5G application access authentication method and 5G application access authentication network architecture
An access authentication and 5G technology, applied in the field of communication security, to achieve the effect of reducing the attack surface
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0022] Specific embodiments of the present invention will be described in detail below in conjunction with the accompanying drawings. It should be understood that the specific embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
[0023] Figure 5 It is a schematic structural diagram of a 5G application access authentication network architecture provided by an embodiment of the present invention. like Figure 5 As shown, the embodiment of the present invention provides a 5G application access authentication network architecture, the network architecture includes: electric power 5G terminal; DN-AAA server, used for identity verification of the electric power 5G terminal; SMF / UPF, used for passing the authentication information exchanged between the electric power 5G terminal and the DN-AAA server.
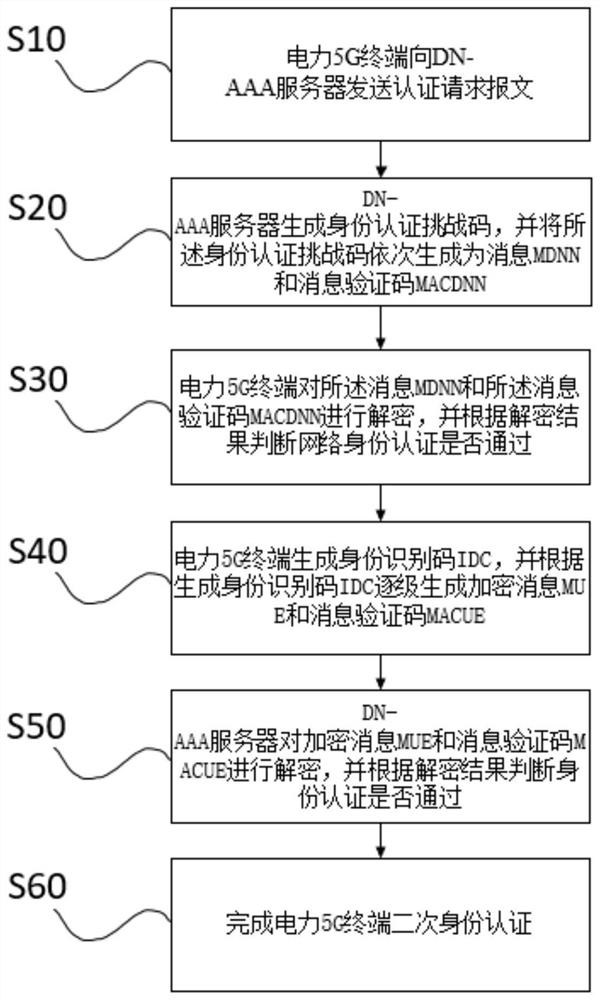
[0024] figure 1 It is a method flowchart of a 5G application access authentication meth...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More