Malicious code detection method and system based on recurrent neural network
A malicious code detection and cyclic neural network technology, applied in the field of network security, can solve the problems of large errors, poor transferability, waste of manpower and material resources, etc., and achieve the effect of strengthening detection capabilities, improving accuracy, and reducing manual operations
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0039] The principles and features of the present invention are described below in conjunction with the accompanying drawings, and the examples given are only used to explain the present invention, and are not intended to limit the scope of the present invention.
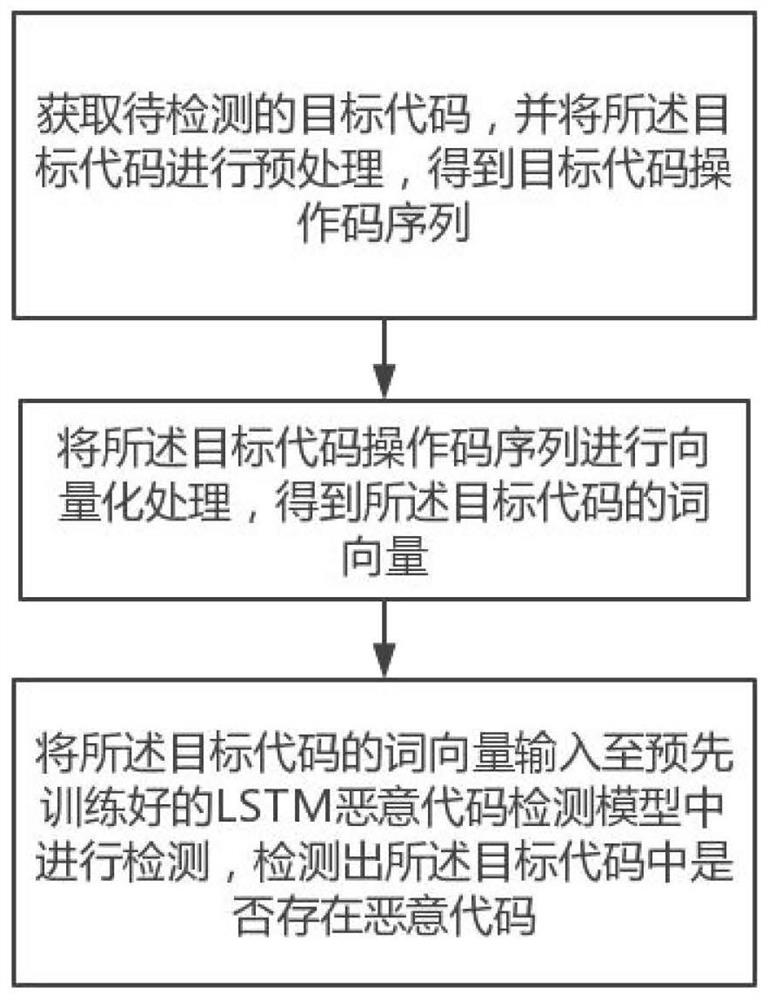
[0040] Such as figure 1 As shown, the present invention provides a malicious code detection method based on a cyclic neural network, comprising the following steps of obtaining the target code to be detected, and preprocessing the target code to obtain the target code operation code sequence; The code operation code sequence is vectorized to obtain the word vector of the target code; the word vector of the target code is input into the pre-trained LSTM malicious code detection model for detection, and the malicious code in the target code is obtained .
[0041] The invention detects the Webshell by using a convolutional neural network of deep learning, and uses a word vector conversion algorithm word2vec to convert...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More