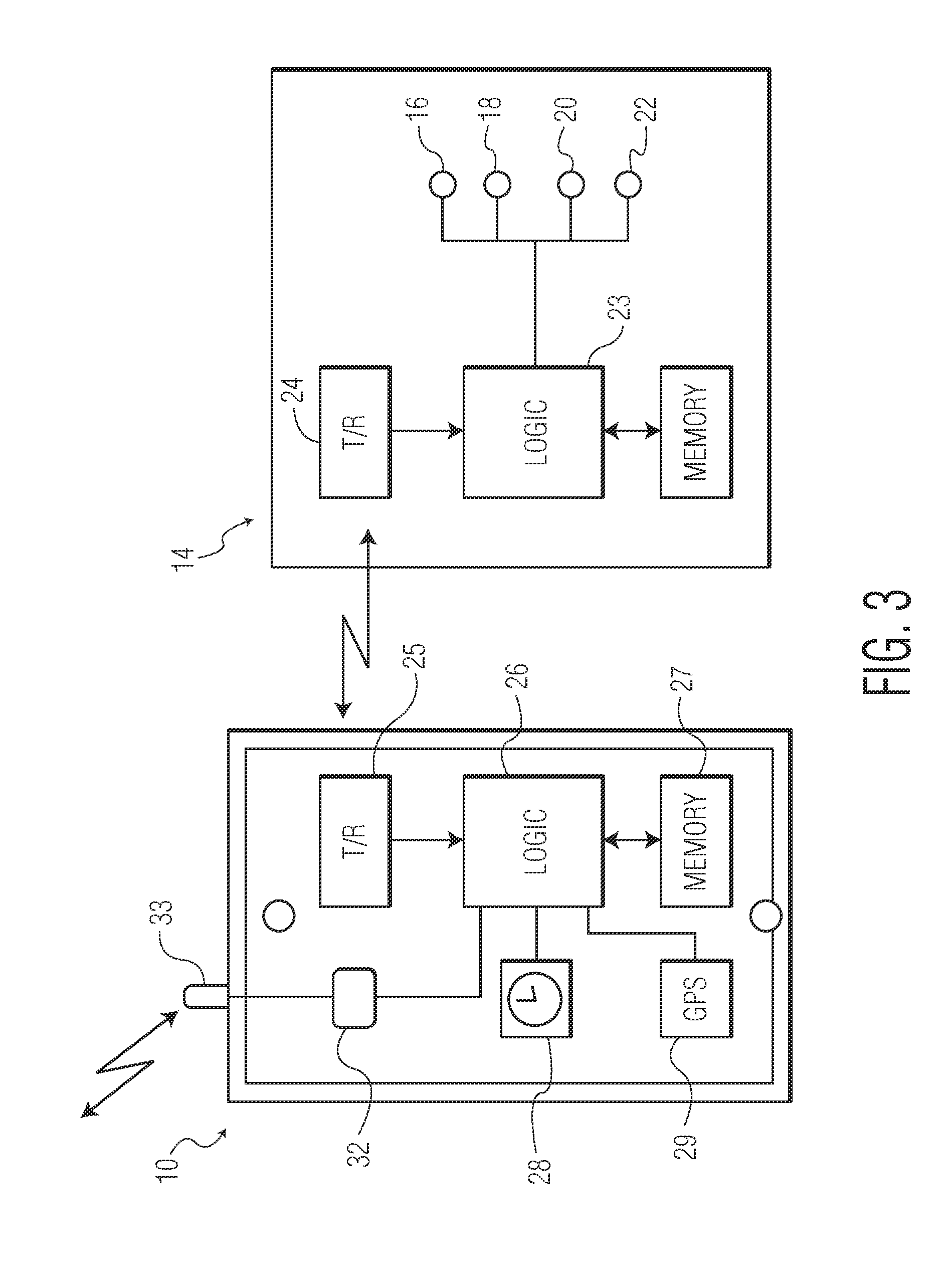
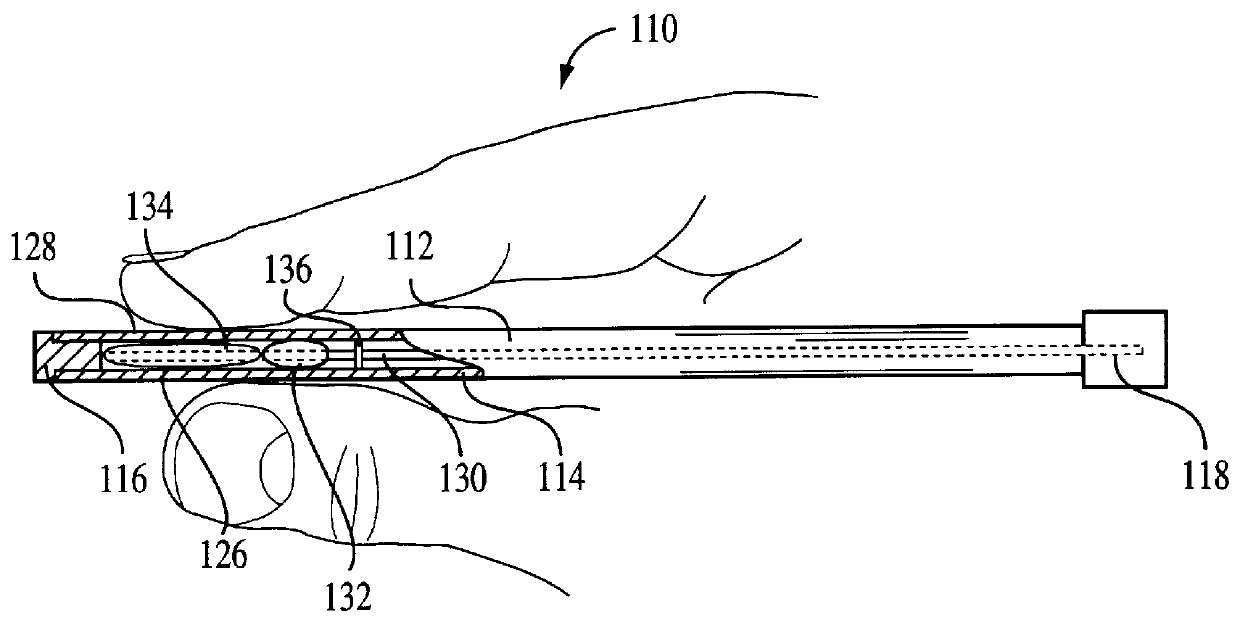
Evidence collecting and recording apparatus for a gun
ActiveUS20140215885A1Safety arrangementFiring/trigger mechanismsEngineeringElectrical and Electronics engineering
A battery-powered electronic evidence-collecting device on the gun that transmits to a smartphone or other device carried by the peace officer for recording and forwarding the evidence to a central station. The evidence collecting and recording apparatus is activated by the removal of the gun from its holster.
Owner:SULLIVAN KEVIN MICHAEL +1
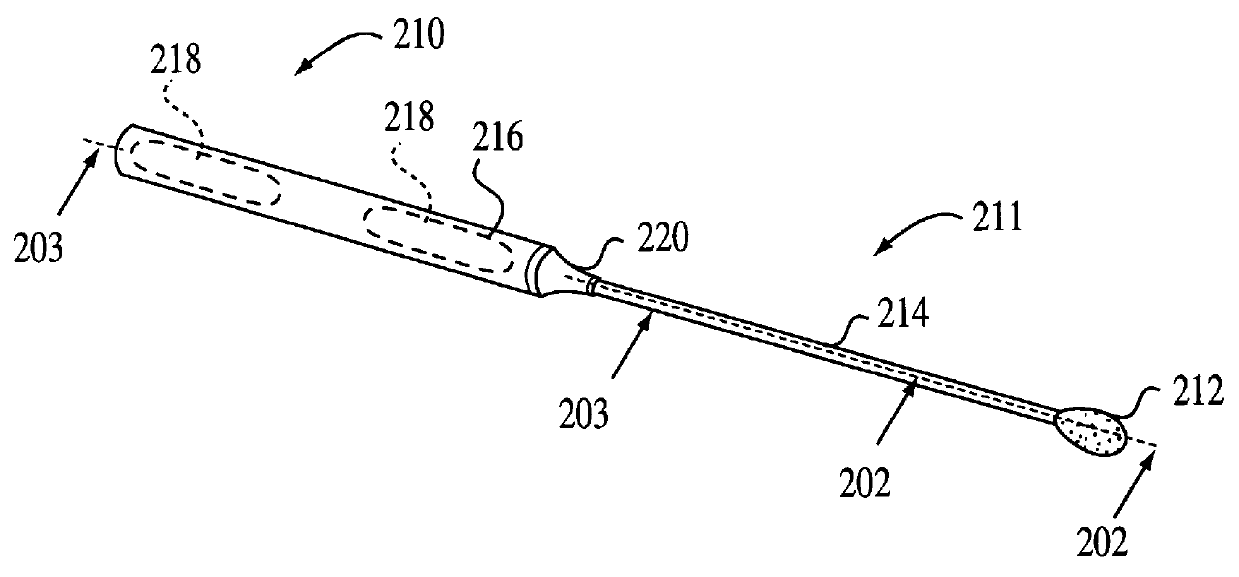
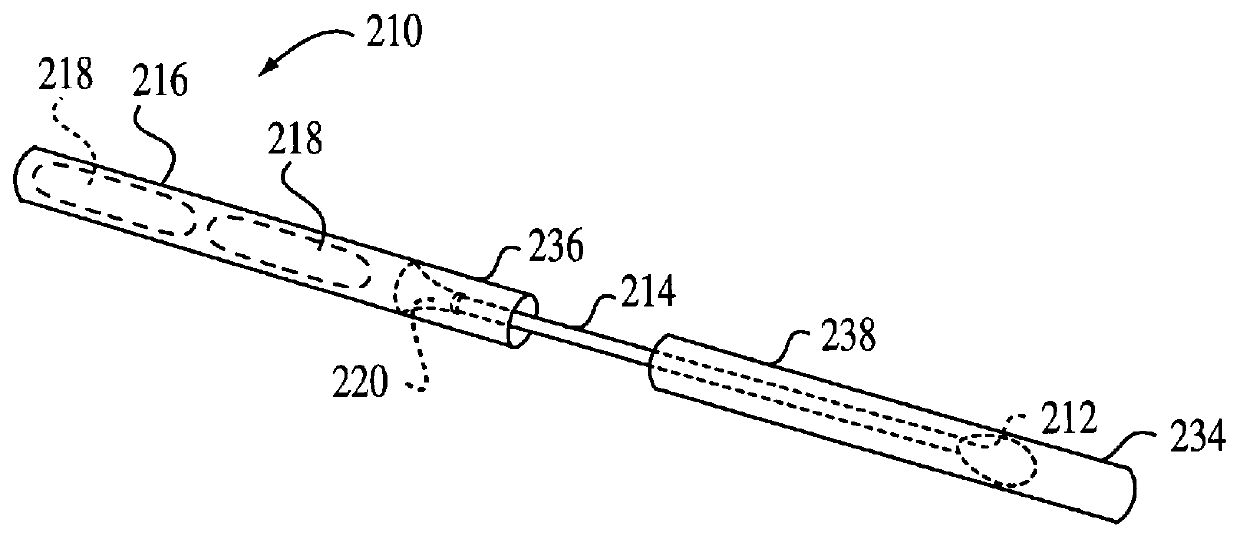
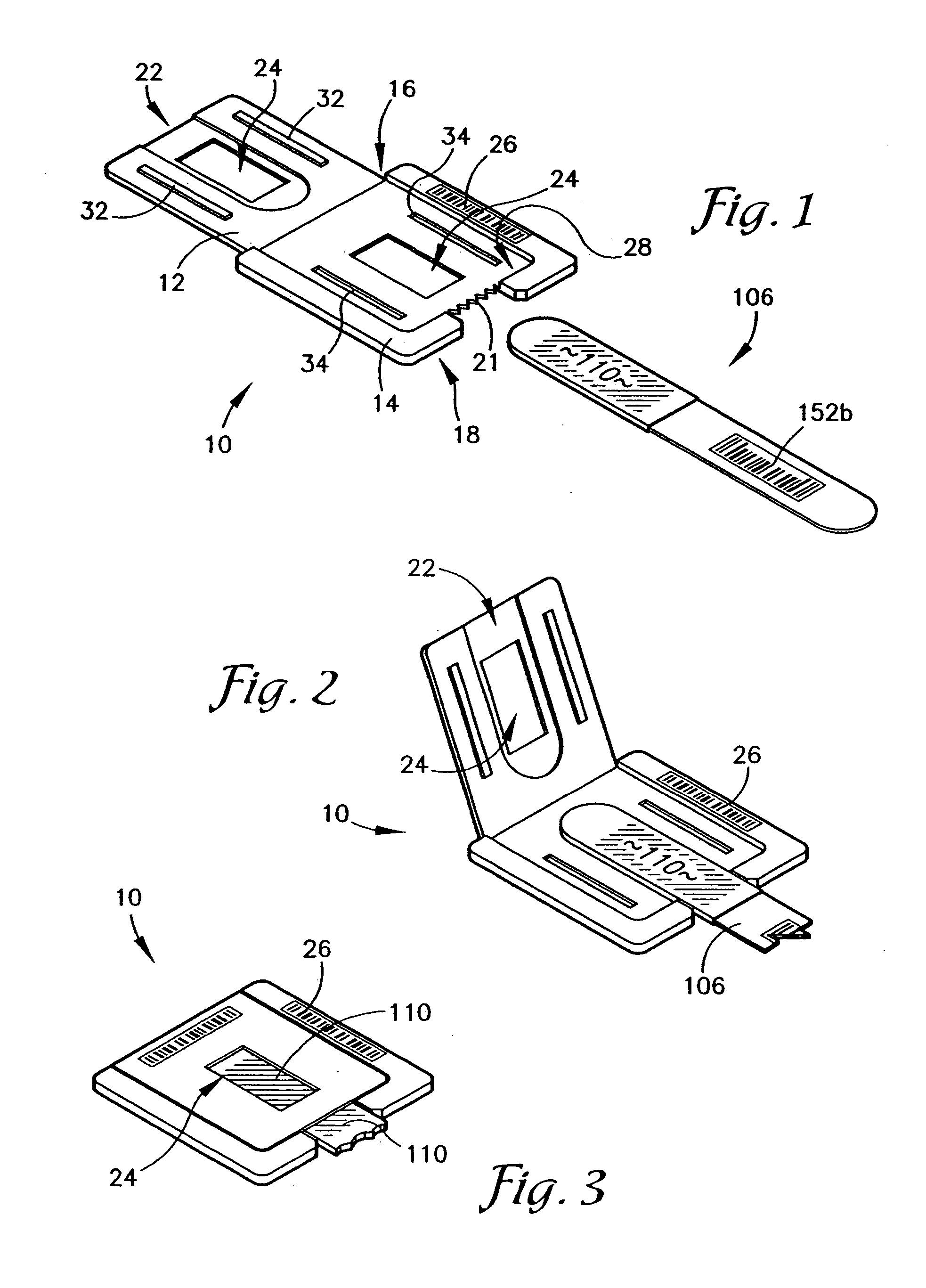
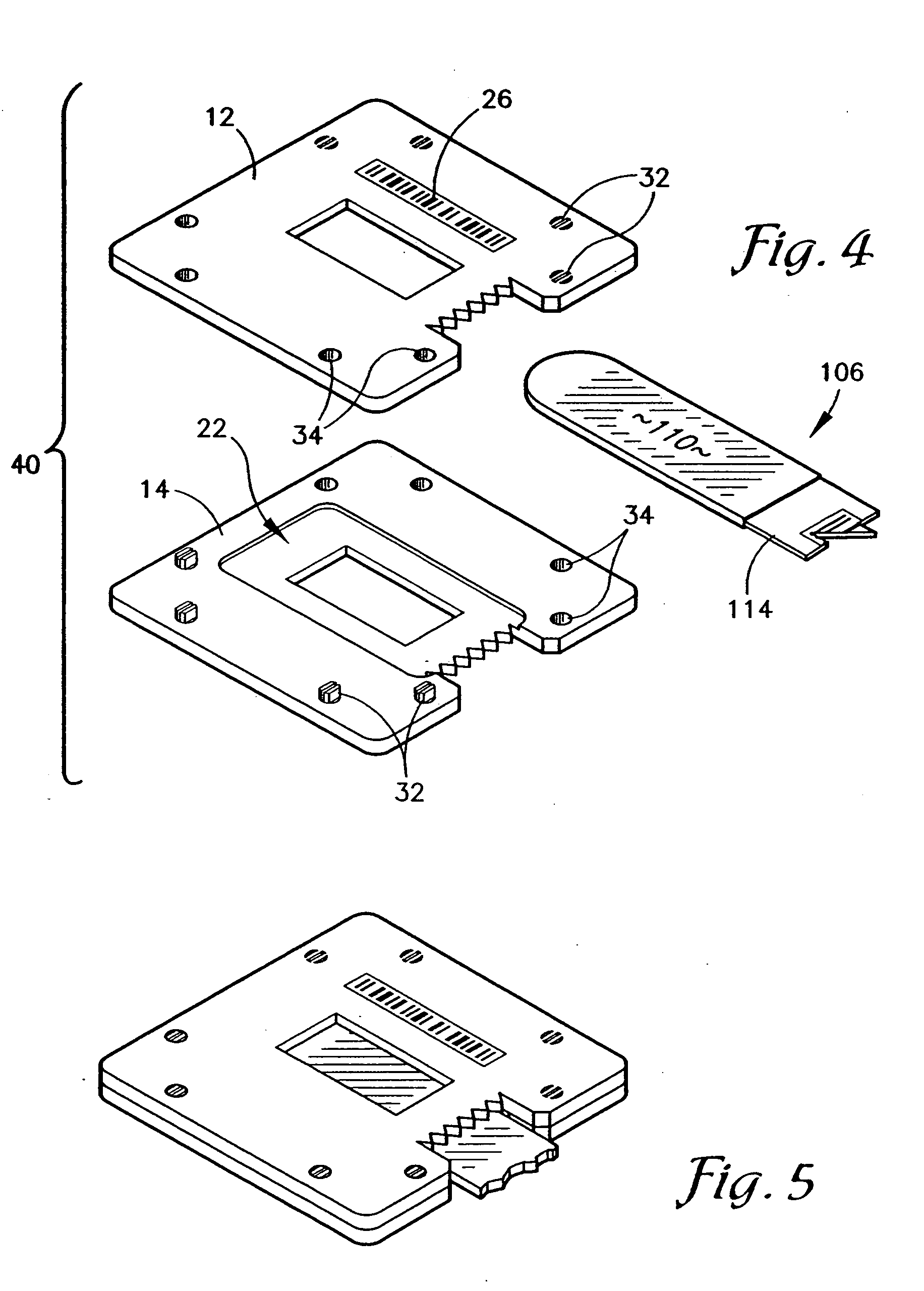
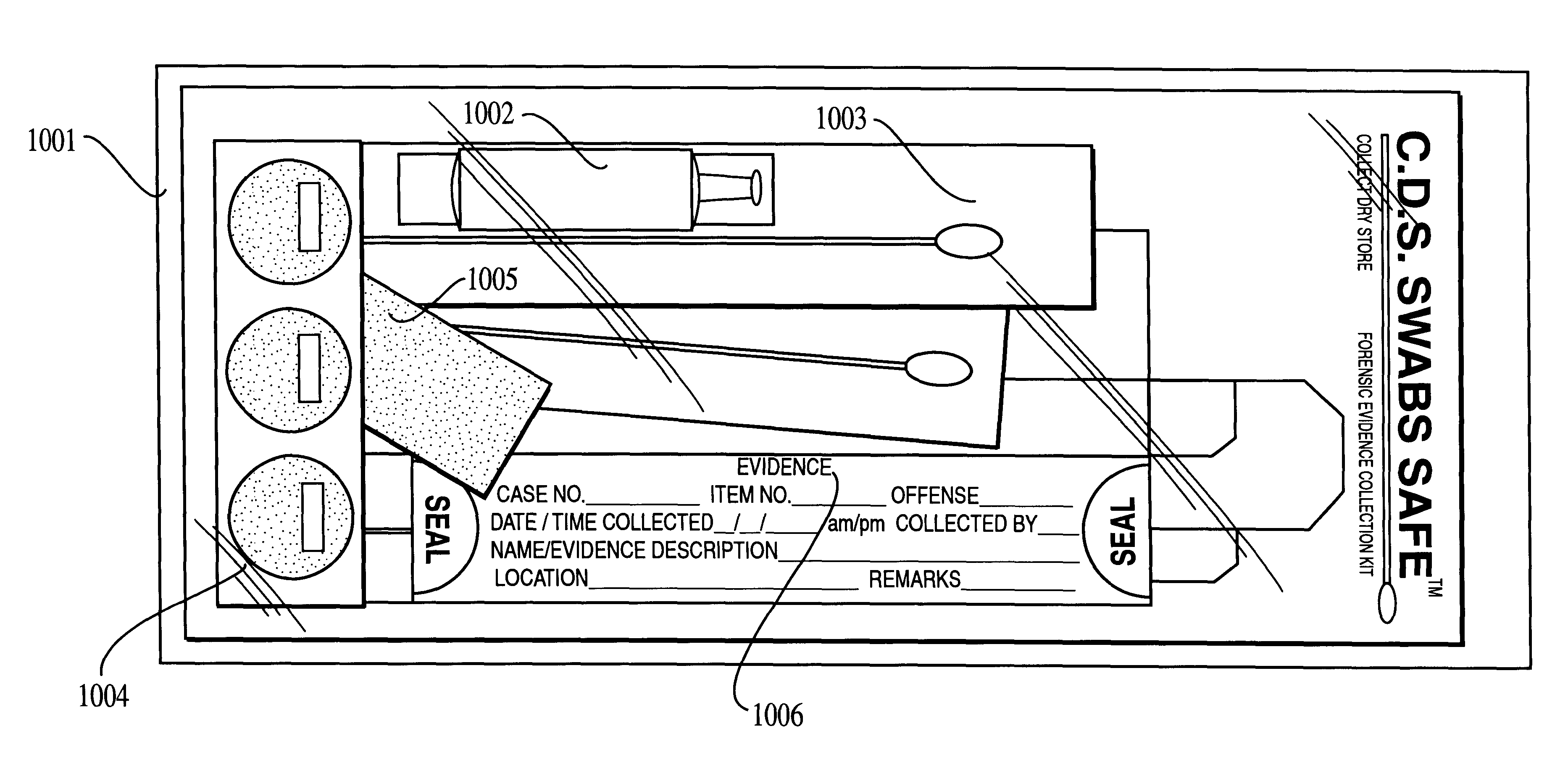
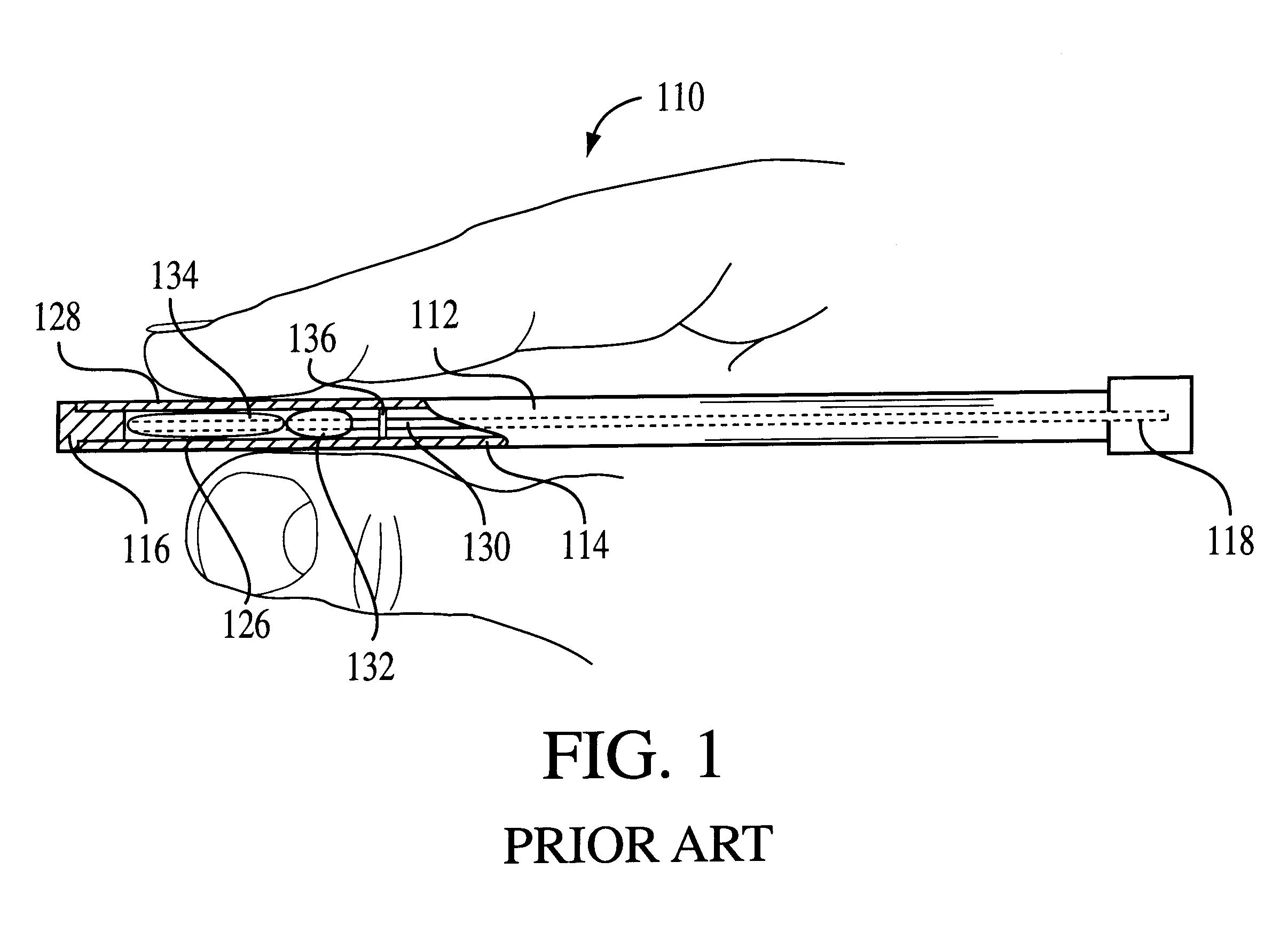
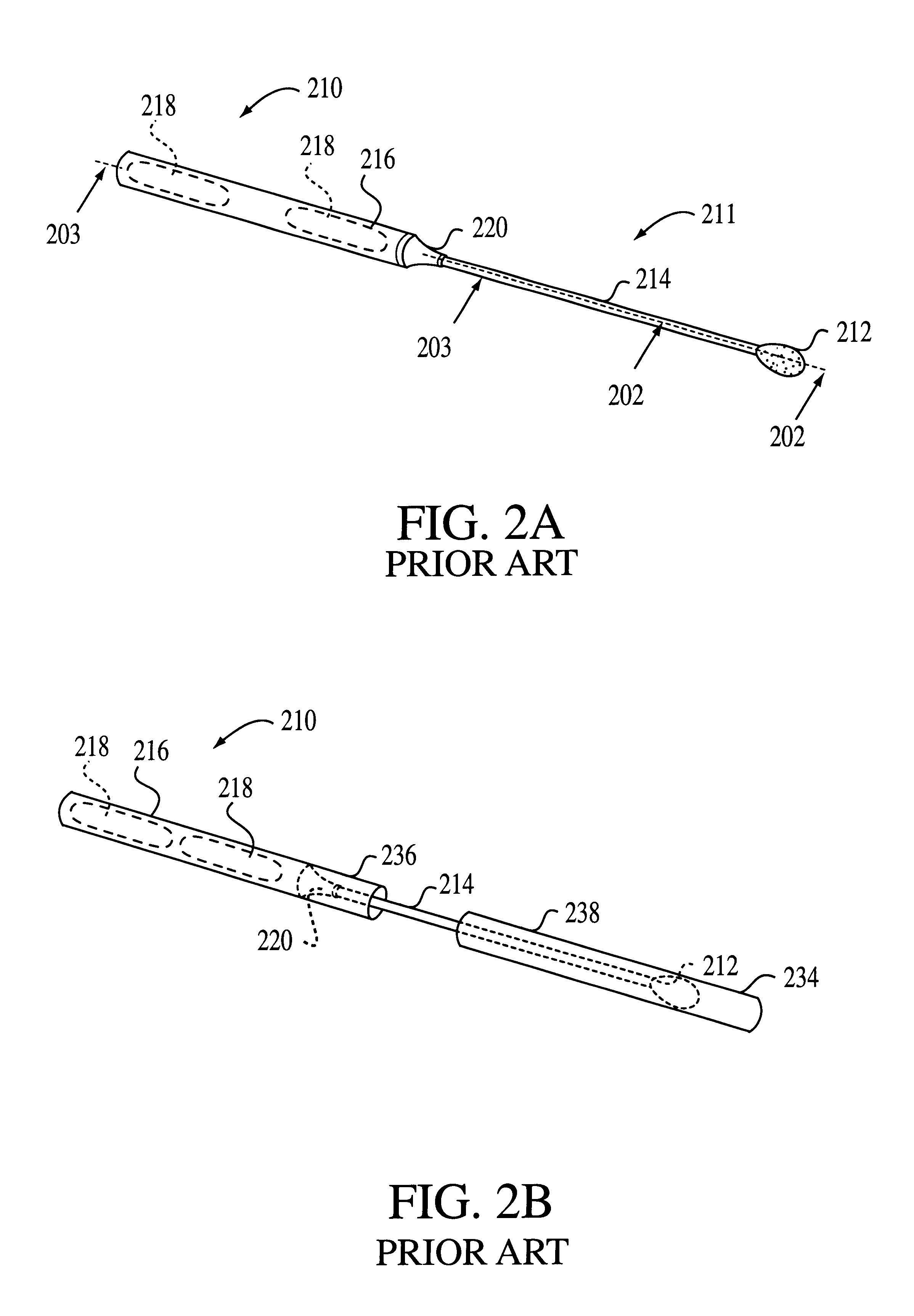
Foldable cardboard box for contact-free drying and long-term storage of biological evidence recovered on cotton swabs and forensic evidence collection kit including same
InactiveUS6085907APrevent tamperingDispensing apparatusVaccination/ovulation diagnosticsContact freeEngineering
A biological evidence collection apparatus provides contact-free drying, storage, identification, and protection against sample switch and contamination of collected biological samples. The apparatus may include the described forensic evidence collection kit which provides a set of tools for the collection and storage of biological evidence. The collection apparatus may also be used as part of a sexual assault evidence collection kit, or a kit for the collection of buccal swabs, and the like.
Owner:INST OF LEGAL MEDICINE OF THE UNIV OF BERNE
Evidence collection holder for sample automation
A device and method of securing the original biological specimen collection absorbent within a holder to permit use of the absorbent within automatic specimen analysis devices and to permit continuance of a chain of custody is provided.
Owner:BODE TECH GROUP
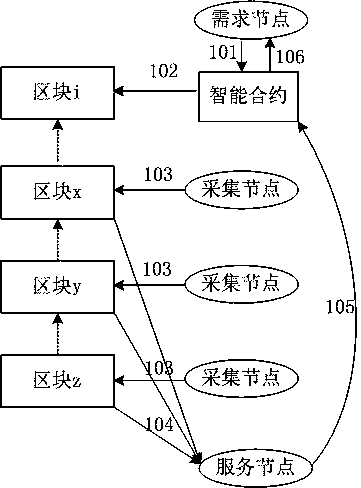
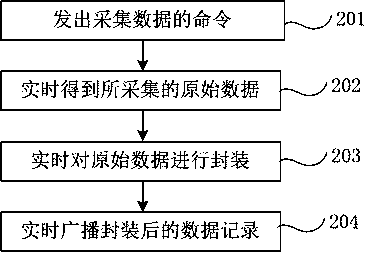
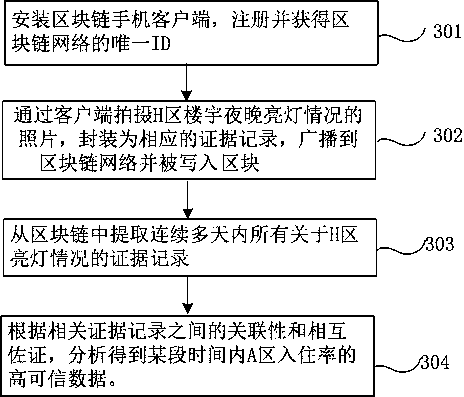
Electronic evidence collection and service method based on block chain
InactiveCN108512653AGuaranteed credibilityGuarantee authenticityEncryption apparatus with shift registers/memoriesDigital data protectionPaymentThird party
The invention discloses an electronic evidence collection and service method based on a block chain. The method comprises the following steps: a demand node issues an electronic evidence demand through a smart contract; a collection node creates an evidence record, that is, firstly collects original data related to the demand, packages the original data into a non-tamperable evidence record in real time and records the evidence record in a block chain network in real time for broadcasting; a bookkeeping node writes the evidence record into a block according to a consensus mechanism; a servicenode screens