Safety verification system, method and device
A security verification and server technology, applied in transmission systems, data processing applications, finance, etc., can solve problems such as poor crawler interception effect, and achieve the effect of solving the decision-making degree and ensuring the interception effect.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
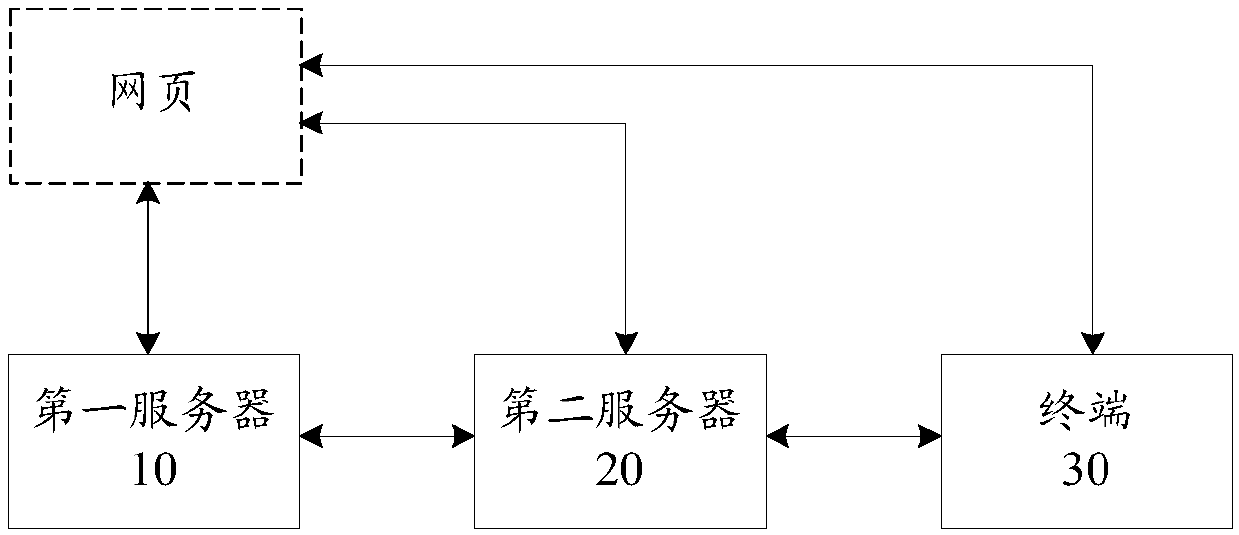
[0040] According to an embodiment of the present invention, an embodiment of a security verification system is provided. This application provides the following figure 1 The schematic diagram of the safety verification system shown, the system includes:
[0041] The first server 10 monitors the behavior data generated by the behavior for operating the webpage when the webpage runs the logged-in target application through the browser, and determines whether the behavior data is risky.
[0042] Specifically, the above-mentioned first server may be a data server deployed remotely or locally for risk control. The first server may be installed with a risk control engine, and run preset risk control rules through the risk control engine, so as to control behavior judge whether the data is at risk. The first server can communicate with the second server and the terminal to send the risk control result of the behavior data (that is, the judgment result of whether there is risk) to th...
