Risk control method and device
A risk control and risk technology, applied in the field of information security, can solve problems such as increasing the complexity of risk control
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0017] The subject matter described herein will now be discussed with reference to various examples. It should be understood that the discussion of these embodiments is only to enable those skilled in the art to better understand and realize the subject matter described herein, and is not intended to limit the protection scope, applicability or examples set forth in the claims. Changes may be made in the function and arrangement of elements discussed without departing from the scope of the claims. Various embodiments may omit, replace or add various procedures or components as needed.
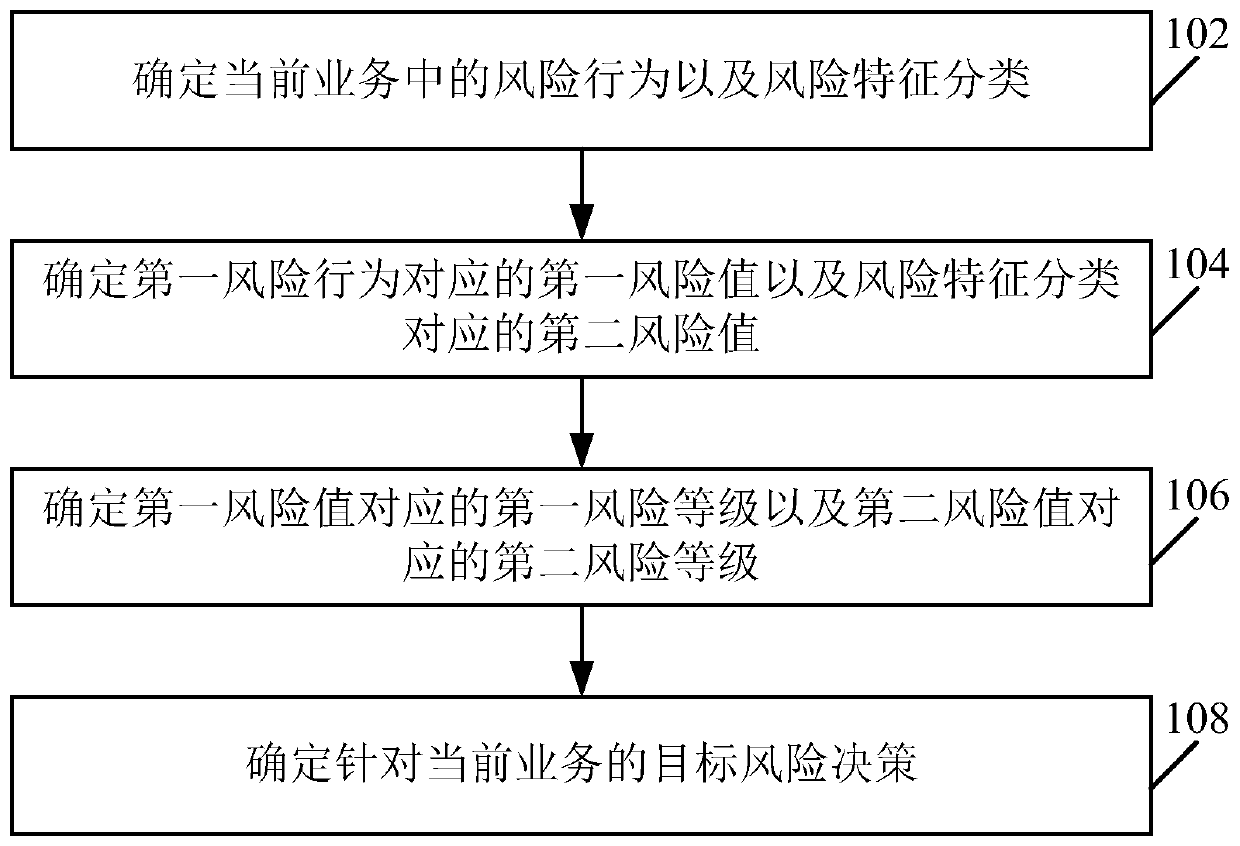
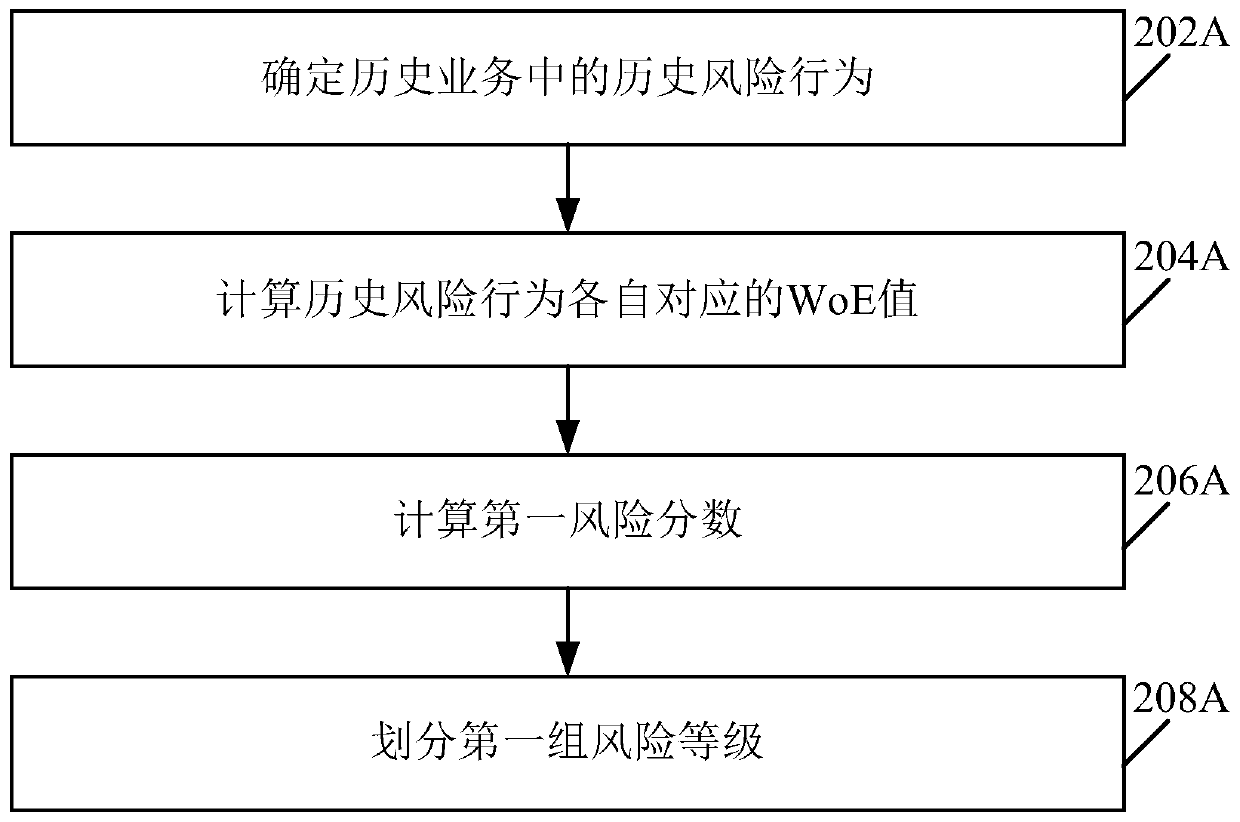
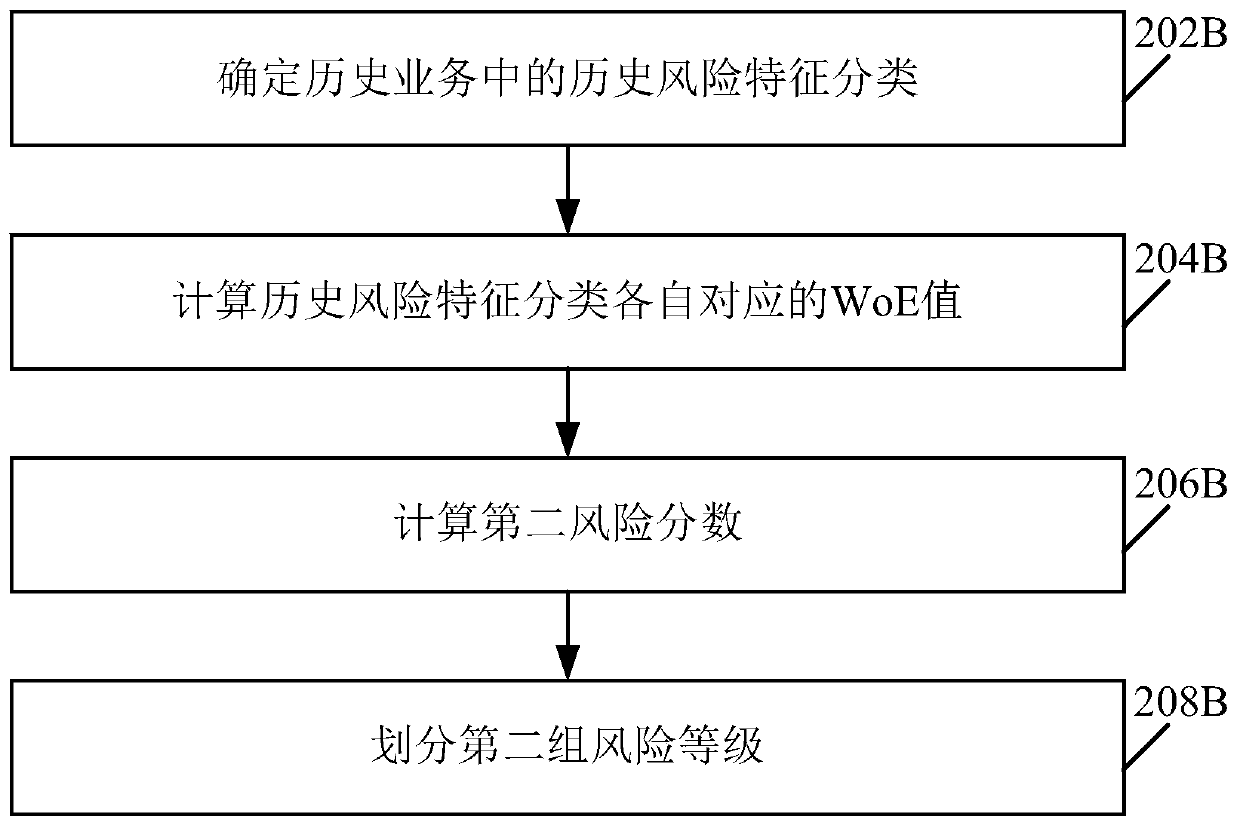
[0018] At present, risk control for various businesses conducted on the network has become one of the main concerns. For example, in Internet finance scenarios, risk control is usually carried out through a standardized policy system. The standardized policy system can include policies in multiple dimensions. For example, the card replacement baseline policy is used to limit the number of ban...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More