the evidence record from the block and forms electronic evidence according to the terms of the smart contract, and activates the smart contract; and the smart contract pays the service node and submits a node reward of the corresponding original record according to payment terms. The method disclosed by the invention has a good application prospect in the application field of independent investigation and evidence collection (such as on-site evidence collection of vehicle insurance) and trusted third party evidence collection (for example, investigation reports of housing vacancyrates).
Owner:CHENGDU LINGGUANG QUANTUM TECH
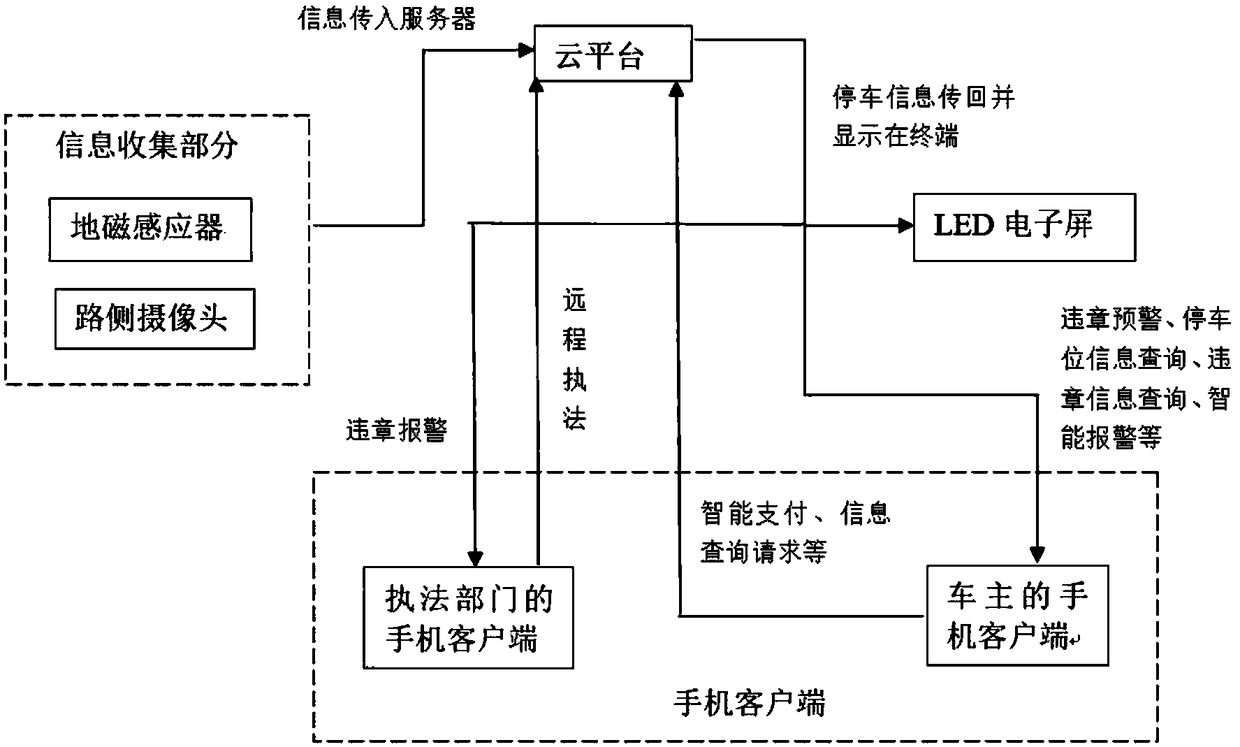
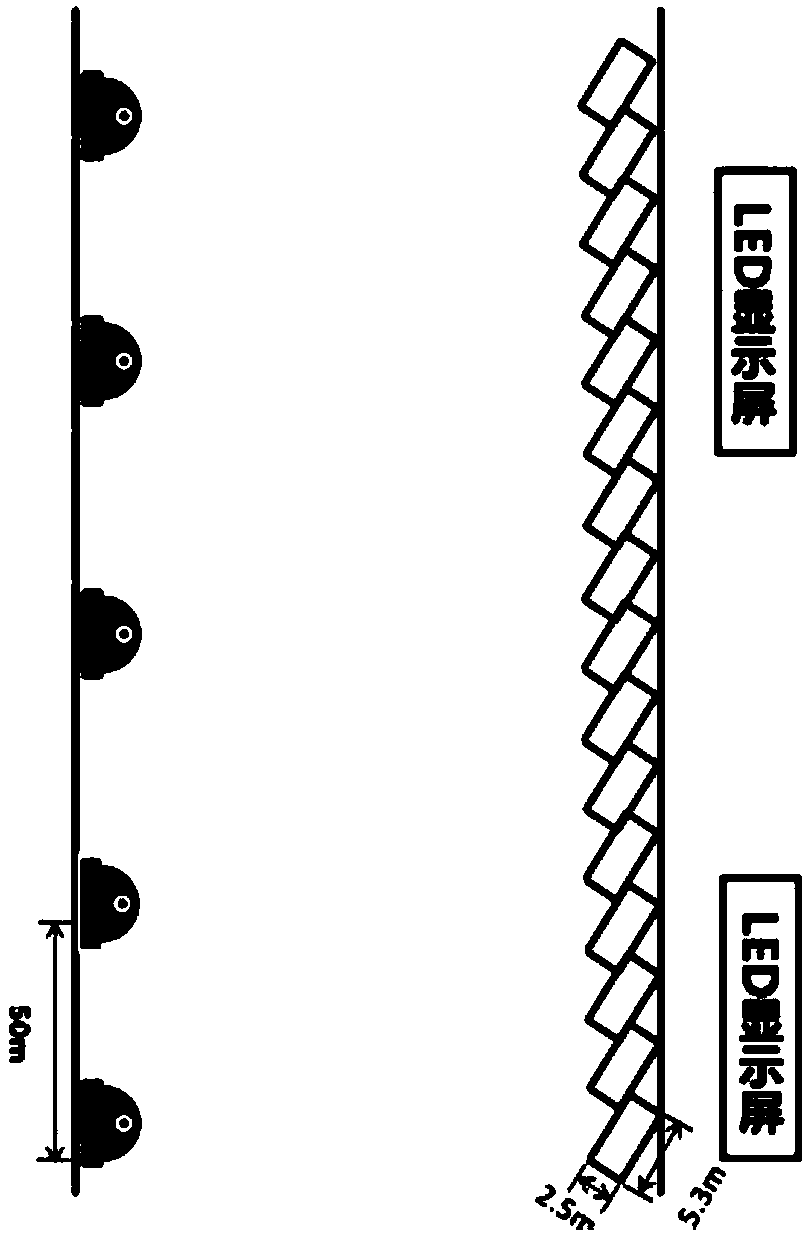
Fine management oriented intelligent inside-road parking space management and control technology
InactiveCN108257412AHigh priceLow priceTicket-issuing apparatusIndication of parksing free spacesPaymentControl system
The invention discloses a fine management oriented intelligent inside-road parking space management and control technology. First, urban inside-road parking spaces suitable for fine management are planned and designed according to the traffic demand and capacity, and then, geomagnetic sensors and cameras are installed to identify the parking state of each parking space in real time. Roadside electronic display screens and mobile phone clients are arranged to display the current state of each parking space. A user can perform functions such as parking management state query, automatic payment and violation pre-warning on the mobile phone client thereof. For the automatic law enforcement function, the law enforcement department can carry out law violation judgment, automatic evidence collection and fast law enforcement remotely according to the fine management requirements and the actual parking state. A central control system, through the analysis of big data of traffic, dynamically optimizes the indexes of the parking spaces and carries out dynamic guidance to balance temporal and spatial parking resources. The beneficial effect of technology is that the contradiction between the current parking demand and traffic demand can be mediated.
Owner:中景博道城市规划发展有限公司
Foldable cardboard box for contact-free drying and long-term storage of biological evidence recovered on cotton swabs and forensic evidence collection kit including same
InactiveUS6171260B1Vaccination/ovulation diagnosticsDiagnostic recording/measuringContact freeEngineering
A biological evidence collection apparatus provides contact-free drying, storage, identification, and protection against sample switch and contamination of collected biological samples. The apparatus may include the described forensic evidence collection kit which provides a set of tools for the collection and storage of biological evidence. The collection apparatus may also be used as part of a sexual assault evidence collection kit, or a kit for the collection of buccal swabs, and the like.