Embodiment 2
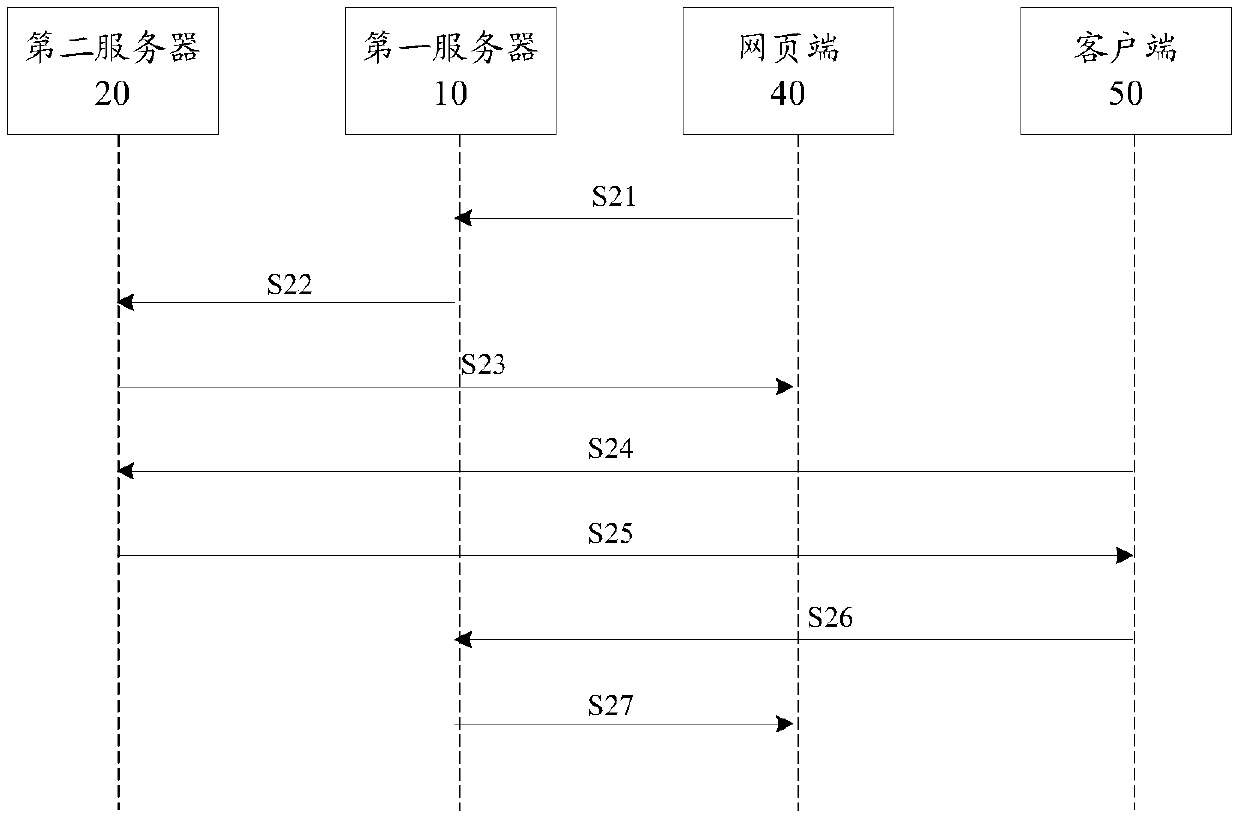
[0102] According to an embodiment of the present invention, an embodiment of a security verification method is also provided. It should be noted that the steps shown in the flow chart of the accompanying drawings can be executed in a computer system such as a set of computer-executable instructions, Also, although a logical order is shown in the flowcharts, in some cases the steps shown or described may be performed in an order different from that shown or described herein.
