Method for interactive authentication between RFID (radio frequency identification) card and card reader
An interactive authentication, 1. RFID technology, applied in the field of authentication between RFID cards and card readers, can solve problems such as potential safety hazards, easy to be cracked, etc., achieve high security level, enhance security and crack difficulty, low cost effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
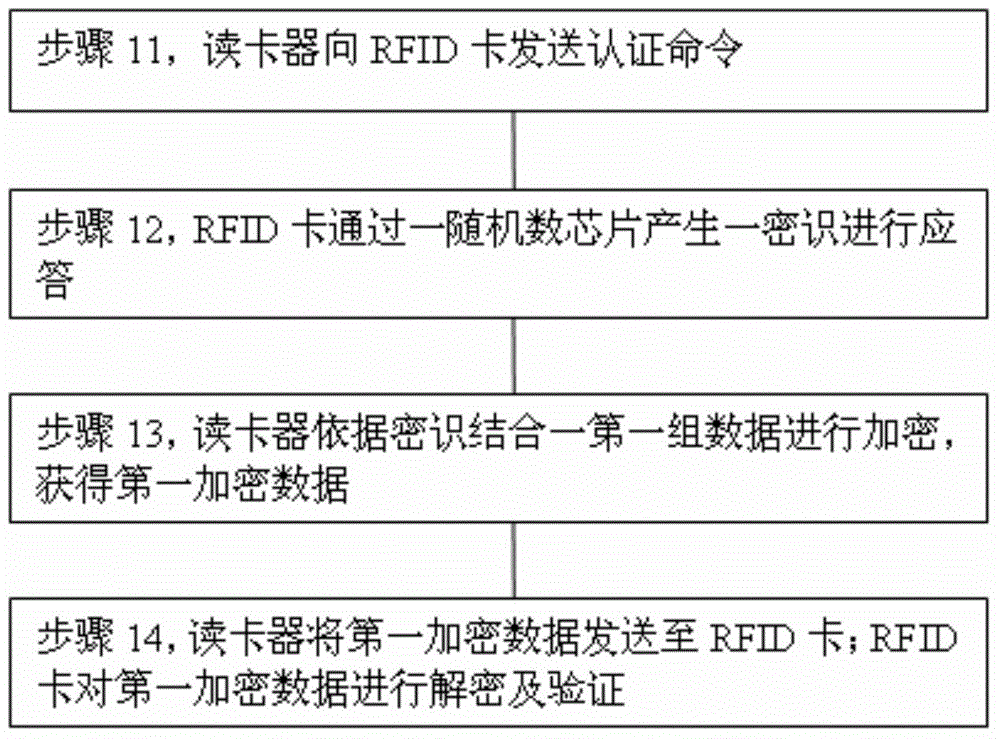
Method used
Image
Examples
specific Embodiment
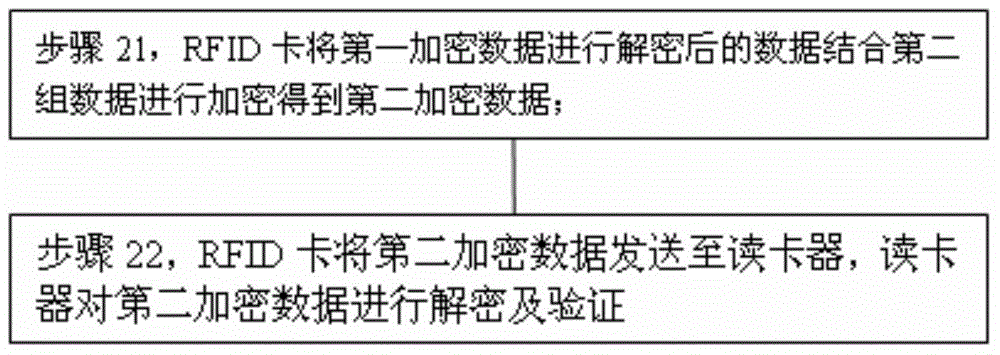
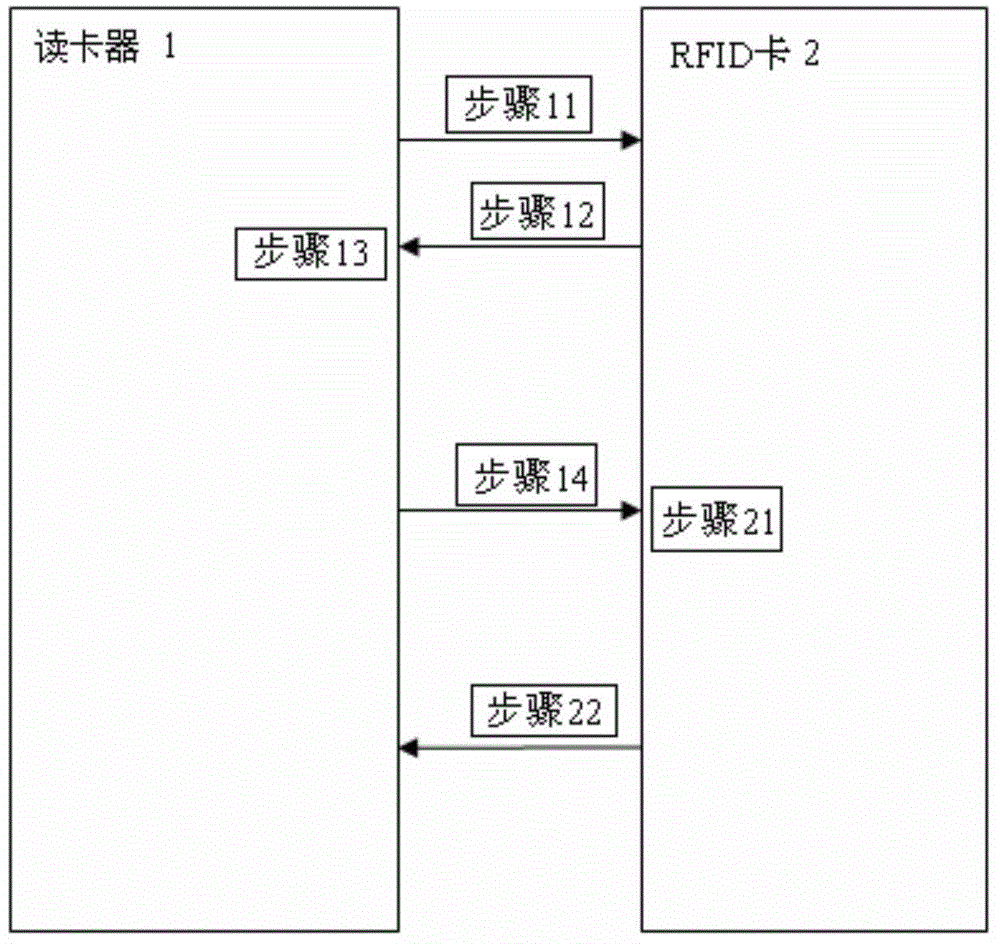
[0047] A kind of specific embodiment, the second group of data comprises 8 byte card reader random number and 8 byte chip ID, the second encrypted data is also a 16 byte encrypted data, card reader random number adopts the random number based on AES algorithm The number of chips is generated. After decrypting the second encrypted data in step 22, the 8-byte card reader random number and the 8-byte chip ID are obtained, and the 8-byte card reader random number is verified. After the verification is successful, the authentication is passed.
[0048] The communication between the card reader 1 and the RFID card 2 of the present invention is to send a command to the RFID card 2 through the card reader 1, and the RFID card 2 feeds back information to the card reader 1 after receiving the command, a two-way interactive verification method, It can make the majority of system integrators improve the security level of the existing system at a lower cost. It can eliminate potential saf...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - Generate Ideas
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com