Methods and systems for extraction of transaction data for compliance monitoring
a technology of transaction data and compliance monitoring, applied in the field of electronic enterprise transaction compliance monitoring, can solve the problems of affecting the integrity of transactions and reporting of an enterprise, affecting the business continuity of the enterprise, and affecting the integrity of the transaction, so as to reduce asset loss, increase operational effectiveness, and increase corporate and shareholder confiden
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Benefits of technology
Problems solved by technology
Method used
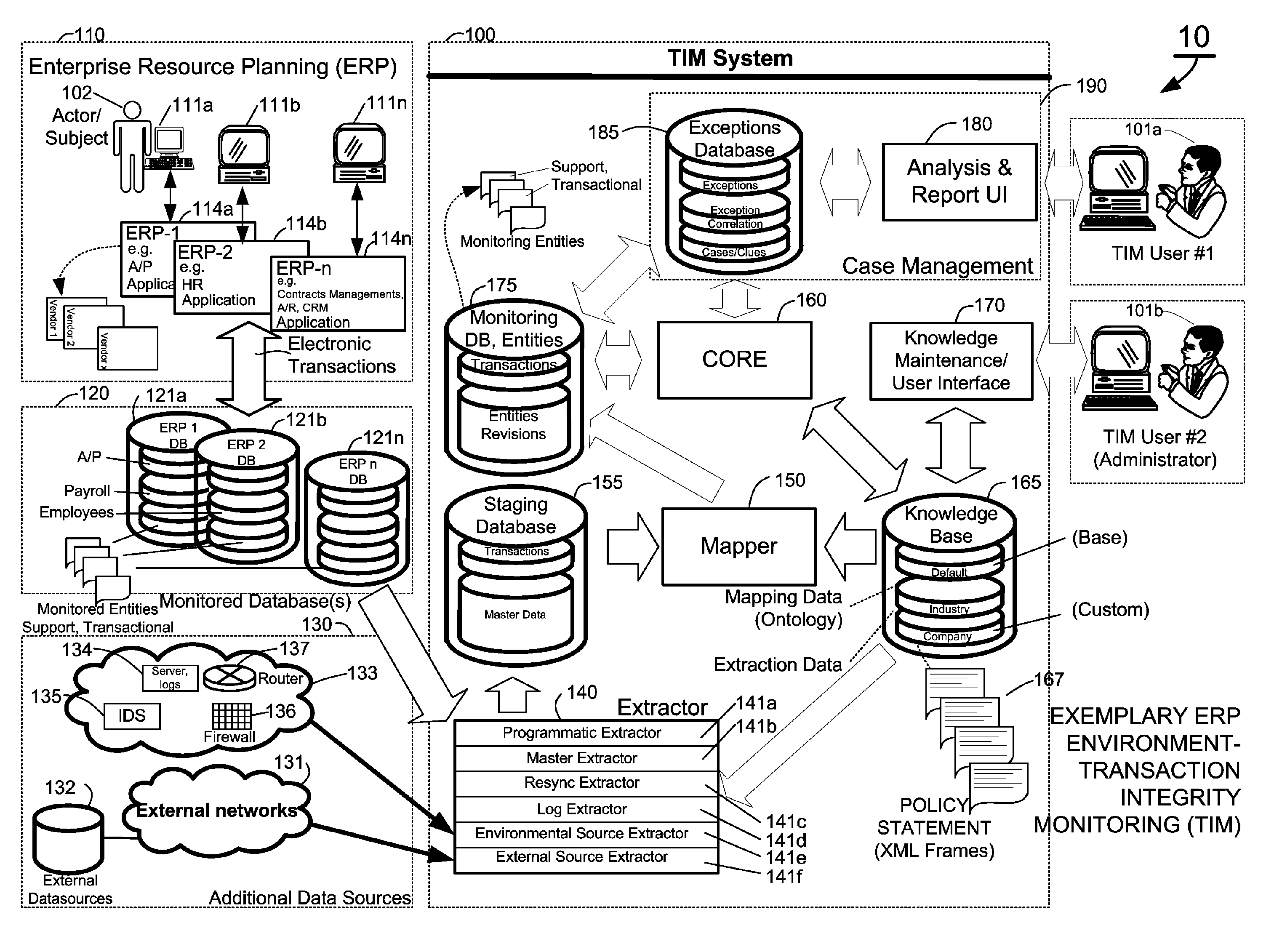
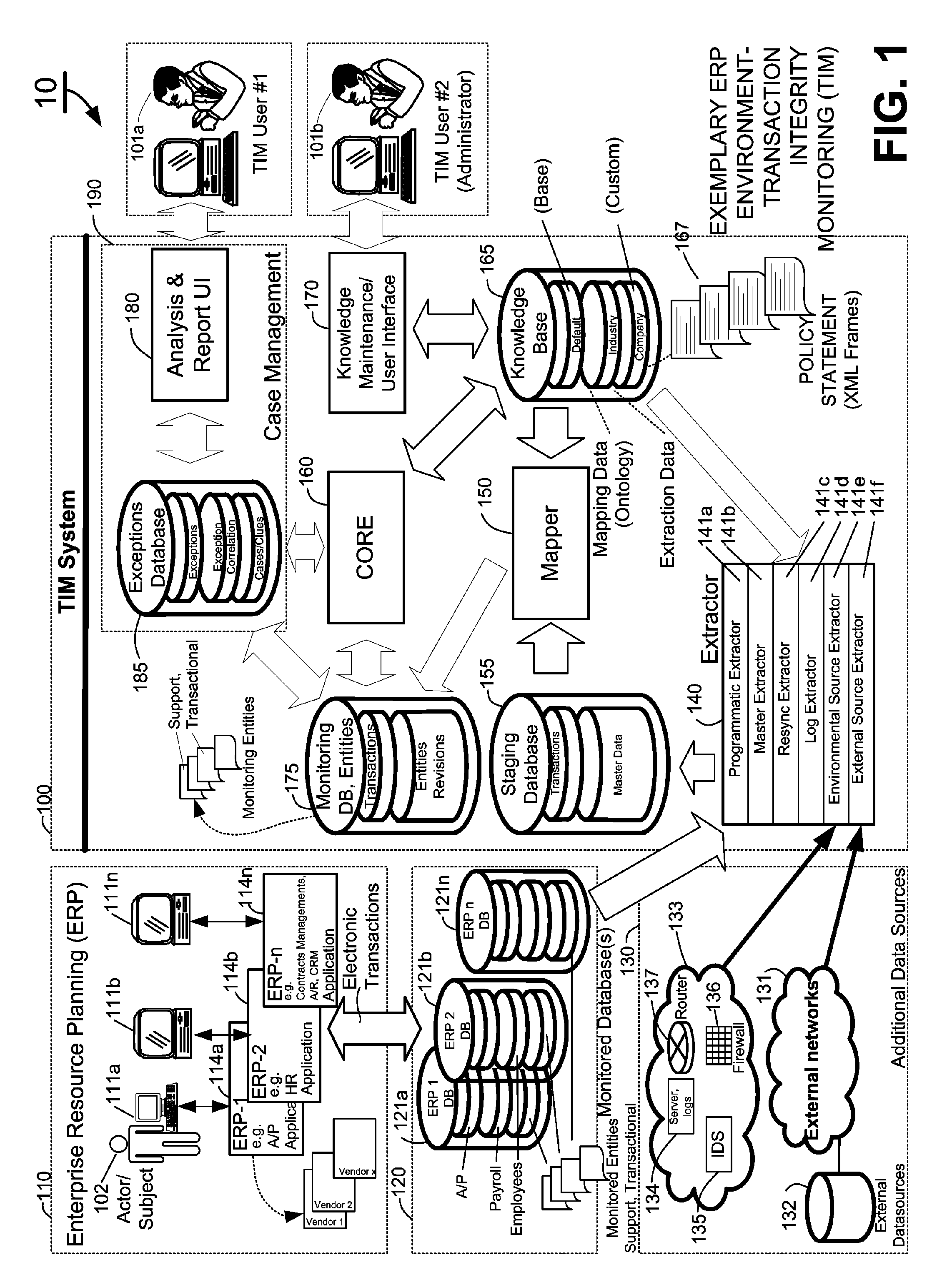
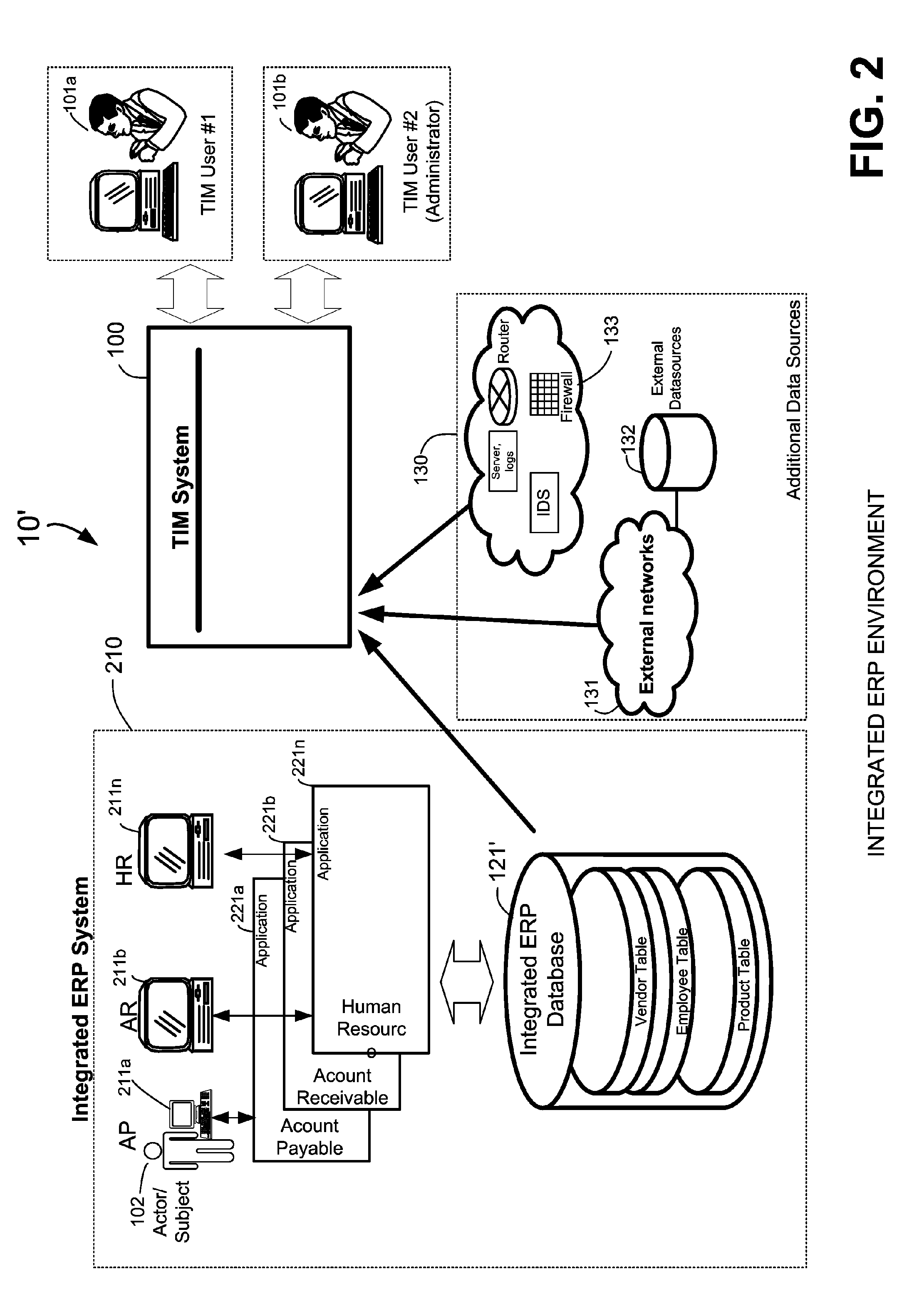
Image
Examples
Embodiment Construction
[0109]Prior to a detailed description of the invention(s), the following definitions are provided as an aid to understanding the subject matter and terminology of aspects of the present invention(s), and not necessarily limiting of the invention(s), which are expressed in the claims. Whether or not a term is capitalized is not considered definitive or limiting of the meaning of a term. As used in this document, a capitalized term shall have the same meaning as an uncapitalized term, unless the context of the usage specifically indicates that a more restrictive meaning for the capitalized term is intended. A capitalized term within the glossary usually indicates that the capitalized term has a separate definition within the glossary. However, the capitalization or lack thereof within the remainder of this document is not intended to be necessarily limiting unless the context clearly indicates that such limitation is intended.
DEFINITIONS / GLOSSARY
[0110]Actor: an individual responsible ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More