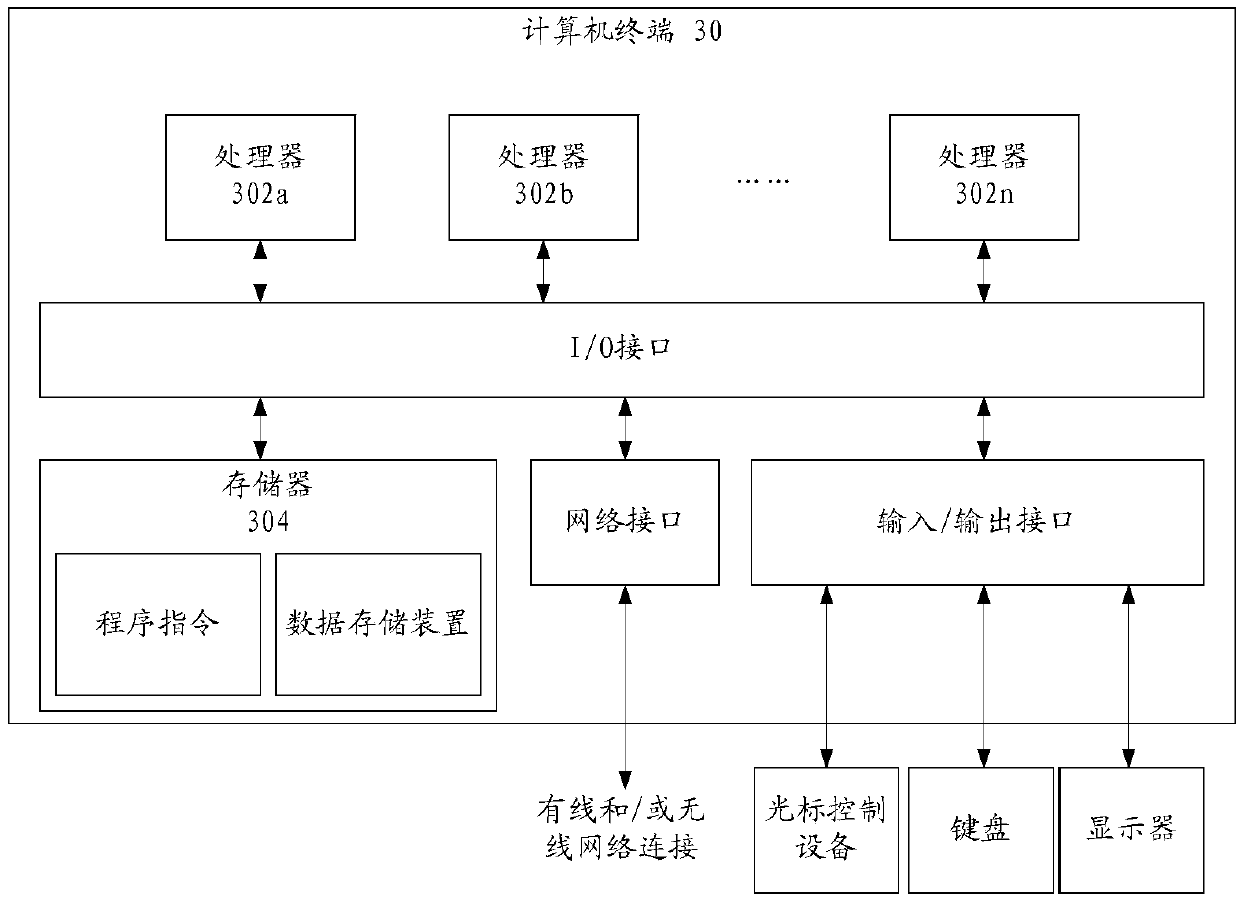
[0103] The method embodiment provided in Embodiment 1 of the present application may be executed in a mobile terminal, a computer terminal, or a similar computing device. image 3 A block diagram of a hardware structure of a computer terminal (or mobile device) for implementing a method for security verification is shown. Such as image 3 As shown, the computer terminal 30 (or mobile device 30) may include one or more (shown by 302a, 302b, ..., 302n in the figure) processor 302 (the processor 302 may inc...
Embodiment 3
[0124] According to an embodiment of the present invention, an embodiment of a security verification method is provided, Figure 5 It is a flowchart of a method for security verification according to Embodiment 3 of the present application, the method includes:
[0125] Step S51, the second server generates a verification ID according to the control of the first server, wherein, when the webpage runs the logged-in target application through the browser, the first server monitors the behavior data generated by the behavior used to operate the webpage, and In the case that the data is at risk, the second server is controlled to generate a verification identifier.
[0126] Specifically, the above-mentioned second server may be a second server deployed on the target application server, and the above-mentioned verification identification may be a two-dimensional code or a bar code, and the second server may generate a verification identification according to the account information...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More