Cooperative secret sharing method, device and system based on vacant transmission algorithm, and medium
A secret sharing and secret technology, applied in the field of distributed computing, can solve problems such as low execution efficiency, inability to obtain information, and large amount of computation in OT protocols
- Summary
- Abstract
- Description
- Claims
- Application Information
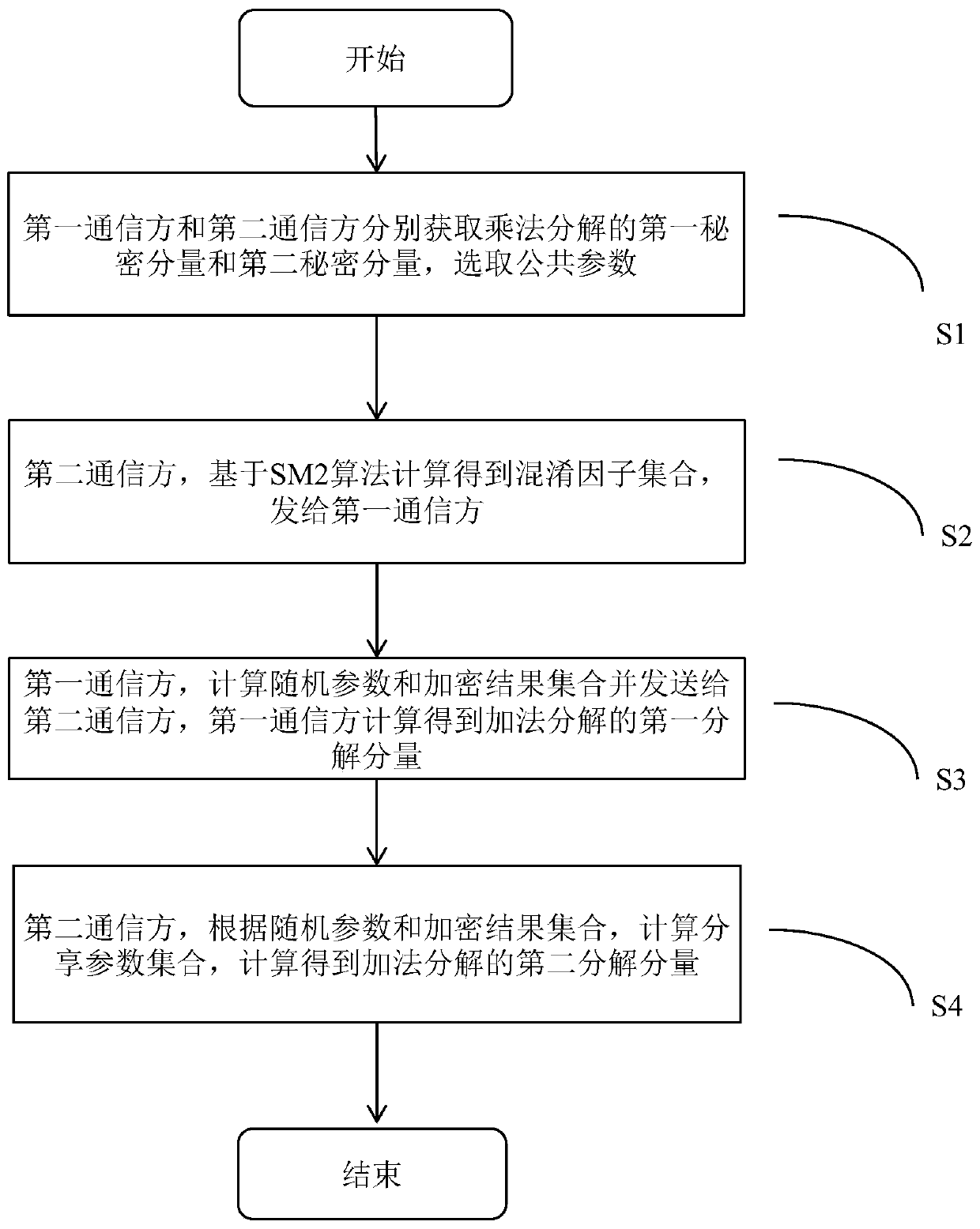
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0106] In order to make the object, technical solution and advantages of the present invention clearer, the present invention will be further described in detail below in conjunction with the accompanying drawings and embodiments. It should be understood that the specific embodiments described here are only used to explain the invention, not to limit the invention.
[0107] Elliptic curve cryptography (ECC, Elliptic curve cryptography) is a public key system based on an elliptic curve algorithm defined on a finite field. The SM2 algorithm is a specific algorithm of the ECC cryptosystem. An elliptic curve public key cryptography algorithm is specified in the national standard "GB / T 32918 Information Security Technology SM2 Elliptic Curve Public Key Cryptography Algorithm". The encryption algorithm and decryption algorithm based on SM2 conform to the provisions of this standard.