Owner:INST OF LEGAL MEDICINE OF THE UNIV OF BERNE
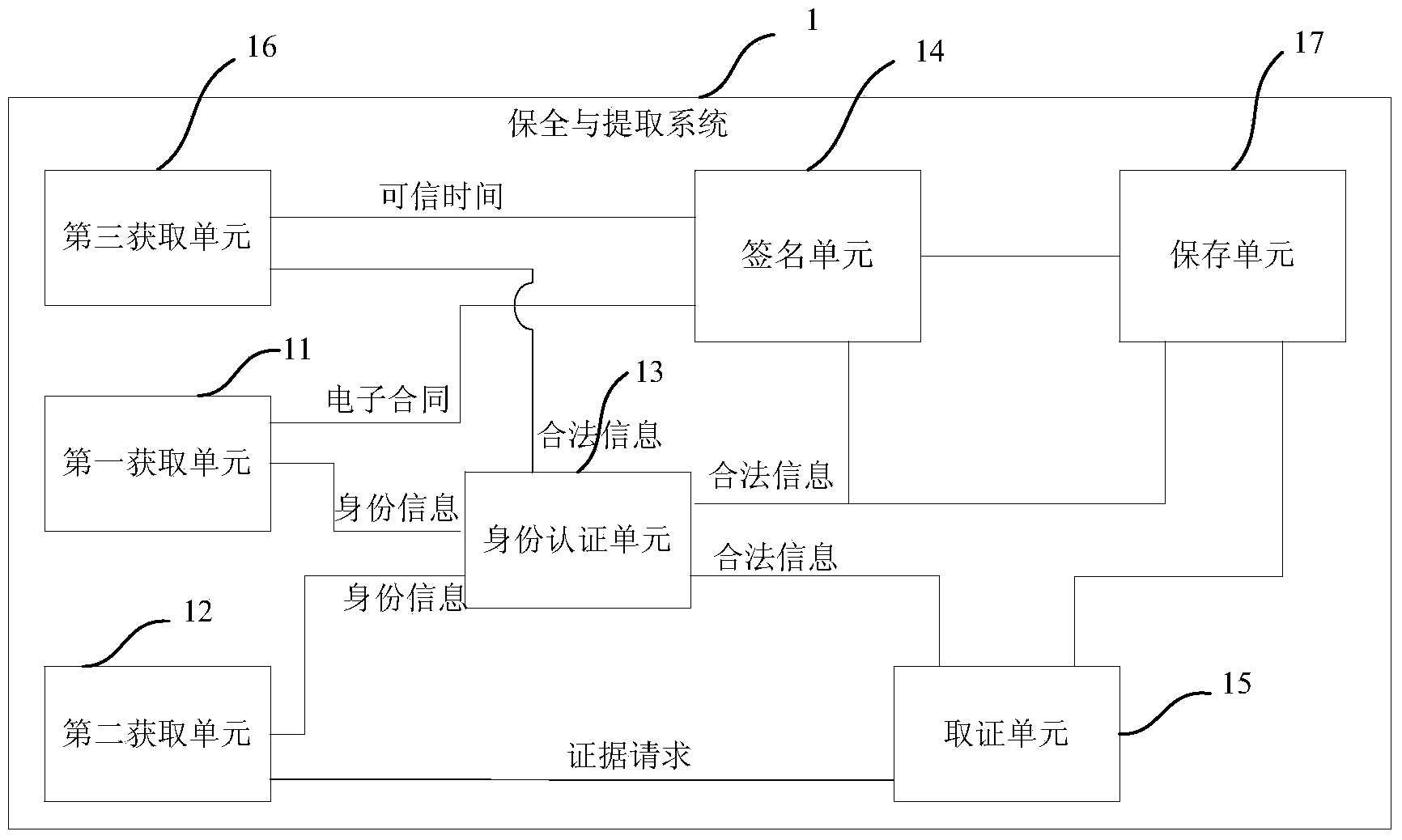
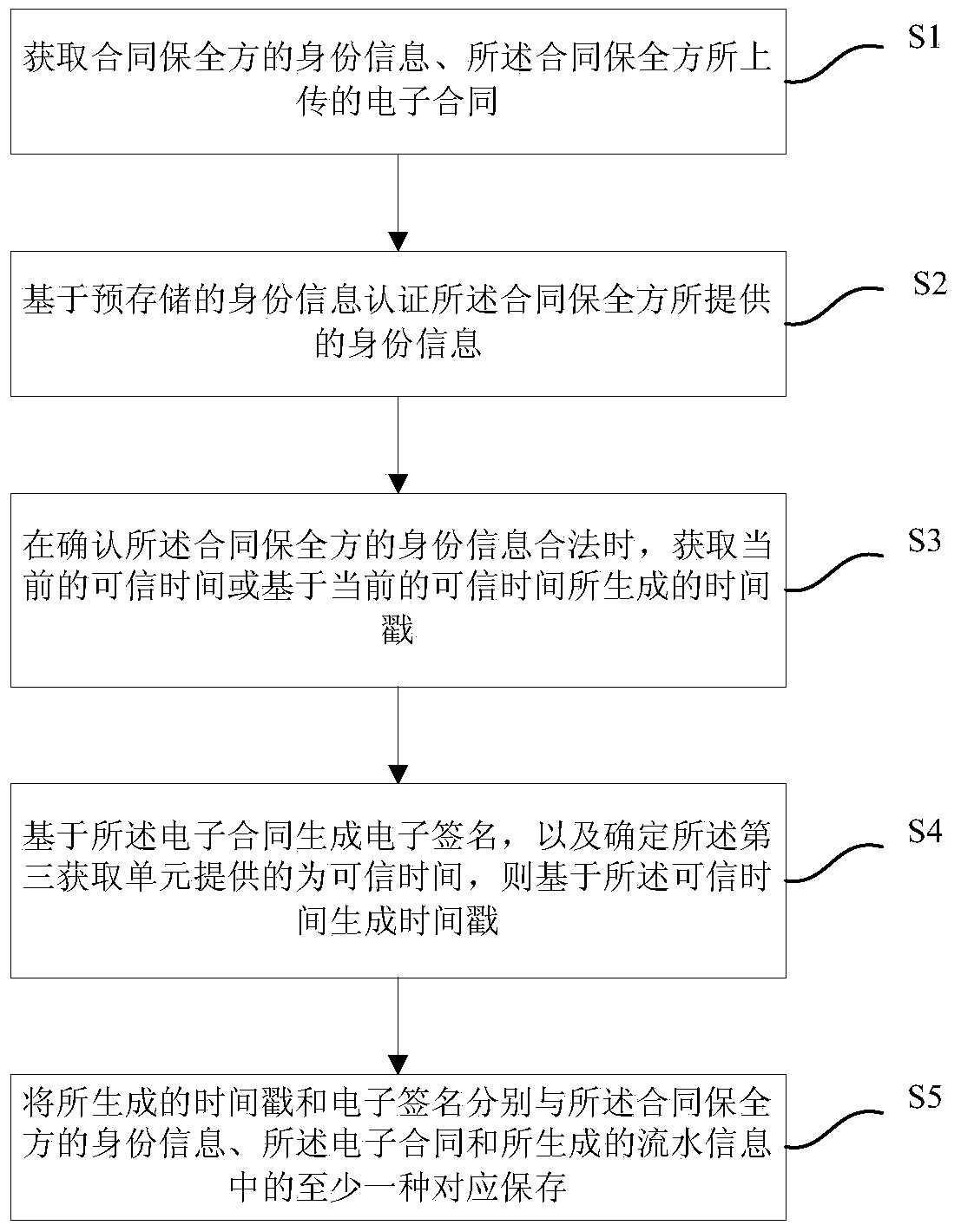
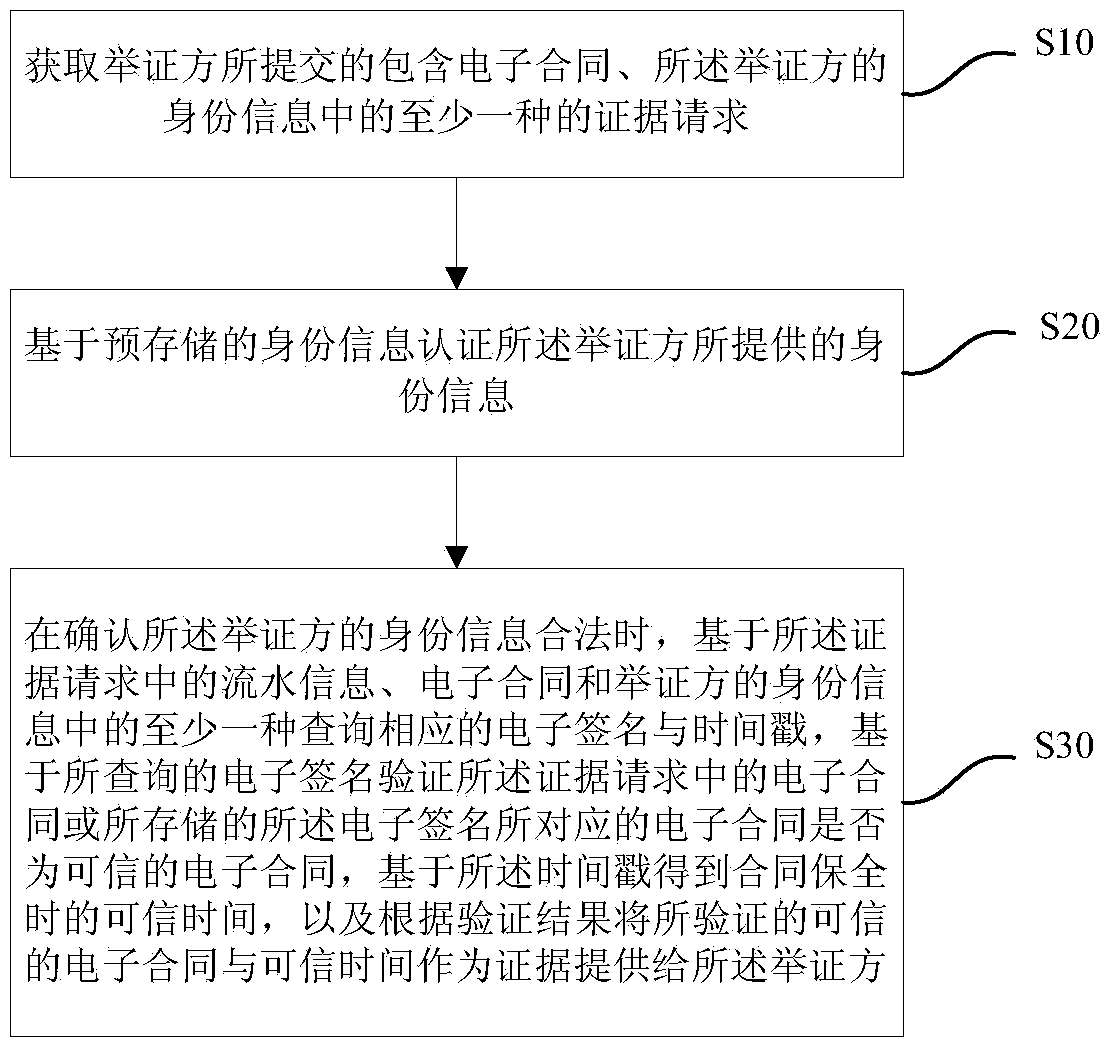
Dependable preservation and evidence collection system and method for electronic contract
ActiveCN103514410AUniqueness guaranteedReliableUser identity/authority verificationDigital data protectionTimestampElectronic contracts
The invention provides a dependable preservation and evidence collection system and method for an electronic contract. In the preservation stage, the system obtains identity information and the electronic contract of a contract preservation side and preserves an electronic signature and a timestamp generated in a signature unit with at least one of the identity information of the contract preservation side, the electronic contract and generated running information in a corresponding mode through authentication of the identity information and by generating the electronic signature based on the electronic contract and generating the timestamp based on current dependable time. In the evidence collection stage, the system obtains an evidence request submitted by a proof side and including at least one of the running information, the electronic contract and the identity information, and a dependable electronic contract and contract preservation time can be provided for the proof side as evidence through authentication of the identity information of the proof side and by inquiring the corresponding electronic signature and the timestamp and verifying the corresponding electronic signature and the timestamp respectively.
Owner:上海市数字证书认证中心有限公司
Security control method of intelligent lock
InactiveCN104766395ASimple and fast operationProlong damage timeIndividual entry/exit registersMotor driveDistance sensors
The invention discloses a security control method of intelligent locks, which includes a security evidence collection step: when a visitor appears in front of a lock or a door in a preset distance and to a preset time duration, a distance sensor controls a camera and a microphone to work according to requirement to perform required image and audio evidence collection to a doubtable person; if the visitor hardly beats or damages the lock or the door, an impact force sensor instantly control the camera and the microphone to perform photographing and recording and instantly uploads an image or a record to cloud and dials an appointed telephone number on the network; if the visitor hardly beats or damages the lock or the door for a preset time, evidence collection and alarm through telephone or network are instantly carried out with warning the visitor through sound, light and the like. The impact force sensor can rapidly respond the impact force at a preset value, present the evidence by all means and control a motor driving apparatus to reinforcing the lock, thereby effectively delaying a destroy time of a criminal and getting a precious police time as more as possible. The security control method can effectively ensure property security of consumers.
Owner:张瞳
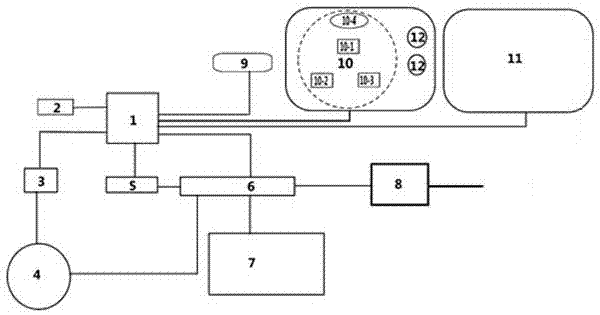
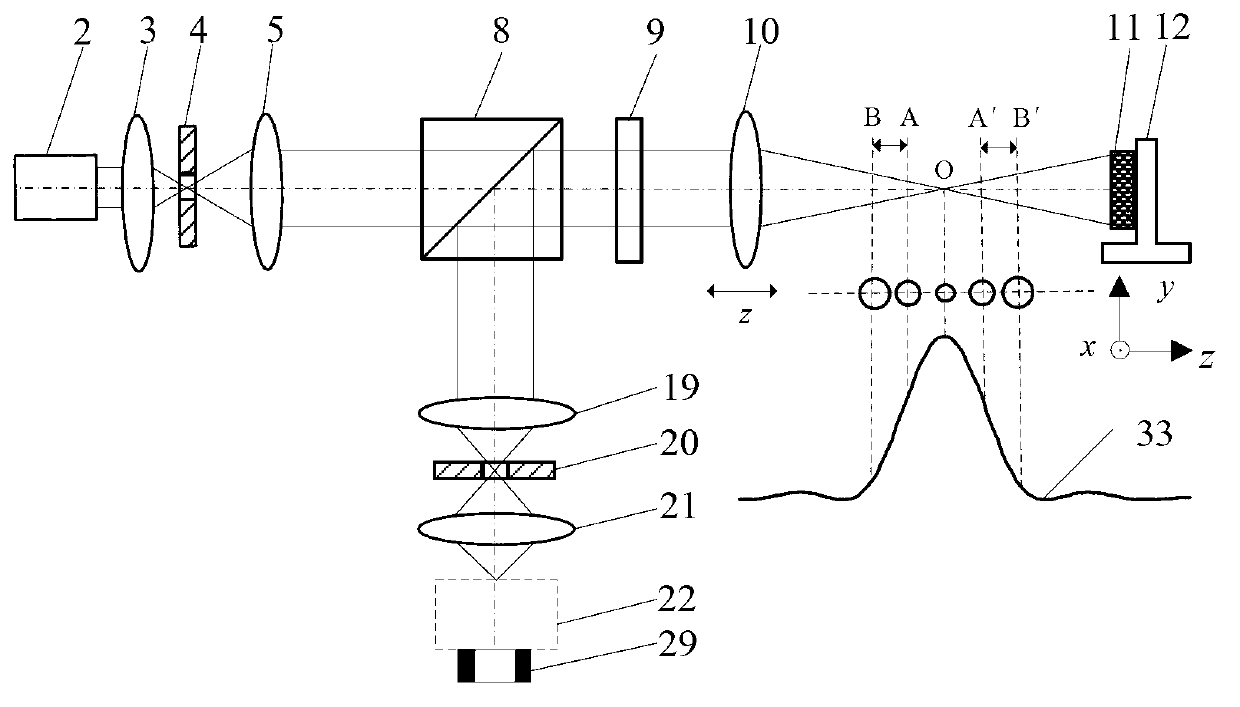
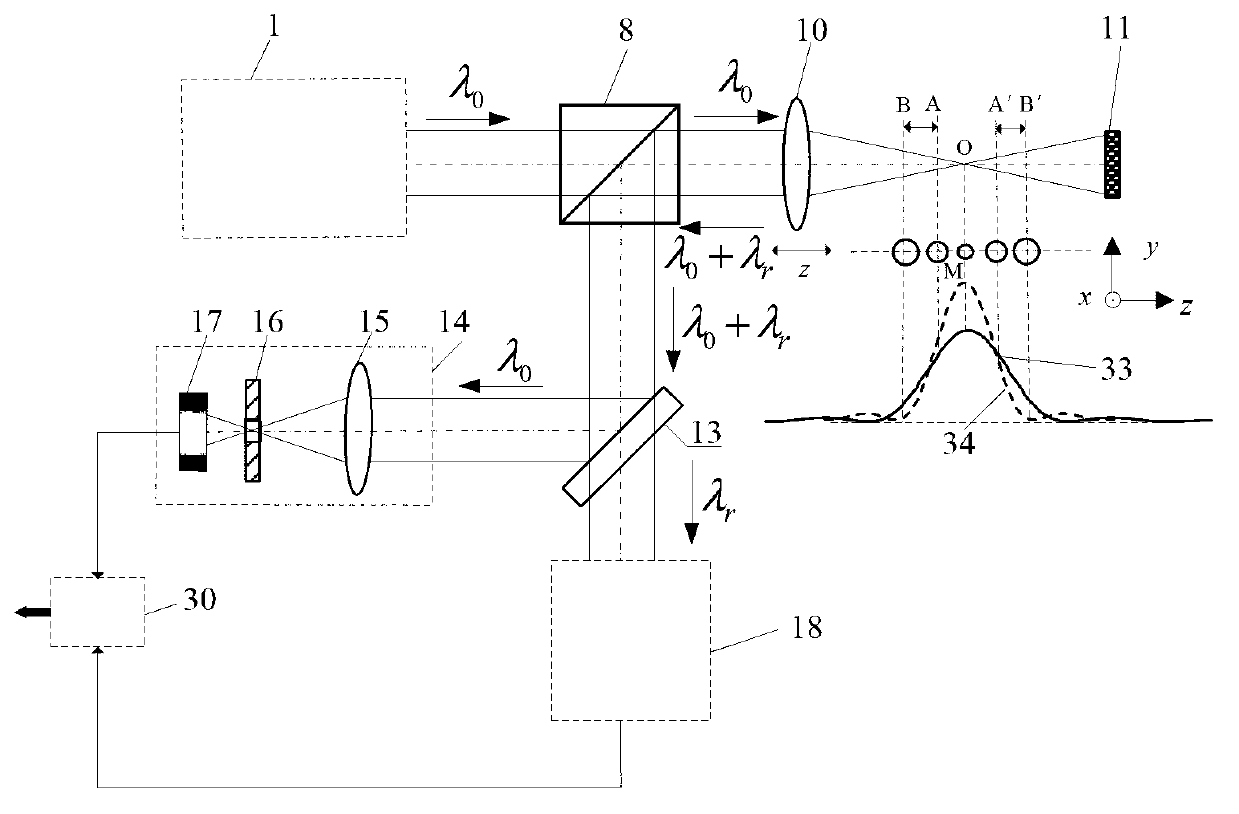
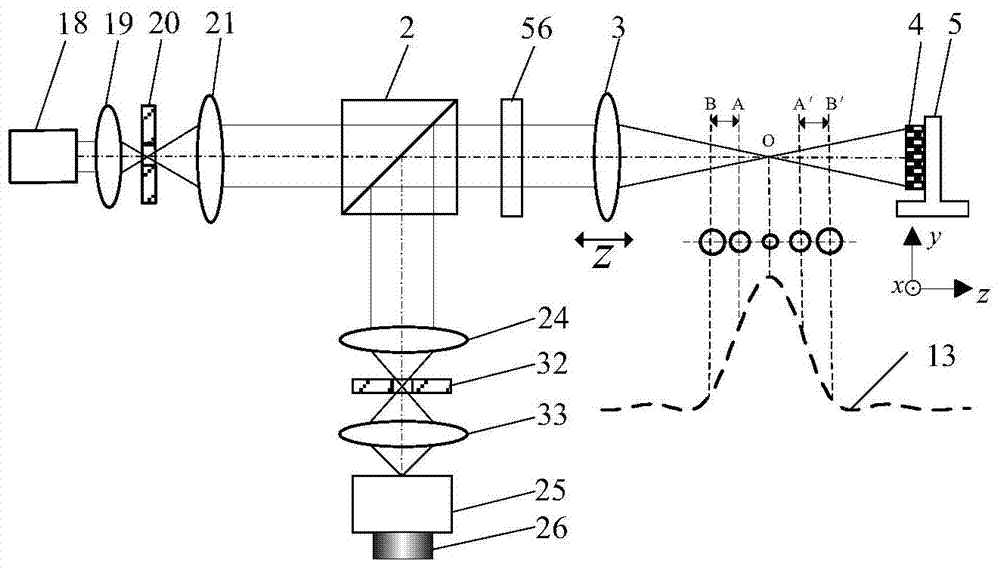
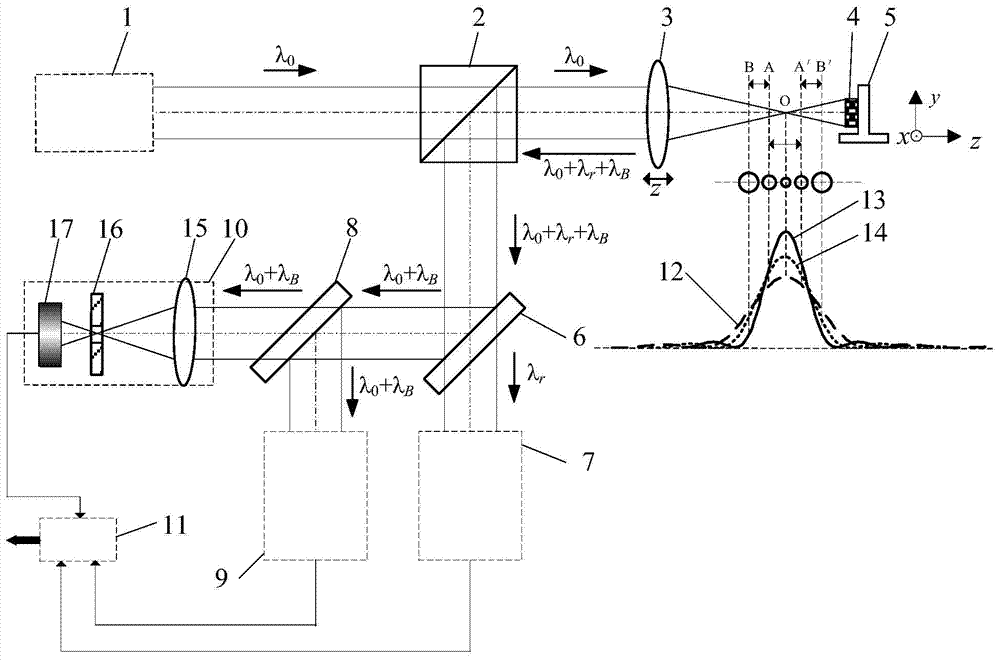
Method and device for confocal Raman spectrum detection with high spatial discrimination
ActiveCN103105231ARealize spectral detectionRealize 3D geometric position detectionRadiation pyrometrySpectrometry/spectrophotometry/monochromatorsRayleigh scatteringLight spot
The invention belongs to the technical field of optical microscopic imaging and spectral measurement, and relates to a method and a device for confocal Raman spectrum detection with high spatial discrimination. According to the method and the device, confocal technique is integrated into the spectrum detection; nondestructive separation is carried out on Rayleigh scattering light and Raman scattering light by using of a dichroic beam splitting system (13); by using the characteristic that the maximum value of a confocal curve (34) corresponds to a focal position accurately, spectral information exciting a light spot focal position is accurately acquired through maximizing; and the spectrum detection with the high spatial discrimination is achieved, and the method and the device which are capable of achieving the sample microcell spectrum detection with the high spatial discrimination are formed. The method and the device for the confocal Raman spectrum detection with the high spatial discrimination have the advantages of being accurate in positioning, high in spatial discrimination, high in spectrum detection sensitivity and the like, and has broad application prospect in the fields of biomedicine, court evidence collection and the like.
