Internet of things, identity authentication and secret communication method, chip, equipment and medium
A technology of identity authentication and confidential communication, applied in the field of communication security, can solve the problem of high cost, achieve the effect of saving development cost, shortening the development and deployment cycle, and strong versatility
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
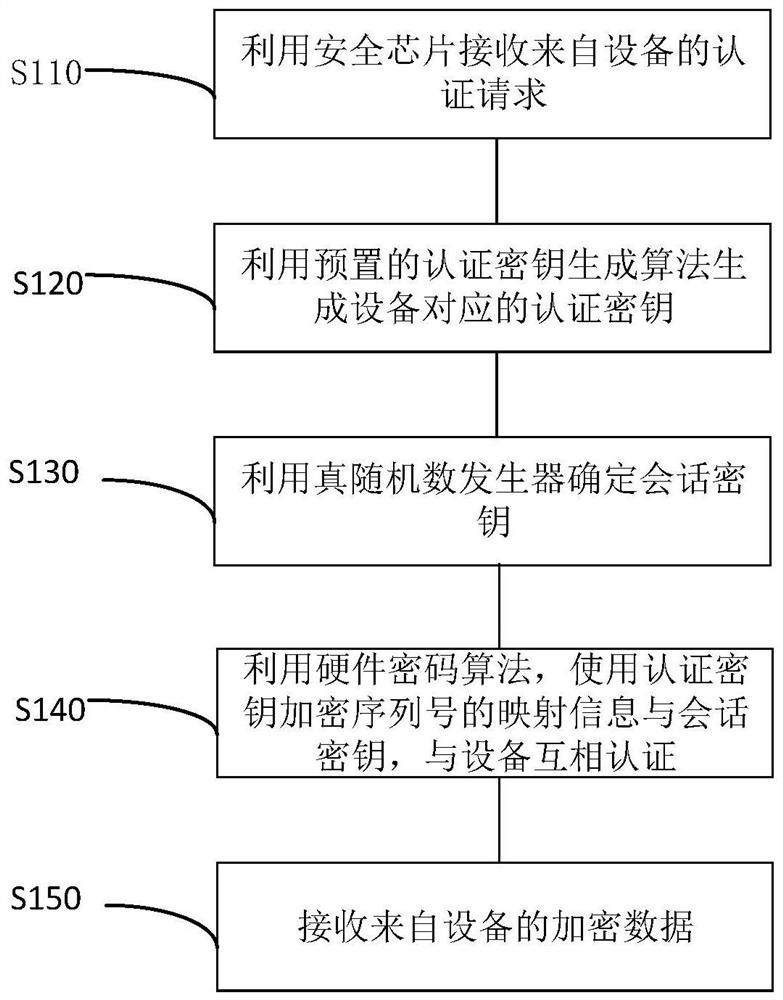
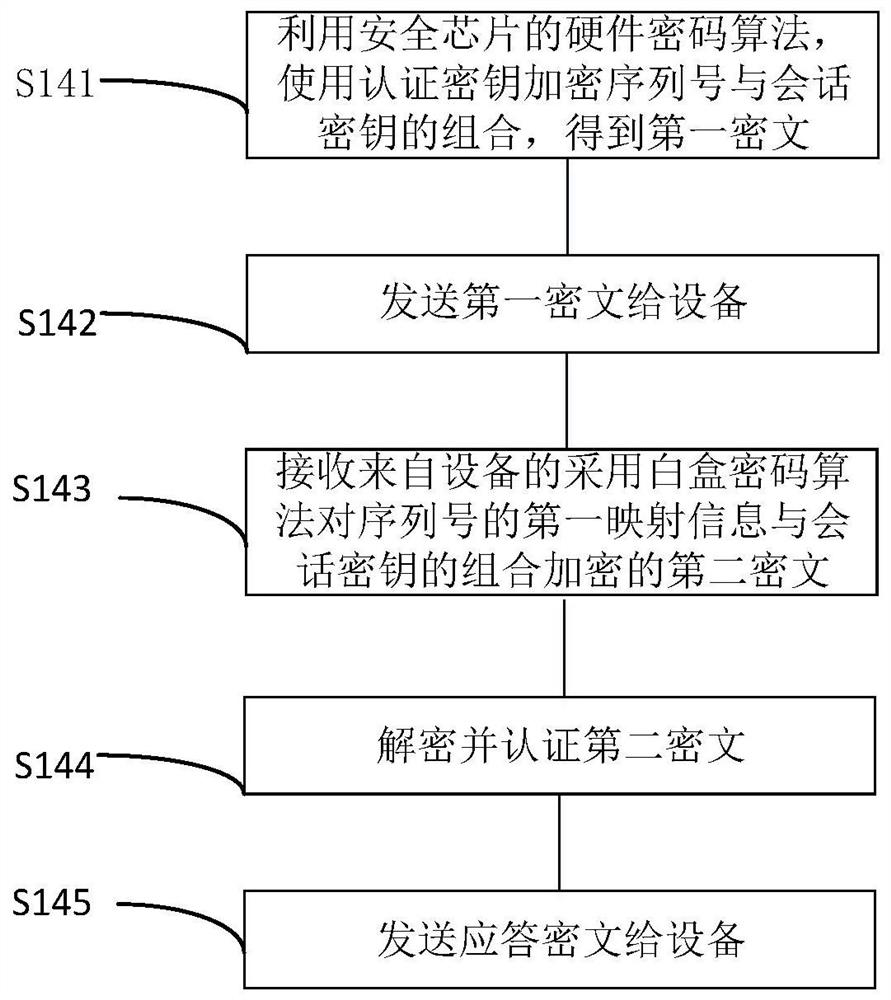
[0046] The following will clearly and completely describe the technical solutions in the embodiments of the present application with reference to the drawings in the embodiments of the present application. Obviously, the described embodiments are part of the embodiments of the present application, not all of them. Based on the embodiments in this application, all other embodiments obtained by those skilled in the art without making creative efforts belong to the scope of protection of this application.
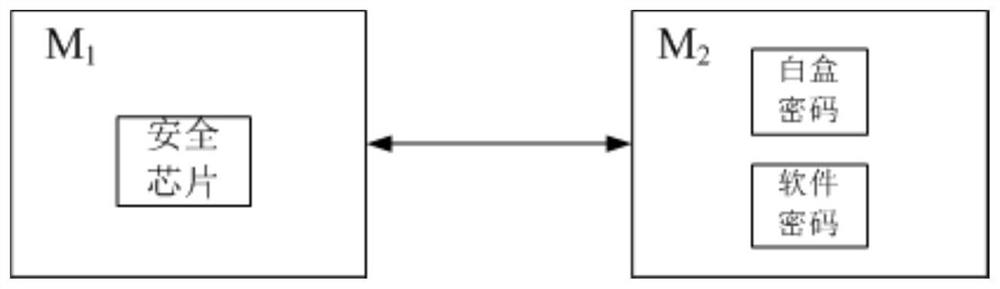
[0047] figure 1 It is a schematic diagram of the composition of the Internet of Things provided by the embodiment of this application.
[0048] Internet of Things includes at least one first device M 1 and at least one second device M 2 . First device M 1 The security chip SE is configured inside. Second device M 2 The first device M with internally configured white-box cryptographic algorithms 1 Through the security chip SE and the second device M 2 Perform identity a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More