An encryption device, a decrypting device, a secret key generation device,a copyright protection system and a cipher communication device
A cryptographic communication and key technology, which is applied in key distribution, can solve the problem of illegal transmission of digital products, etc., and achieve the effect of safe transmission, high practical value, and prevention of attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
no. 1 example
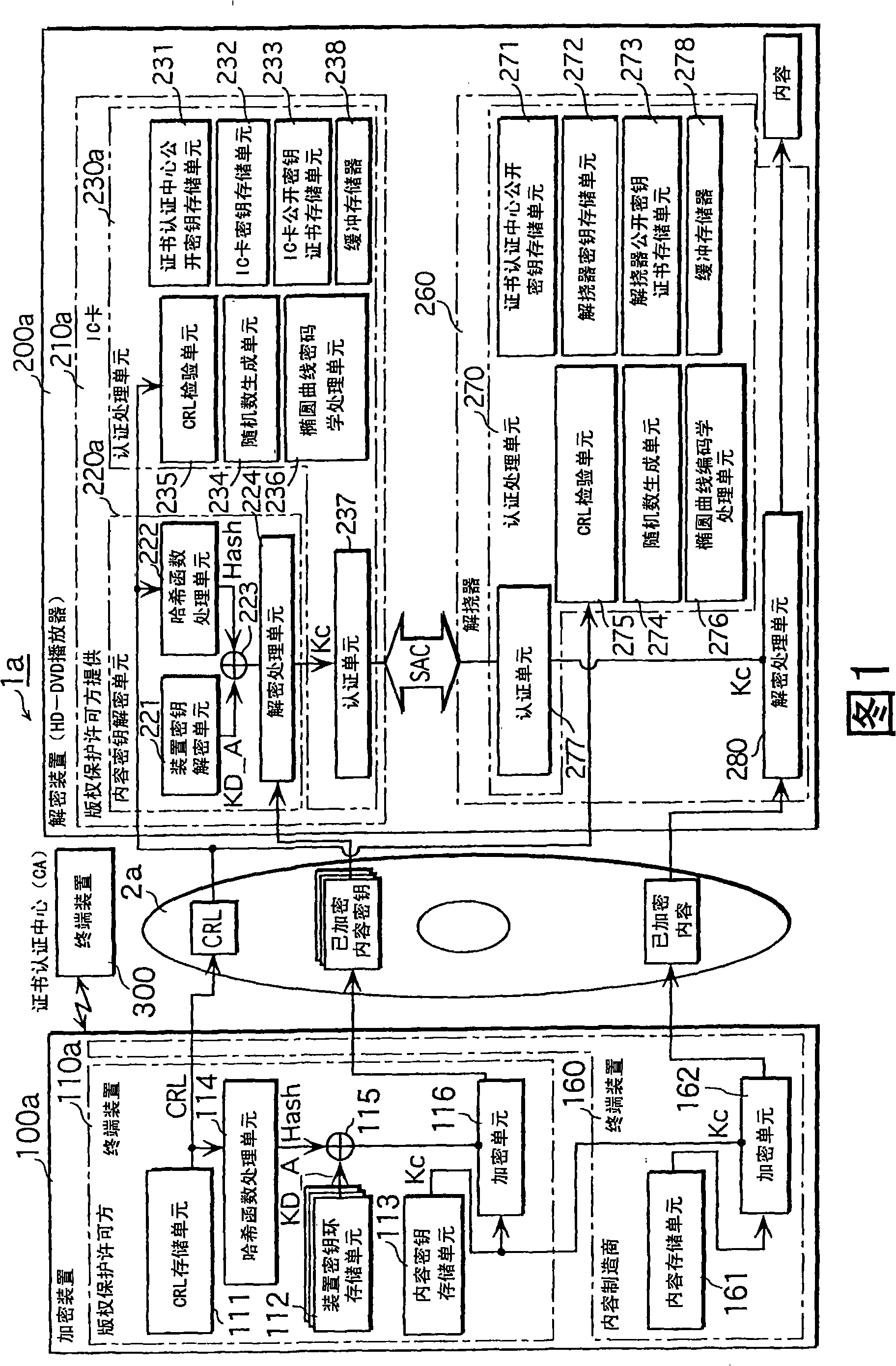
[0050] FIG. 1 is a functional block diagram showing the overall structure of a recording medium copyright protection system according to a first embodiment of the present invention.
