Method, device, storage medium and electronic device for defending data stream attack
A storage medium and data flow technology, applied in the field of communication, can solve problems such as occupation, limited resources of industrial control terminals, and damage to the operation of industrial control networks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
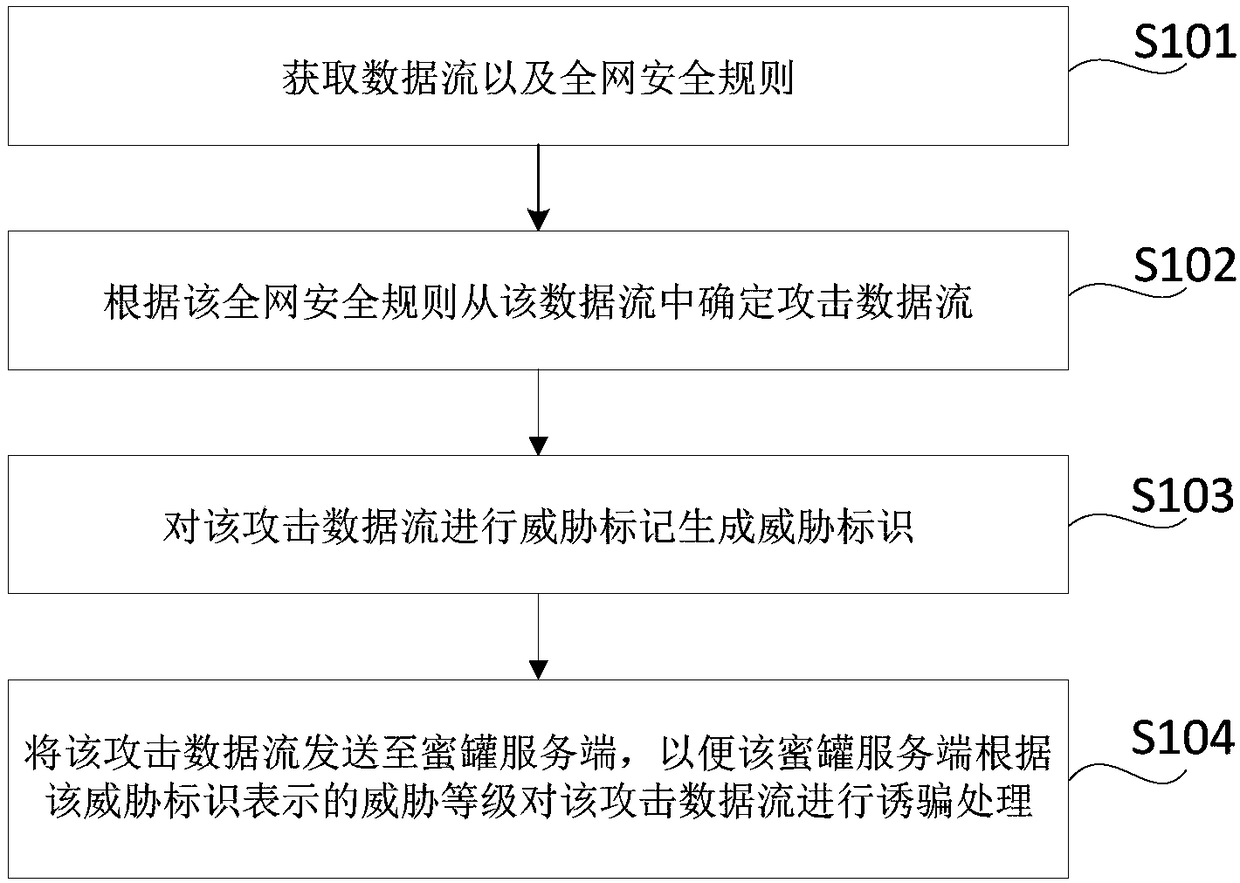
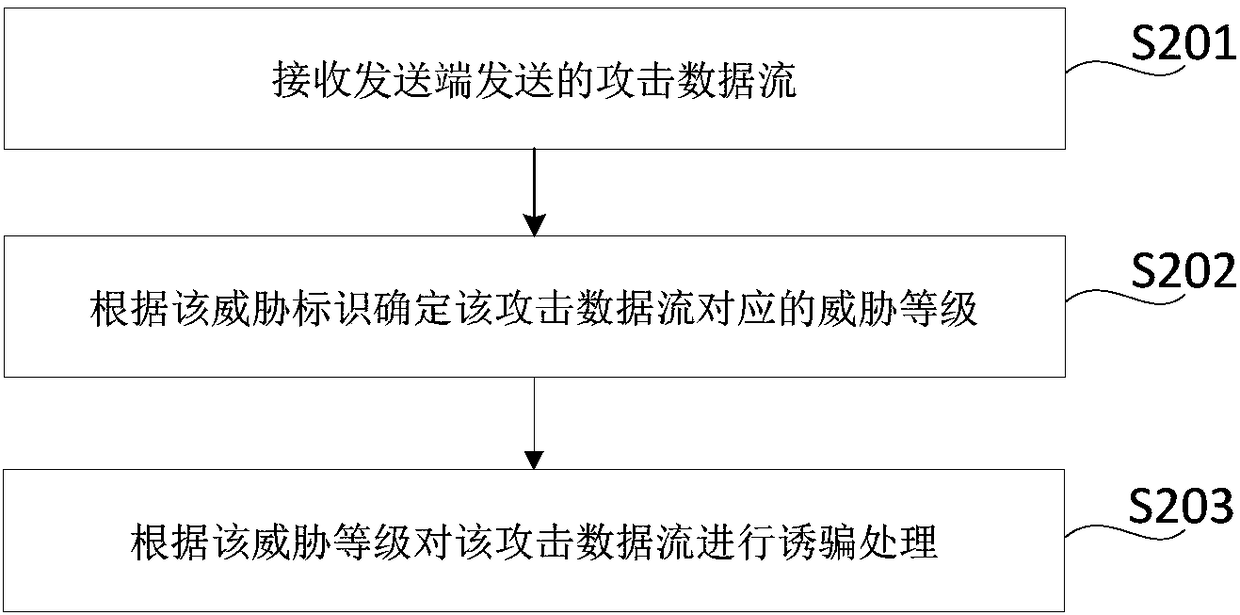
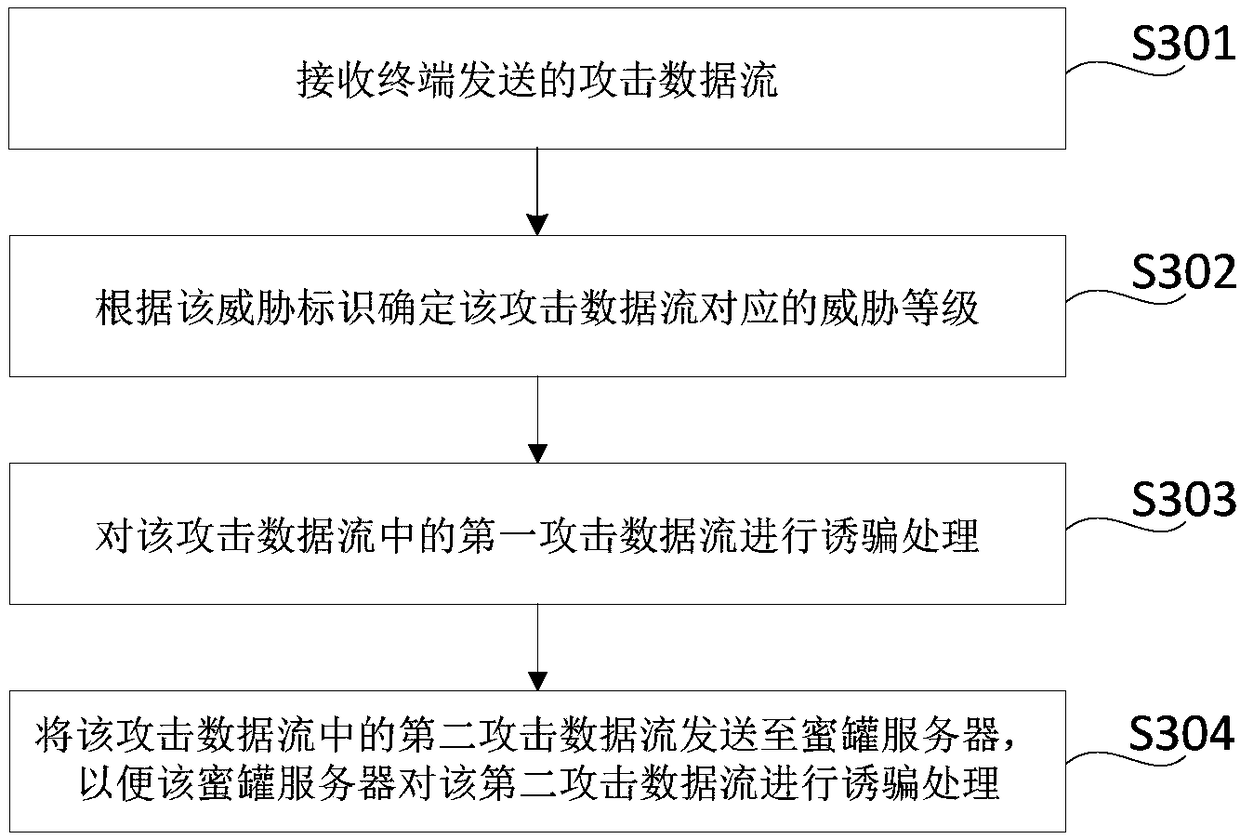
Method used
Image
Examples
Embodiment Construction
[0058] Specific embodiments of the present disclosure will be described in detail below in conjunction with the accompanying drawings. It should be understood that the specific embodiments described here are only used to illustrate and explain the present disclosure, and are not intended to limit the present disclosure.
[0059] First of all, the application scenario of the present disclosure is described. The present disclosure can be applied in industrial control networks to defend against data flow attacks through honeypot technology. Among them, the honeypot technology can attack by using real or simulated loopholes to lure attack data flows, thereby Ensure that the network is in a safe state, wherein the honeypot can be a trap program set on the terminal (such as the trap program can be a simulated system vulnerability), so that when the trap program lures the attack data flow to scan or attack, it can Activate the alarm and control decision tree for alarming.
[0060] H...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More