Identity-based closed key management method and system
A key management system and key management technology, applied in the field of identity-based closed key management methods and systems, can solve the problems of cumbersome use and poor scalability, so as to improve practicability, avoid tediousness and mistakes, and improve The effect of efficiency and safety
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0054] In order to make the purpose, features and advantages of the present invention more obvious and understandable, the technical solutions in the present invention will be clearly and completely described below in conjunction with the drawings in the specific embodiments of the present invention.
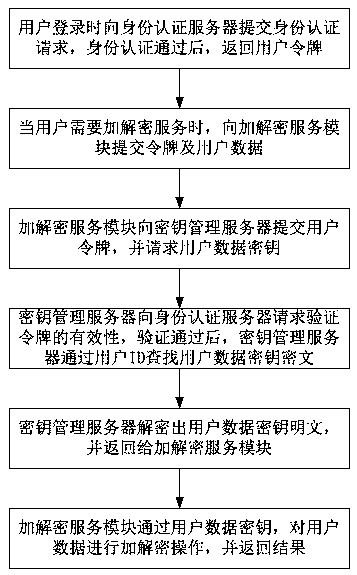
[0055] Such as figure 1 As shown, the present invention provides an identity-based closed key management method, which is characterized in that it includes the following steps:
[0056] Step 1. Submit an identity authentication request to the identity authentication server when the user logs in, and return the user token after the identity authentication is passed;
[0057] Step 2. When the user needs encryption and decryption services, submit the token and user data to the encryption and decryption service module;
[0058] Step 3. The encryption and decryption service module submits the user token to the key management server, and requests the user data key;
[0059] Step 4. ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More