SM2-based data processing method and system and electronic equipment
A data processing and equipment technology, applied in the field of information security, can solve the problems of low data processing efficiency and large data processing volume
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
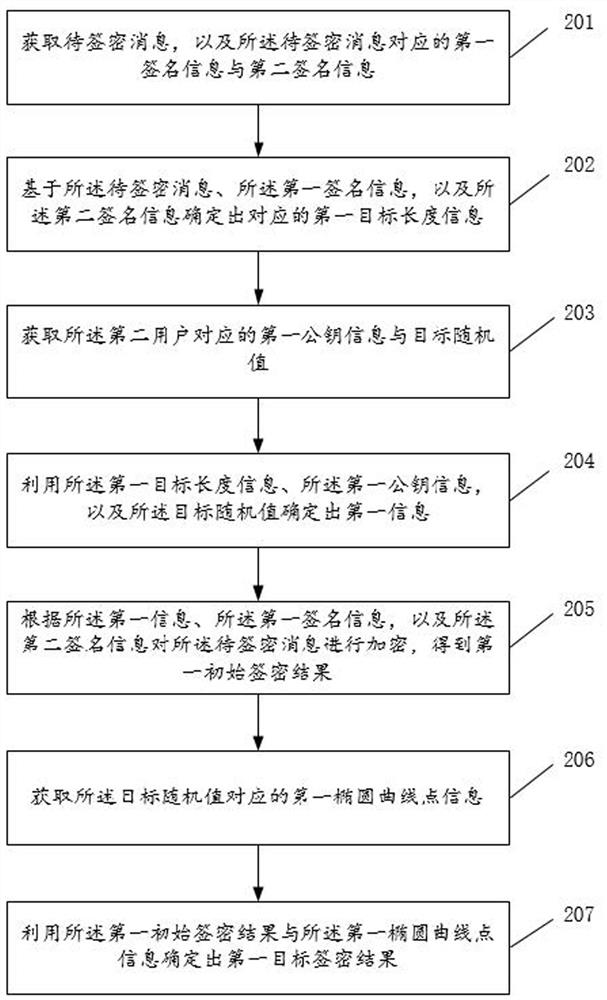
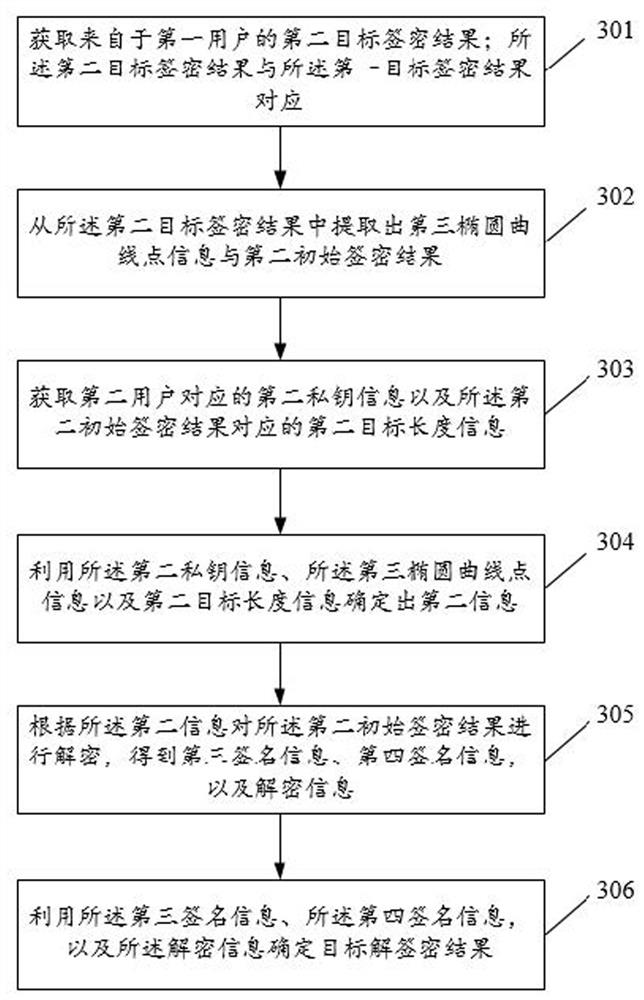
Method used
Image
Examples
Embodiment Construction
[0019] Abbreviations and key terms involved in this application:
[0020] F p : a prime field containing p elements;
[0021] E(F p ): F p The set of all rational points (including the point O at infinity) on the elliptic curve E;
[0022] (p ,a ,b ,G ,n ,h): the curve parameters of the SM2 algorithm, where p is a prime number with a length of 256 bits;
[0023] a and b are F p elements in which define F p an elliptic curve E on
[0024] G is the base point, and the coordinates are expressed as G=(x G ,y G );
[0025] n is the order of G; h is the cofactor;
[0026] H v ( ): A cryptographic hash function with a message digest length of v bits, which uses SM3;
[0027] ID A : User A's identity;
[0028] ENTL A :ID A length, ENTL A The length is 2 bytes;
[0029] mod n: modulo n operation;
[0030] O: A special point on the elliptic curve, called the infinity point or the zero point, is the identity element of the additive group of the elliptic curve;
[0031...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More