Attack detection method based on Internet cross search defects
A cross-search and attack detection technology, applied in the field of Internet search, can solve problems such as poor security performance, poor reliability, and single detection means, and achieve the effect of efficiently restricting operation
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
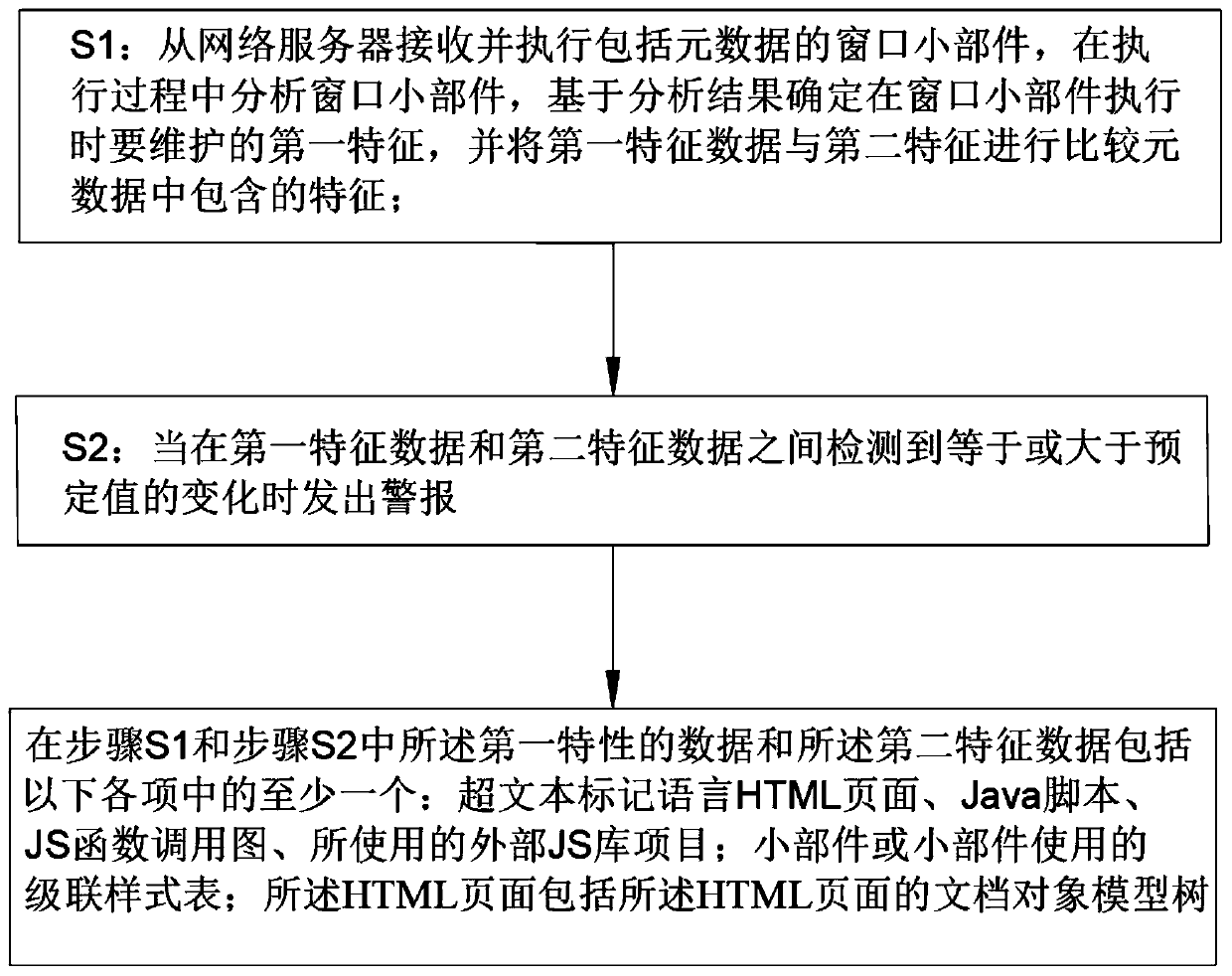
Embodiment 1
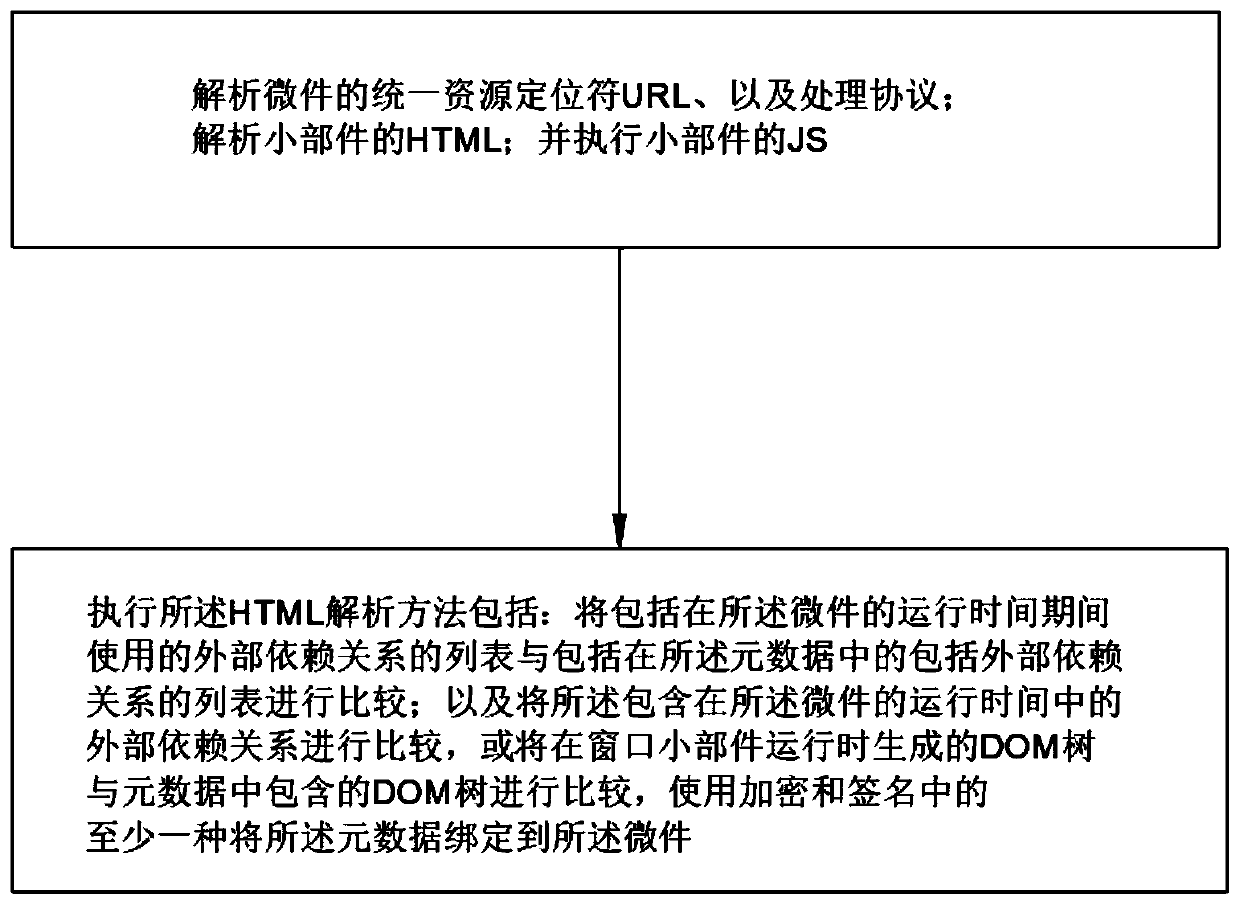
[0036] Embodiment 1: An attack detection method based on Internet cross search flaws, S1: Receive and execute a widget including metadata from a web server, analyze the widget during execution, and determine based on the analysis result that the widget is executed The first feature to be maintained, and compare the data of the first feature with the features contained in the second feature metadata; S2: configured to be equal to when detected between the data of the first feature and the data of the second feature or a change greater than a predetermined value; the data of the first characteristic and the data of the second characteristic include at least one of the following items: hypertext markup language HTML pages, Java scripts, JS function call graphs, so An external JS library item used; a widget or a cascading style sheet used by the widget; the HTML page includes a document object model tree of the HTML page; parsing the uniform resource locator URL of the widget, and ...