Owner:BEIJING INSTITUTE OF TECHNOLOGYGY
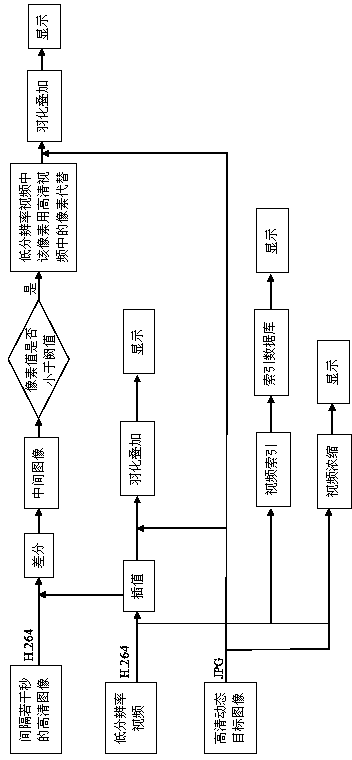
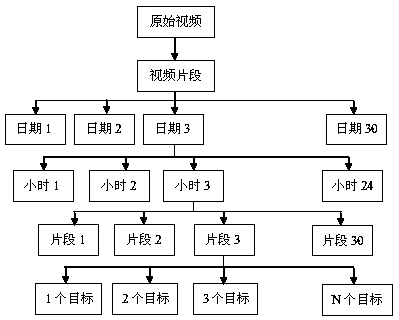
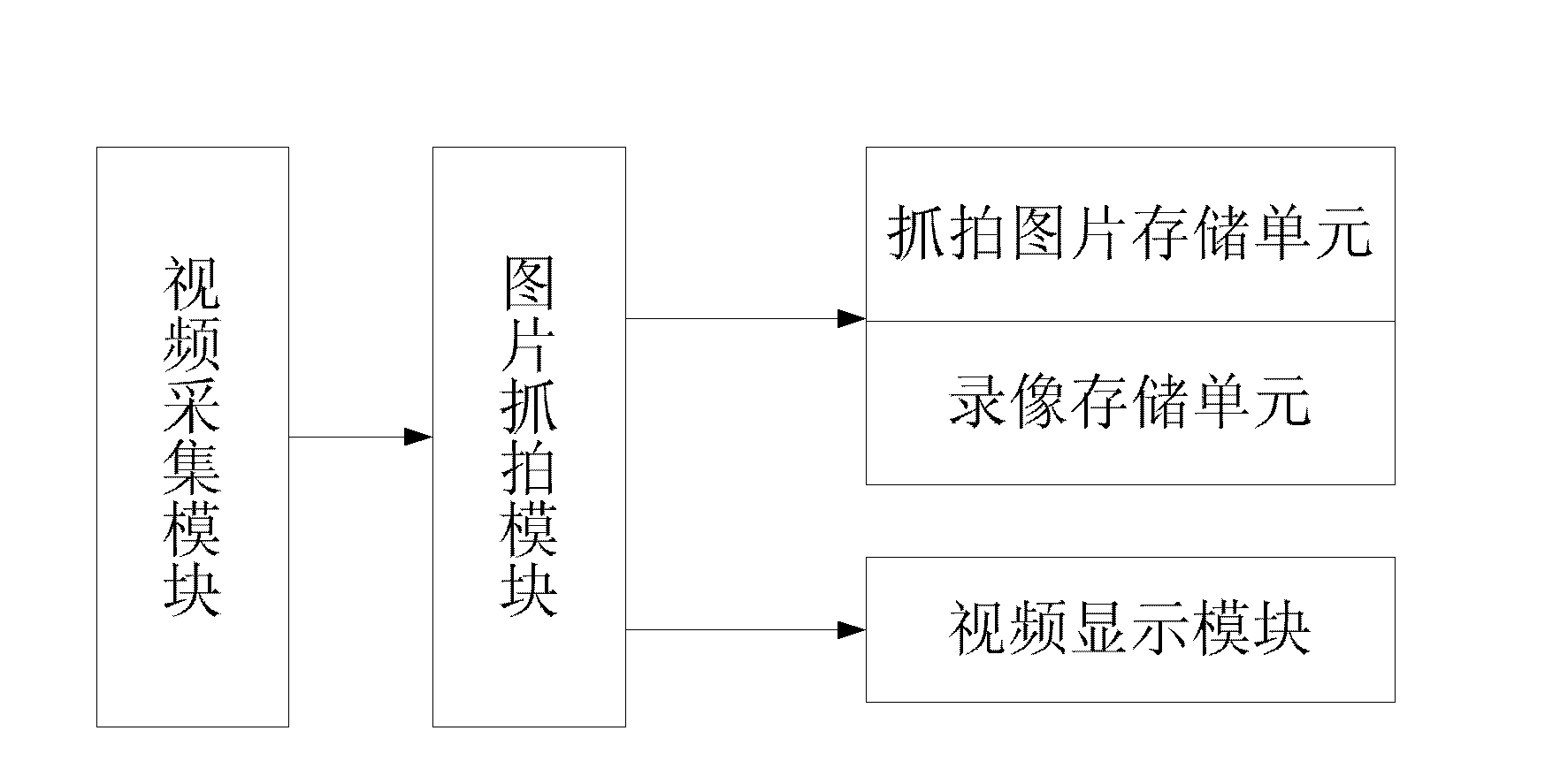
Event-oriented intelligent camera monitoring method
ActiveCN104284158ASave browsing timeImprove the efficiency of investigation and evidence collectionImage analysisClosed circuit television systemsComputer graphics (images)Engineering
The invention provides an event-oriented intelligent camera monitoring method. The method includes the steps that after video capture is conducted, processing is carried out, three code streams are obtained, the three code streams include a low-resolution video, high-definition images which are spaced by a plurality of seconds and a high-definition moving object image, and the three code streams are displayed on a display terminal independently or are displayed on the display terminal after being overlaid and fused. By means of the event-oriented intelligent camera monitoring method, one video which is much shorter than an original video can be provided, and the browsing time is greatly shortened; event clues can be searched for quickly according to the information such as time, and thus the investigation and evidence collection efficiency is improved; space information in the scene is fully utilized, space-time redundancy in the video is reduced, events which happen at different periods of time are displayed at the same time, and activities in the video can be understood and grasped easily; activities and events in the original video cannot be lost, and the effects that fast playing can be achieved and video information cannot be lost are achieved; the code stream bandwidth and the definition of special areas are both considered, hence, powerful support is provided for evidence collection after events, and a wide application requirement for the method can be met in the video security and protection monitoring field.
Owner:NANJING XINBIDA INTELLIGENT TECH
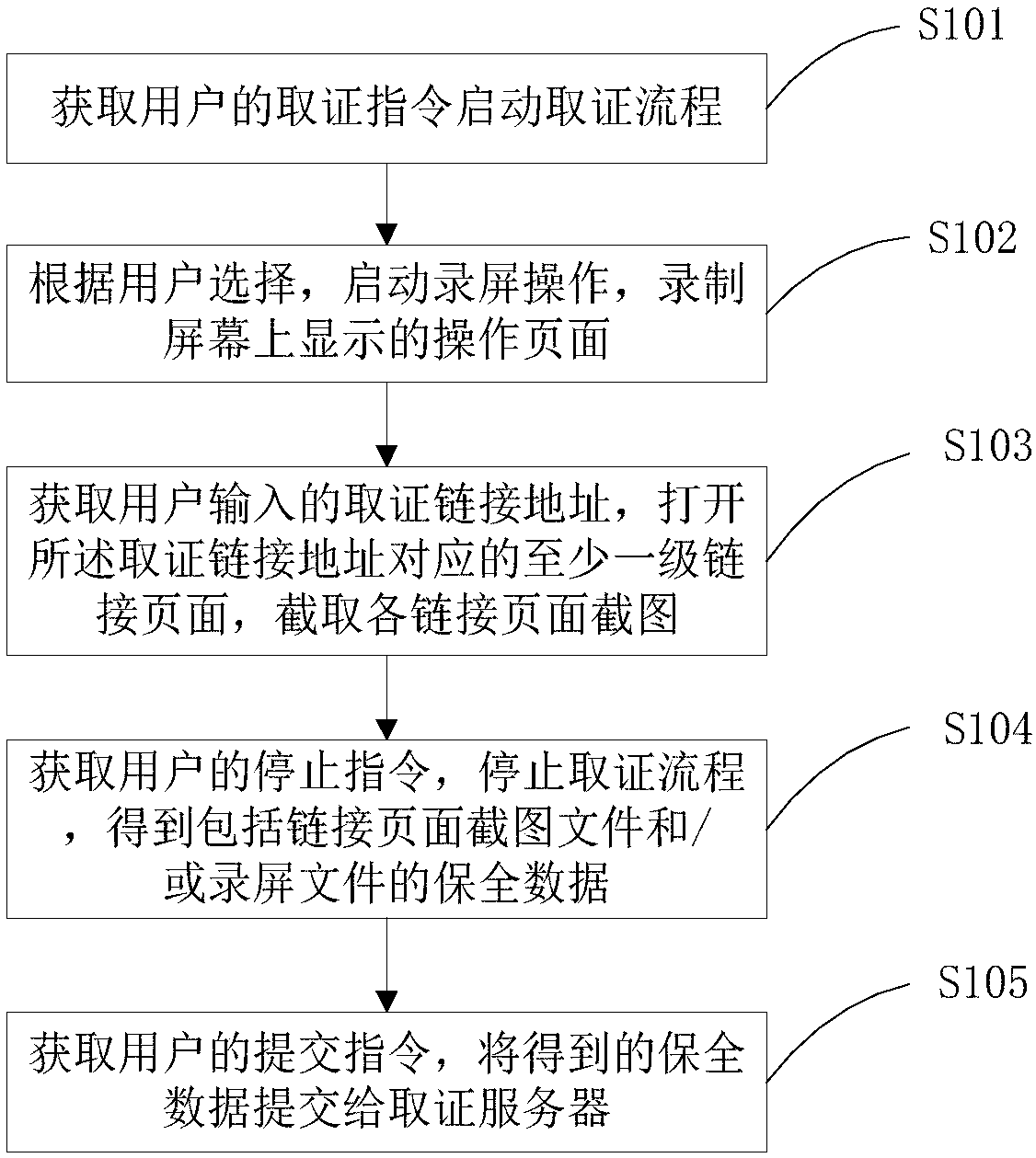
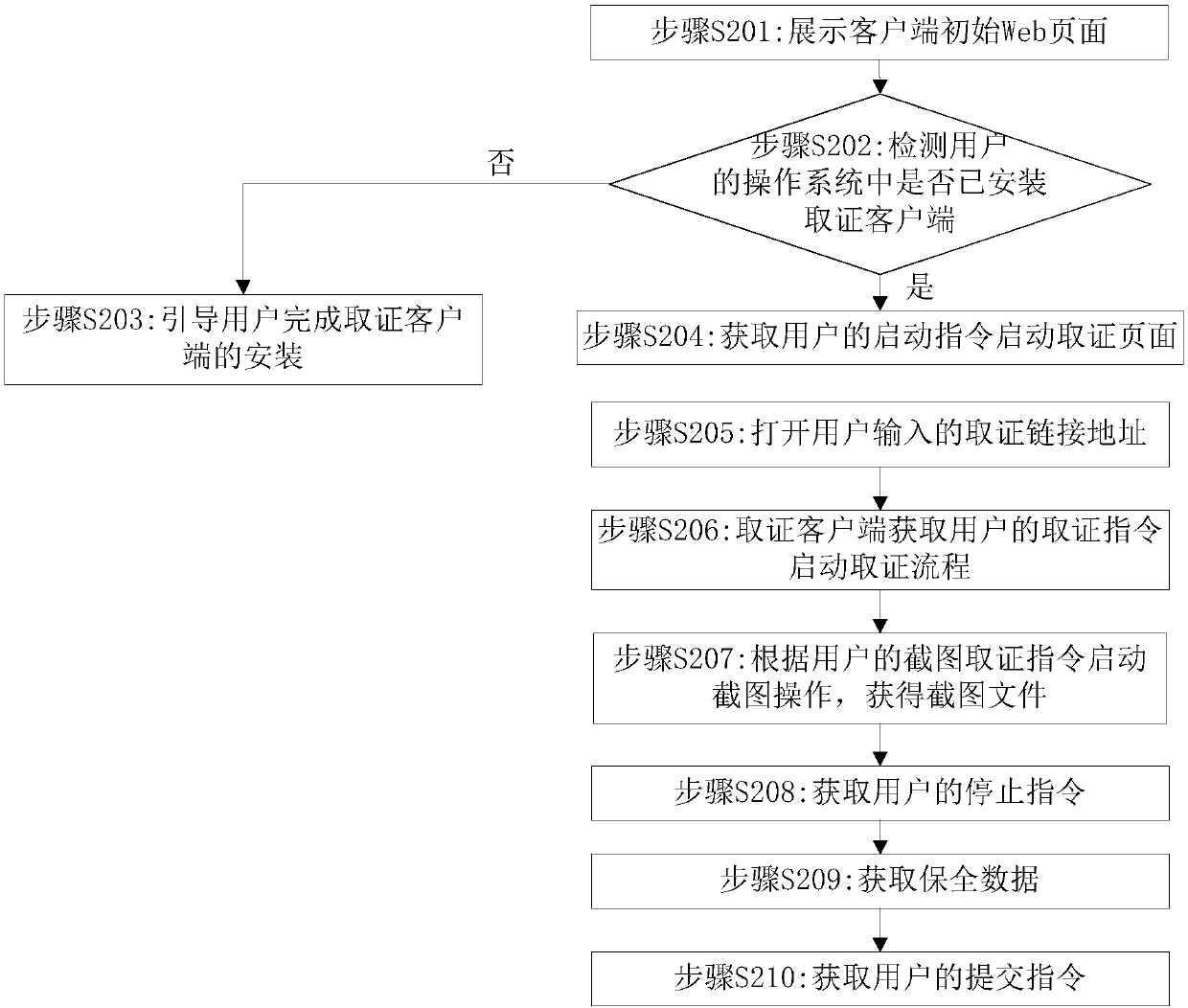
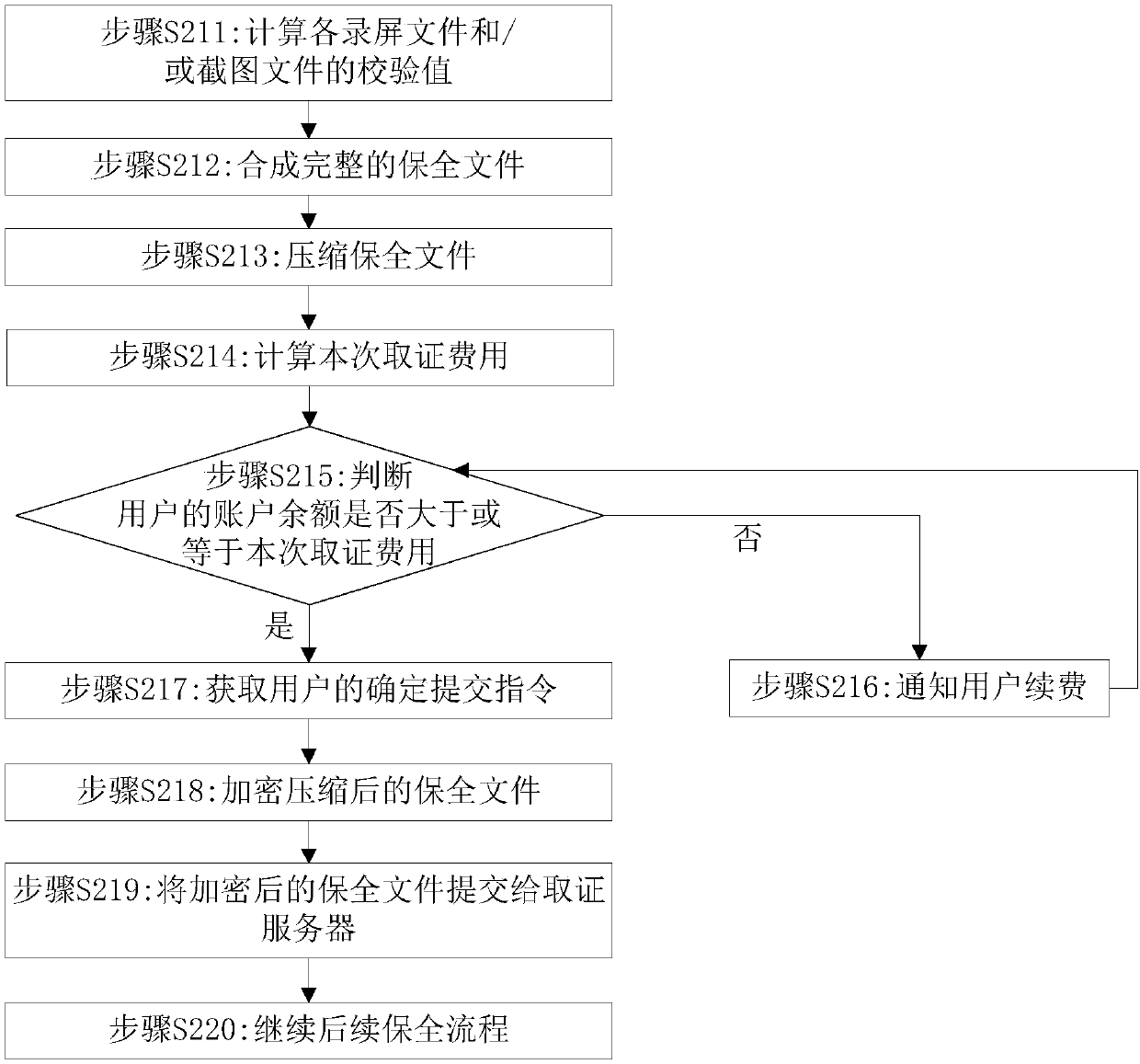
Electronic evidence collection method and device
InactiveCN107688754AGuaranteed reliabilityNot tampered with by addition or subtractionData processing applicationsDigital data protectionUser inputEvidence collection
The invention discloses an electronic evidence collection method and device. The method includes the steps: acquiring an evidence collection instruction of a user, starting an evidence collection process: starting a screen recording operation according to user selection and recording an operation page displayed on a screen; and / or acquiring an evidence collection link address inputted by the user,opening at least one link page corresponding to the evidence collection link address, and capturing screenshots of the link pages; acquiring a stop instruction of the user, stopping the evidence collection process to obtain preservation data comprising a link page screenshot file and / or a screen recording file; acquiring a submission instruction of the user, and submitting the obtained preservation data to an evidence collection server. Real and effective electronic evidences can be acquired, and reliability of the electronic evidences is ensured.
