Method of locking/unlocking computer screen based on NFC terminal
A computer screen and terminal technology, applied in the field of information security, can solve problems such as troublesome operation, inability to meet the needs of users for higher security, and inability to reasonably utilize the usage habits of stock assets. Effect
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0065] In order to make the object, technical solution and advantages of the present invention clearer, the following examples are given to further describe the present invention in detail.
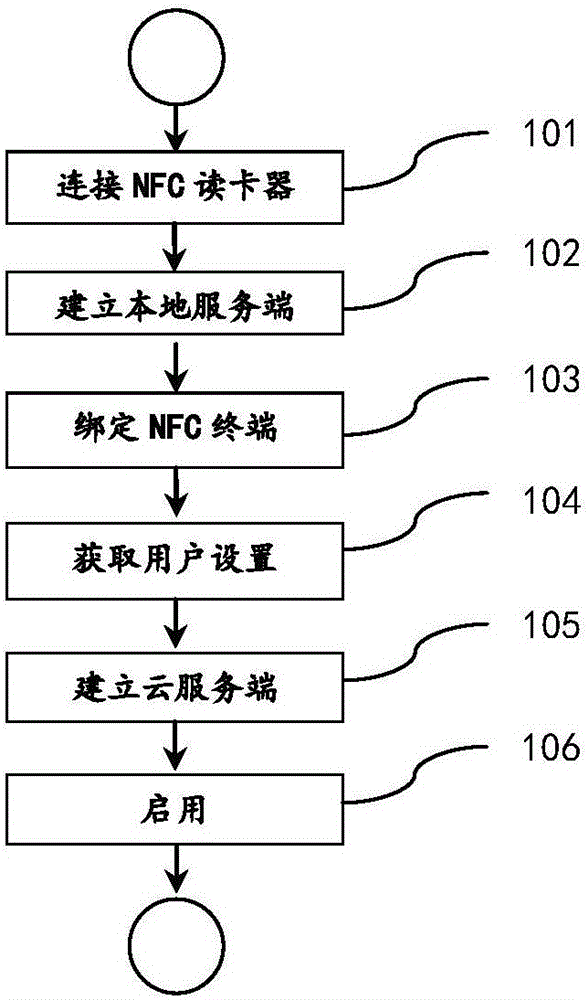
[0066] Such as figure 1 As shown, a method for locking / unlocking a computer screen based on an NFC terminal comprises the following steps:
[0067] 101: Connect the NFC card reader, the NFC card reader includes: an identification module, a processing module, a communication module, and a radio frequency antenna;
[0068] The identification module: periodically switches between a card emulation mode and a peer-to-peer mode (P2P mode). In Card emulation, identify the ID and unique terminal identification number of the NFC terminal that simulates the radio frequency card; in P2P mode, identify the ID and unique terminal identification number of the NFC terminal;
[0069] The processing module: converting the identified ID and terminal unique identification number into data signals;
[007...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More