Method and device for application program authority management
An application and permission management technology, applied in the field of network security, can solve problems such as inability to prohibit applications, and achieve the effect of saving power and improving running speed
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
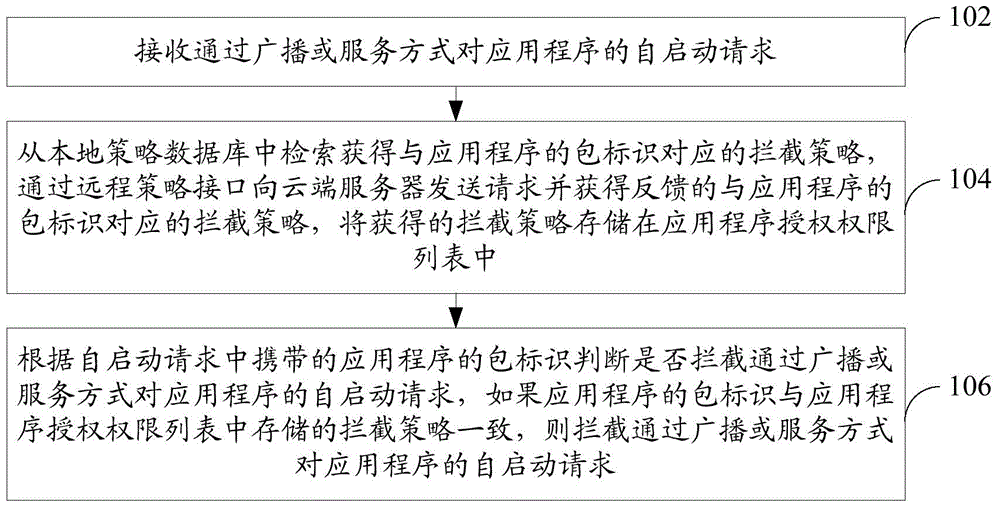
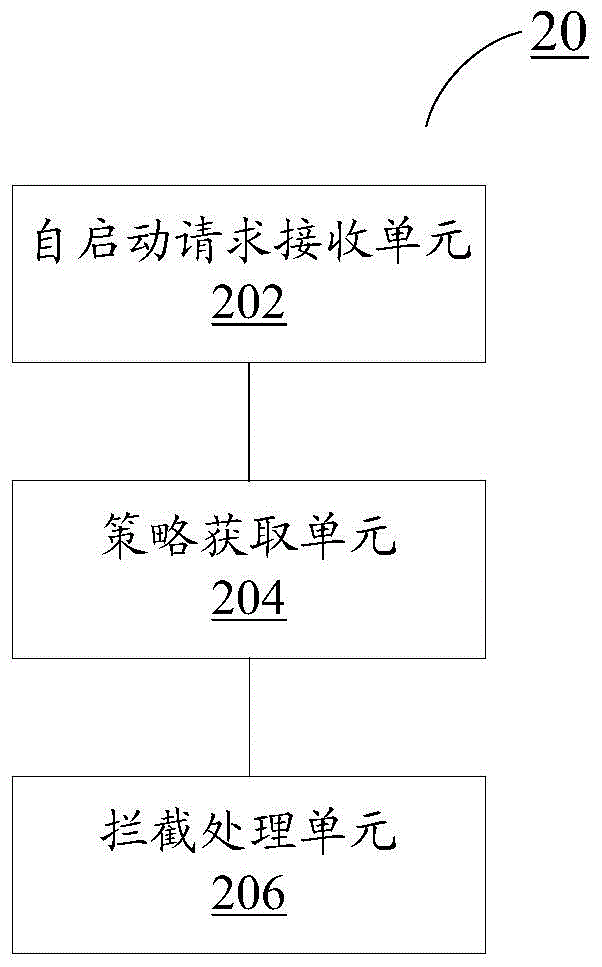
Method used
Image
Examples
Embodiment Construction
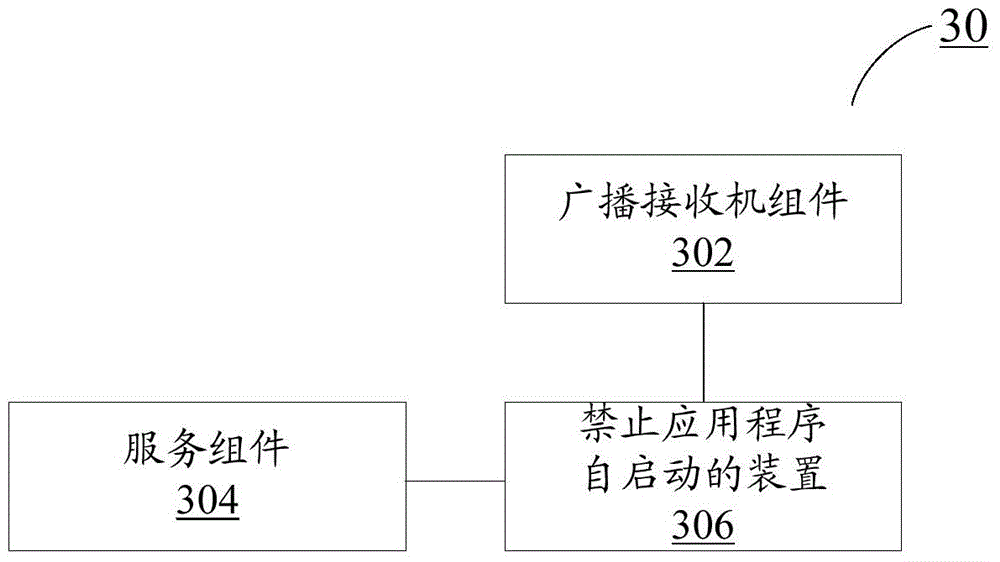
[0054]The present invention will be described more fully hereinafter with reference to the accompanying drawings, in which exemplary embodiments of the invention are illustrated. The technical solutions in the embodiments of the present invention will be clearly and completely described below in conjunction with the drawings in the embodiments of the present invention. Obviously, the described embodiments are only part of the embodiments of the present invention, not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without creative efforts fall within the protection scope of the present invention.
[0055] The Android system has four major components: Activity, Service, Broadcast Receiver and Content Provider, all of which can be managed by ActivityManagerService. It will be executed through ActivityManagerService when the application is self-started.
[0056] The environment to which the me...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More