Owner:国信嘉宁数据技术有限公司
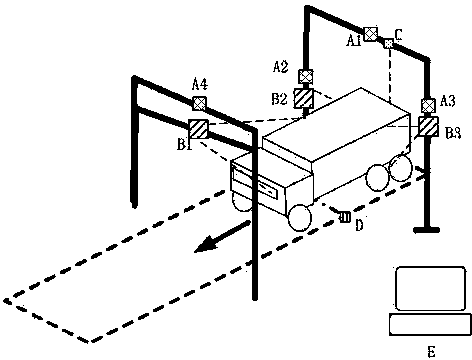
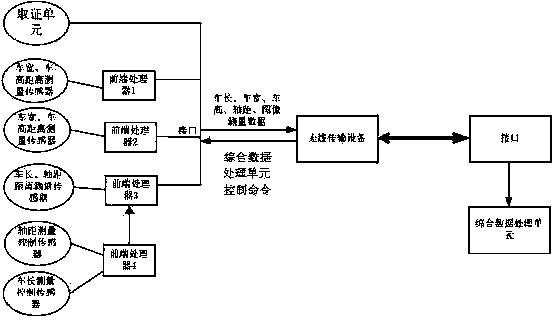
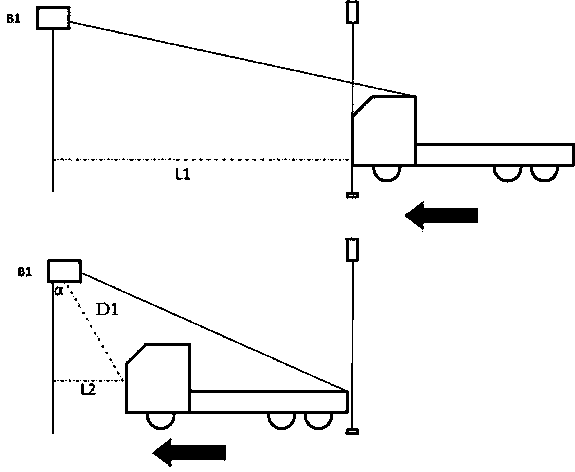
Vehicle outline and wheel base automatic measuring system and measuring algorithm
InactiveCN103954222ASimple structureOptimize the installation positionUsing optical meansTime conditionSynthetic data
The invention discloses a vehicle outline and wheel base automatic measuring system and a measuring algorithm. The vehicle outline and wheel base automatic measuring system comprises three distance measuring units, an outline measurement control unit, a wheel base measurement control unit, an evidence collection unit, a comprehensive data processing unit and a measurement channel. The distance measuring units, the outline measurement control unit, the wheel base measurement control unit and the evidence collection unit are arranged on the measurement channel. The three distance measuring units are the first distance measuring unit B1, the second distance measuring unit B2 and the third distance measuring unit B3 respectively. The outline measurement control unit is connected with the three distance measuring units respectively. The wheel base measurement control unit is connected with the first distance measuring unit B1. The distance measuring units are connected with the comprehensive data processing unit. The evidence collection unit is used for monitoring and recording the real-time condition of running of a detected vehicle. The vehicle outline and wheel base automatic measuring system can automatically measure vehicle outline data including the length, width and height of the vehicle and wheel base data of the vehicle, ensure the measuring accuracy and improve the measuring efficiency.
Owner:NANJING UNIV OF SCI & TECH
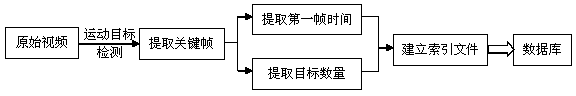
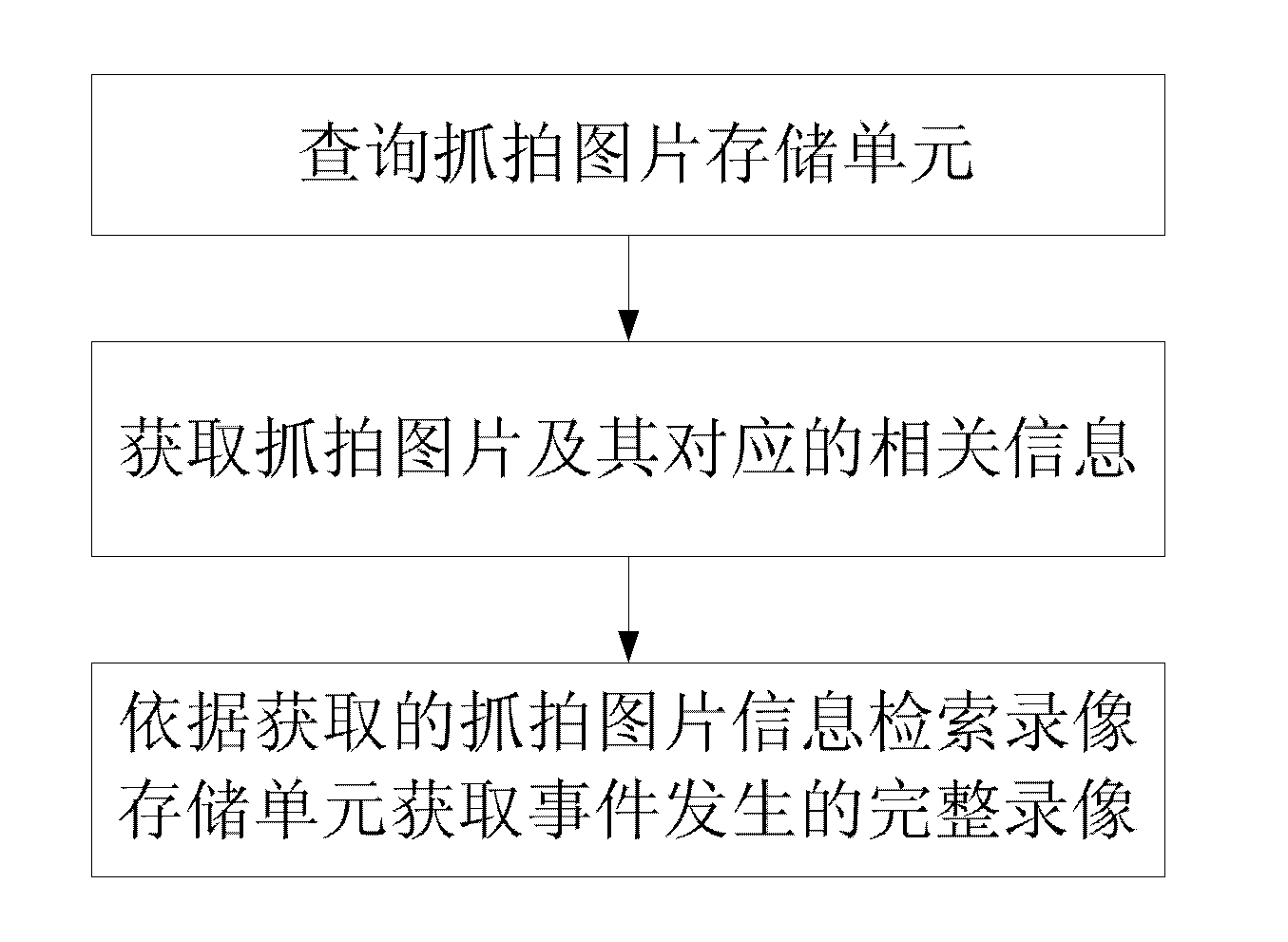
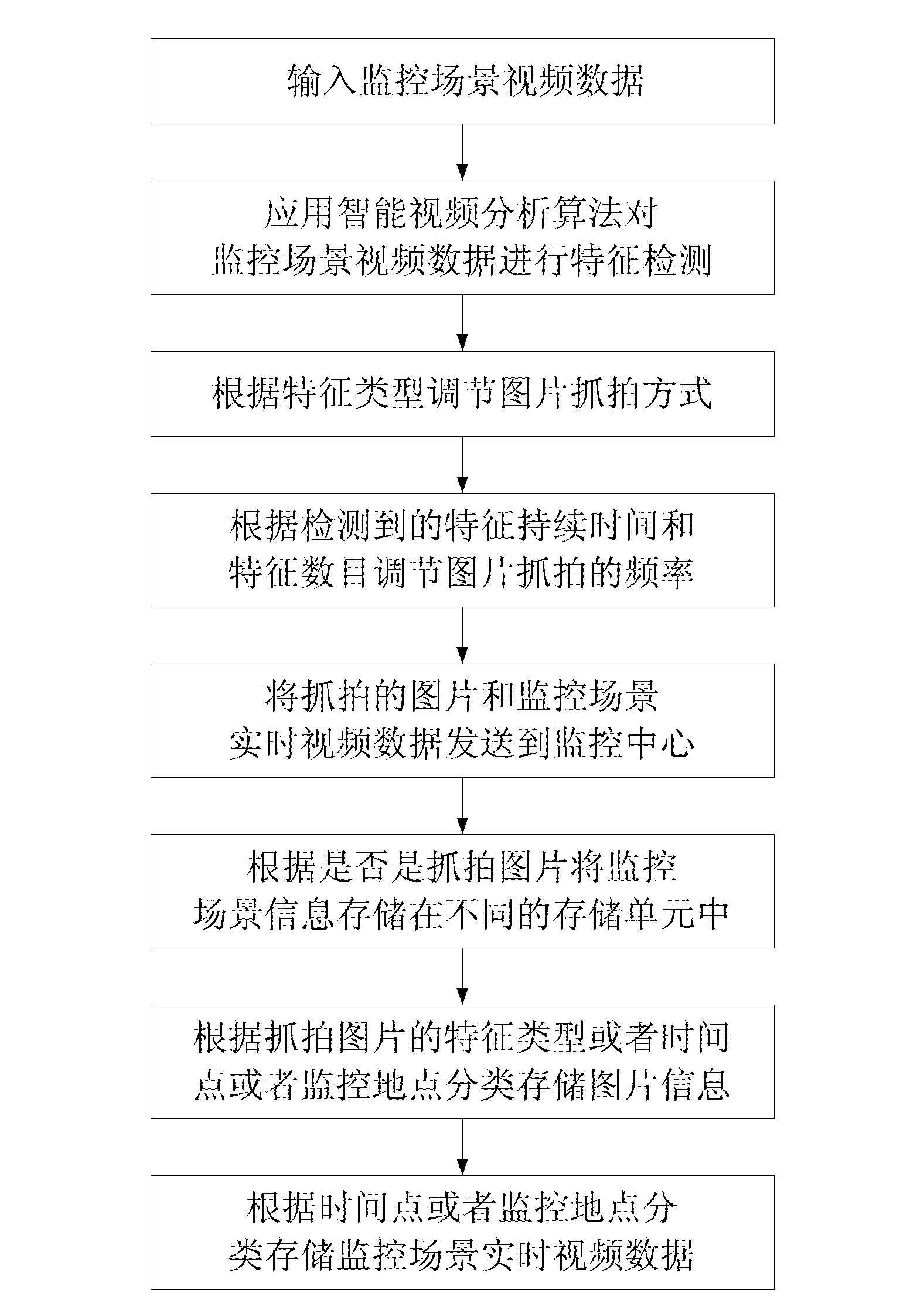
Video surveillance scene information classifying and storing method and search method
InactiveCN103049460AQuick searchImprove effectivenessClosed circuit television systemsSpecial data processing applicationsFace detectionVideo monitoring
The invention discloses a video surveillance scene information classifying and storing method. Firstly, a face detection or plate number detection technology and other technologies are applied to process surveillance scene video data of a video processing portion, and when face or plate number characteristics are found, a video acquiring device is controlled to snapshot images and record relevant information of the snapshot images. In addition, the snapshot images are stored in real time according to a preset strategy, and accordingly classification and storage of surveillance scene information are achieved. When the method is applied to investigation and evidence collection after an event, stored videos can be quickly indexed by querying the snapshot images and the relevant information, and complete videos of the event can be obtained.
Owner:TIANJIN YAAN TECH CO LTD
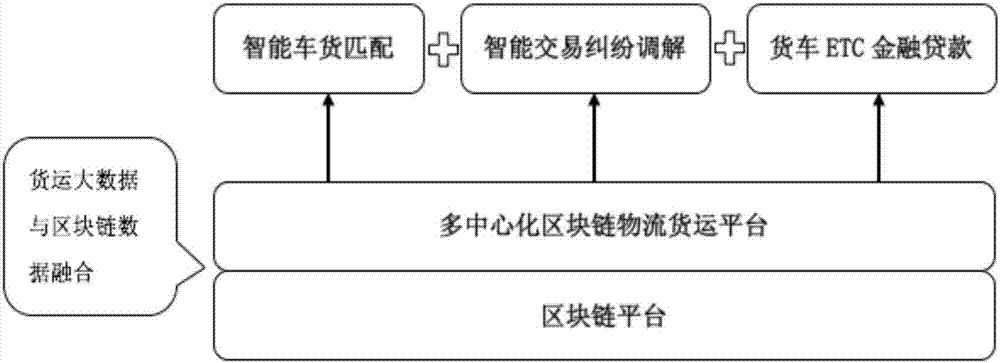
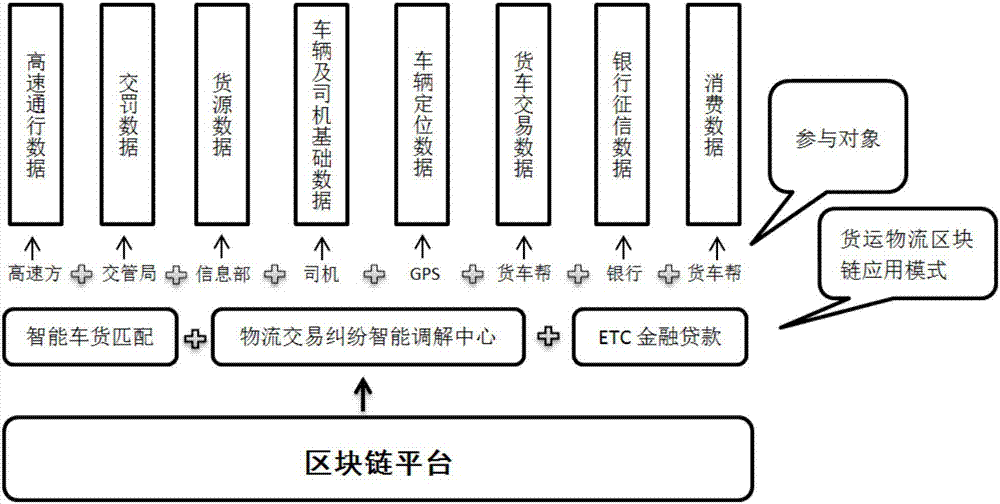
Freight logistics application method based on block chain
InactiveCN107122937ASolve the problem of mutual mistrustVerify authenticityFinanceLogisticsLogistics managementData sharing
The invention relates to the field of freight logistics application, specifically discloses a freight logistics application method based on a block chain and is to solve the problem of large data evidence collection difficulty in the later freight logistics link caused since all links in the freight logistics process are mutually independent, and data cannot be shared. The method is characterized by collecting freight logistics object data and establishing sub-block chains, and combining the sub-block chains to establish a block chain platform, thereby realizing trustworthy data sharing in the whole freight logistics process, enabling the data in the later freight logistics process to be scheduled, used and obtained for evidence as needed, and further promoting intelligent development of freight logistics application.
Owner:UNIV OF ELECTRONICS SCI & TECH OF CHINA
Combination flashlight and camera system
InactiveUS7646973B2Ease and convenienceSpeed up the processPrintersPoint-like light sourceEffect lightHand held
Owner:LYNK3 TECH
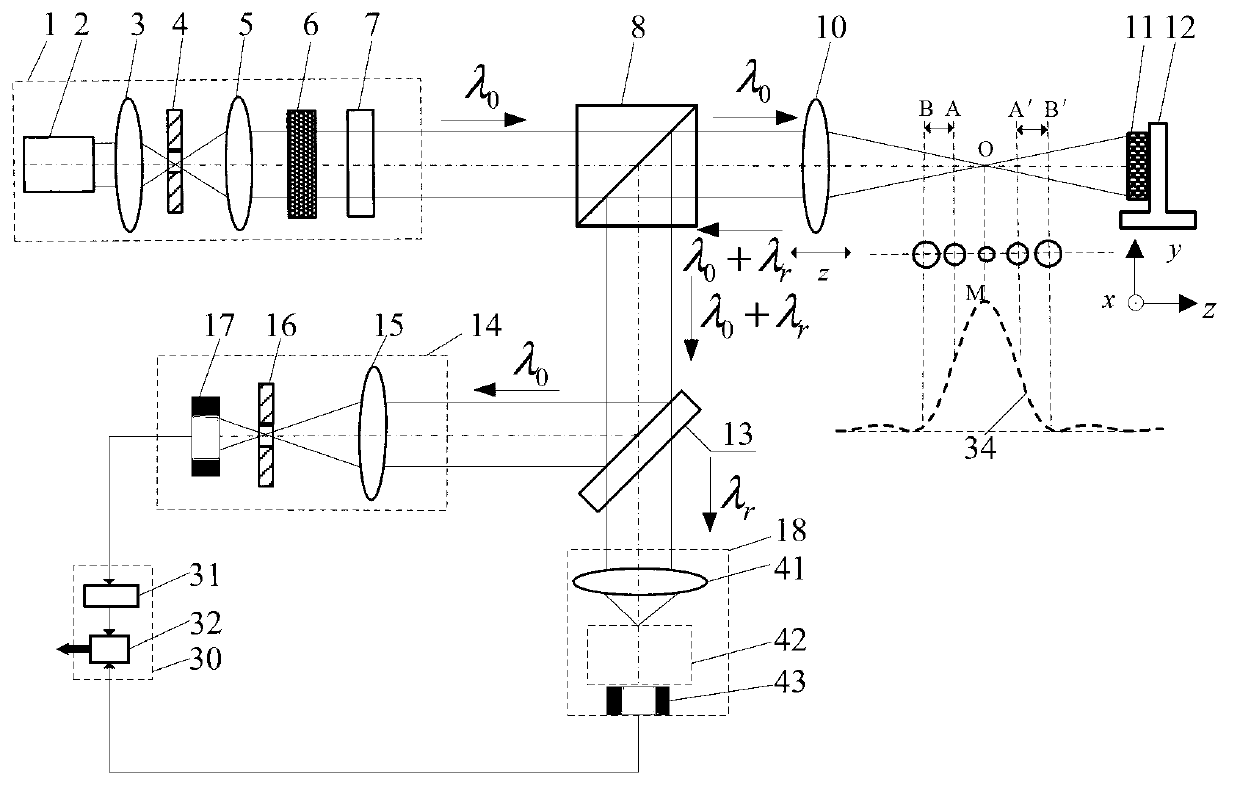
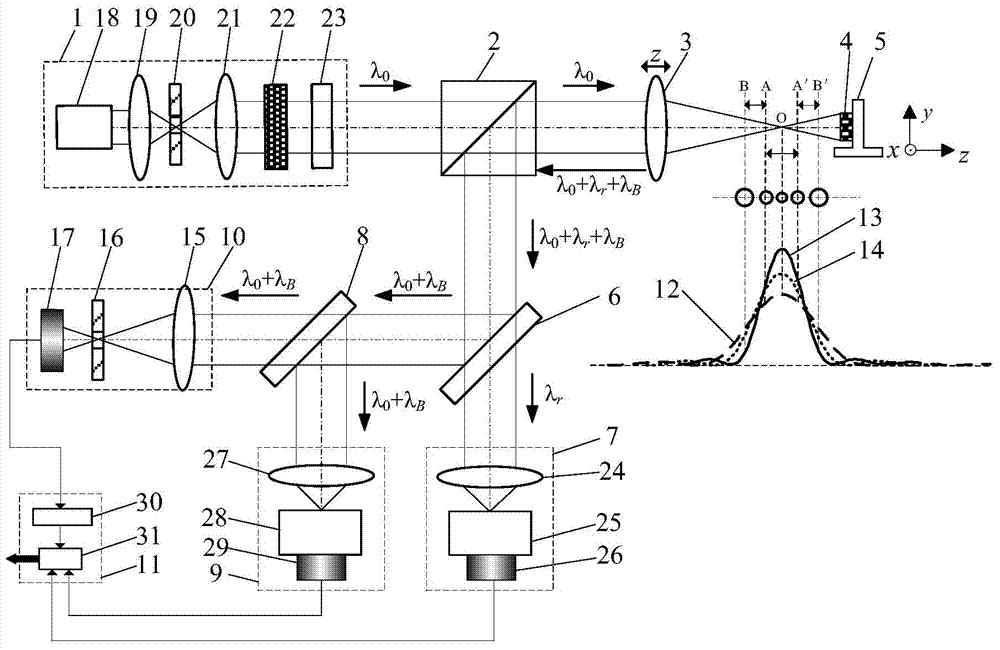
Laser confocal Brillouin-Raman spectral measurement method and apparatus
ActiveCN103940800AGood size controlEasy to testRaman scatteringElectricityThree dimensional morphology
The invention belongs to the technical field of microscopic imaging and spectral measurement and relates to a high resolution spectral imaging and detection method and apparatus which combine confocal microscopic technology and spectral detection technology together, realize integration of images and spectrums and are used for three dimensional morphology reconstruction and micro-area morphological performance parameter measurement of a variety of samples. The method and apparatus utilize Rayleigh light abandoned by a traditional confocal Raman system and confocal technology for detection of the position of a sample, employs a spectral detection system for spectral detection and uses Brillouin diffusion light abandoned by a traditional confocal Raman detection technology to test properties like elasticity and piezoelectricity of a material, thereby realizing measurement of micro-area high spatial resolution morphological parameters of a sample. The method and apparatus provided by the invention have the advantages of accurate positioning, high spatial resolution, high spectral detection sensitivity, controllable measured spot size, etc. and have wide application prospects in fields like biomedicine, evidence collection of court, micro and nano-fabrication, material engineering, engineering physics, precise metering and physical chemistry.
