Privacy protection frequent item set mining method for large-scale shopping mall transaction record
A frequent item set mining and transaction recording technology, applied in the field of information security, can solve problems such as large amount of calculation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0049] The present invention will be described in further detail below in conjunction with the accompanying drawings and specific embodiments.
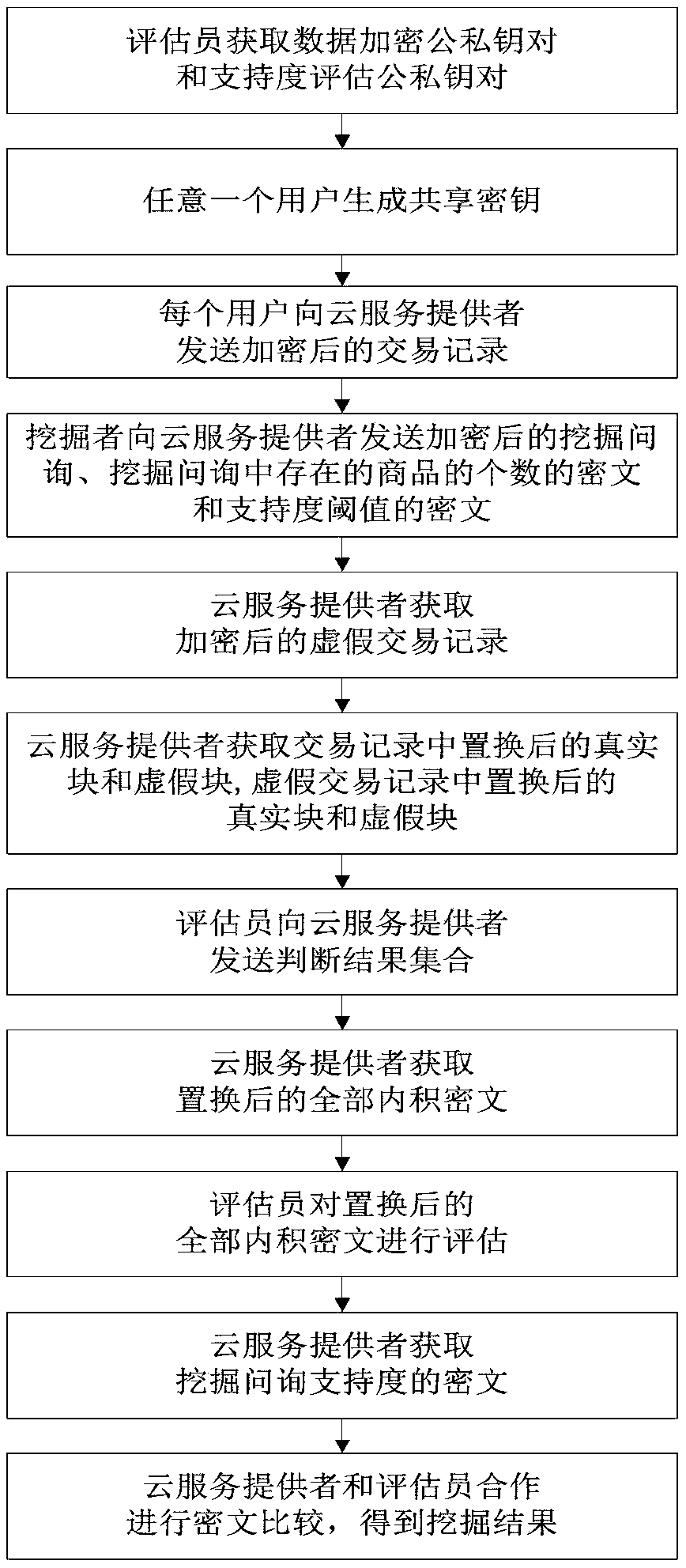
[0050] refer to figure 1 , a privacy-preserving frequent itemset mining method for transaction records of large shopping malls, including the following steps:
[0051] Step 1) The evaluator obtains the public-private key pair for data encryption and the public-private key pair for support evaluation:
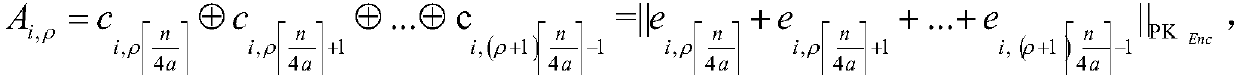
[0052] Step 1.1) Assessor adopts key generation algorithm Generate data encryption public-private key pair: Among them, λ 1 is the security parameter of the BGN cryptosystem, PK Enc is the public key used for data encryption, SK Enc is the private key used for data encryption;
[0053] Step 1.2) Assessor adopts key generation algorithm Generate support evaluation public-private key pair: Among them, λ 2 is the security parameter of the Paillier cryptosystem, PK Eva is the public key used for support evaluation, SK Eva is ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More