NIN neural network-based malicious code variation detection method
A malicious code and neural network technology, applied in biological neural network models, neural architectures, instruments, etc., can solve the problem of small image data, achieve the effects of improving performance, solving data imbalance, and suppressing useless information
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
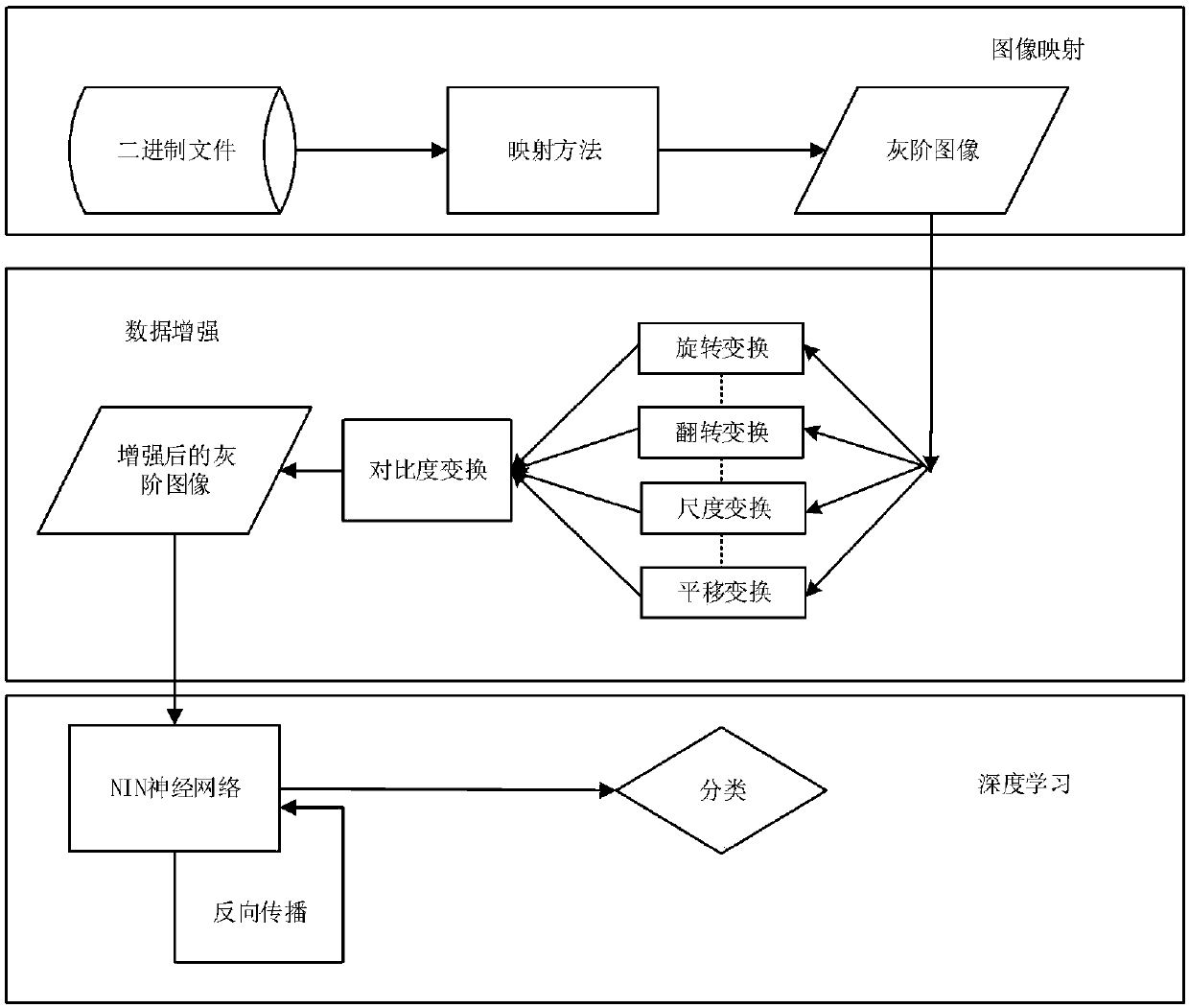
[0045] In order to make the object, technical solution and features of the present invention clearer, the present invention will be further described in detail below in conjunction with specific implementation examples and with reference to the accompanying drawings. The basic flow chart of the detection method for malicious code variants is as follows: figure 1 shown.
