Identity authentication method for access control of MIPS (Million Instructions Per Second) platform network system
A technology of identity authentication and access control, which is applied in transmission systems, network data retrieval, special data processing applications, etc. It can solve the problems that computers are vulnerable to viruses and hackers, and ordinary browsers cannot
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
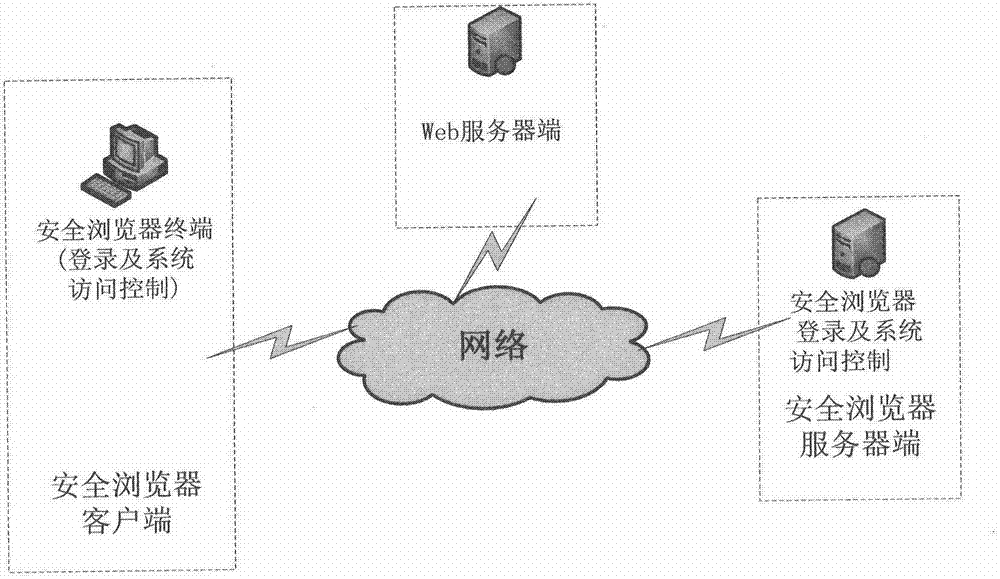
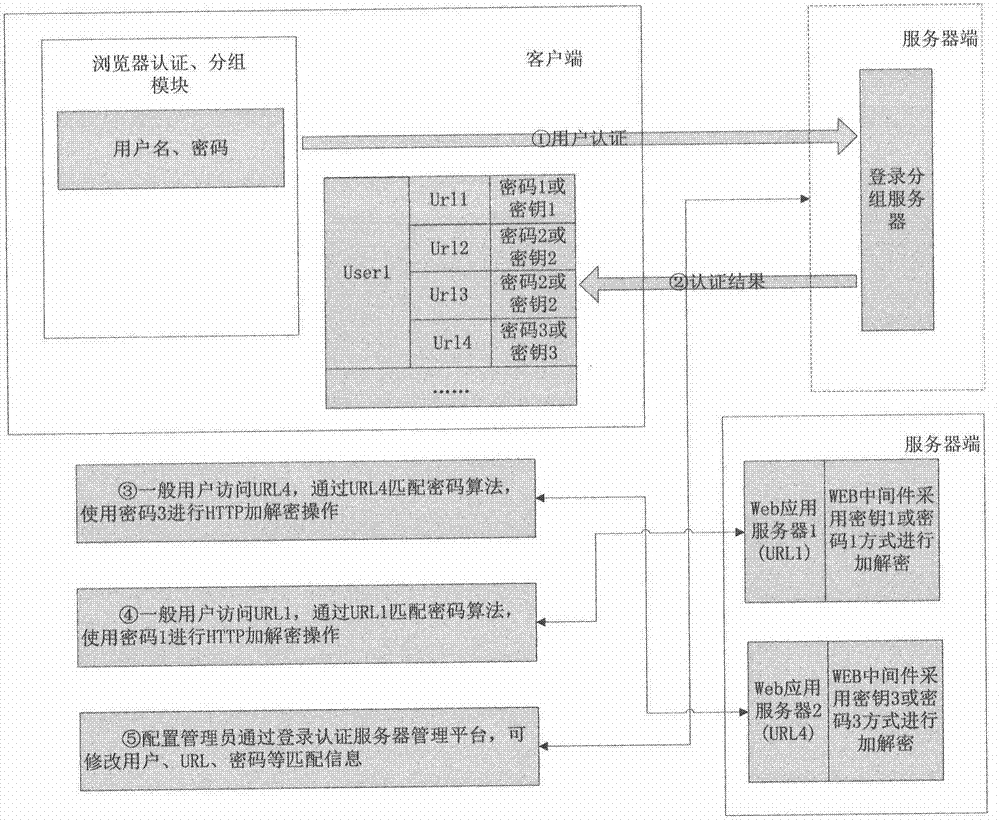
[0016] Such as Figure 1-2 Shown, a kind of identity authentication method of MIPS platform network system access control, described MIPS platform comprises safe browser client end, WEB server end and safe browser server end, and described client end is safe browser terminal, and described server The terminal can log in and control the system access to the secure browser of the secure browser terminal, and the identity authentication method specifically includes the following steps:
[0017] 1. User A opens the browser, enters the user name and password in the input box of the browser authentication and grouping module, and sends the user information to the login grouping server on the WEB server side;
[0018] 2. Log in to the group server to verify the legitimacy of the user name and password. If the authentication fails, an error message will be returned; if the legitimacy is passed, the URL list information that user A can access will be returned. This information is invis...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More