Owner:BEIJING INSTITUTE OF TECHNOLOGYGY
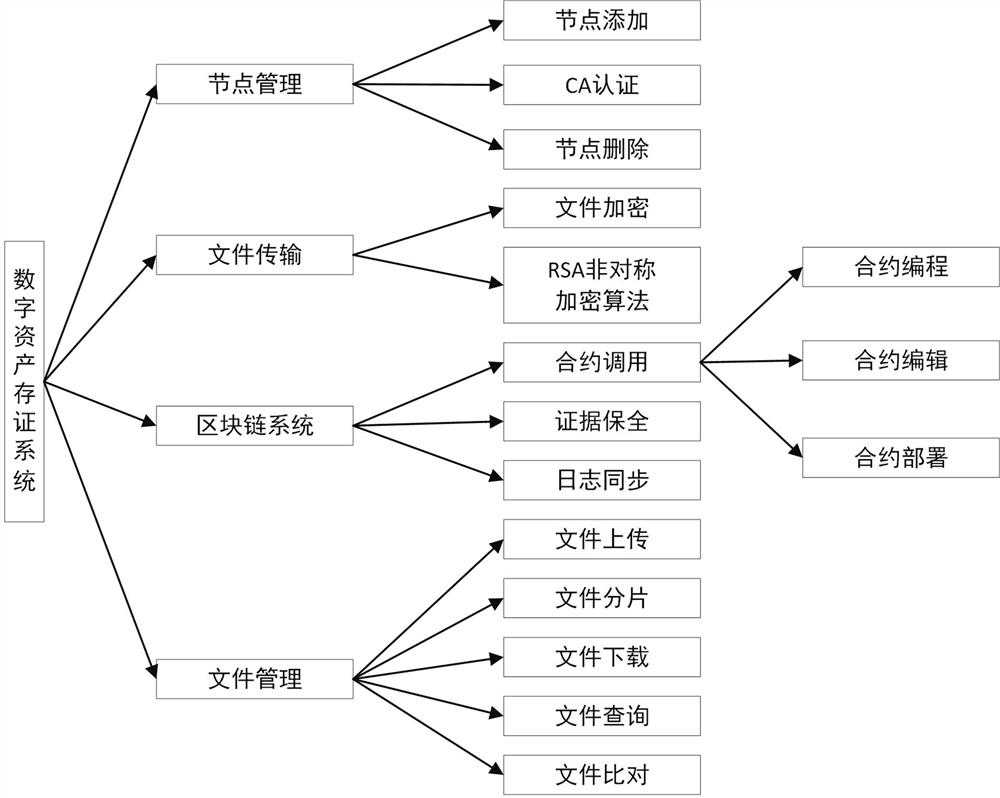
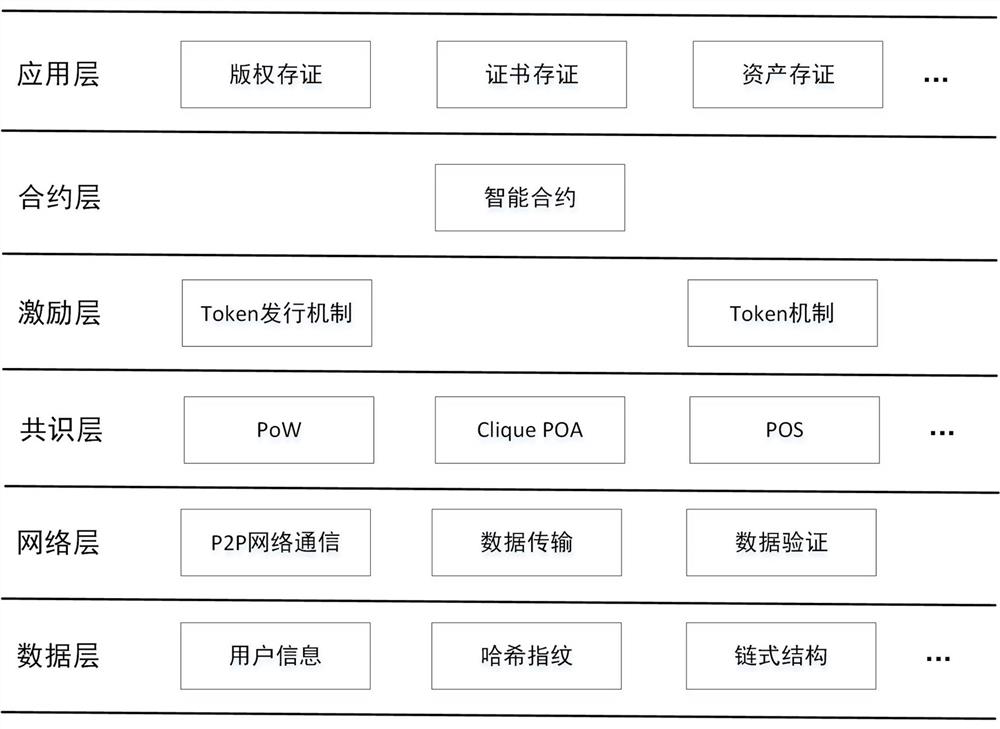
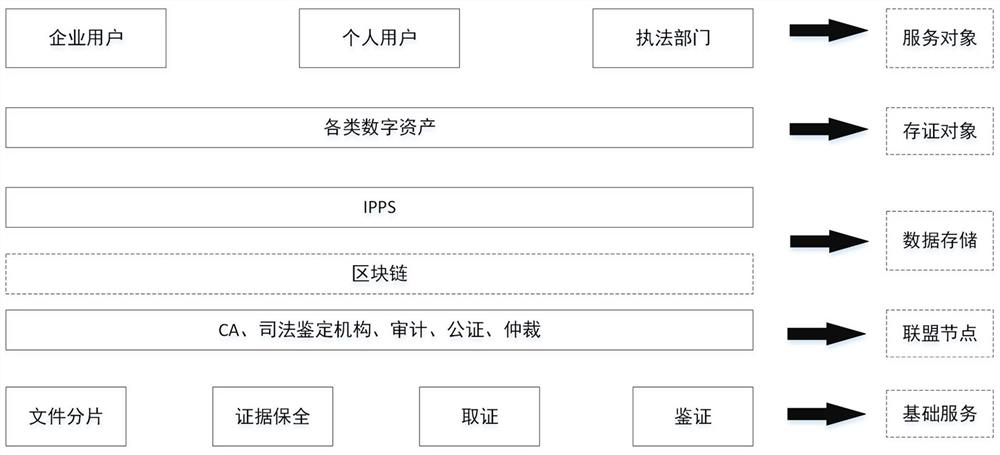
Digital asset evidence storage system based on blockchain
PendingCN111859422AImprove securityProtection securityDatabase distribution/replicationDigital data protectionUser verificationHash function
The invention provides a digital asset evidence storage method based on a blockchain. The method comprises the following steps: enabling a user to verify a node and log in; encrypting the original file; selecting nodes which are active and have few times of going wrong in the IPFS system as evidence storage nodes; distributing file fragments to the selected evidence storage node, and returning a corresponding Hash value by the IPFS system; calling an intelligent contract, and storing metadata of the file and fingerprint data obtained by performing Hash function calculation after encryption into a blockchain; screening out a main node for accounting through a PoA consensus algorithm, wherein the main node is responsible for generating blocks and packaging transaction data, and then broadcasting and synchronizing; and when authentication is needed, authorizing the authentication mechanism to access the original file and historical data stored in the blockchain, and verifying whether thedata is modified or not. According to the evidence storage method, the evidence storage file is stored based on the blockchain by utilizing the blockchain technology, meanwhile, bloating of the blockchain is avoided, the confidentiality of the uploaded file is guaranteed, and evidence collection is easier and more direct.
Owner:郑州信大先进技术研究院
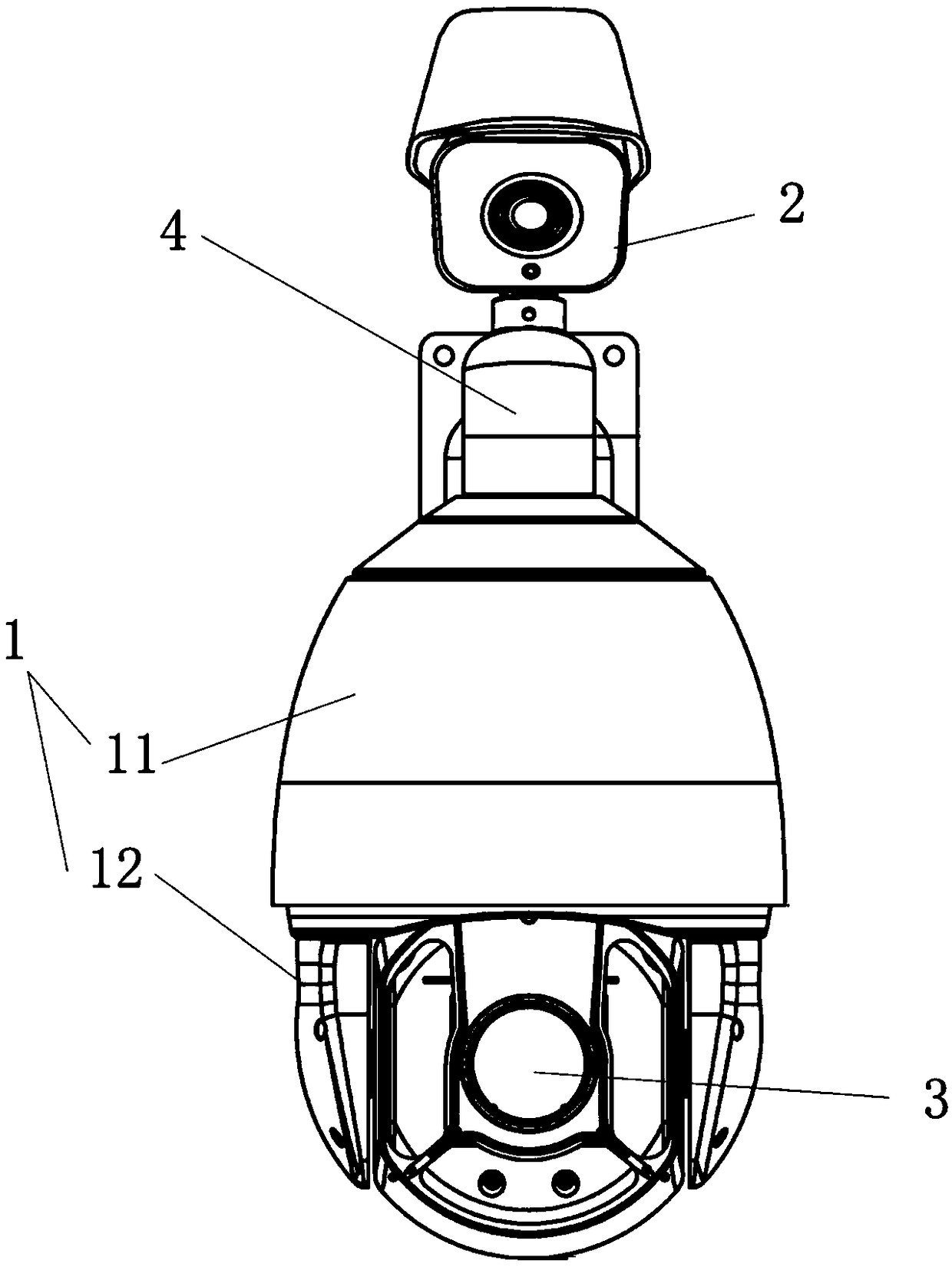
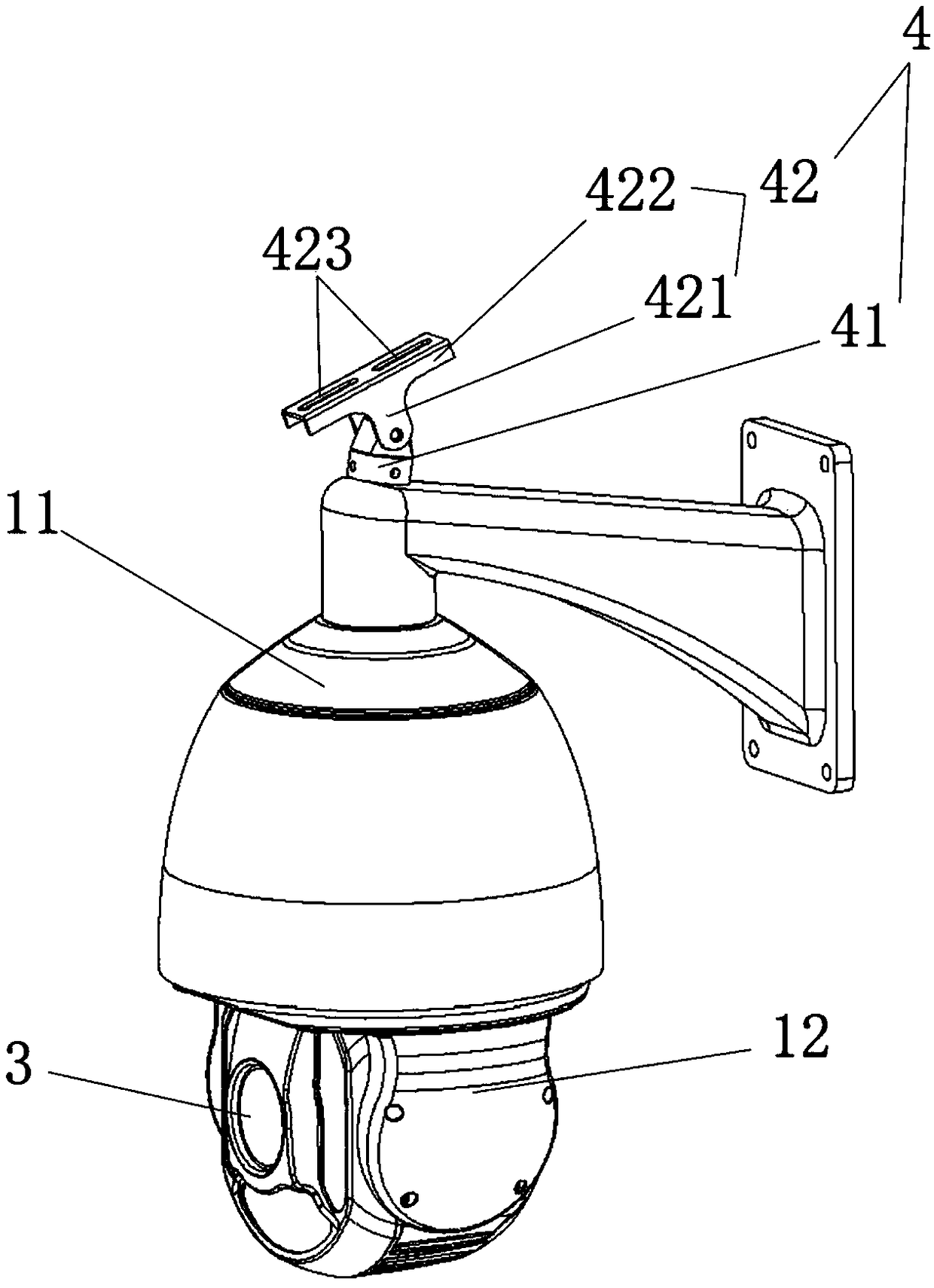
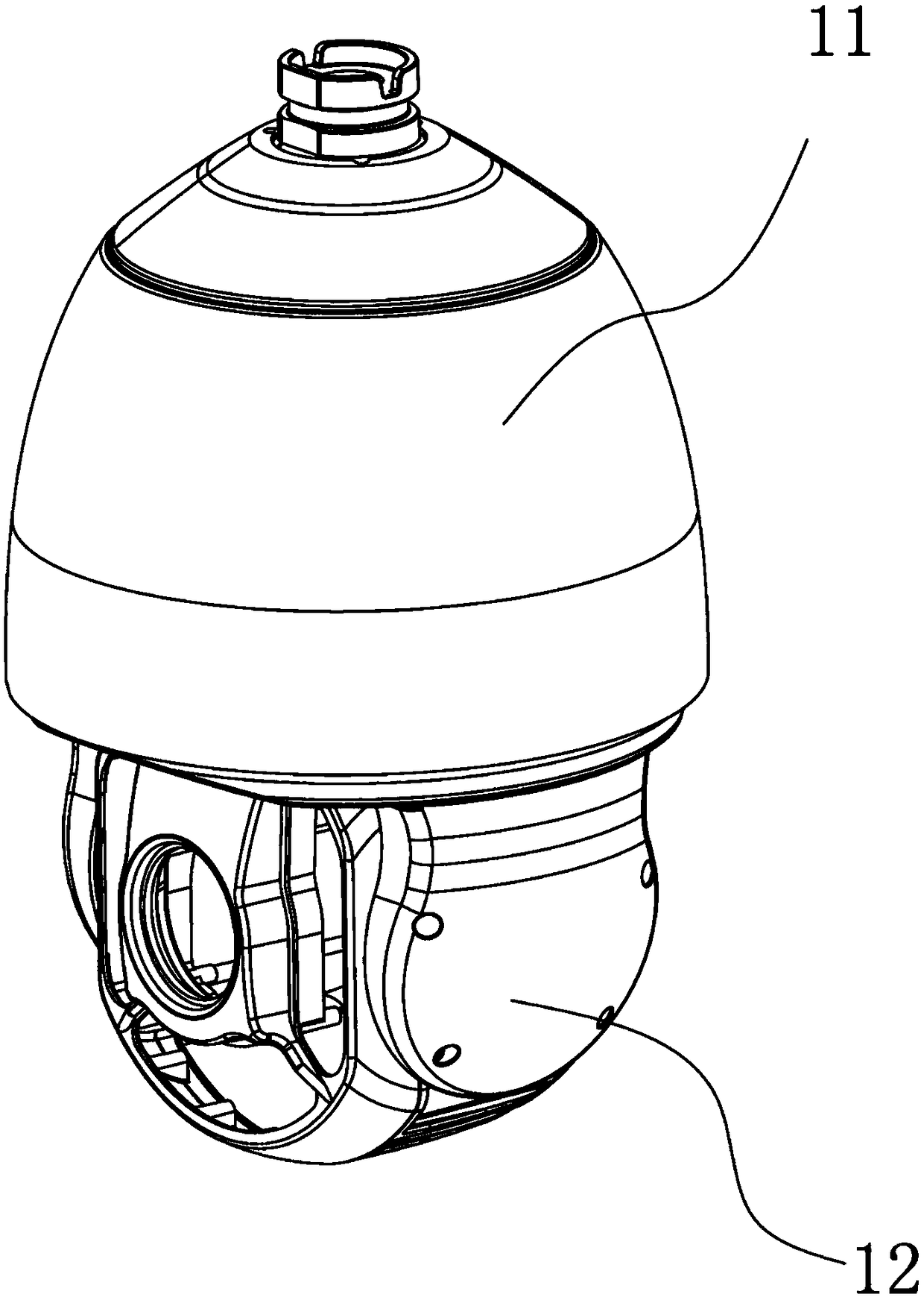
Box camera and dome camera collaborative large-scene vehicle illegal snapshot camera and vehicle illegal snapshot method thereof
PendingCN108810390AImplement trackingEffective shootingTelevision system detailsRoad vehicles traffic controlVideo monitoringEvidence collection
The invention belongs to the field of video monitoring, and particularly relates to a box camera and dome camera collaborative large-scene vehicle illegal snapshot camera and a vehicle illegal snapshot method thereof for realizing vehicle illegal automatic evidence collection based on a box camera and dome camera linkage intelligent video analysis technology. The system adopts a box camera to recognize a vehicle and a dome camera to amplify and obtain a clear license plate, and has the characteristics of unattended automatic snapshot, large snapshot range and capability of snapshotting a plurality of violations at the same time. The box camera and dome camera collaborative large-scene vehicle illegal snapshot camera comprises a rack, a box camera shooting module, a dome camera shooting module and a master control chip, wherein the box camera shooting module and the dome camera shooting module are integrated on the rack, and are respectively in communication connection with the master control chip.
