Distributed system and registration verification method thereof
A distributed system, login verification technology, applied in transmission systems, electrical components, etc., can solve business system security threats and other issues, achieve the effects of maintaining login security, improving system security, and preventing cookie cracking
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0012] In order to make the object, technical solution and advantages of the present invention clearer, the solutions of the present invention will be further described in detail below with reference to the accompanying drawings and examples.
[0013] Aiming at the defects existing in the existing distributed system, the present invention adopts a key list and a method for dynamically managing keys to add and invalidate keys, so as to regularly replace keys. Prevent a series of problems caused by key disclosure.
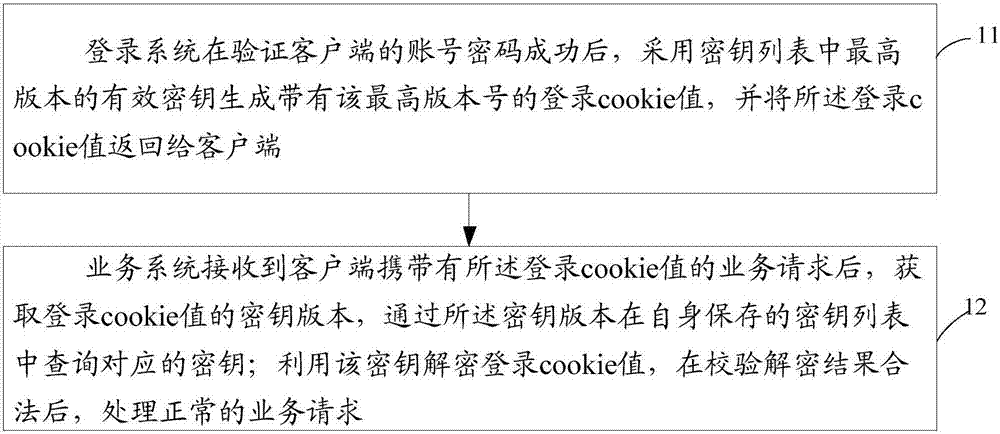
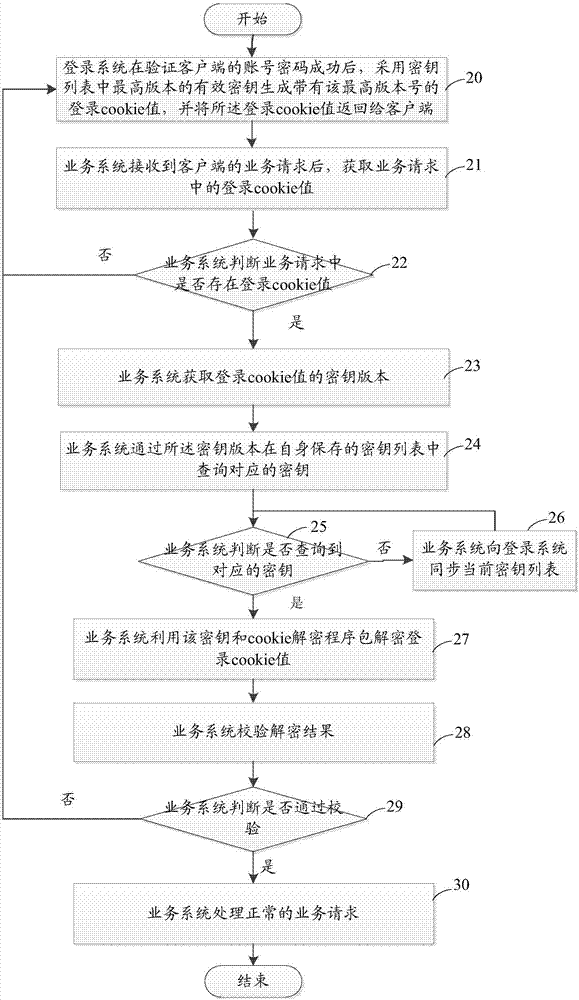
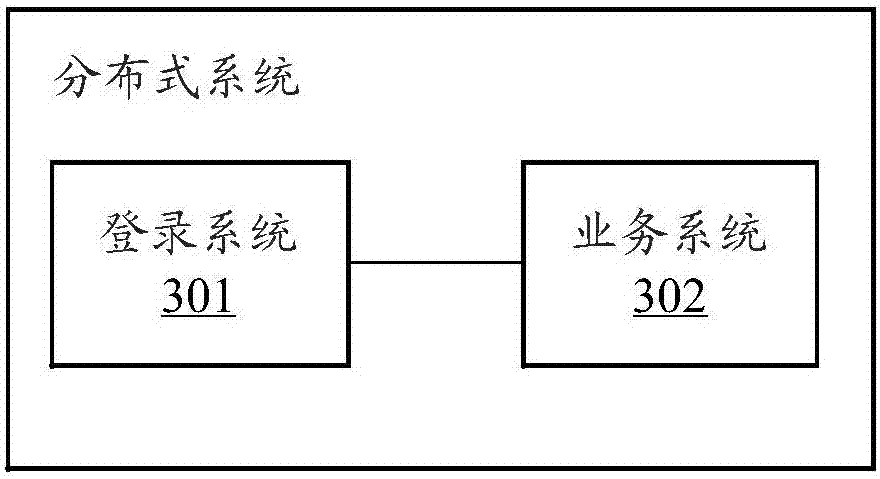
[0014] The schematic flow chart of the login verification method of the distributed system in the embodiment of the present invention is as follows figure 1 shown, including the following steps:
[0015] Step 11, after the login system successfully verifies the client's account password, it uses the highest version of the effective key in the key list to generate a login cookie value with the highest version number, and returns the login cookie value to the client; ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More