Data security controlling system and implementation method of system
A technology of data security and implementation method, applied in the field of data security control system, can solve the problems of poor security, high use cost, inconvenient portability, etc., and achieve the effect of reducing the burden of use, wide application prospects, and avoiding the effect of biometric technology.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0026] The present invention will be described in detail below in conjunction with the accompanying drawings and specific embodiments, but not as a limitation of the present invention.
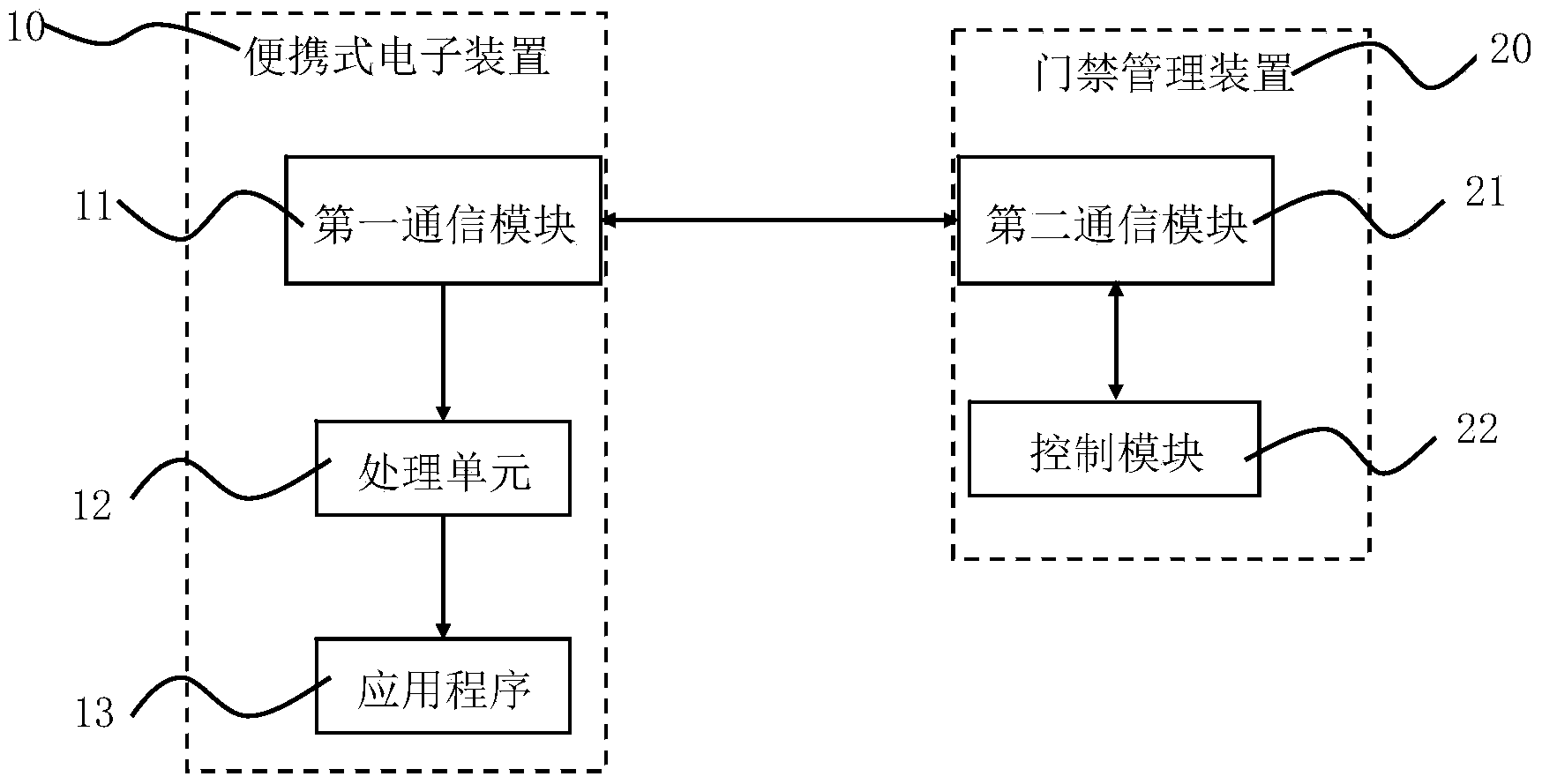
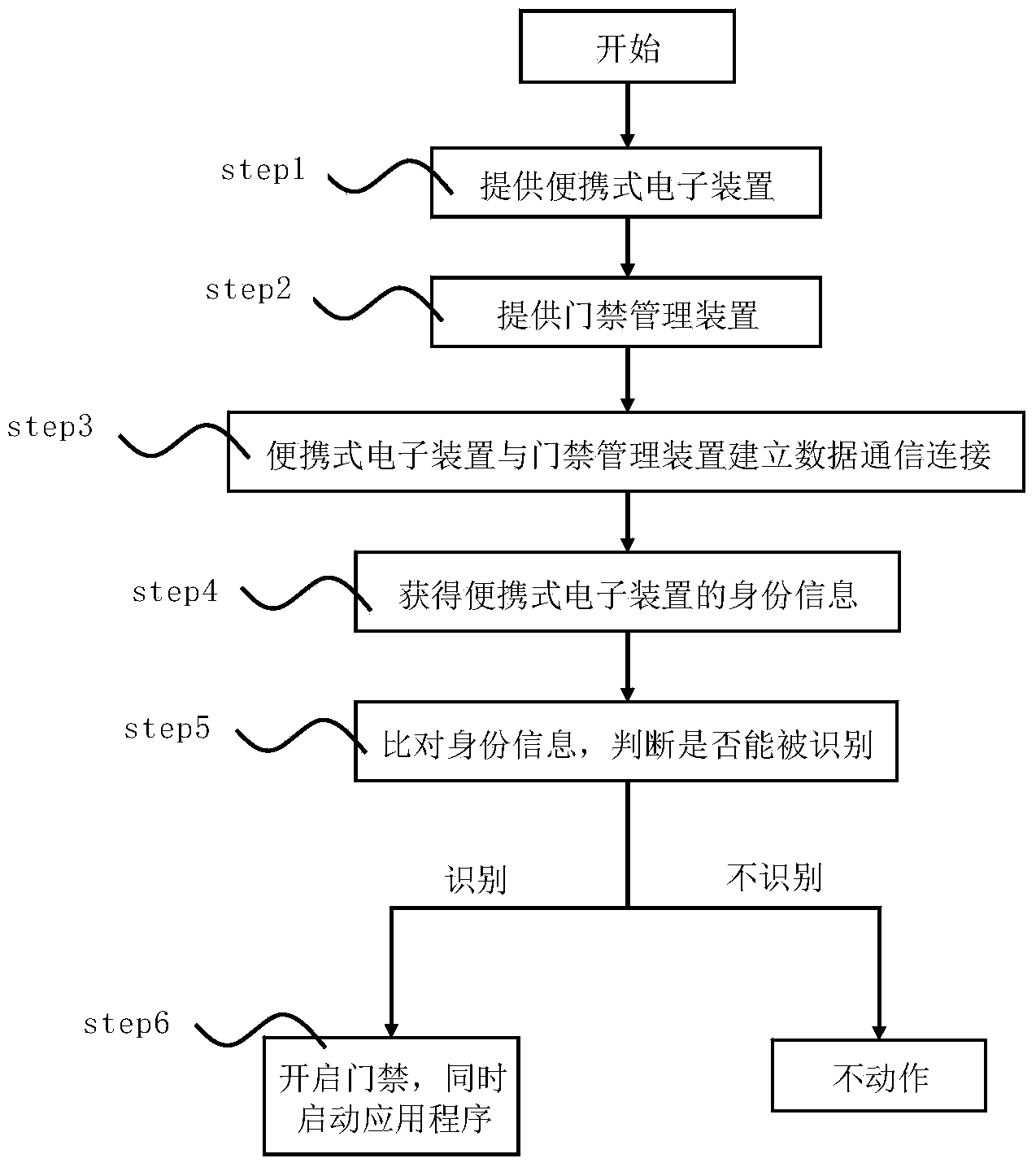
[0027] figure 1 It is a schematic diagram of the composition of the data security control system of the present invention. As shown in the figure, the data security control system includes a portable electronic device 10, an application program 13 and an access control management device 20, wherein the portable electronic device 10 has a first communication module 11, the second A communication module 11 stores identity information of the portable electronic device 10 . The application program 13 is a computer program developed based on the operating system of the electronic device 10 and capable of running on the portable electronic device 10 . The access control management device 20 has a second communication module 21 and a control module 22, the control module 22 is connected with the sec...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com