Distributed denial of service attack detection method, device and equipment and storage medium
A distributed rejection and detection method technology, applied in the Internet field, can solve the problems of low detection efficiency and detection accuracy, large traffic, and the inability to effectively distinguish whether the burst traffic is normal burst traffic or DDoS attack traffic, so as to improve detection efficiency and detection accuracy, avoiding the effect of misjudgment
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment 1
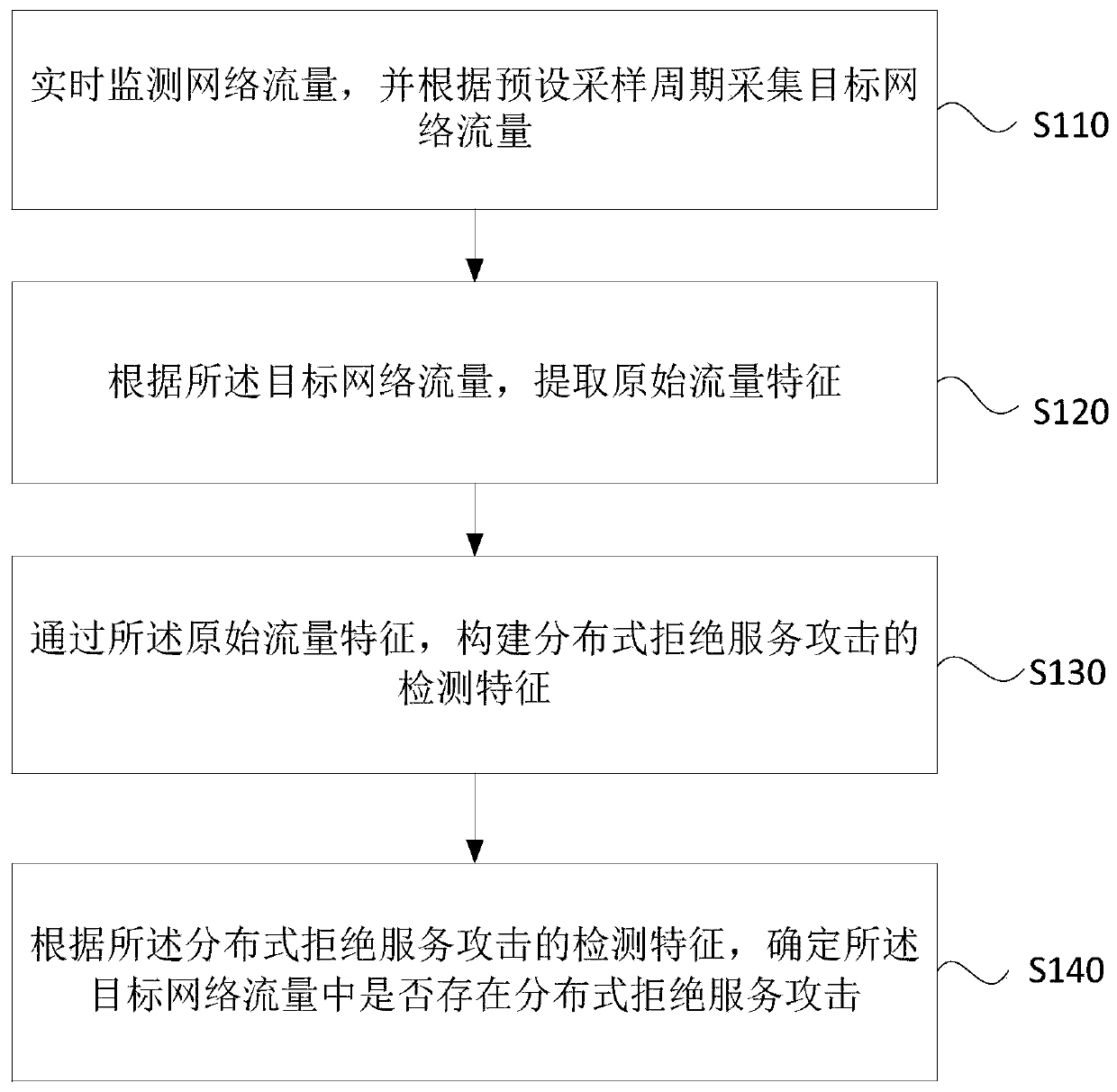
[0028] figure 1 This is a flowchart of a method for detecting a distributed denial of service attack according to Embodiment 1 of the present invention. This embodiment is applicable to detecting whether there is a distributed denial of service attack in network traffic. A distributed denial-of-service attack detection device can be implemented by software and / or hardware and integrated in a server, typically a Web (World Wide Web, global wide area network) server or a DNS (Domain Name System, Domain Name System Protocol) server, the method specifically includes the following steps:
[0029] S110. Monitor network traffic in real time, and collect target network traffic according to a preset sampling period.
[0030] In order to improve the security performance of the server, the sampling period can be set to a small value, so that the server can detect as many distributed denial-of-service attacks as possible to ensure the security of network communication; to reduce the proc...
Embodiment 2
[0076] figure 2 A flowchart of a method for detecting a DDoS attack provided in Embodiment 2 of the present invention. In this embodiment, the method for detecting a DDoS attack is embodied, and the detection features of a DDoS attack are Input into the pre-trained detection model, and determine whether there is a distributed denial of service attack in the target network traffic according to the output result. Specifically, the method includes the following steps:
[0077] S201, obtaining an initial GHSOM neural network detection model; and performing S202.
[0078] Specifically, the acquisition of the initial growing hierarchical self-organizing mapping neural network model mainly includes the following steps:
[0079] First, initialize the neurons in layer 0; since there is only one neuron in layer 0, the initial weight of the neuron is the average value of all training samples, and the average quantization error of this layer is calculated based on this; among them, the ...
Embodiment 3
[0102] image 3 It is a structural block diagram of a distributed denial-of-service attack detection device provided in Embodiment 3 of the present invention. The device is applied to a server and specifically includes: a target network traffic acquisition module 310, an original traffic feature extraction module 320, and a detection feature acquisition module. module 330 and an attack detection execution module 340 .
[0103] A target network traffic acquisition module 310, configured to monitor network traffic in real time, and collect target network traffic according to a preset sampling period;
[0104] An original traffic feature extraction module 320, configured to extract original traffic features according to the target network traffic;
[0105] A detection feature acquisition module 330, configured to construct a detection feature of a distributed denial-of-service attack through the original traffic feature;
[0106] The attack detection execution module 340 is con...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More