Physical layer encryption/decryption method based on ONU (optical network unit) end time-varying keys in OFDM-PON (orthogonal frequency division multiplexing-passive optical network)
An OFDM-PON, physical layer technology, applied in the field of physical layer encryption/decryption based on the time-varying secret key at the ONU end in OFDM-PON, can solve problems such as the limitation of encryption performance, improve security, reduce complexity and complexity degree-reducing effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
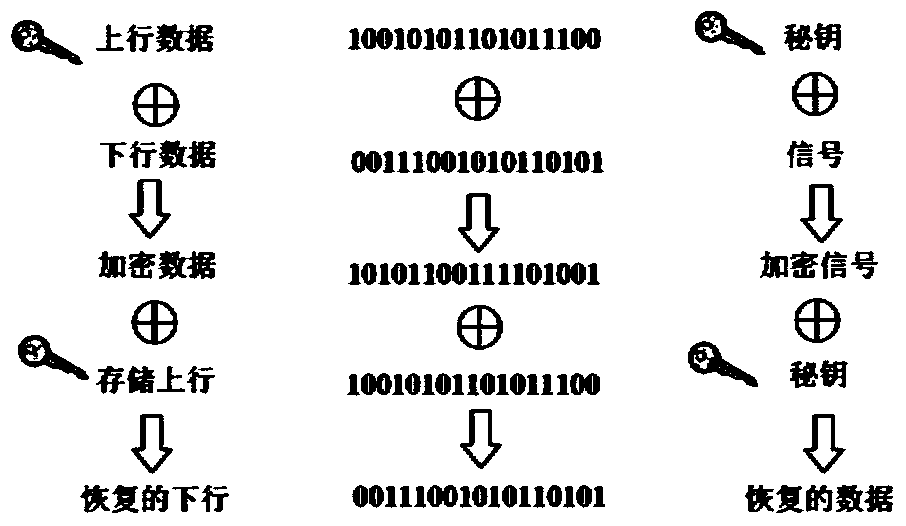
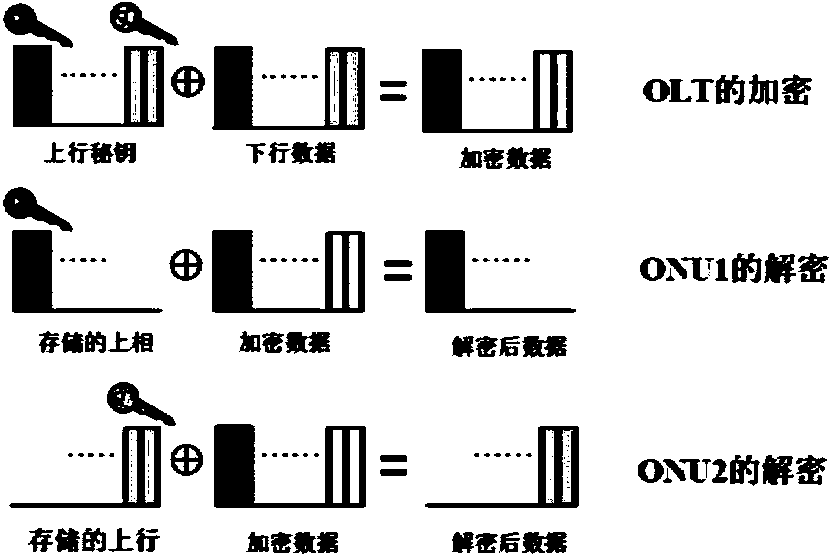
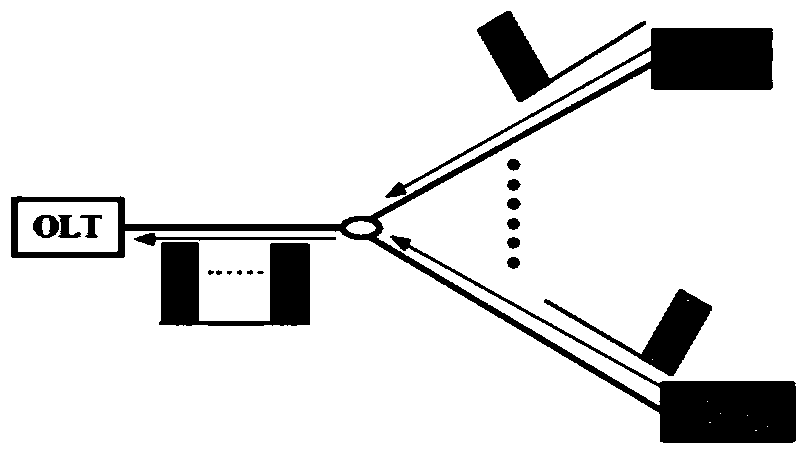
[0032] Such as figure 1 , Figure 8 with Image 6As shown, this embodiment takes two units of ONU1 and ONU2 as examples, and the encryption method is specifically: by transmitting the upstream data of ONU1 and ONU2 to the OLT as a secret key and performing an XOR operation with the downstream data detected on the OLT The encrypted data is obtained, so as to realize the encryption of the downlink data. After the encrypted data is transmitted downlink to ONU1 and ONU2 through the downlink subcarrier, ONU1 and ONU2 decrypt according to the uplink data stored locally to obtain the decrypted downlink data.
[0033] When the uplink data and downlink data are asymmetrical, the asymmetric coefficient A is calculated according to (A-1)<(Rd / Ru)≤A, and the uplink data is repeated A times to perform the encryption operation of XOR operation, wherein: Rd and Ru are data rates of downlink data and uplink data respectively.
[0034] The encrypted data for downlink transmission is divided ...
Embodiment 2
[0055] Such as Image 6 As shown, the device based on the method described in Embodiment 1 includes: an exclusive OR module arranged in the OLT for encryption calculation, an asymmetric data rate calculation module, an exclusive OR module arranged in each ONU for decryption, and an uplink data storage module, wherein: the output end of the asymmetric data rate calculation module is connected to the XOR module used for encryption calculation and outputs the asymmetric transmission coefficient when the uplink data and downlink data are asymmetric; the XOR module used for encryption calculation is composed of The terminal transmits the encrypted downlink data to the XOR module used for decryption in each ONU, and the XOR module used for decryption is connected to the uplink data storage module, so as to obtain the decrypted downlink data from the encrypted data.
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More