Identity-based cloud storage efficient auditing method capable of acting and uploading data
A cloud storage and identity technology, applied in the field of cyberspace security, can solve problems such as inability to ensure data confidentiality and high computational overhead
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0051] The technical solutions of the present invention will be clearly and completely described below with reference to the embodiments. Obviously, the described embodiments are only a part of the embodiments of the present invention, rather than all the embodiments. Based on the embodiments of the present invention, all other embodiments obtained by those skilled in the art without creative efforts shall fall within the protection scope of the present invention.
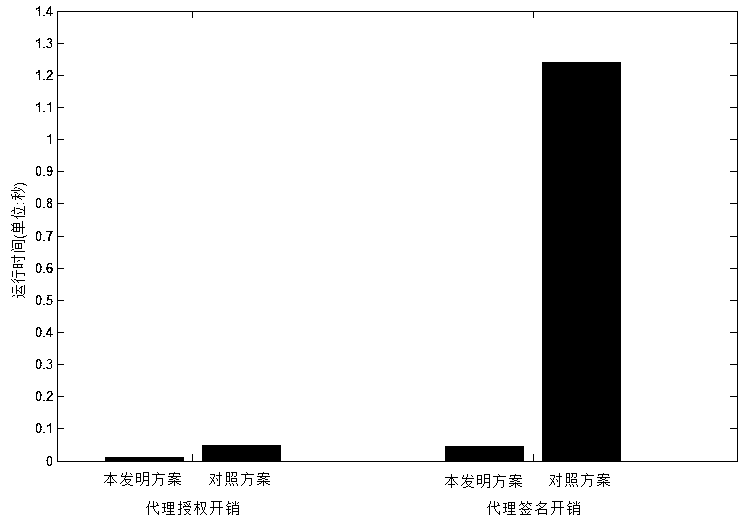
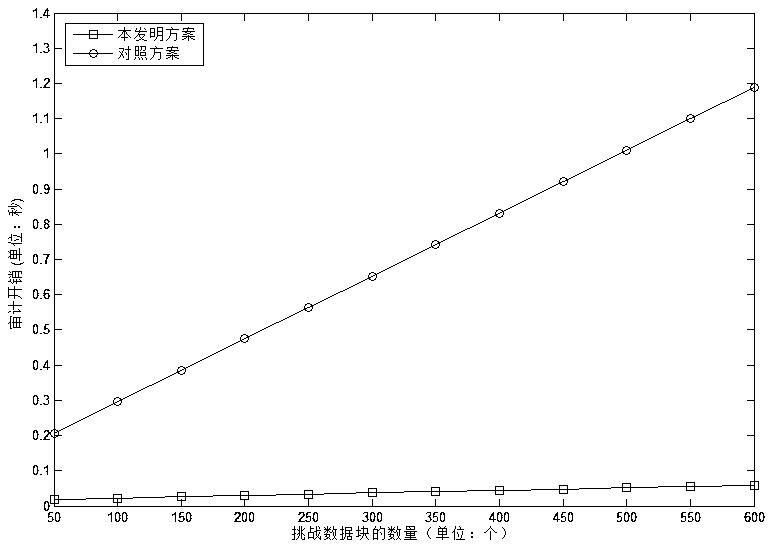
[0052] see Figure 1-3 , the present invention provides a technical solution based on an identity-based cloud storage efficient audit method that can upload data by proxy:
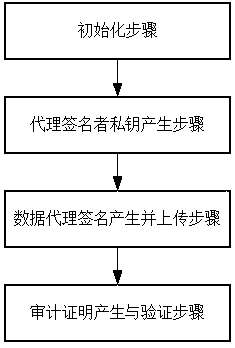
[0053] like figure 1 As shown, an efficient audit method for cloud storage based on identity that can proxy upload data, including:
[0054] S1. Initialization step: set the parameters of the elliptic curve-based digital signature algorithm, hash function, symmetric encryption algorithm, pseudo-random function and pseudo-random numb...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More