Virtual machine security group configuration method and device
A configuration method and security group technology, applied in the field of communication, can solve problems such as lack, complicated process of creating security groups, inconvenient rapid creation of security groups, etc., and achieve the effect of convenient configuration
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0070] Hereinafter, the present invention will be described in detail with reference to the drawings and examples. It should be noted that, in the case of no conflict, the embodiments in the present application and the features in the embodiments can be combined with each other.
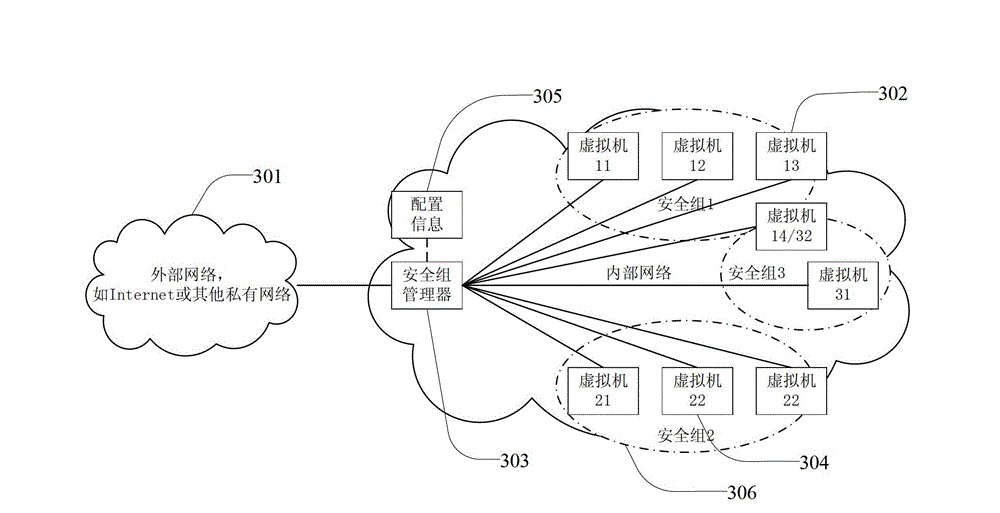
[0071] Figure 6 is a flowchart of a method for configuring a virtual machine security group according to an embodiment of the present invention, such as Figure 6 As shown, the method mainly includes the following steps (step S602-step S604):
[0072] Step S602, when receiving an operation request to bind, update or unbind the created virtual machine and the security group, the virtualization platform binds, updates or unbinds the virtual machine and the security group;
[0073] Step S604, when receiving an operation request for importing and exporting a designated security group, the virtualization platform imports and exports the designated security group.
[0074] In this embodiment, binding t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More