Embodiment 2
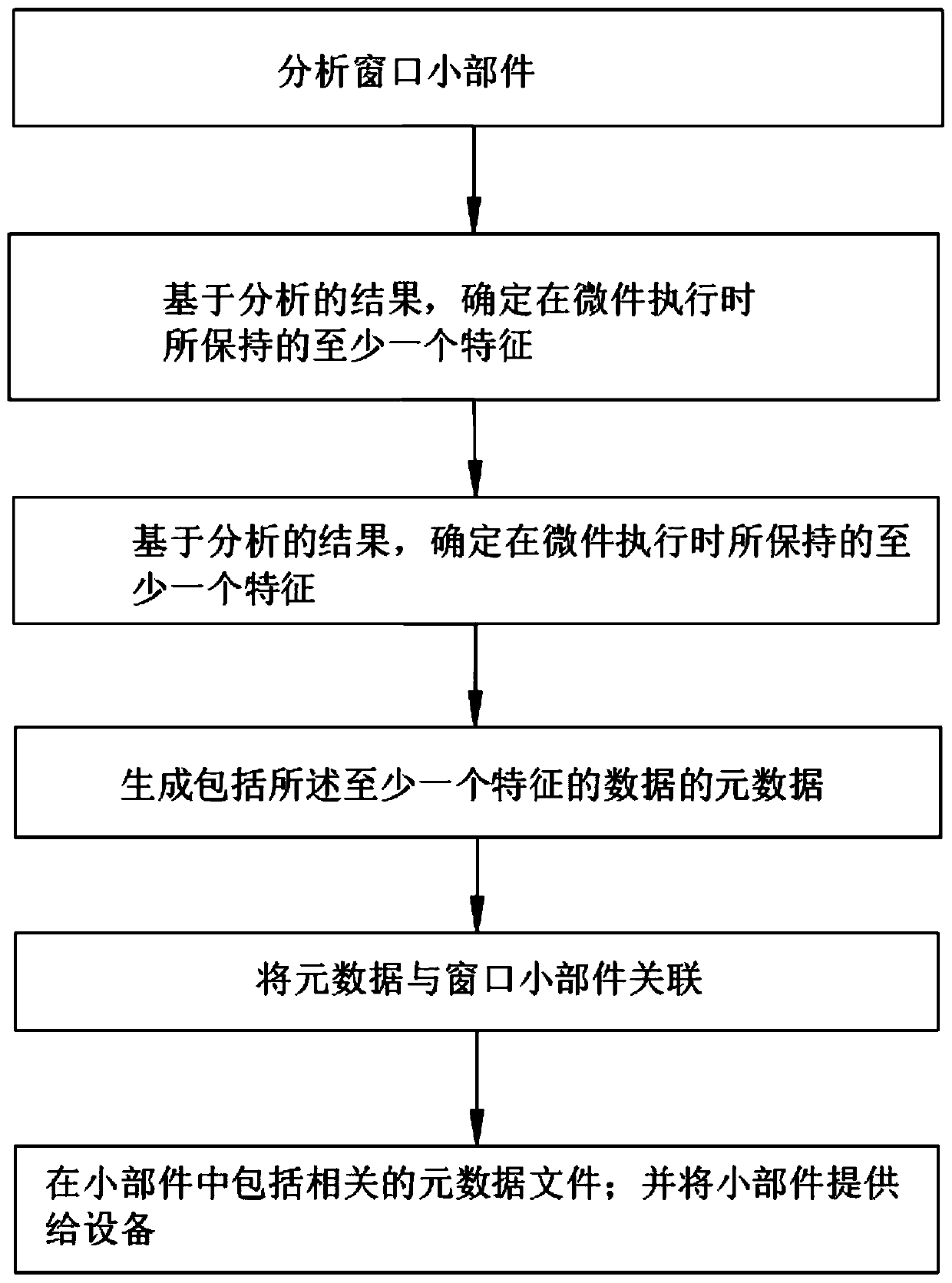
[0037]Embodiment 2: This embodiment should be understood as at least including all the features of any one of the foregoing embodiments, and further improvements are made on the basis of it. Specifically, an attack detection method based on Internet cross search defects includes the following steps: S1: Receive and execute a widget including metadata from a web server, analyze the widget during execution, determine a first feature to be maintained when the widget is executed based on the analysis result, and compare the data of the first feature with the The second feature compares the features contained in the metadata; S2: configured to issue an alarm when a change equal to or greater than a predetermined value is detected between the data of the first feature and the data of the second feature; specifically, when performing crossover During the search process, web pages often have orphan pages implanted. In this case, there are various small windows floating on the surface o...
Embodiment 3
[0049] Embodiment 3: This embodiment should be understood as at least including all the features of any one of the foregoing embodiments, and further improvements are made on the basis thereof. Specifically, this embodiment provides a product for executing a Web program, including: a hardware storage device , having stored therein computer executable program code which, when executed by a computer hardware system comprising a security system configured to test a Web service, causes the computer hardware system to perform the following operations: The service performs static analysis; the security system performs static analysis on the web service; during the static analysis, locates seed instructions in the program code of the web service, where the identity of the requester is determined by the web service; during the static analysis, determines the seed Whether the value in the instruction selects between multiple paths branched in the program code is determinative; and the s...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More