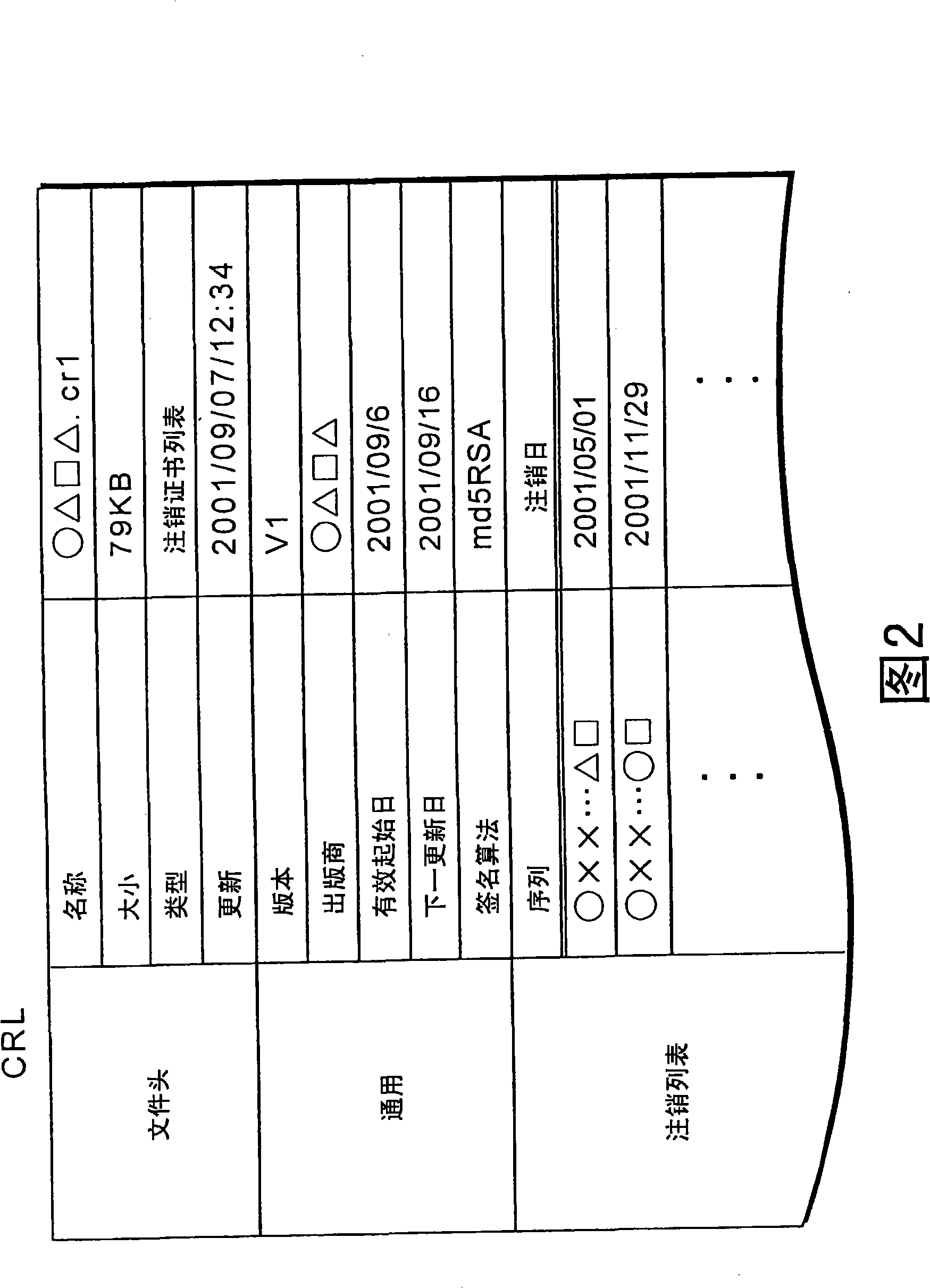
[0051] The recording medium copyright protection system 1a is a system that records encrypted content on a DVD 2a as a recording medium, or reads encrypted content from the DVD 2a and decrypts it. The system includes an encryption device 100a that stores encrypted content on a DVD 2a; a decryption device 200a that reads encrypted content from the DVD 2a and decrypts it; and a terminal device 300 used by a certificate authority (CA) that issues a CRL, and the like.
[0052] The encryption device 100a includes two terminal devices, the terminal device 110a is used by a copyright protection licensor, and the terminal device 160 is used by a content manufacturer.