Owner:AQUILLANETWORKTECH
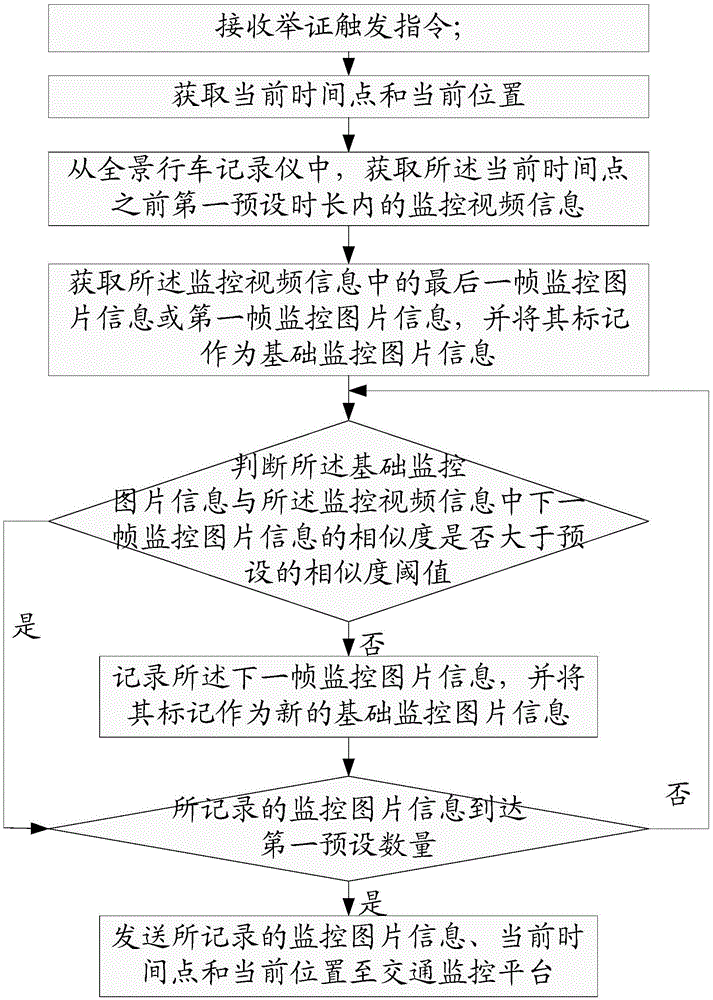
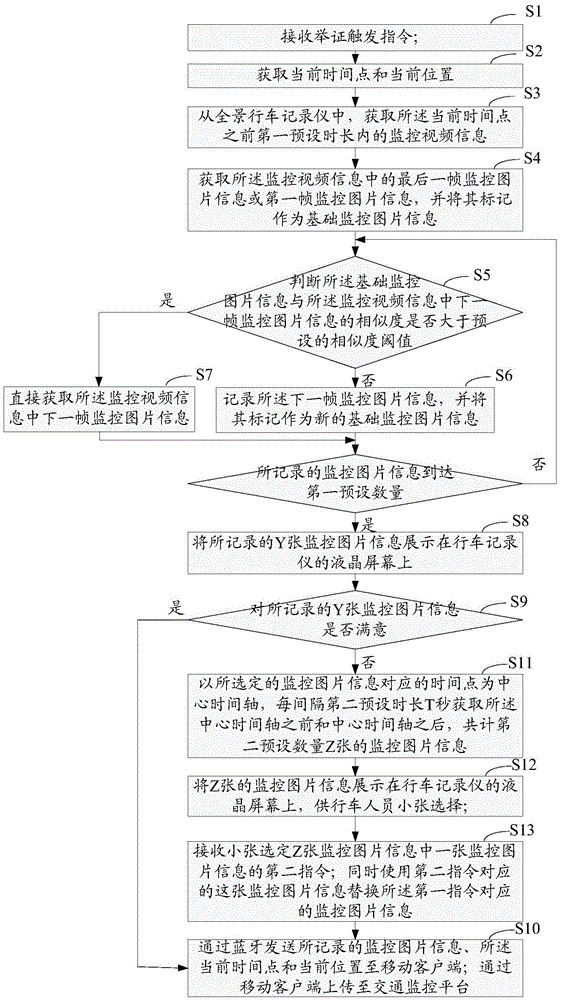
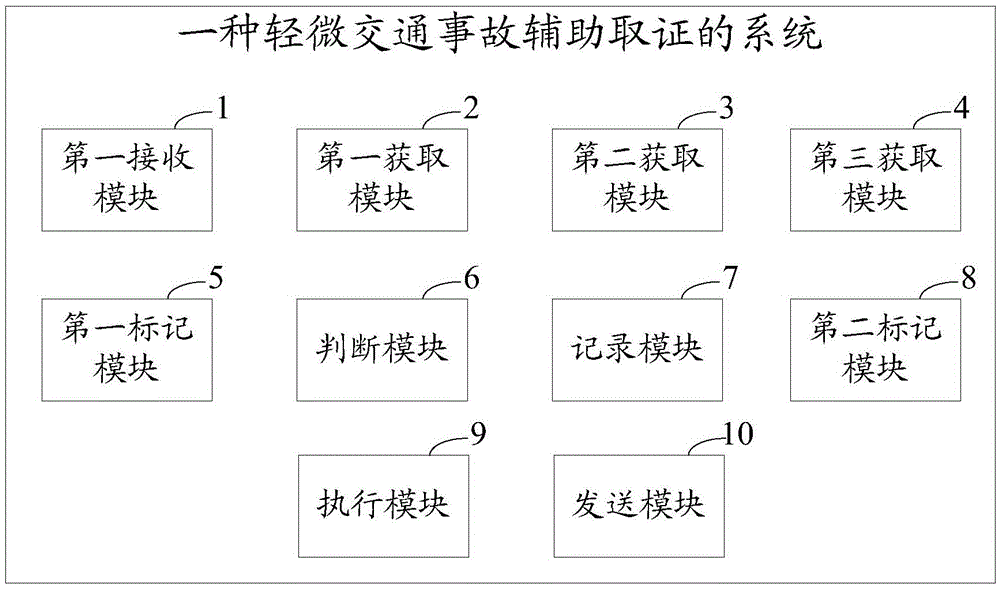
Slight traffic accident assistant evidence collection method and system
ActiveCN105679017AImprove processing efficiencyDetection of traffic movementClosed circuit television systemsTraffic accidentComputer science
The invention provides a slight traffic accident assistant evidence collection method and system. The method comprises the following steps: receiving an evidence trigger instruction; obtaining monitoring video information within a preset time period before the current time point; obtaining the last frame of monitoring picture information or the first frame of monitoring picture information in the monitoring video information, and marking the monitoring picture information as basic monitoring picture information; judging whether the similarity between the basic monitoring picture information and the next frame of monitoring picture information is larger than a preset similarity threshold value; if not, recording the next frame of monitoring picture information, and marking the next frame of monitoring picture information as new basic monitoring picture information; returning to the judgment step till the recorded monitoring picture information reaches first preset quantity; and sending the recorded monitoring picture information, the current time point and the current position to a traffic monitoring platform. The slight traffic accident assistant evidence collection method and system can obtain the monitoring picture information in different states in the accident happening process, so that an accident occurrence site can be restored, and the traffic accident disposing efficiency is improved.
Owner:FUJIAN UNIV OF TECH
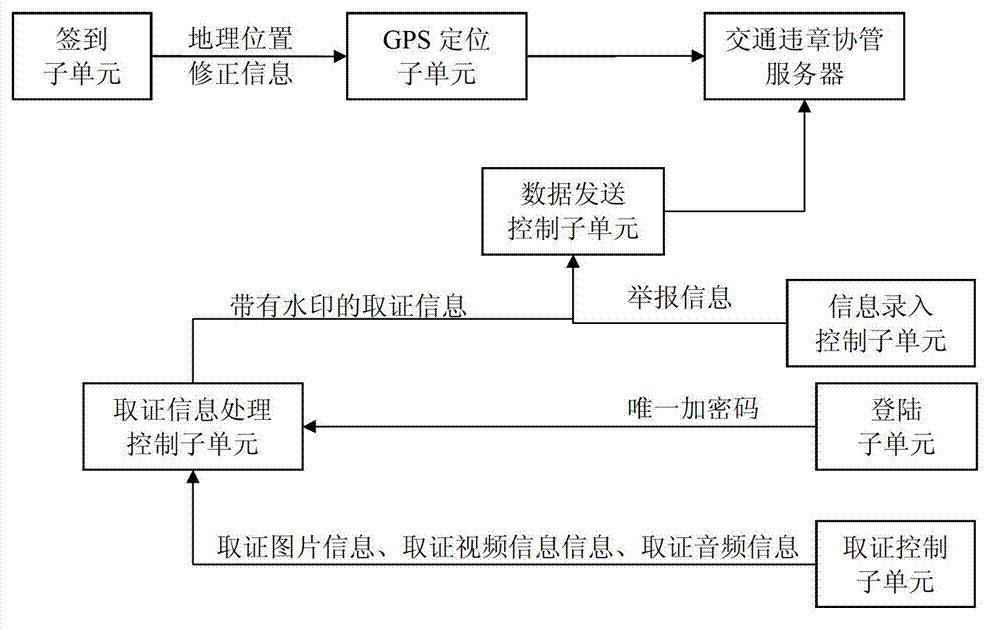
Traffic offence assistant management system based on mobile internet device
InactiveCN103116982AEfficient managementReal-time uploadDetection of traffic movementLocation information based serviceThe InternetGeolocation
The invention provides a traffic offence assistant management system based on a mobile internet device and relates to the internet technology which is applied to the traffic field. The traffic offence assistant management system based on the mobile internet device aims at designing an interconnection system which is suitable for traffic assistant management and is speedy in communication. A mobile terminal is an intelligent mobile terminal which is provided with a global position system (GPS) location module and near field communication (NFC) modules. The mobile terminal can achieve data interaction among traffic offence assistant management servers through a wireless network. A plurality of hot points are NFC modules which are installed in a traffic network and are provided with precise geographic information in an embedded mode. A traffic offence assistant management software module is embedded in the mobile terminal. The software module comprises a register subunit, a sign in subunit, a GPS location subunit, an evidence collection control subunit, an evidence collection information handling and a control subunit, an information entry control subunit, a data sending and control subunit, an information receiving and a control subunit. The traffic offence assistant management system based on the mobile internet device is suitable for traffic assistant management.
Owner:DAQING YIDA WANLIAN TECH
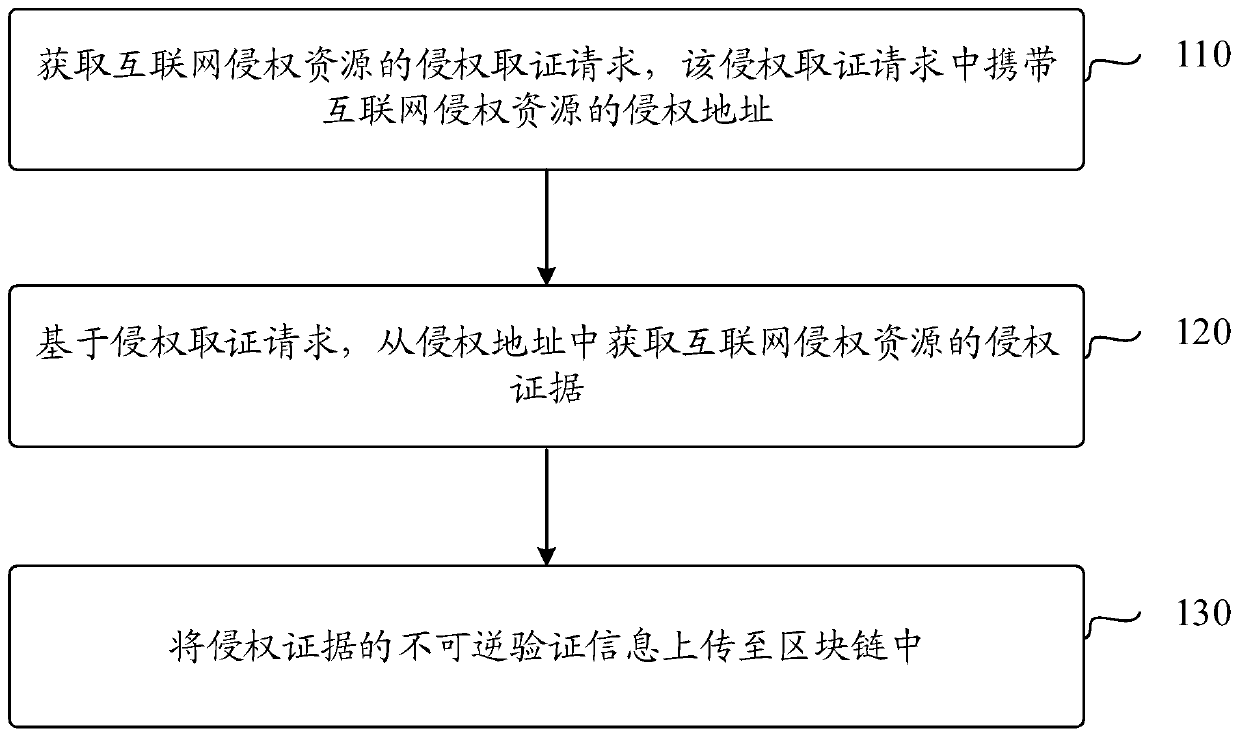
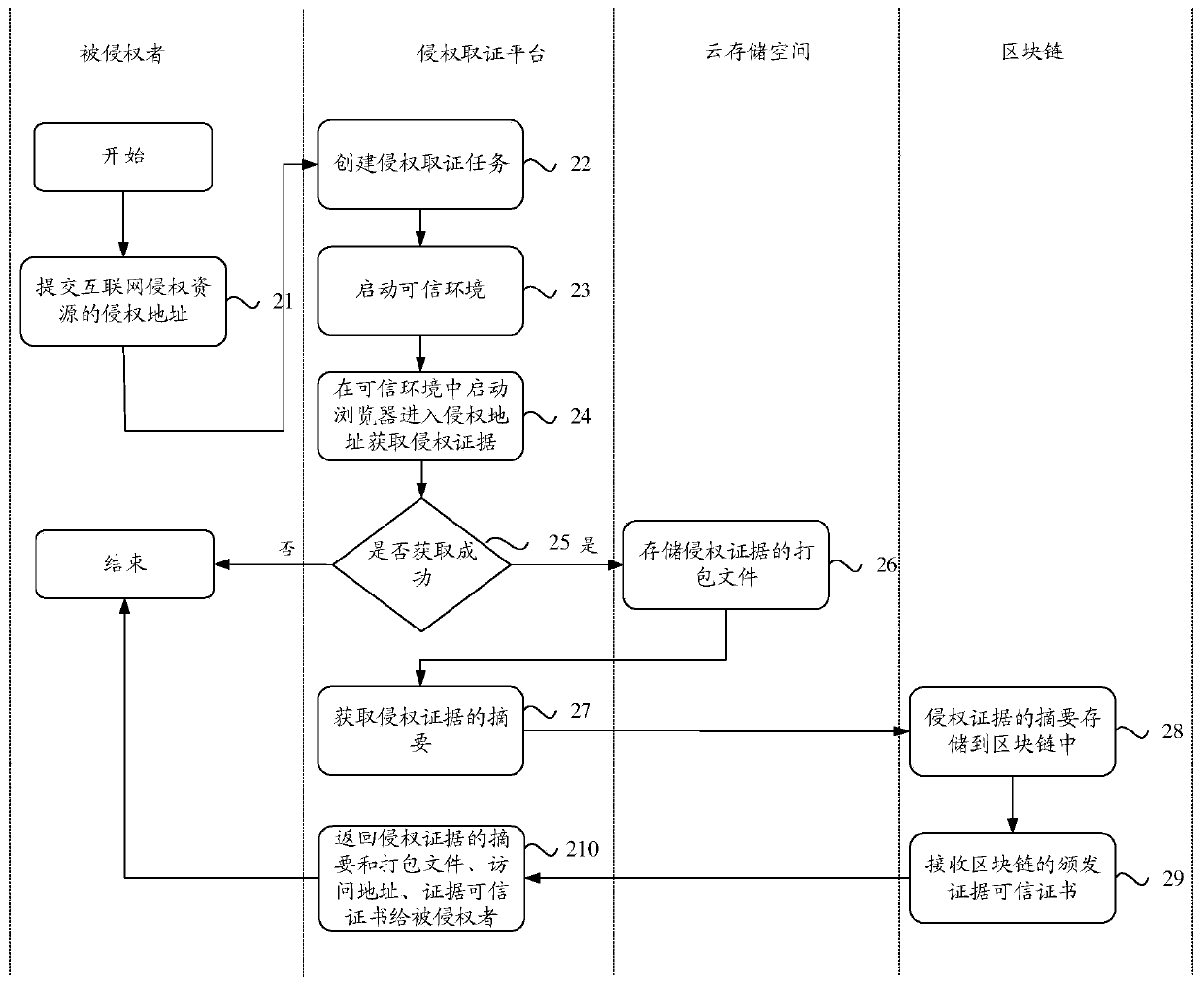
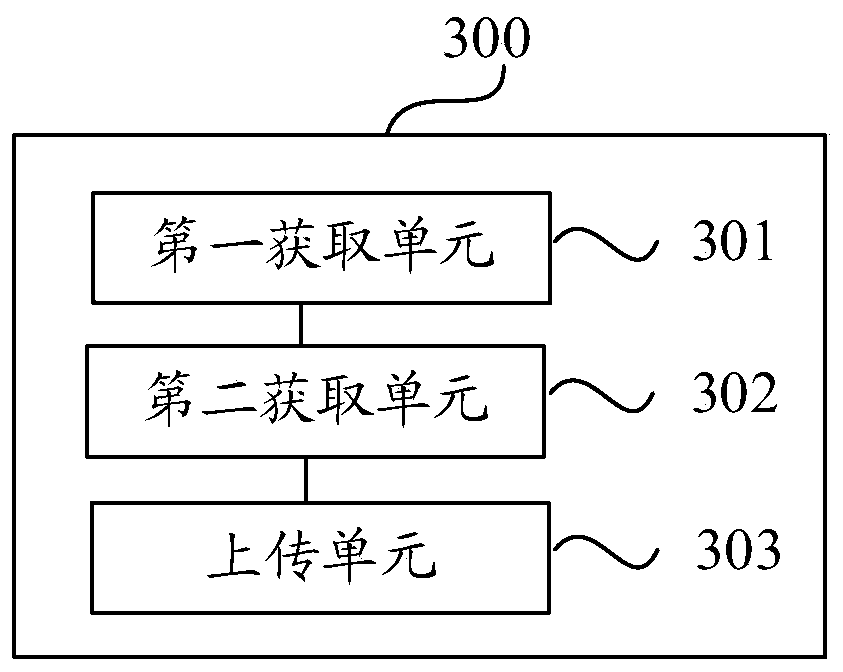
Infringement evidence storage method and device based on block chain, and electronic equipment
ActiveCN110263583AVerify the authenticityIncrease credibilityWeb data indexingDigital data protectionThe InternetElectric equipment
The invention discloses an infringement evidence storage method and device based on a block chain, and electronic equipment, and the method comprises the steps: obtaining an infringement evidence collection request for Internet infringement resources, the infringement evidence collection request carrying an infringement address of the Internet infringement resources; acquiring infringement evidence of the Internet infringement resource from the infringement address based on the infringement evidence collection request; and uploading the irreversible verification information of the infringement evidence to the block chain.
