Single-point login method under point-to-point model
A single-sign-on, point-to-point technology, applied to the public key of secure communication, user identity/authority verification, electrical components, etc., can solve problems such as reducing security, and achieve the effect of increasing security, reducing burden, and improving efficiency
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
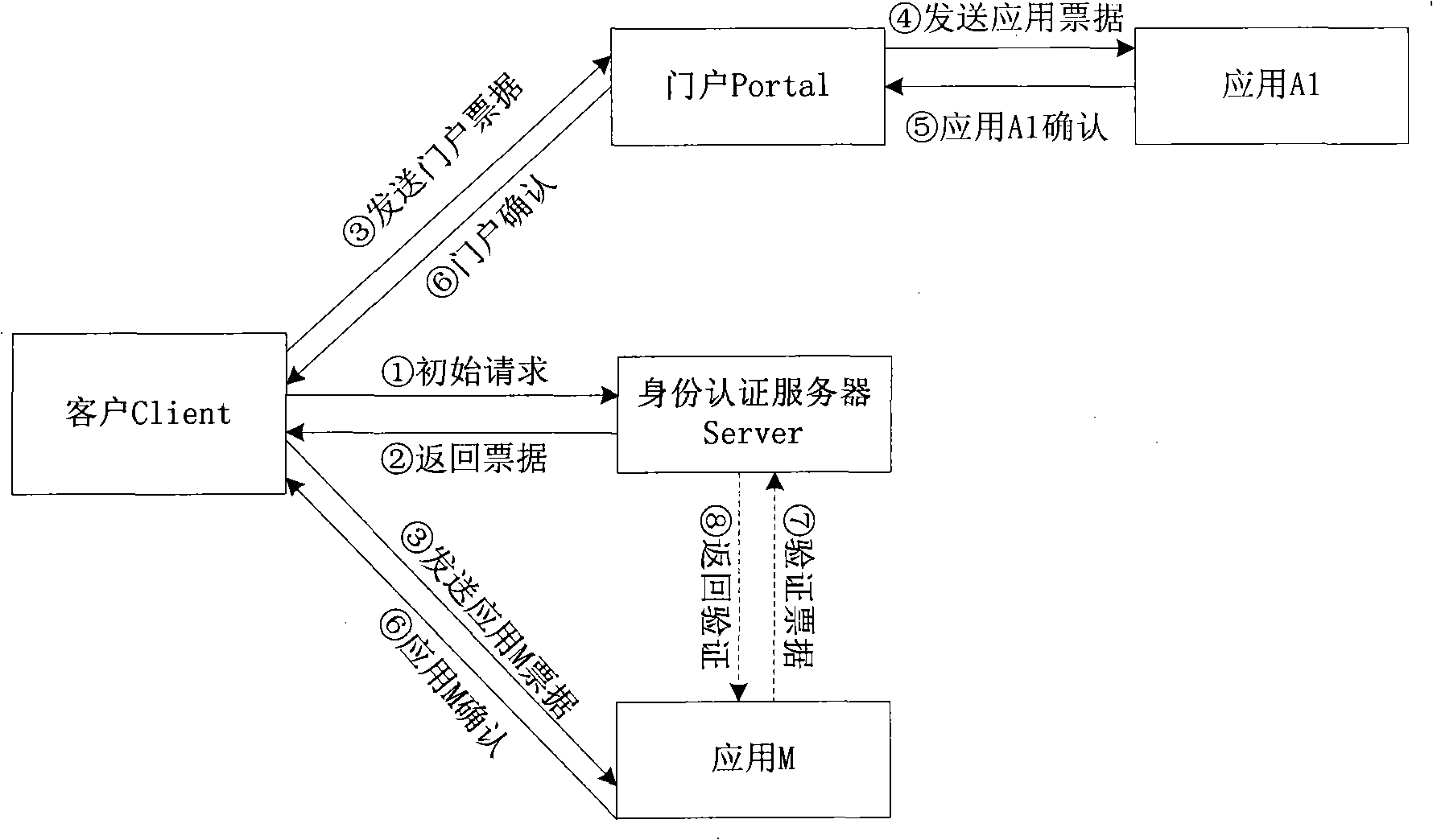
[0019] see figure 1 , the application system A1 has been connected to the portal P. When the client C needs to access the application system A1, the client C first visits the identity authentication server S to obtain the corresponding certificate. The client C passes the certificate to the portal P, and the portal P sends the certificate to Application system A1, application system A1 authorizes the user according to the customer role marked in the certificate, portal P and application system A1 judge whether the certificate held by the user is valid according to the start time and end time of the certificate mark, and manage the user's life cycle.
[0020] The complete login process is divided into 8 steps:
[0021] Step 1. Client C uses the public key of the authentication server S to encrypt the client's identity C, client name, password, application system A1 and random number N CS , and then send the encrypted message to the authentication server.
[0022] EK S {S, Us...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More