Multi-backup secure deletion method and system based on blockchain
A security deletion, blockchain technology, applied in the field of information security, can solve the problem of not being able to guarantee that the data in the cloud will not be cracked
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0047] The technical solutions in the embodiments of the present invention will be described clearly and in detail below with reference to the drawings in the embodiments of the present invention. The described embodiments are only some of the embodiments of the invention.
[0048] The technical scheme that the present invention solves the problems of the technologies described above is:
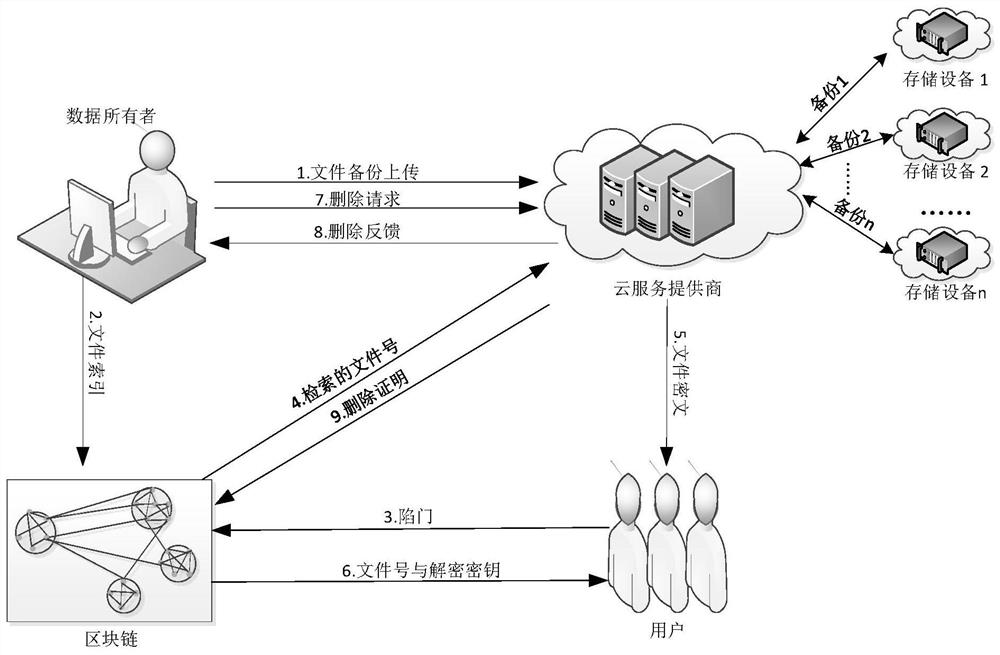
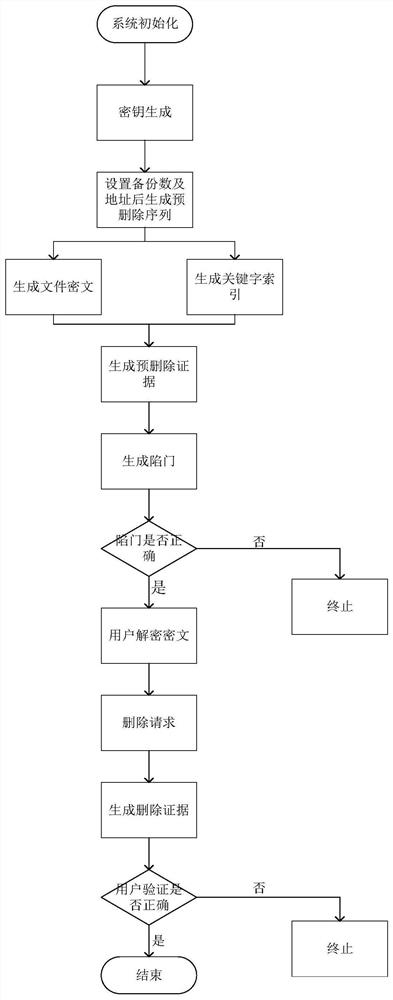
[0049] Attached below figure 1 Describe the framework of the system.
[0050](1) Data owner: After generating the file number and master key, encrypt and upload the file that needs to be uploaded to the cloud server to the cloud server, and extract the file keyword and calculate it as a file index and upload it to the smart contract; in the deletion stage, the data owner A deletion request can be sent to the cloud server, and the cloud server can receive deletion feedback after deletion; in the verification phase, the data owner can verify deletion according to the deletion feedback sent b...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More