Share secret key management method
A technology for sharing keys and management methods, applied in the field of wireless communication, can solve the problems of easy access, poor confidentiality, trouble, etc., and achieve the effect of enhancing security and protecting interests
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0032] The preferred embodiments of the present invention will be described below in conjunction with the accompanying drawings. It should be understood that the preferred embodiments described here are only used to illustrate and explain the present invention, and are not intended to limit the present invention.
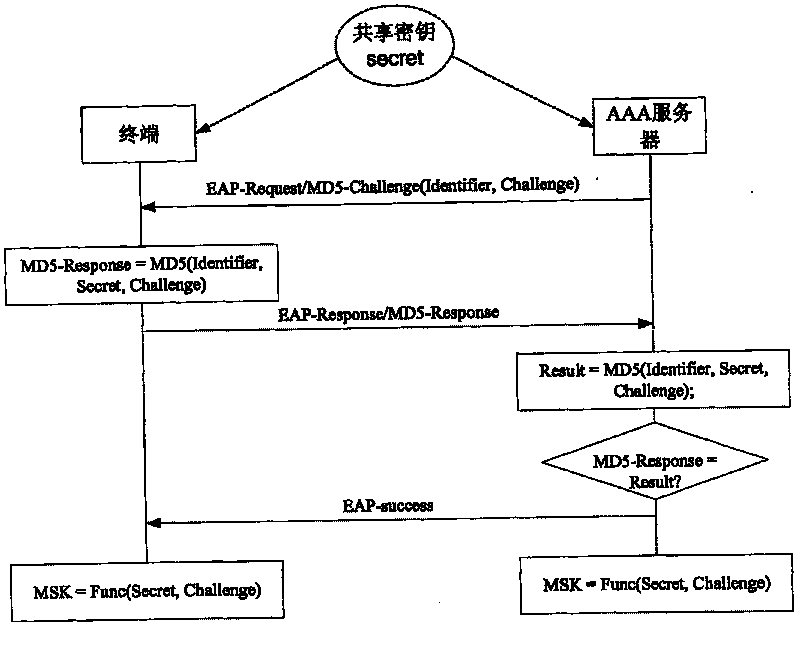
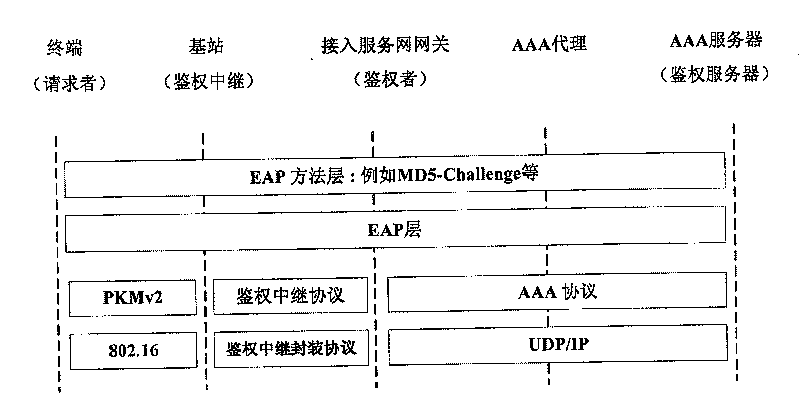
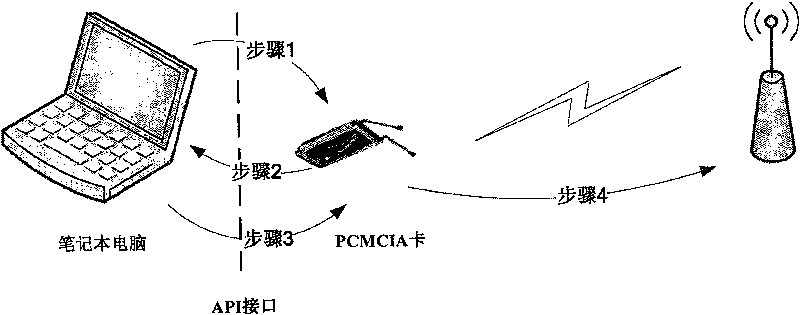
[0033] Figure 4 It is a schematic diagram of assigning and saving shared passwords when users log in to the network according to an embodiment of the present invention. Figure 5 It is a schematic diagram of storing and using terminal shared passwords according to an embodiment of the present invention. Image 6 is a flowchart of the shared key management method according to the present invention.
[0034] The following will combine Figure 4 and Figure 5 Details such as Image 6 The shared key management method of the present invention is shown. According to an embodiment of the present invention, the business acceptance terminal of the operator is composed ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More