Android malicious code family classifying method based on bytecode image clustering
A malicious code and classification method technology, applied in the field of Android malicious code family classification, can solve the problem of high false alarm rate, achieve the effect of low false positive rate, effective Android malicious code family classification, and high detection accuracy
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0033] The present invention will be further described below in conjunction with the accompanying drawings.
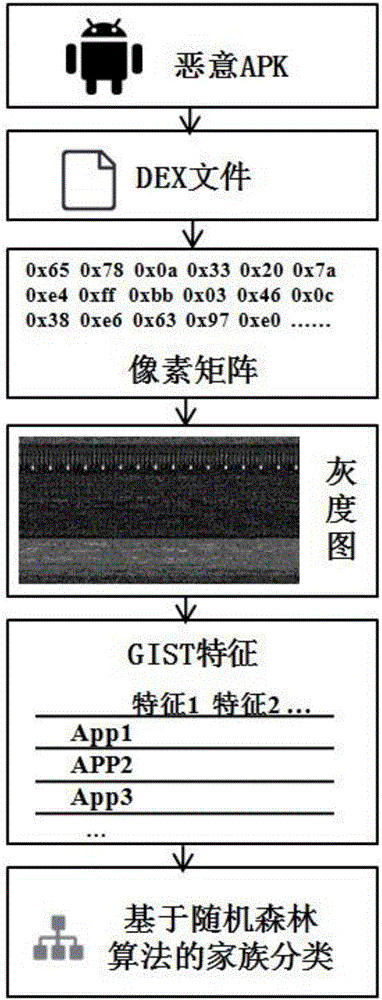
[0034] refer to Figure 1 to Figure 5 , a kind of Android malicious code family classification method based on bytecode image clustering, comprises the following steps:
[0035] 1) The APK program code is mapped into a grayscale image
[0036] APK format files usually include a file named classes.dex, which encapsulates all Dalvik bytecodes that can be executed by the Dalvik virtual machine. The structure of the DEX file is composed of multiple structures, including dex header, string_ids, type_ids, proto_ids, field_ids, method_ids, class_def, data and other parts. The DEX file header specifies some attributes of the DEX file, and records the physical offset of the other 6 data structures in the DEX file.
[0037] If the bytecode of the DEX file is constructed into a pixel matrix of appropriate width (see Table 1 for the width suggestion), the pixel in the matrix is...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More