Method and system for using asymmetric cryptographic algorithm to prevent codes from being maliciously tampered
An asymmetric encryption and code technology, applied in the field of encryption to avoid malicious tampering
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0016] The present invention will be further described in detail below through specific embodiments in conjunction with the accompanying drawings. The following examples are only descriptive, not restrictive, and cannot limit the protection scope of the present invention.
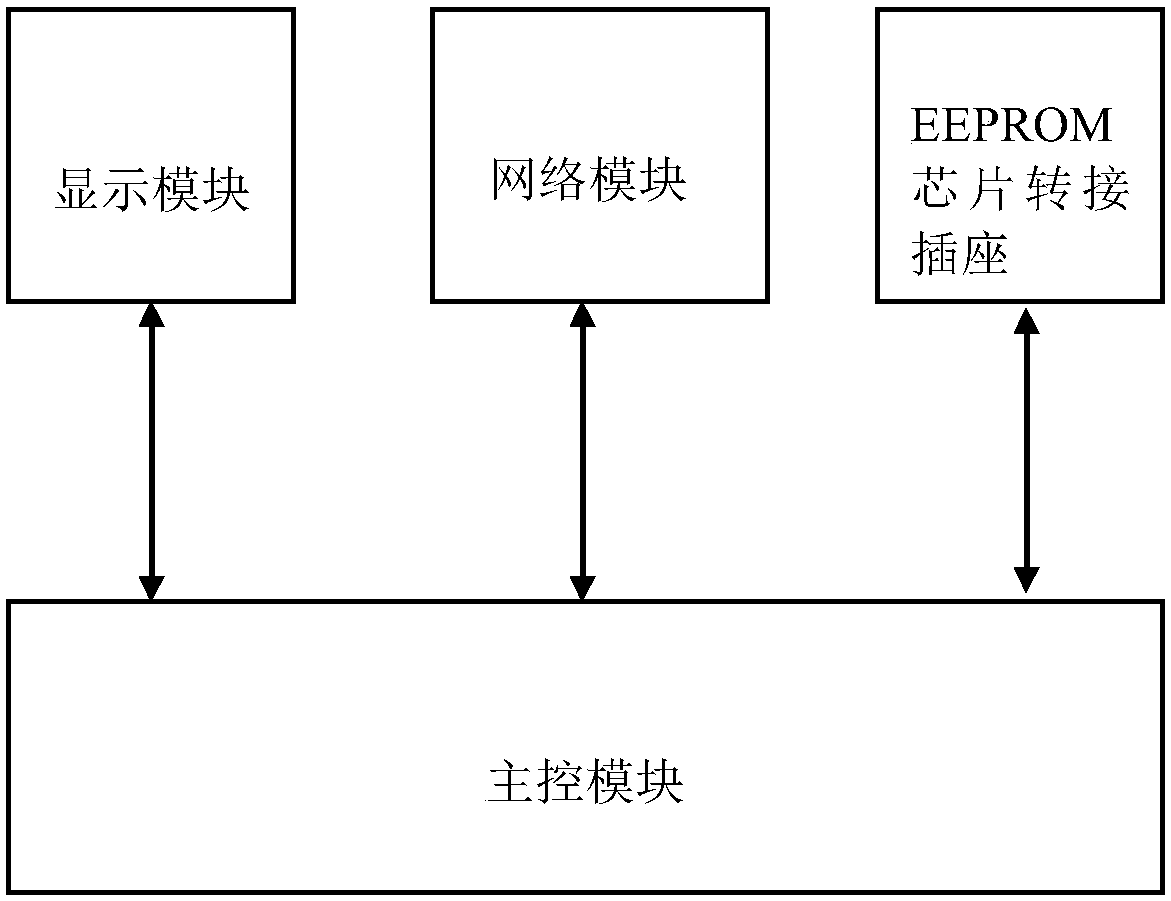
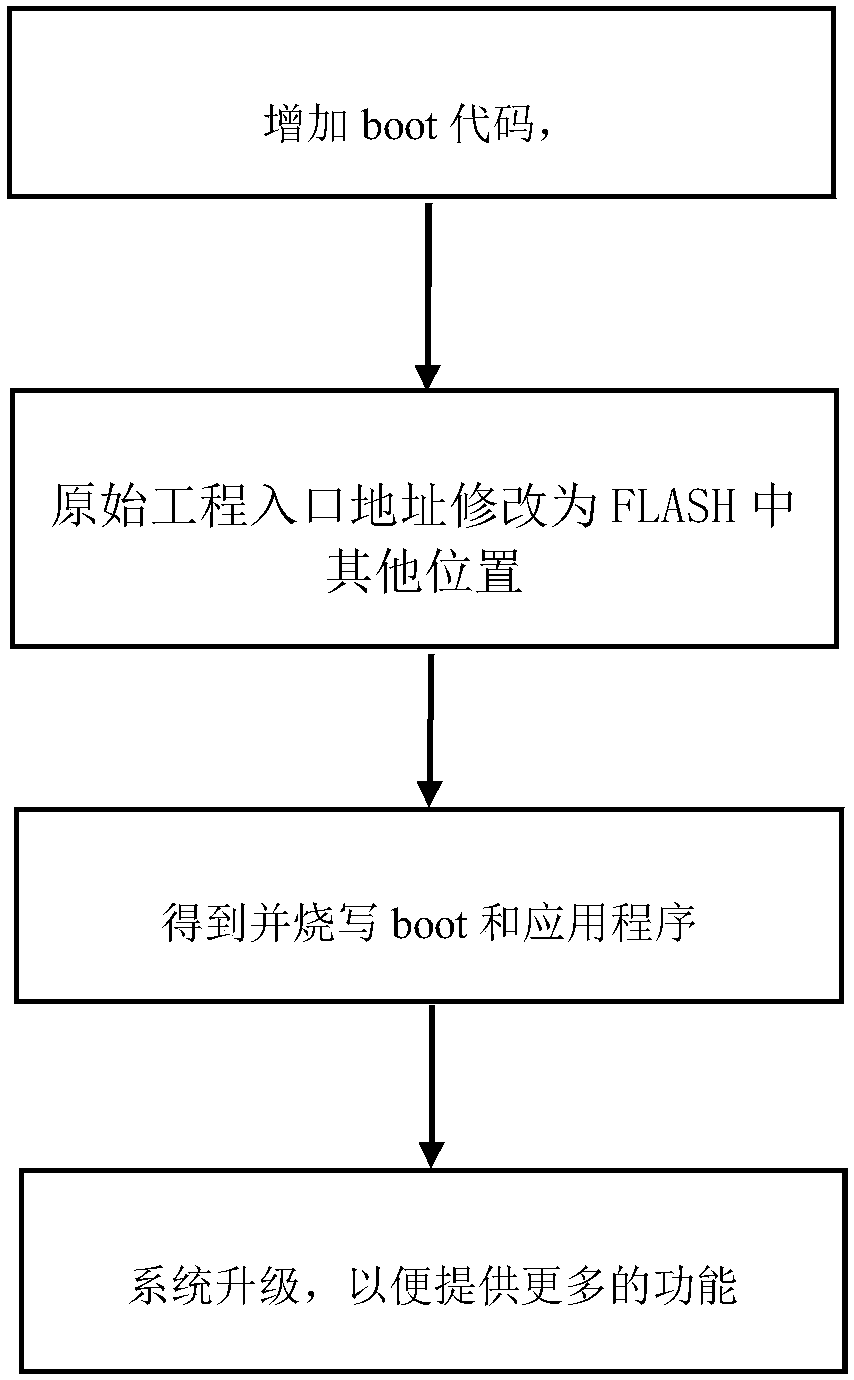
