Method and system for identifying harmful video based on user IP and video copying
A video and user technology, applied in the field of information security, can solve problems such as insufficient recognition efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
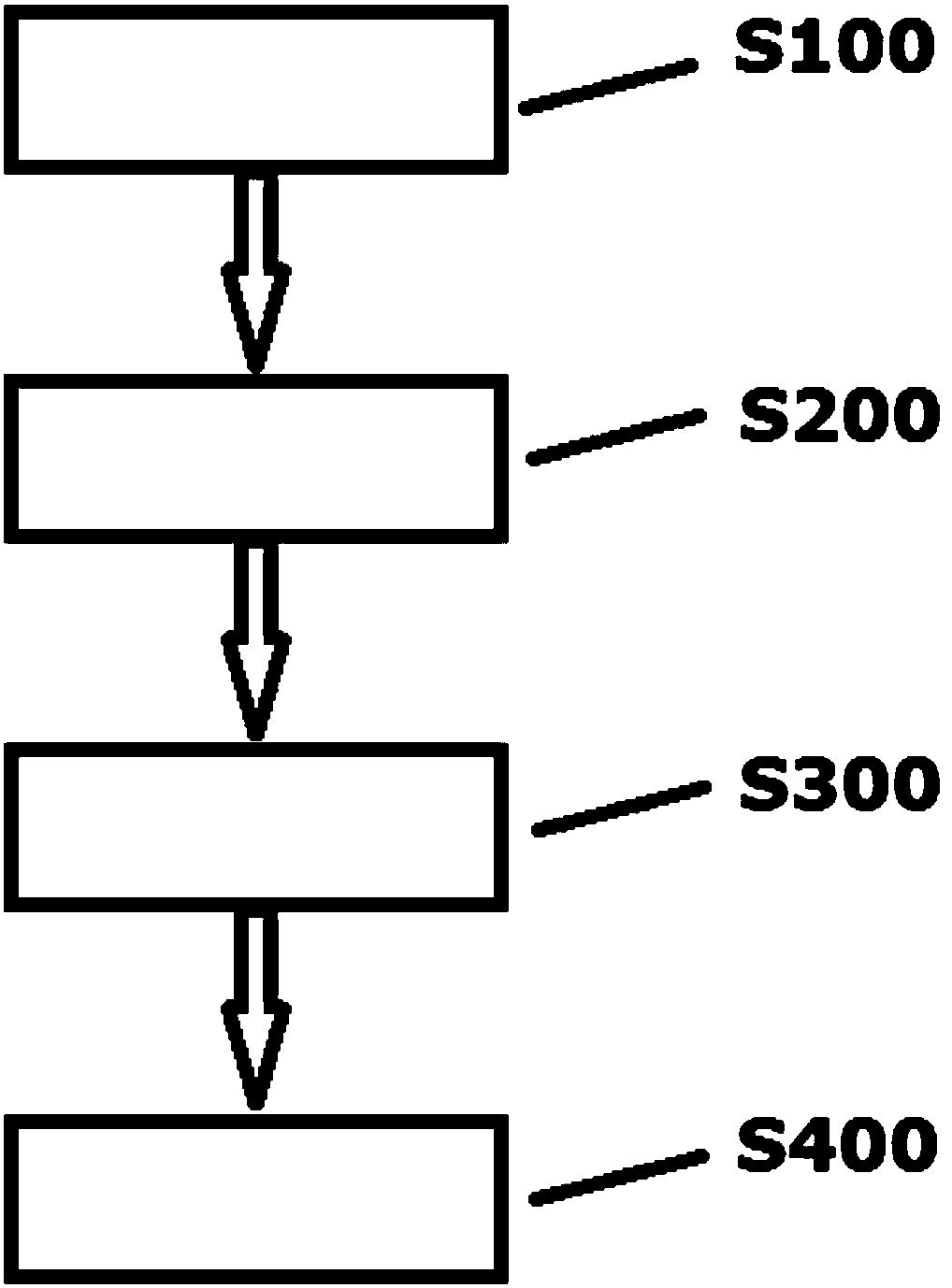
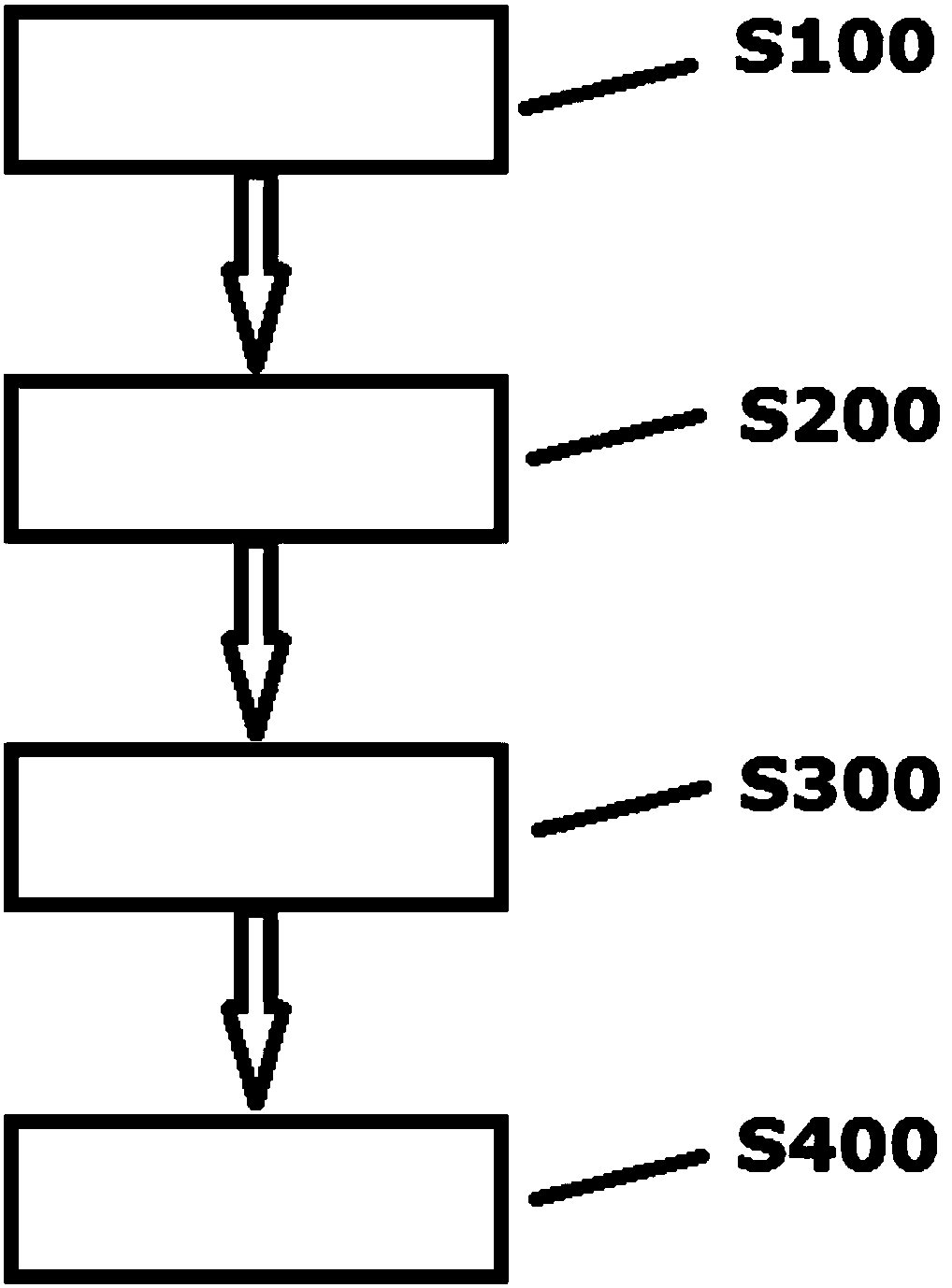
Image
Examples
Embodiment Construction
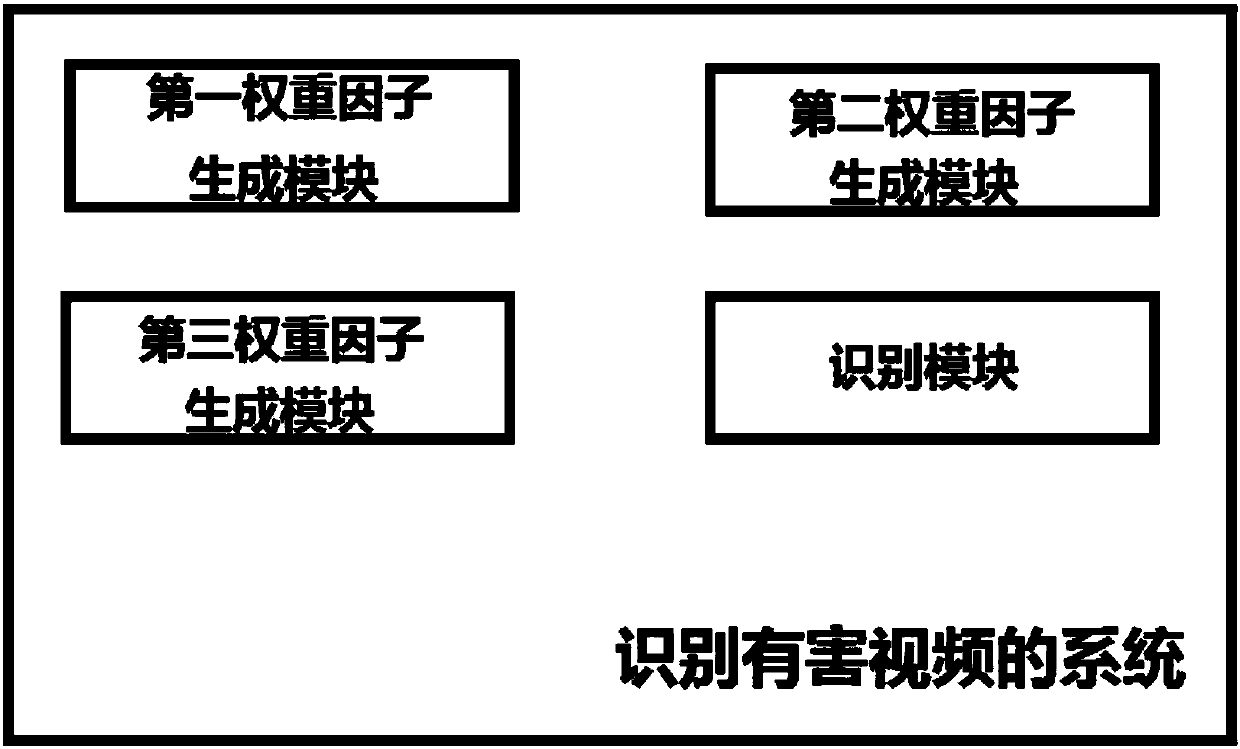
[0019] In order for those skilled in the art to understand the technical solutions disclosed in the present disclosure, the technical solutions of various embodiments will be described below in conjunction with the embodiments and related drawings. The described embodiments are part of the embodiments of the present disclosure, rather than Full examples. The terms "first", "second" and the like used in the present disclosure are used to distinguish different objects, not to describe a specific order. Furthermore, "comprising" and "having", as well as any variations thereof, are intended to be inclusive and non-exclusive. For example, a process comprising a series of steps or units, or a method, or a system, or a product or a device is not limited to the listed steps or units, but optionally also includes steps or units not listed, or optionally It also includes other steps or elements inherent to these processes, methods, systems, products or devices.
[0020] Reference here...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More