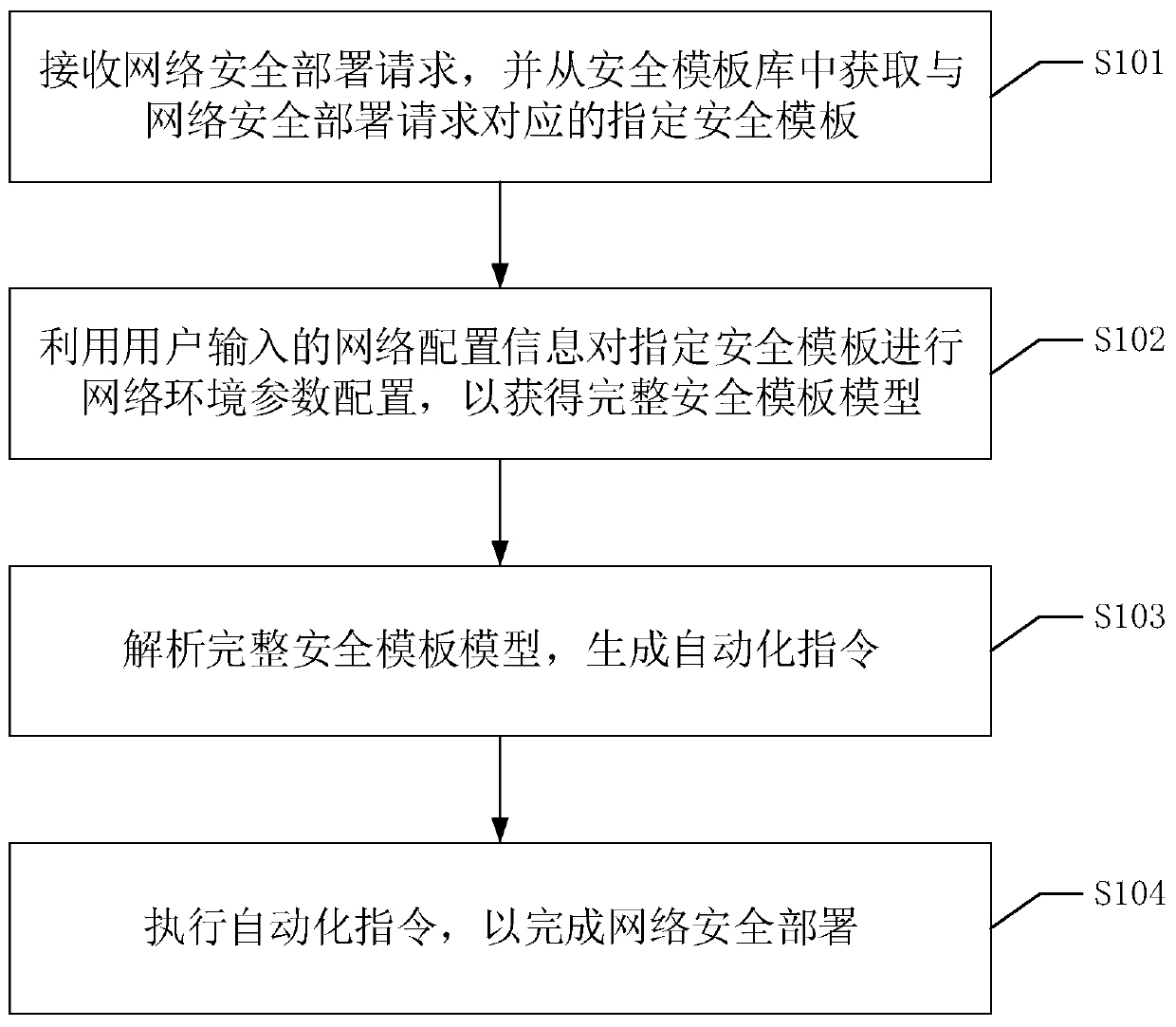
Network security deployment method, device and equipment and readable storage medium
A technology for network security and network configuration information, which is applied in the fields of equipment and readable storage media, network security deployment methods, and devices, and can solve problems such as low efficiency and failure to meet user needs
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
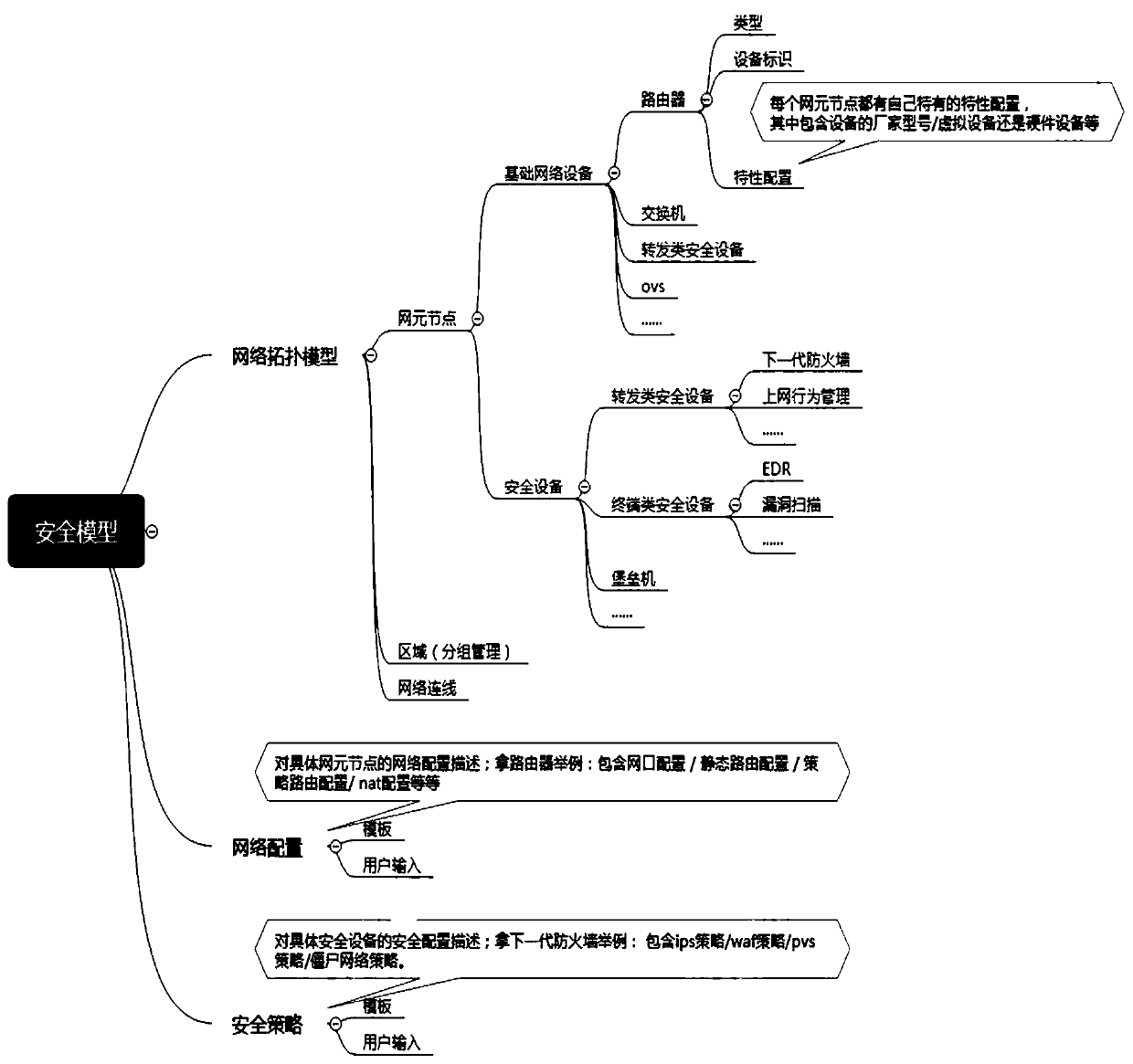
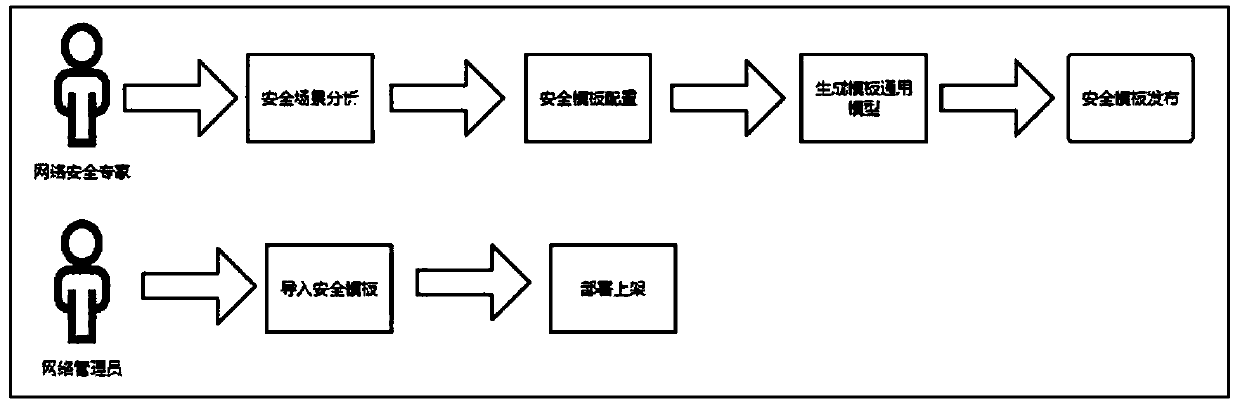
Method used
Image
Examples
Embodiment Construction
[0053] In order to enable those skilled in the art to better understand the solution of the present invention, the present invention will be further described in detail below in conjunction with the accompanying drawings and specific embodiments. Apparently, the described embodiments are only some of the embodiments of the present invention, but not all of them. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
[0054] For the convenience of description, the abbreviations or related technical names involved in this article are explained below:
[0055] NFV (Network Functions Virtualization): Network function virtualization, using virtualization technology to divide the functions of the network node level into several functional blocks, which are implemented in software, and are no longer limited to hardware architectu...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More