Owner:ADVANCED NEW TECH CO LTD
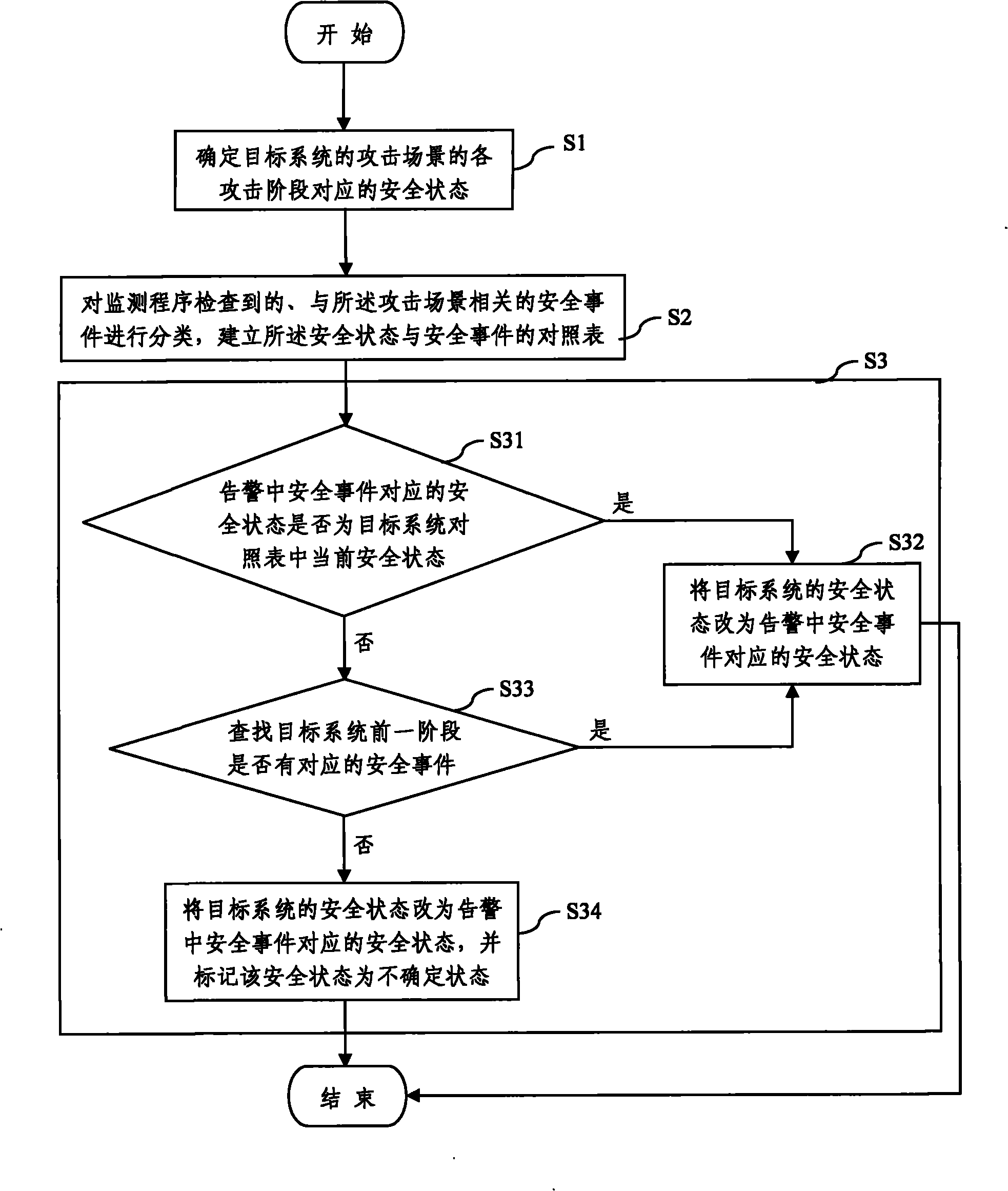
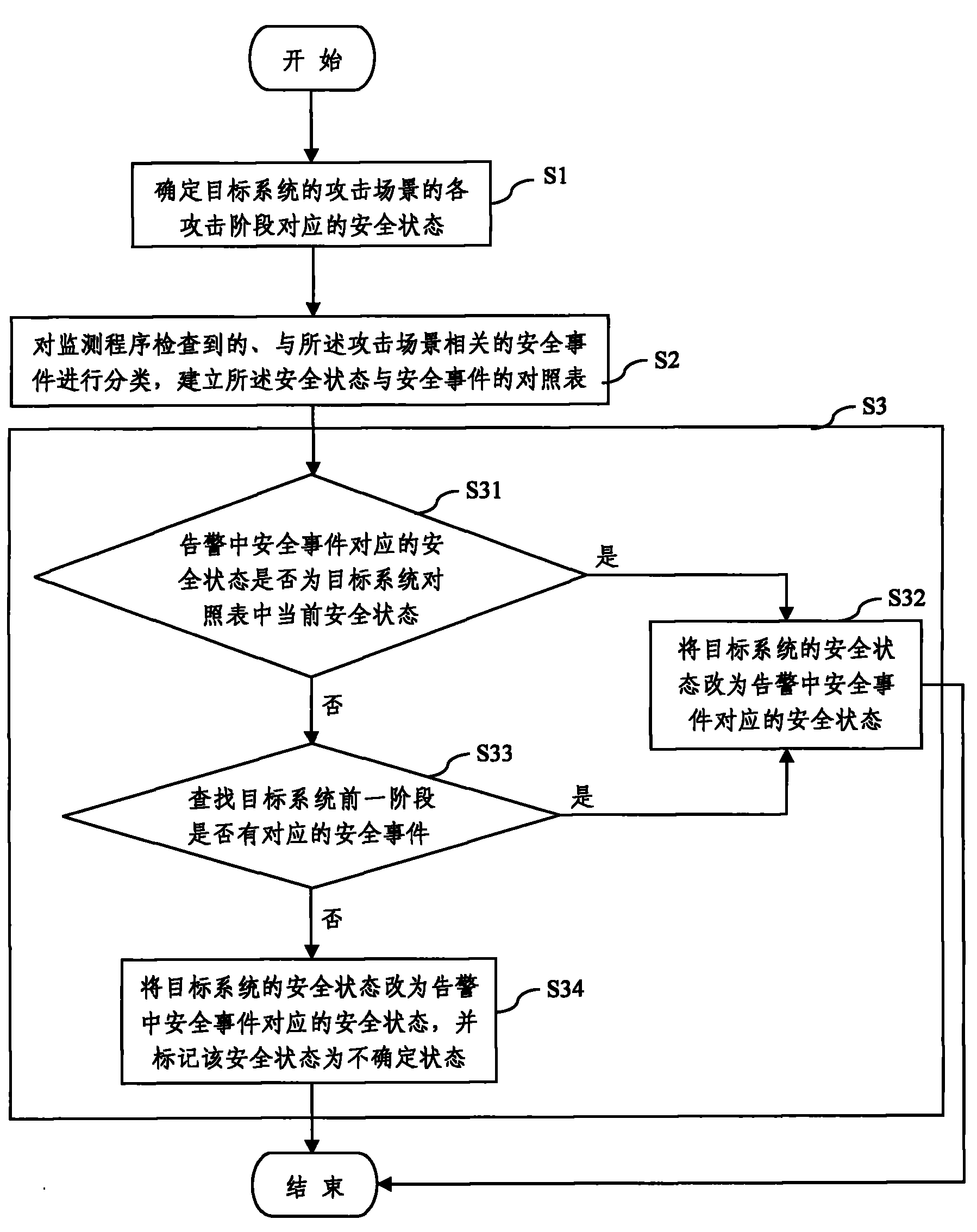
Safety monitoring correlation analysis method based on state machine
The invention discloses a safety monitoring correlation analysis method based on a state machine, which comprises the following steps: determining the safety state corresponding to attack phases of an attack scenario of a target system, the attack scenario is a safety event set which is generated when interdependent interactive behaviors with time order occur; categorizing the safety events which are inspected by a monitoring program of the target system and relative to the attack scenario and establishing a comparison table of the safety state and the safety events; and inspecting and recording the safety state of the target system according to the comparison table. In the condition of guaranteeing the sustainable system running speed, the method can store the safety state of assets for a longer time; the method can inspect distributed system attacks; in the condition of not defining an accurate attack scenario, the method can determine the safety state of the system; and the method can analyze the attacked track of the system and provide evidence for investigation and evidence collection.
Owner:ULTRAPOWER SOFTWARE
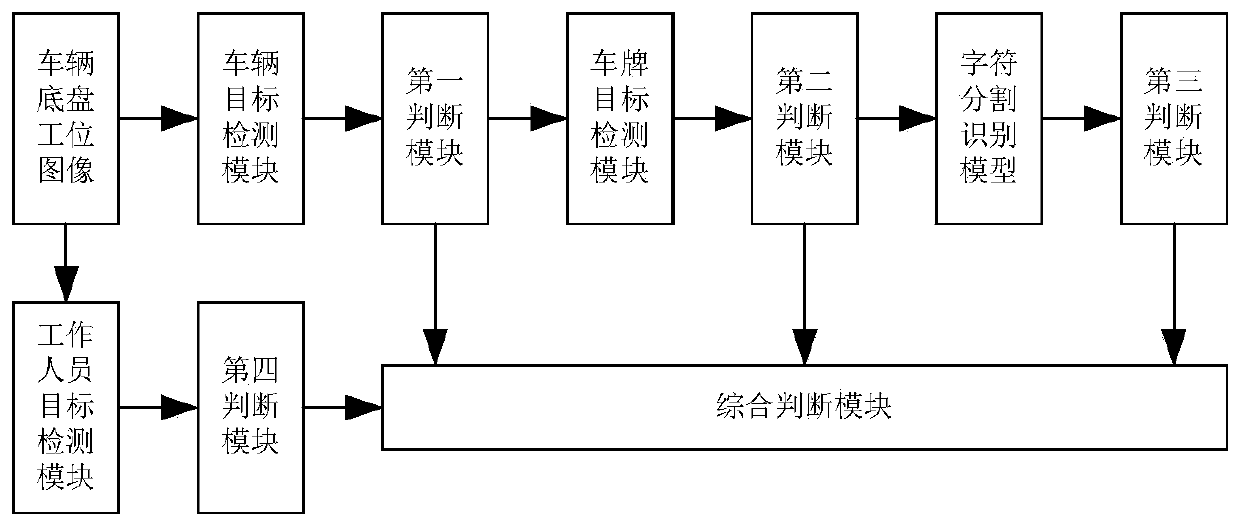
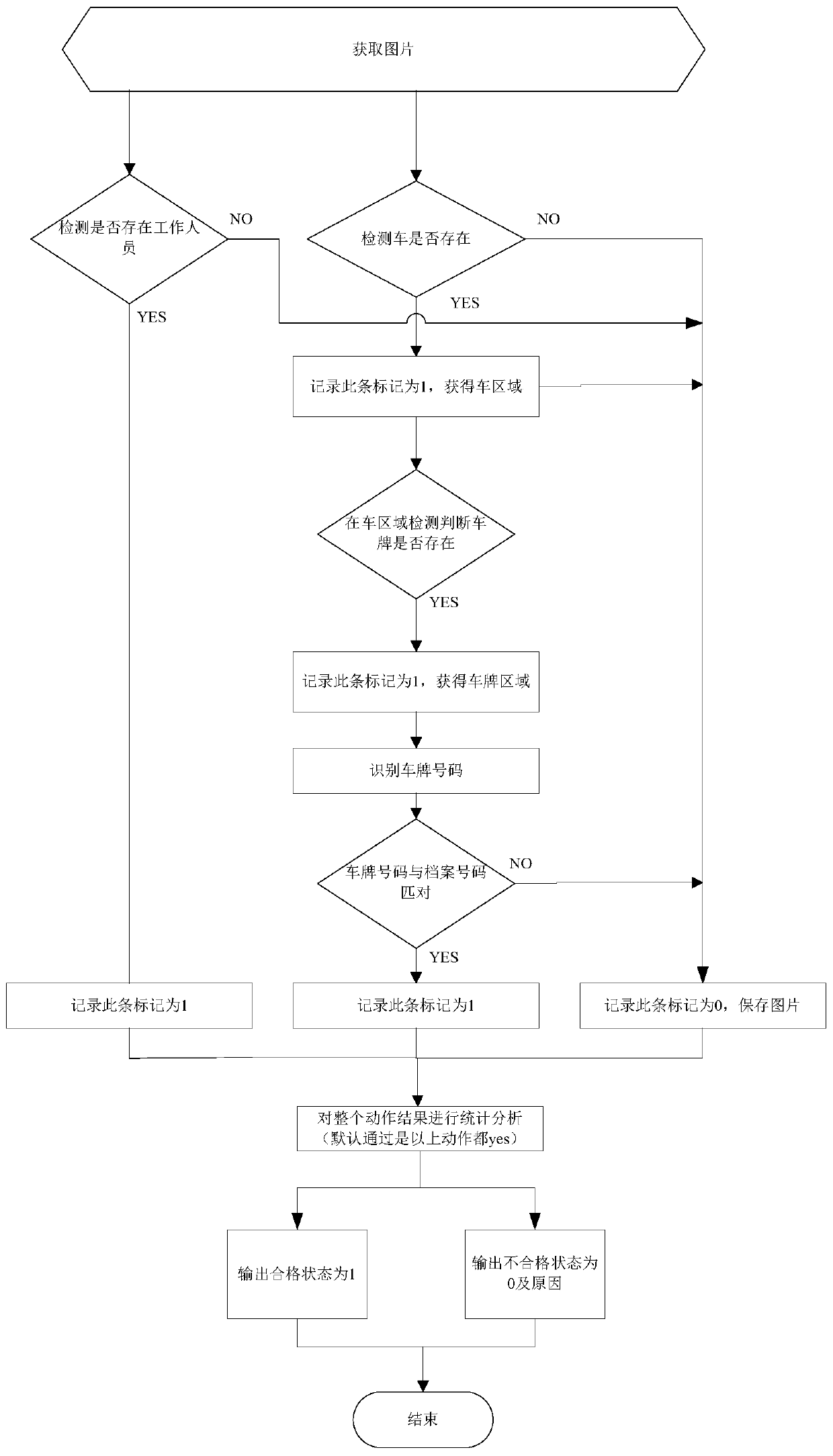
A vehicle chassis detection method based on deep learning
InactiveCN109784326AGuarantee justiceGuaranteed to be openCharacter and pattern recognitionPattern recognitionStatistical analysis
The invention discloses a vehicle chassis detection method based on deep learning. The method comprises the following steps: obtaining a to-be-detected vehicle chassis image; Detecting a vehicle chassis image by adopting a vehicle target detection model, and judging and extracting a vehicle region image; Detecting the vehicle area image by adopting a license plate target detection model, and judging and extracting the license plate area image; Detecting the license plate number area by adopting a character segmentation recognition model to recognize the license plate number, and matching a recognition result with the archived license plate number; Detecting the vehicle chassis image by adopting a worker target detection model, and judging whether a worker exists in the vehicle chassis image or not; And counting and analyzing the action result of the whole process. According to the invention, license plate number automatic verification matching inspection and chassis station worker inspection are realized, and unpassed verification images and reasons can be sent back to the server to be saved for evidence collection, so that manpower is saved, and justice and disclosure of verification work are ensured.
Owner:上海眼控科技股份有限公司
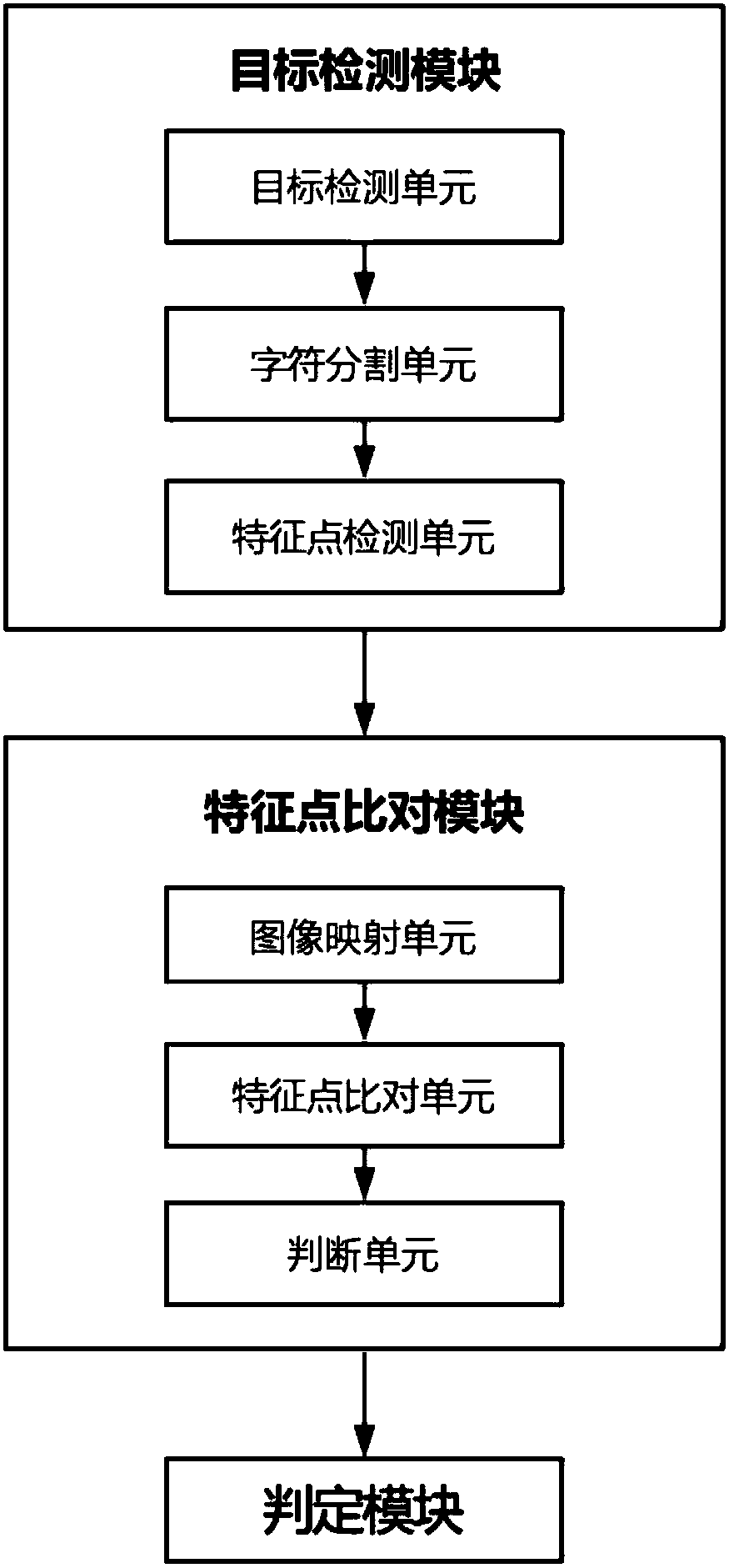
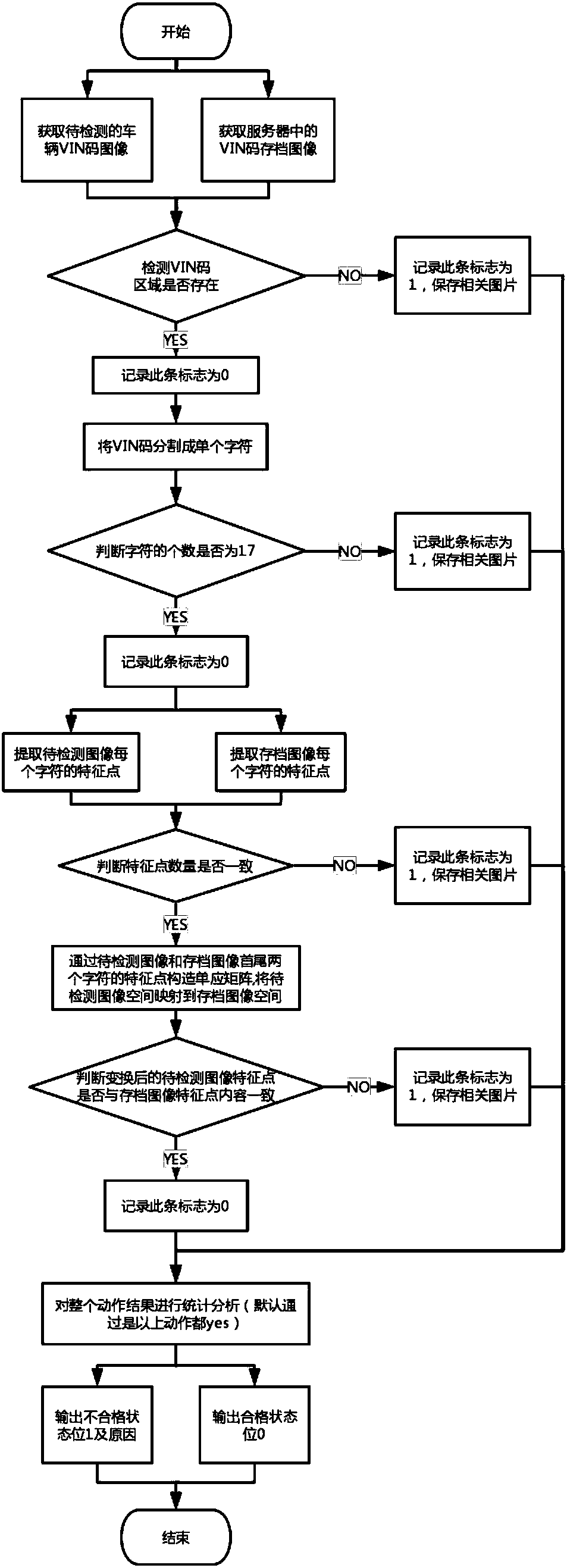
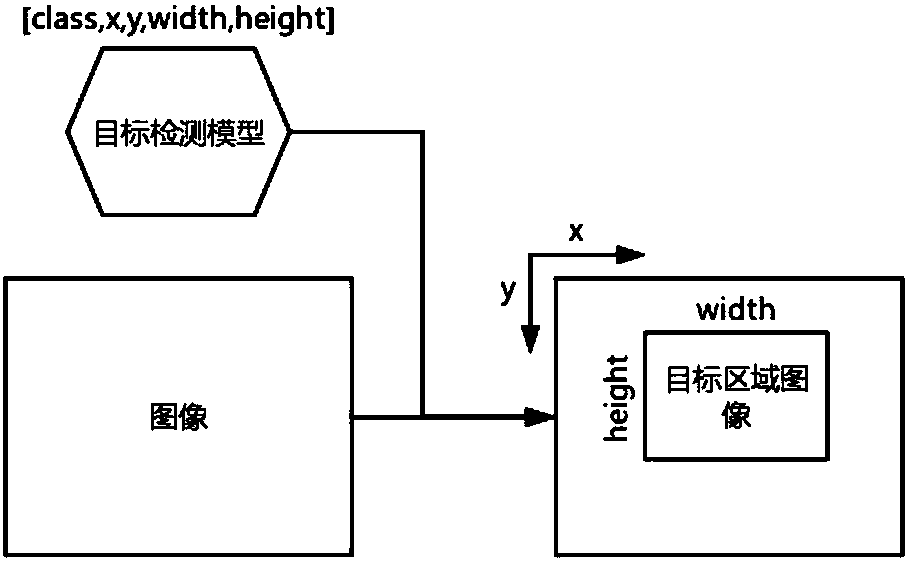
Vehicle VIN code tamper detection system and method for vehicle annual inspection
InactiveCN107818322ARealize automatic calibrationGuarantee justiceCharacter recognitionSystem structureEvidence collection
The invention discloses a vehicle VIN code tamper detection system and method for vehicle annual inspection. The system structurally comprises a target detection module, a feature point comparison module and a judgment module, wherein the target detection module is composed of a target detection unit, a character segmentation unit and a feature point detection unit; the feature point comparison module comprises an image mapping unit, a feature point comparison unit and a judgment unit; and the judgment module judges whether a vehicle VIN code passes temper inspection or not according to checking standards, an inspection success identifier is directly returned if the vehicle VIN code passes the tamper inspection, and a reason for failure inspection and a picture are returned if the vehicleVIN code fails the tamper inspection. The vehicle VIN code temper detection system and method are mainly applied to vehicle VIN code temper detection in annual inspection of motor vehicles, automaticchecking for VIN code tamper is achieved, and a checking image and reason for failure inspection can be returned to a server for storage and evidence collection at the same time, thereby not only saving manpower, but also ensuring the fairness and the openness of the checking work.
Owner:上海眼控科技股份有限公司