Trusted computing terminal integrity measuring and proving method and device
A technology of integrity measurement and trusted computing, applied in platform integrity maintenance, internal/peripheral computer component protection, electrical digital data processing, etc., and can solve problems such as application program failure
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0057] All features disclosed in this specification, or steps in all methods or processes disclosed, may be combined in any manner, except for mutually exclusive features and / or steps.
[0058] Any feature disclosed in this specification, unless specifically stated, can be replaced by other equivalent or similar purpose alternative features. That is, unless expressly stated otherwise, each feature is one example only of a series of equivalent or similar features.
[0059] Relevant description of the present invention:
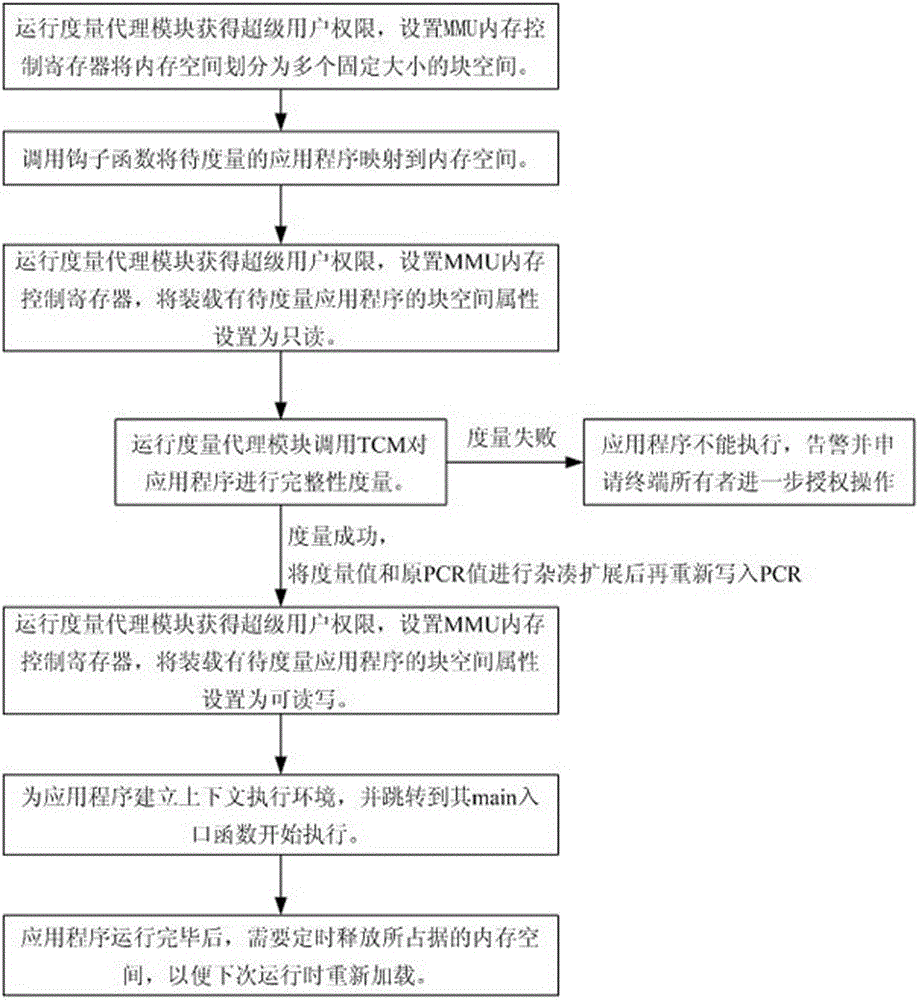
[0060] The measurement proxy module calls the trusted cryptographic module TCM to measure the application program: the measurement proxy module is a section of OS kernel program, and the programming of this program should refer to the relevant trusted cryptographic module interface specifications of the State Administration of Commercial Secrets.
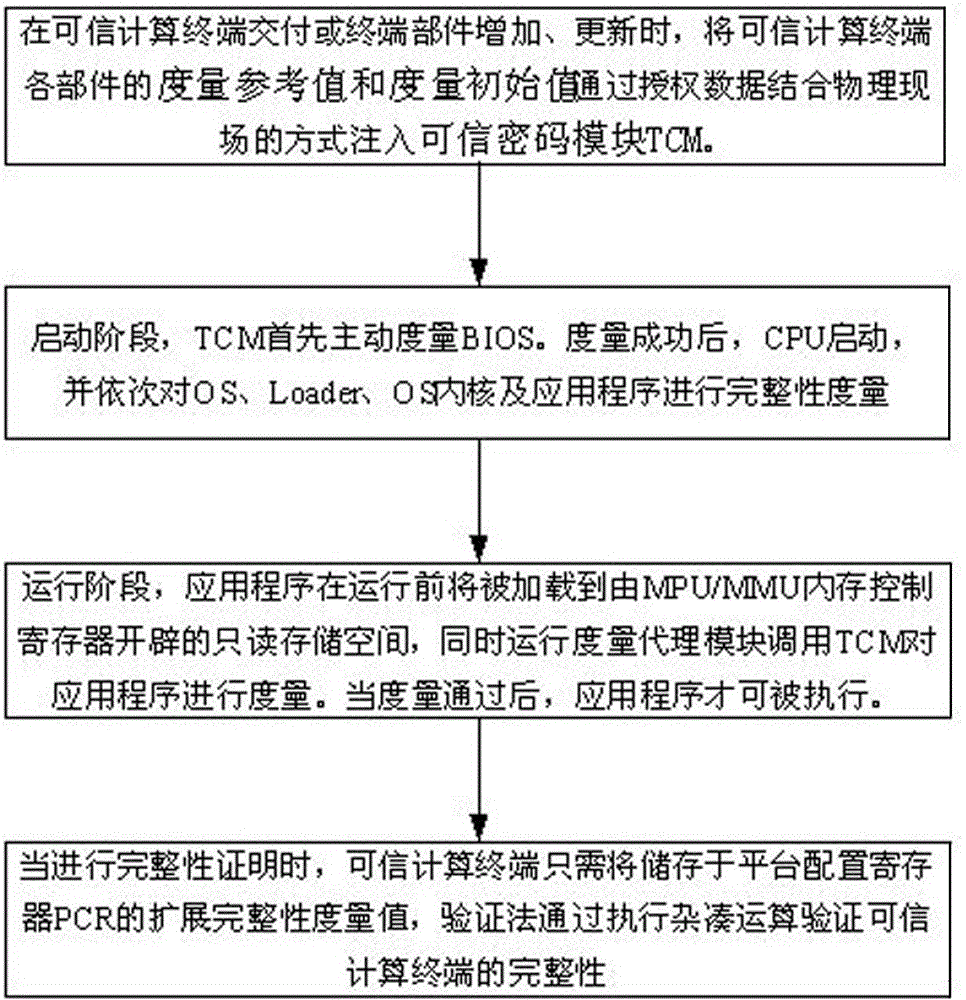
[0061] The present invention includes: 1) Integrity measurement (refer to steps 1, 2, 3) and proof phase (refer t...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More