Method and system for simulating a hacking attack on a network
A hacker attack, network technology, applied in transmission systems, instruments, electrical digital data processing, etc., can solve problems such as inability to find attacks
- Summary
- Abstract
- Description
- Claims
- Application Information
AI Technical Summary
Problems solved by technology
Method used
Image
Examples
Embodiment Construction
[0025]While preferred embodiments of the invention have been shown and described, it should be understood that the invention is not limited to these embodiments. Numerous modifications, changes, changes, substitutions and equivalents will be apparent to those skilled in the art without departing from the spirit and scope of the present invention described in the claims.
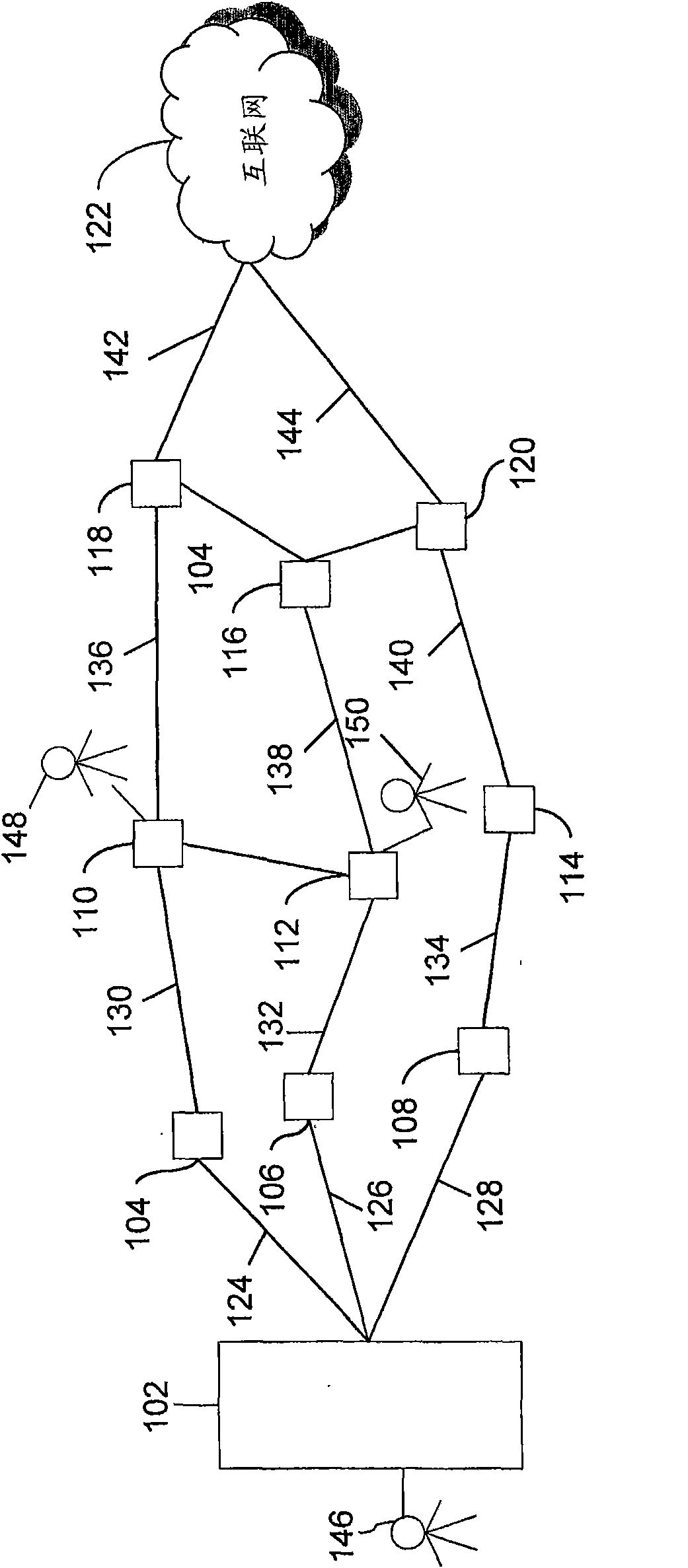
[0026] figure 1 is an exemplary environment in which the invention may be practiced in accordance with various embodiments of the invention. figure 1 A number of data processing units (DPUs) are shown connected together with various components of a DPU network (such as a mainframe server, intranet, Internet). Examples of DPUs may be devices such as personal computers, laptop computers, mobile phones, personal digital assistants (PDAs), Various computing devices such as smartphones. Furthermore, examples of networks between which different DPUs can exchange information or data with each other may be Local ...
PUM
 Login to View More
Login to View More Abstract
Description
Claims
Application Information
 Login to View More
Login to View More