Security access assessment method and device for power terminal equipment
A power terminal and secure access technology, applied in the field of communication security, can solve problems such as not combining the behavior characteristics of end users
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0060] The present invention will be further described below in conjunction with the accompanying drawings. The following examples are only used to illustrate the technical solution of the present invention more clearly, but not to limit the protection scope of the present invention.
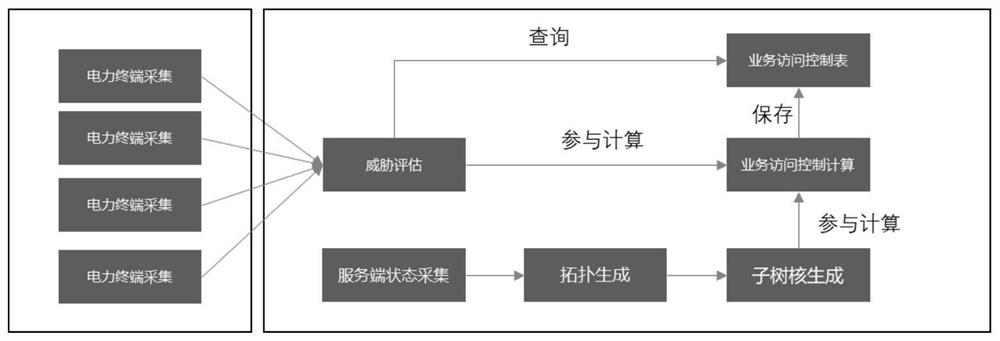
[0061] An embodiment of the present invention provides a security access control evaluation method for power terminal equipment, such as figure 1 As shown, including the following process:
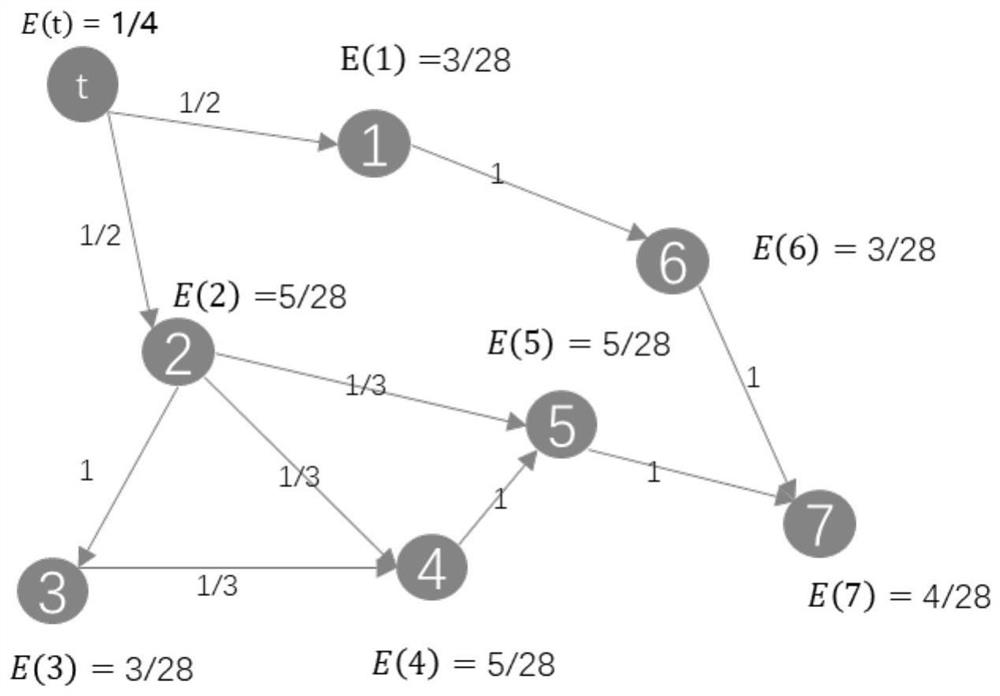
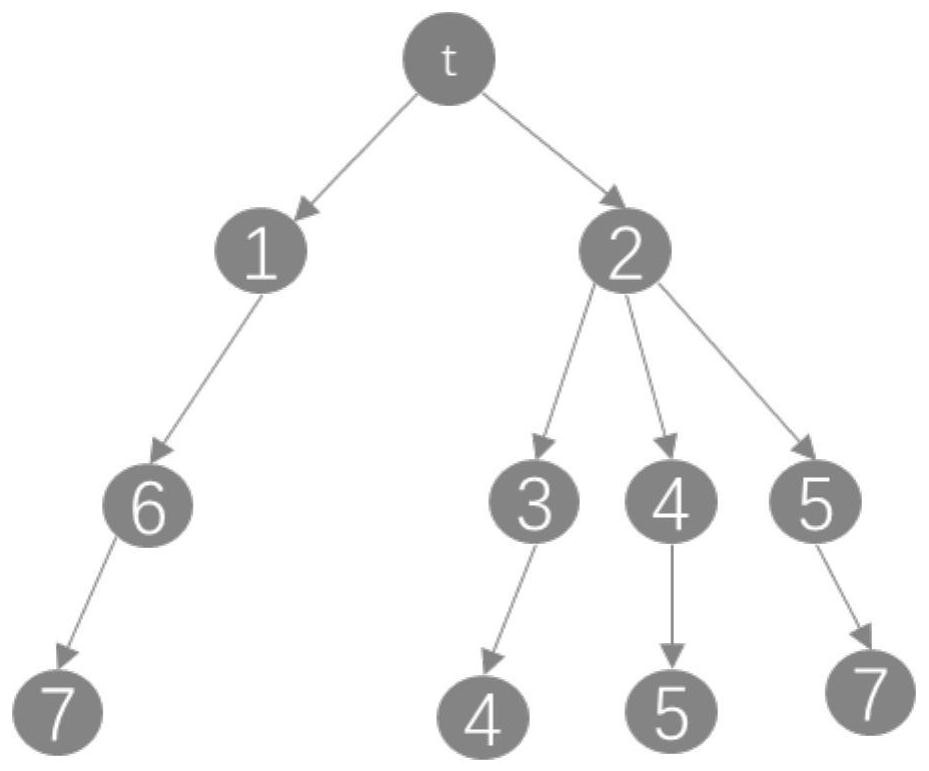
[0062] S1. Deploy the acquisition probe on the power terminal equipment to collect the security status information of the terminal equipment, and use the expert system to evaluate the security status of the terminal equipment according to the collected static configuration and dynamic operating status, and calculate that the terminal equipment is under attack The probability of the power terminal being attacked is related to its vulnerability, and also related to whether the dynamic behavior of the applicat...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More