[0017] In the present invention, an EEPROM chip programmer is used as an example for description. In this embodiment, the STM32 series chip is used as the main control chip. The STM32 chip is a series of single-chip microcomputers widely used in embedded systems, and this chip supports online programming. Assume that the system is designed to be upgraded online to support more types of EEPROM chips.
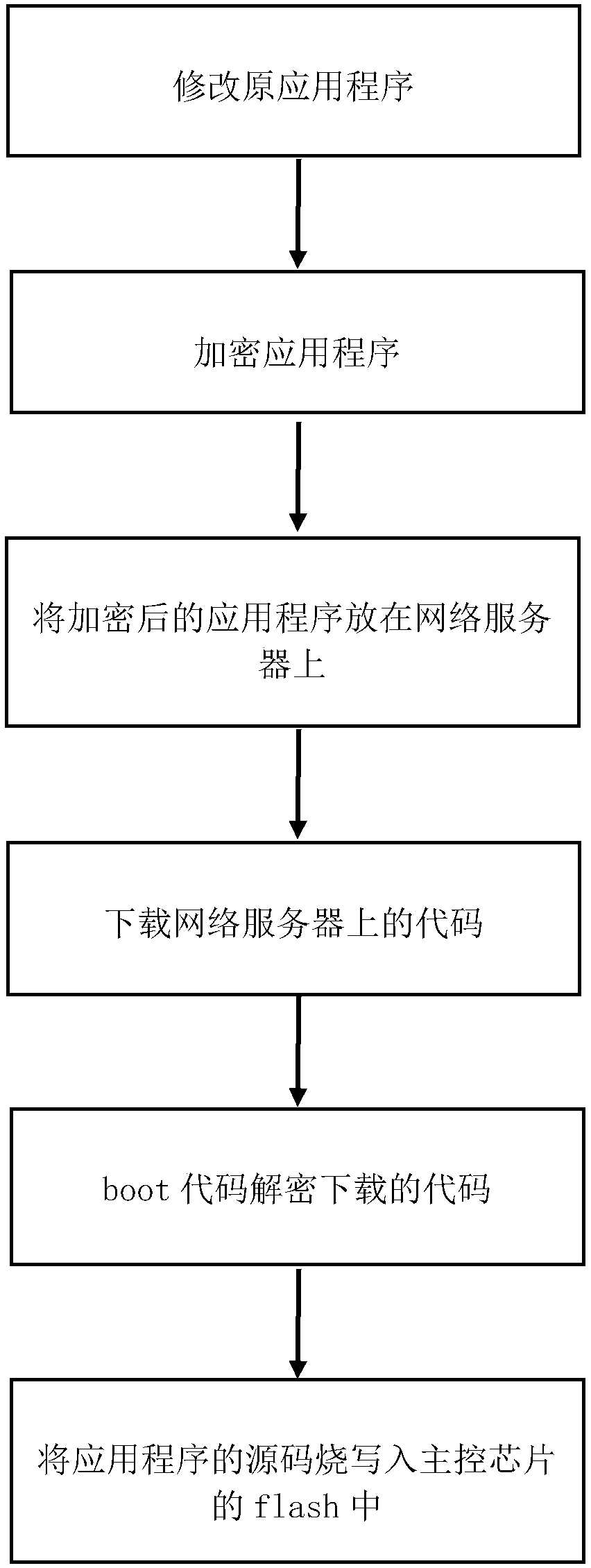
[0018] The RSA public key encryption algorithm is an asymmetric algorithm. RSA is a public key cryptosystem. The so-called public key cryptosystem uses different encryption keys and decryption keys. It is computationally infeasible to deduce the encryption key from the key".
[0019] Such as figure 1 as sh...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More