[0046] The individual steps are explained below:
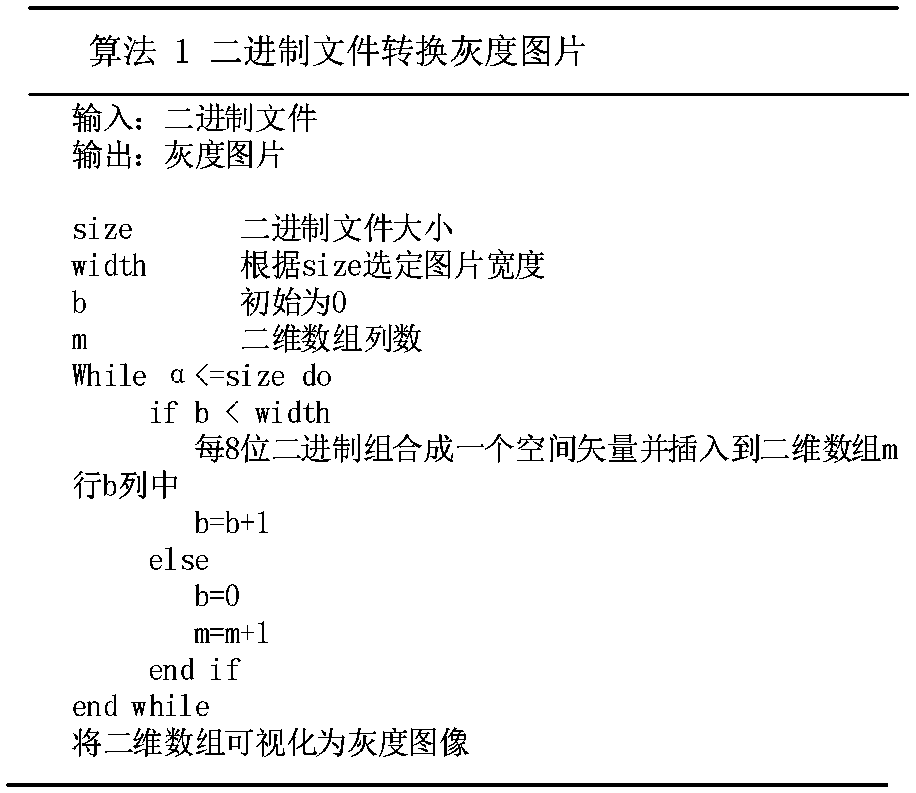
[0047] 1) A method of processing malicious code and converting it into an uncompressed grayscale image is proposed, so that the original malicious code detection technology can be transformed into an image detection problem.
[0048] 2) Propose the use of data augmentation techniques to overcome the lack of data, and study the impact of different data augmentation combinations on the test results.
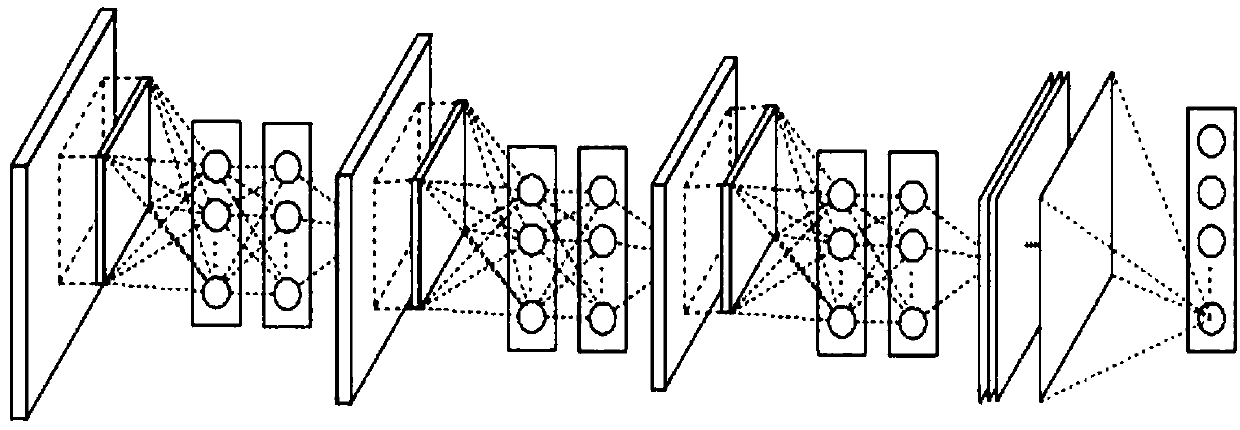
[0049] 3) A NIN neural network model for gray-scale image detection is proposed, which greatly speeds up the detection speed and effectively improves the detect...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More