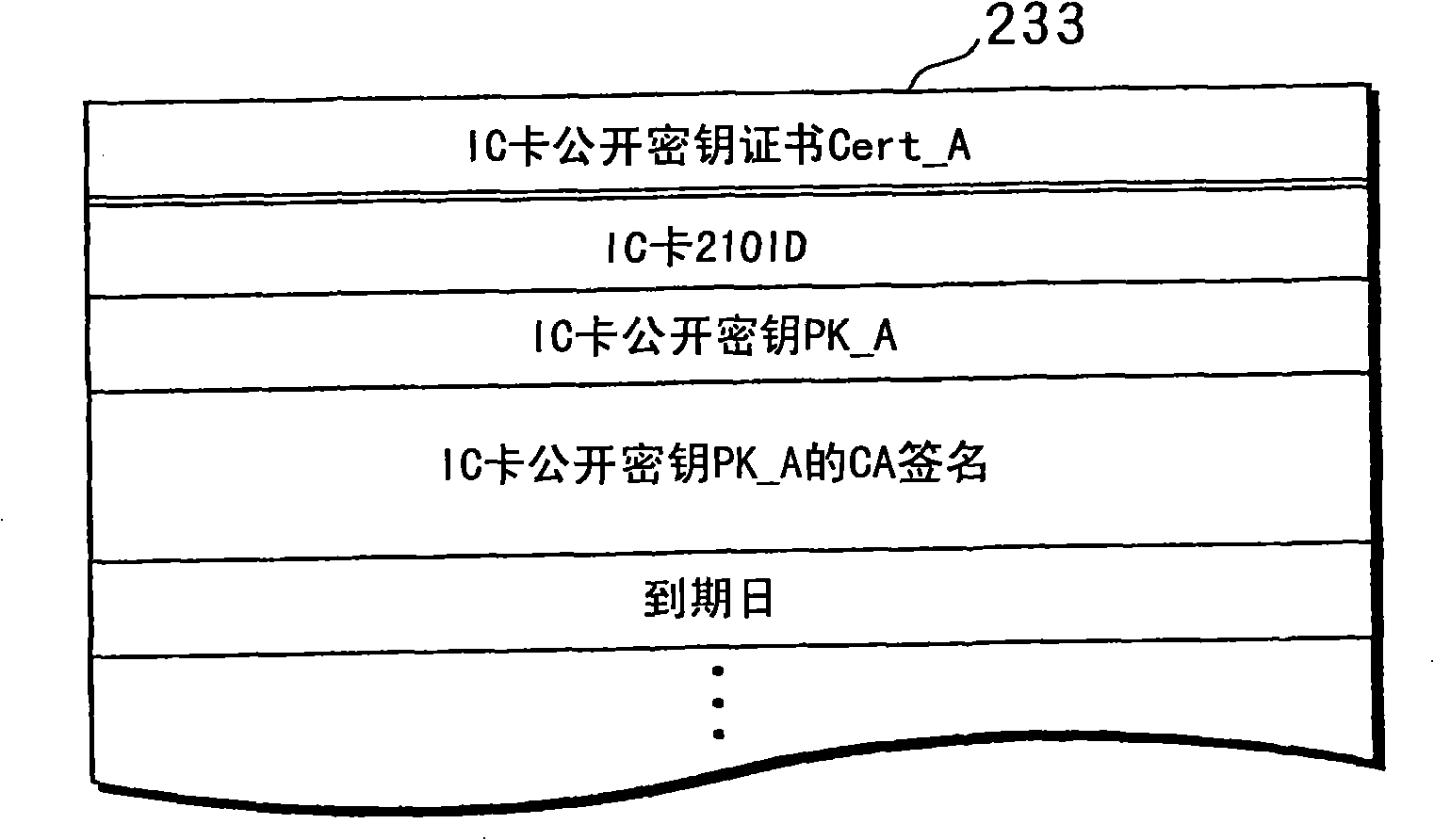
[0053] The decryption device 200a is, for example, an HD-DVD player capable of reproducing the content of HD (1125i / 750p) at the image le...
no. 2 example
[0108] Fig. 6 is an external view of the structure of a recording medium copyright protection system 1b according to the second embodiment. Since the constituent parts of the recording medium copyright protection system 1b corresponding to the constituent parts of the recording medium copyright protection system 1a of the first embodiment have the same reference numerals, they are omitted except for parts different from the recording medium copyright protection system 1a. illustrate.
[0109] In the terminal device 110a of the encryption device 100a according to the first embodiment, the exclusive OR unit 115 performs an exclusive OR operation between the CRL hash value Hash output from the hash function processing unit 114 and each device key. The encryption unit 116 encrypts the content key Kc using the exclusive OR value, and generates an encrypted content key ring. On the other hand, according to the terminal device 110b in the encryption device 100b of the second embodim...
no. 3 example
[0117] FIG. 7 is a functional block diagram of the overall structure of a recording medium copyright protection system 1c according to the third embodiment. In this figure, functional portions corresponding to the recording medium copyright protection system 1a of the first embodiment are not shown, and only portions specific to the recording medium copyright protection system 1c are shown.
[0118] The IC card 210a of the decryption device 200c according to the first embodiment simply transmits the obtained content key Kc to the descrambler 260b. In this way, it is impossible for the IC card 210a itself to know whether the obtained key is a qualified key capable of decrypting encrypted content. Therefore, it is desirable to check in advance whether or not the descrambler 260 has a correct value before transferring the obtained content key Kc to the descrambler 260b.
[0119] Therefore, the recording medium copyright protection system 1c according to the third embodiment is a...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More