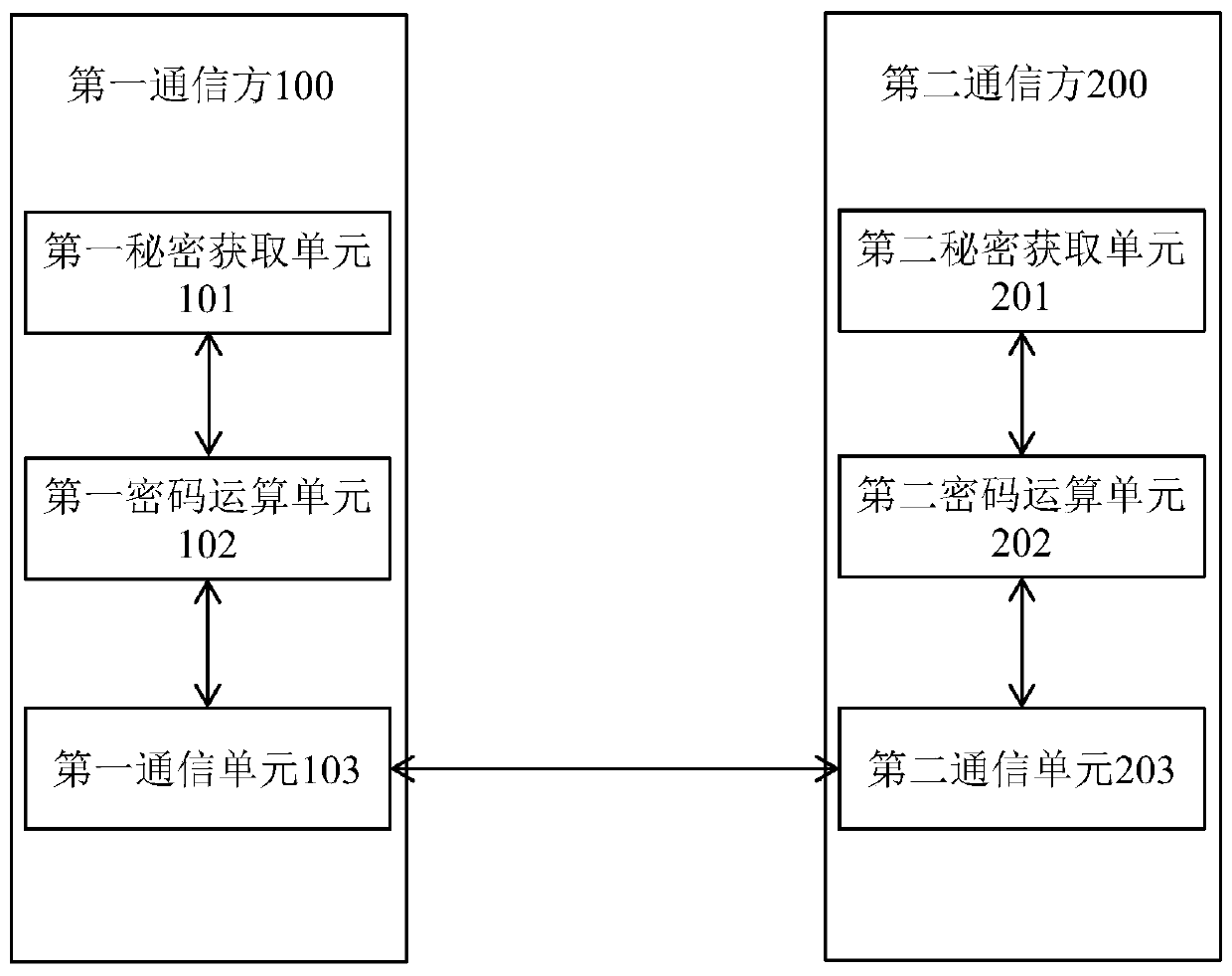
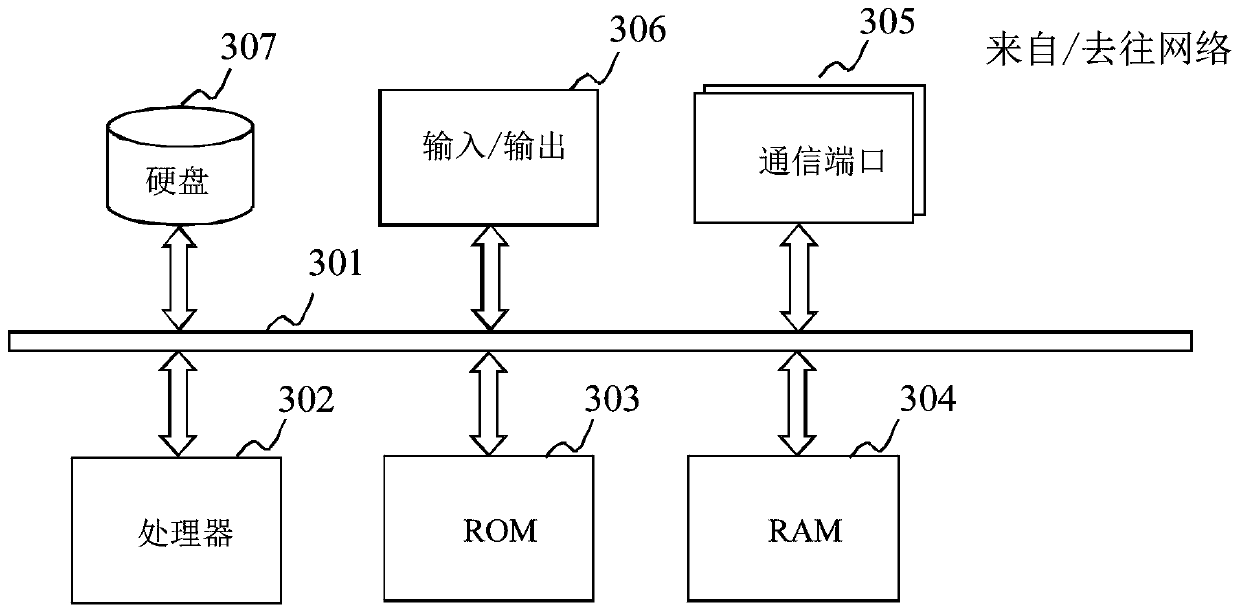
[0108] The technical solution of the present invention is based on Elliptic Curve Cryptography (EC...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More