Method and system for hierarchical management of whole network security
A hierarchical management and security technology, applied in the network field, can solve the problems of waste of financial resources, material resources and manpower, lack of information security, and inability to achieve results, and achieve the effect of convenient office, saving manpower and network resources.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
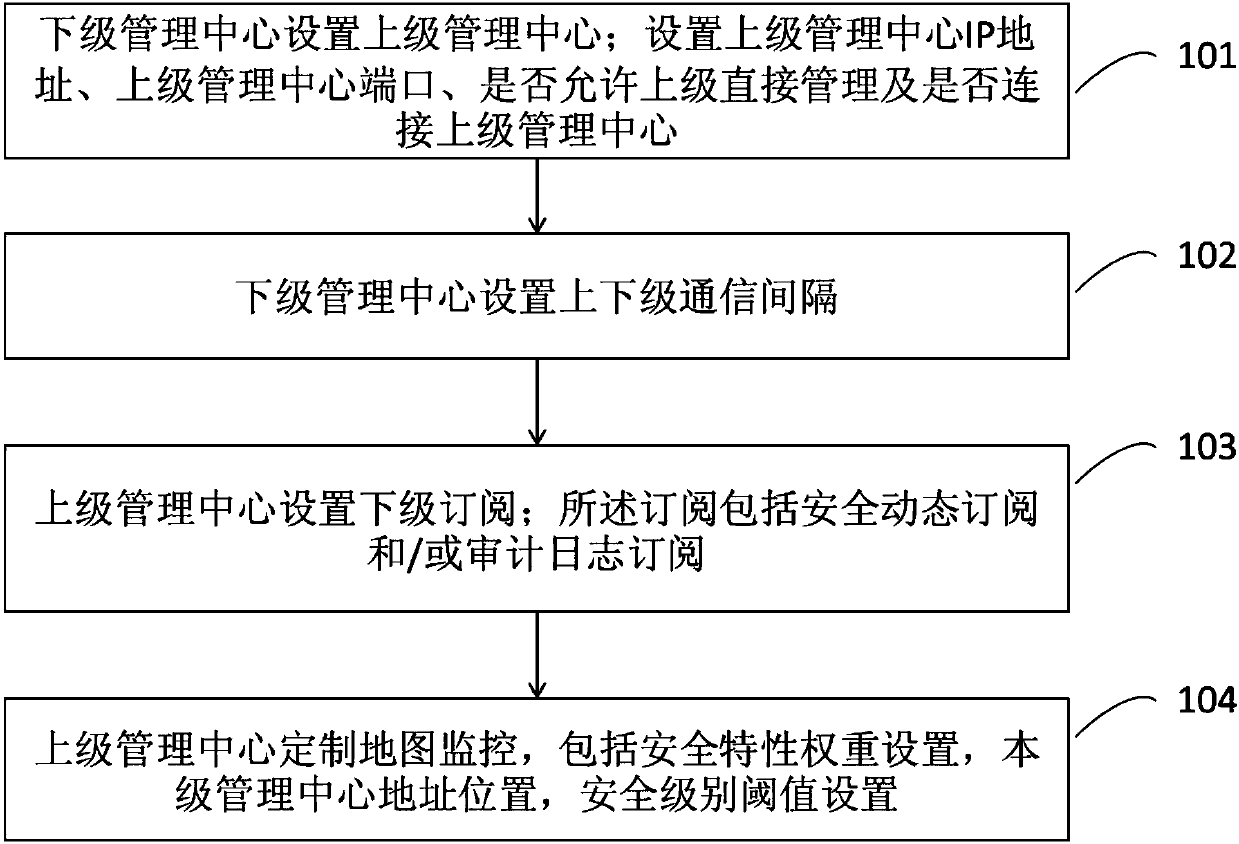
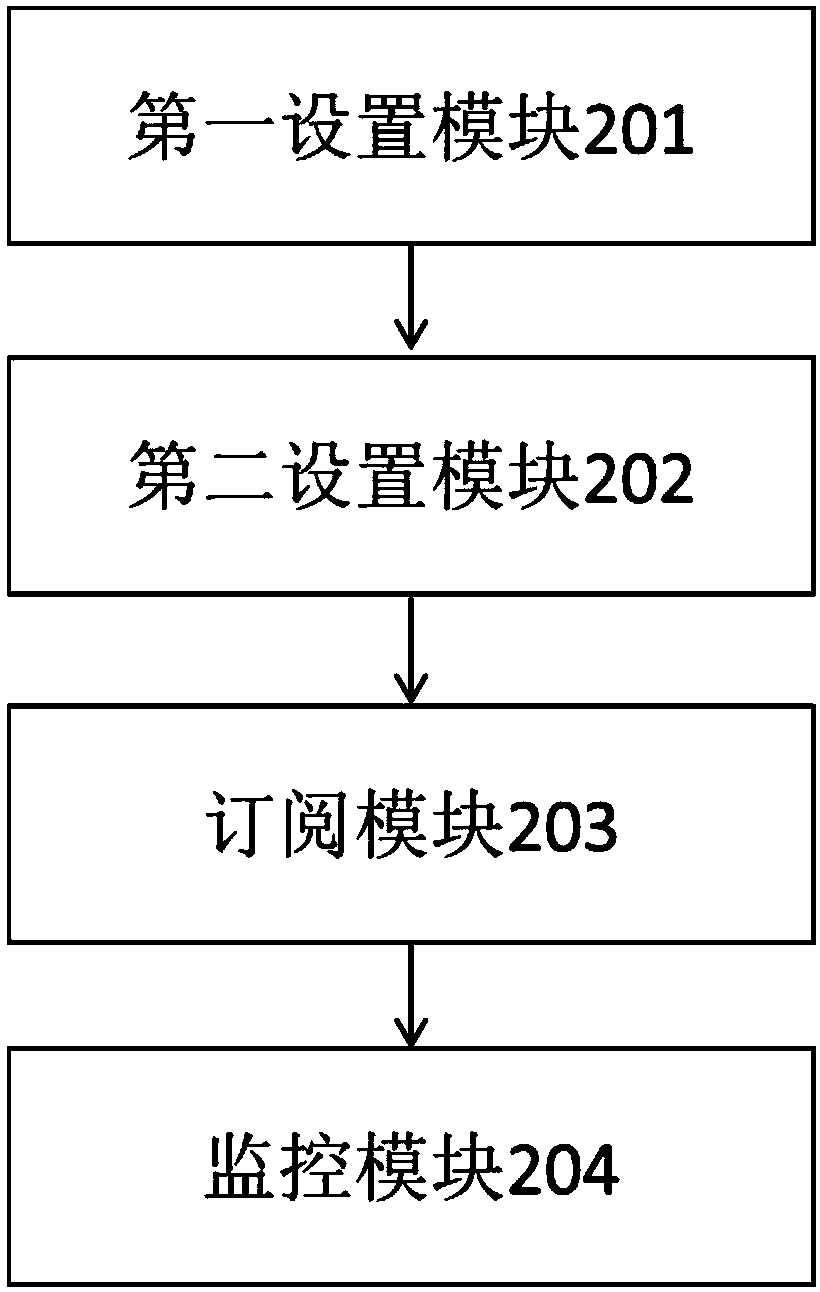
[0023] In order to more clearly illustrate the technical solutions in the embodiments of the present invention, the following will briefly introduce the accompanying drawings that need to be used in the embodiments. Obviously, the accompanying drawings in the following description are only some embodiments of the present invention. For Those of ordinary skill in the art can also obtain other drawings based on these drawings without making creative efforts.
[0024] The invention realizes hierarchical management of resources, realizes different levels of management centers to distribute security policies of different levels, and the upper management center controls the lower level to upload specified types of violation logs and security dynamics, realizes hierarchical monitoring of the entire network, and realizes security protection of key resources. At the same time, it saves manpower and network resources, making the office more convenient.
[0025] On the one hand, the embo...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More