Data confidential information protection system based on zero-trust network
An information protection and confidentiality technology, applied in the field of communications, can solve the problems of illegal client theft, high protection difficulty, malicious deletion of databases, etc., to prevent interception or forgery, ensure data security, and increase information security.
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0091] The following will clearly and completely describe the technical solutions in the embodiments of the present invention with reference to the accompanying drawings in the embodiments of the present invention. Obviously, the described embodiments are only some, not all, embodiments of the present invention. Based on the embodiments of the present invention, all other embodiments obtained by persons of ordinary skill in the art without making creative efforts belong to the protection scope of the present invention.
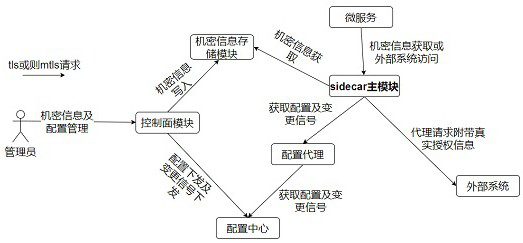
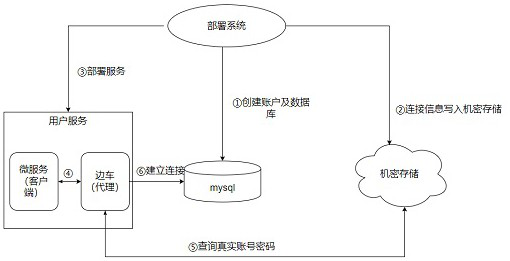
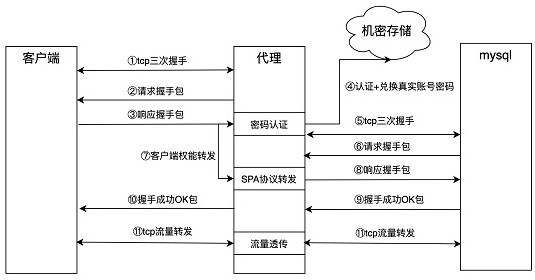
[0092] see Figure 1-Figure 4 , in this example:
[0093] The construction scenario is the password and other information protection scenarios when the service accesses the external mysql system, and mainly describes the case where the mysql access information is used as confidential information for protection.
[0094] MySQL is used as a persistent data storage facility for services, and its security determines the security of the entire service. In real li...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More