Method for detecting resistance of OCB authentication encryption algorithm to differential fault attacks
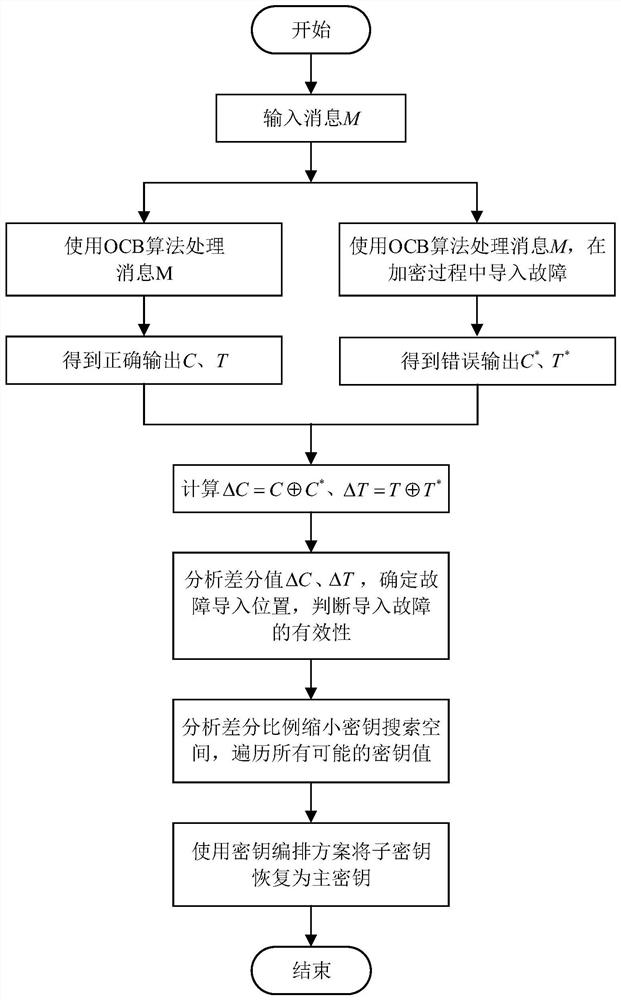
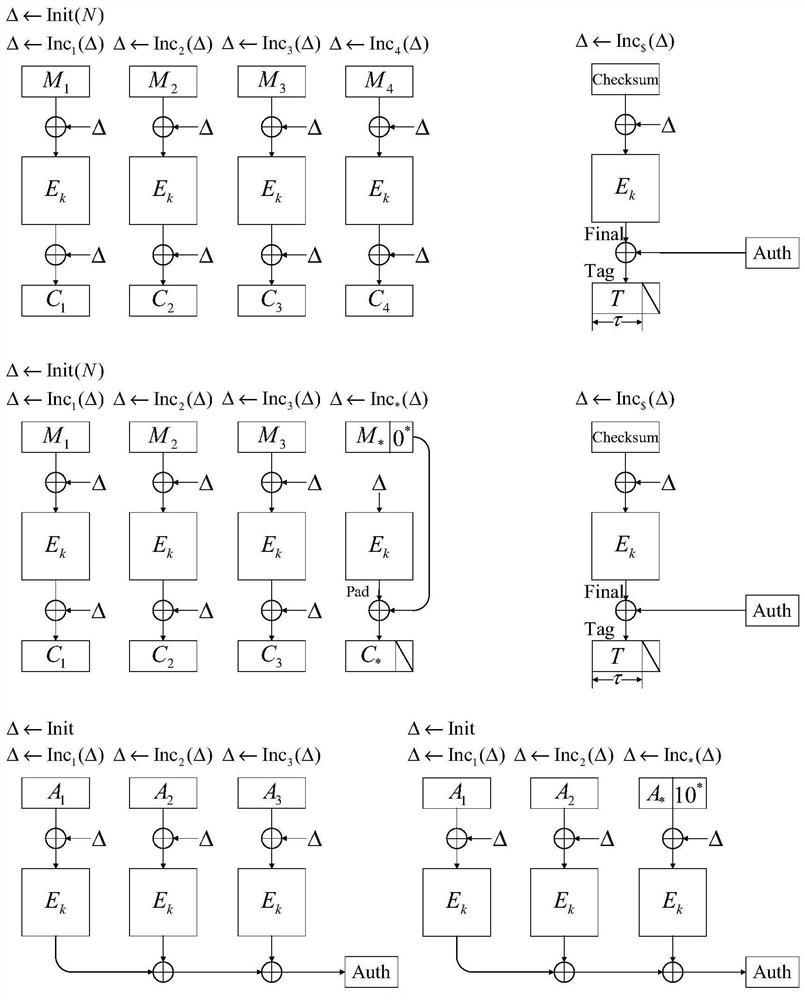
A differential fault attack, authentication and encryption technology, applied in the field of information security, can solve security risks, evaluate OCB authentication and encryption algorithms to resist differential fault attacks, etc.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
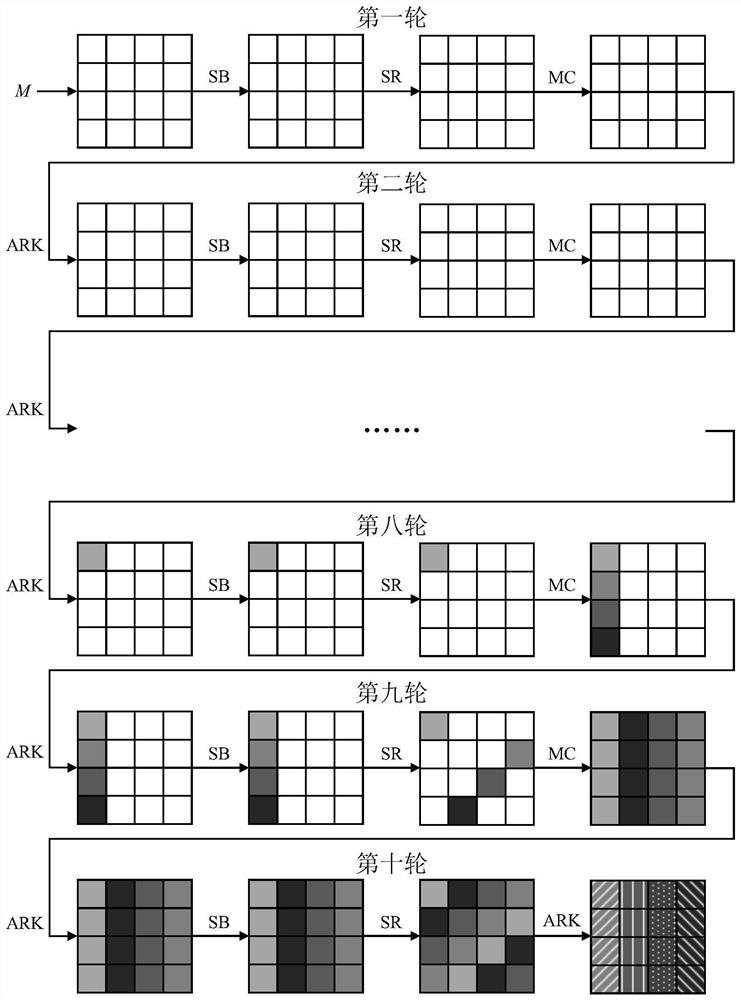
Embodiment Construction
[0051] Below in conjunction with specific embodiment, further illustrate the present invention. It should be understood that these examples are only used to illustrate the present invention and are not intended to limit the scope of the present invention. In addition, it should be understood that after reading the teachings of the present invention, those skilled in the art can make various changes or modifications to the present invention, and these equivalent forms also fall within the scope defined by the appended claims of the present application.
[0052] The symbols used in this example are explained as follows:
[0053] : XOR operation;
[0054] Δ: difference operation;
[0055] M: message plaintext;
[0056] K i : the i-th byte of the key K;
[0057] C: the correct ciphertext output;
[0058] C * : The wrong ciphertext output after the import failure;
[0059] ΔC: the difference between the correct ciphertext and the wrong ciphertext in the ninth round after ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More - R&D
- Intellectual Property
- Life Sciences
- Materials
- Tech Scout
- Unparalleled Data Quality
- Higher Quality Content
- 60% Fewer Hallucinations
Browse by: Latest US Patents, China's latest patents, Technical Efficacy Thesaurus, Application Domain, Technology Topic, Popular Technical Reports.
© 2025 PatSnap. All rights reserved.Legal|Privacy policy|Modern Slavery Act Transparency Statement|Sitemap|About US| Contact US: help@patsnap.com