Authentication processing method of organization identity information of individual user
A technology of identity information and processing methods, applied to electrical components, transmission systems, etc., can solve problems such as authenticity cannot be guaranteed, accuracy is not necessarily accurate, and inconvenience
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
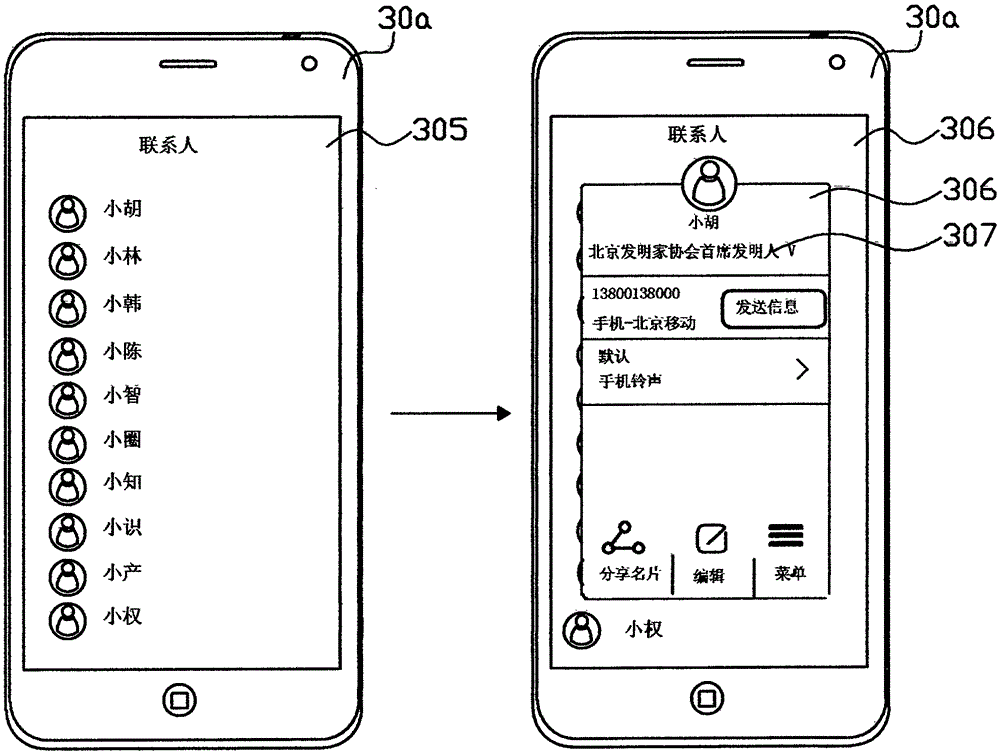
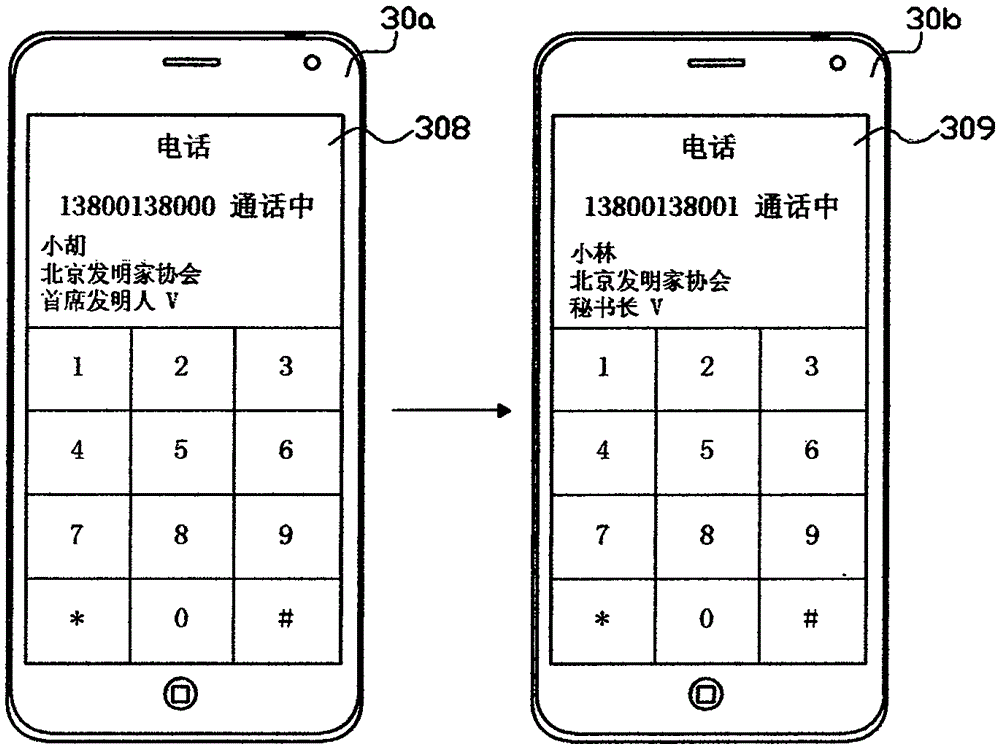
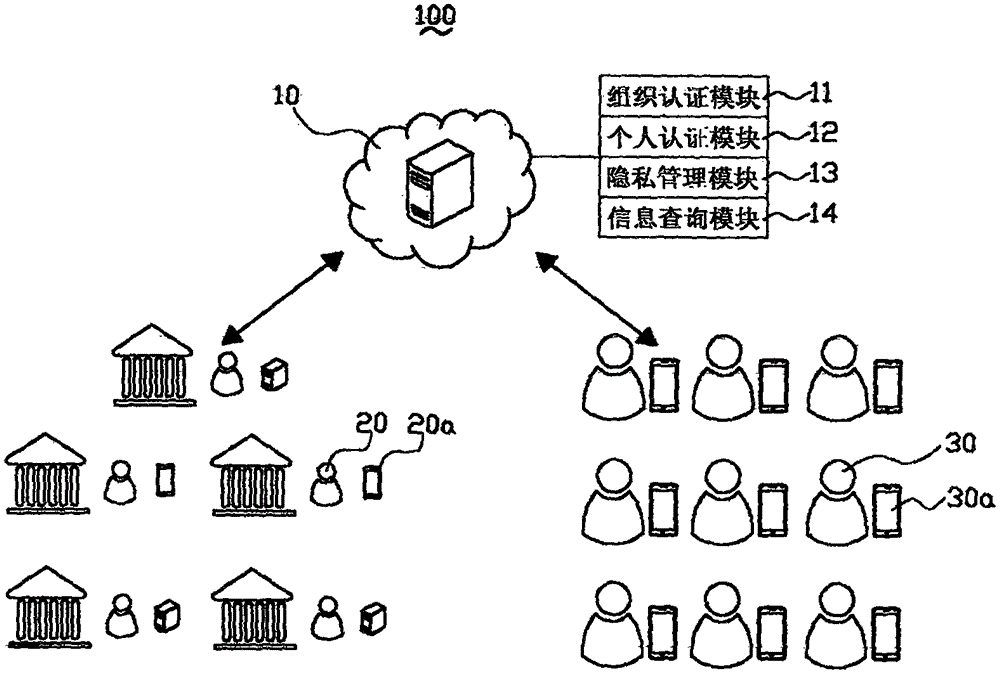
[0039] In order to further explain the technical means and effects of the present invention to achieve the purpose of the invention, the specific implementation, structure, features and effects of the present invention will be described in detail below in conjunction with the accompanying drawings and preferred embodiments.
[0040] refer to figure 1 , which is a schematic diagram of the architecture of an individual user's organization identity information authentication system provided by an embodiment of the present invention. like figure 1 As shown, an individual user's organization identity information authentication system 100 includes a cloud server 10 . The cloud server 10 includes: an organization authentication module 11 , an individual authentication module 12 , a privacy management module 13 , and an information query module 14 . The above-mentioned organization authentication module 11, personal authentication module 12, privacy management module 13, and informa...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More