Method and device of detection processing of core-level rootkit
A processing method and a kernel-level technology, applied in the computer field, can solve problems such as the inability to detect the recovery of a kernel-level rootkit system well, and achieve the effect of ensuring safe operation and improving reliability.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0053] The invention provides a kernel-level rootkit detection and processing method and a related system. In order to make the object, technical solution and effect of the present invention more clear and definite, the present invention will be further described in detail below. It should be understood that the specific embodiments described here are only used to explain the present invention, not to limit the present invention.
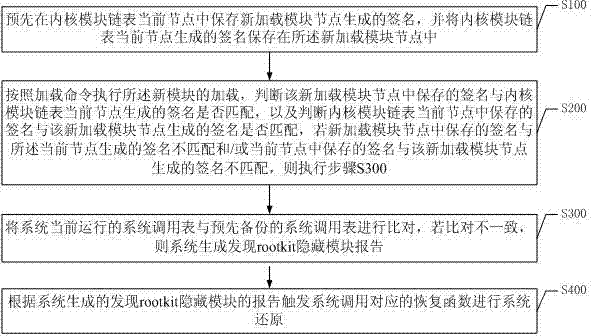
[0054] Such as figure 2 A kernel-level rootkit detection processing method shown, wherein the method includes the following steps:
[0055] S100. Pre-save the signature generated by the new load module node in the current node of the kernel module linked list, and save the signature generated by the current node of the kernel module linked list in the new load module node.
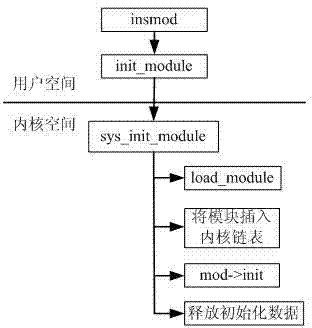
[0056] The Android system maintains the kernel module through a global two-way linked list. Each node of the linked list includes data and two pointers to the predecessor and...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More