Video authentication method and device
An authentication method and video technology, applied in the field of communication information security, can solve problems such as the complexity of digital watermarking algorithm, the inability of perceptual hash technology to locate tampering, and the impact on video image quality
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
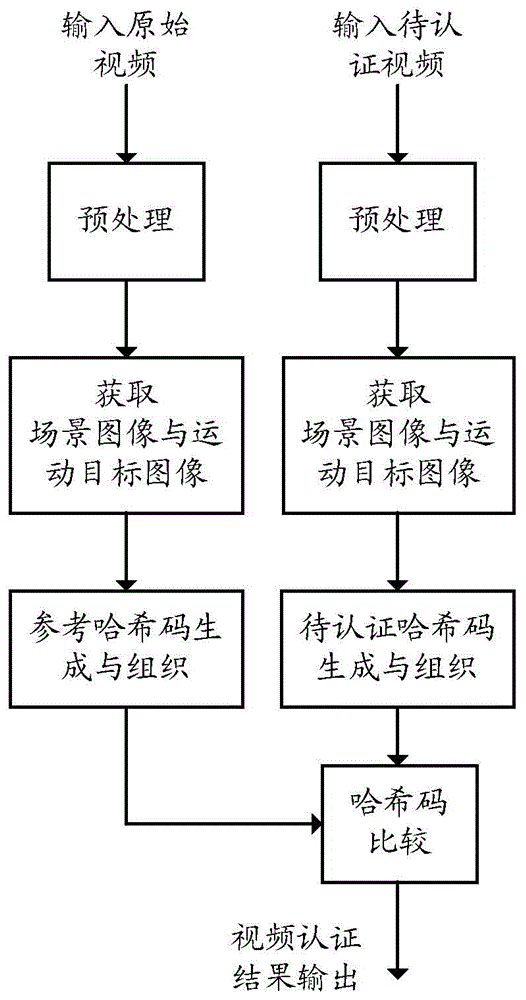
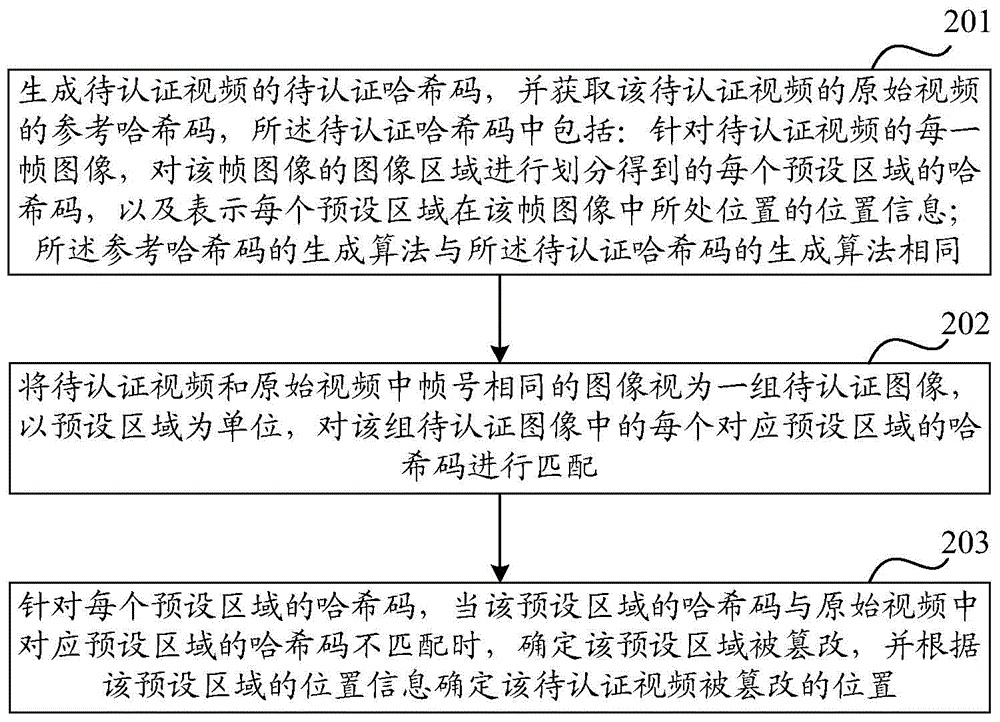
[0070] Such as figure 2 Shown is an exemplary flowchart of a method for video authentication in an embodiment of the present invention, the method includes the following steps:
[0071] Step 201: Generate a hash code to be authenticated of the video to be authenticated, and obtain a reference hash code of the original video of the video to be authenticated, the hash code to be authenticated includes: for each frame of the video to be authenticated, the The hash code of each preset area obtained by dividing the image area of the frame image, and the position information indicating the position of each preset area in the frame image; the generation algorithm of the reference hash code is the same as the The algorithm for generating hash codes to be authenticated is the same as described above.
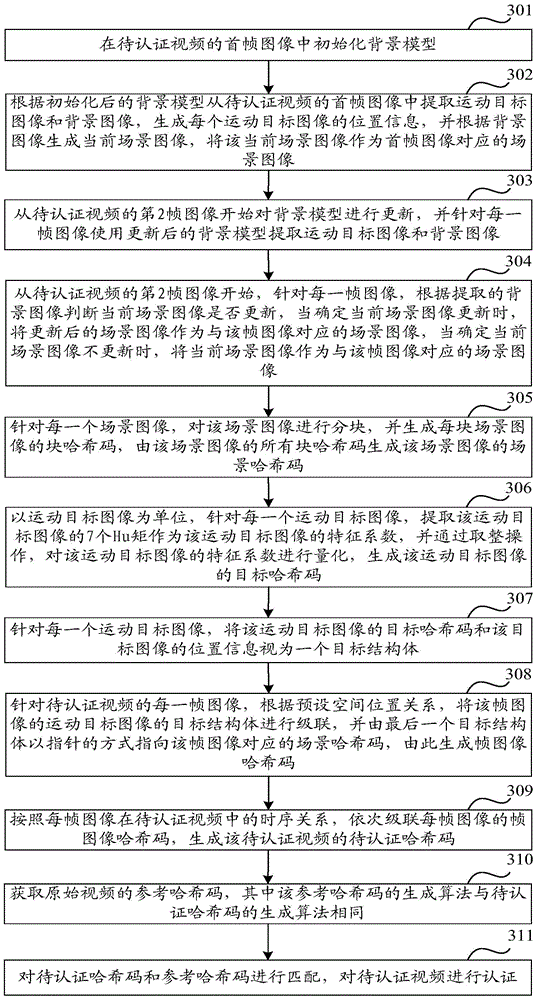
[0072] Wherein, the scene image is used to characterize the characteristics of the background image of the video. In one frame of image, it is divided into a background image and a m...
Embodiment 2
[0177] Taking the video authentication of the surveillance video as an example below, since the scene image of the surveillance video is relatively stable, at least one scene image may be established to represent the scene image of the surveillance video. Corresponding to the scene image of the surveillance video, the perceptual hash feature extraction of each block can be performed by pre-blocking and performing DCT transformation on each block, and the perceptual hash feature extraction of each block is composed of 1 DC coefficient and 5 AC coefficients. The characteristic coefficient matrix, and then obtain the block hash code of each block through multi-interval non-uniform quantization. Since the moving target image in the surveillance video accounts for a small proportion of the entire frame image, each target image can be used as a unit, and the 7 Hu moments obtained for each target image are used as the characteristic coefficient matrix of the moving target image, and t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More